-
Title
How to set up E-Mail OTP tokens in Defender -
Description
E-Mail OTP tokens are new in Defender 5.6
-
Resolution
There are two parts to enabling emailed one-time passwords (OTPs): enabling them in the Defender Policy, and enabling them on the Self-Service Portal. The ability to issue the token from ADUC was added in Defender 5.7 and above; in earlier versions (5.6) the user must request it from the Defender Software Token Request web page. There is no separate license necessary.
For full detail regarding configuring the Defender E-Mail tokens please review the Defender documentation.
To enable email OTP tokens in the Defender Policy:
1. In ADUC, navigate to the domain for which the OTP tokens are to be enabled and select Defender | Policies.
2. Right-click on the Policy for which e-mail OTP tokens should be enabled and select Properties.
3. Select the E-Mail OTP tab.
4. Check the Enable E-Mail OTP Tokens check box.
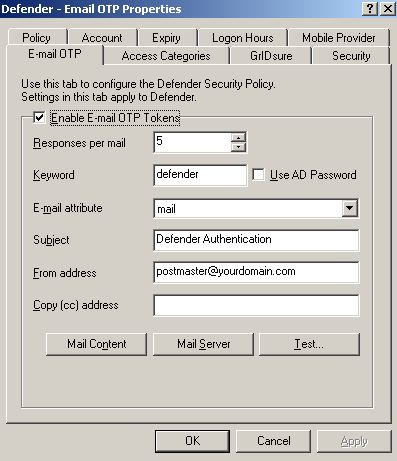
5. There are options that affect the ability of the user to trigger the sending of an email with a list of new OTPs. If there is a string in the Keyword field, the user can use that string instead of the expected OTP to trigger the sending of an email with a list of new OTPs. If the Use AD Password box is checked, the user can enter their domain password instead of an expected OTP to trigger the sending of an email with a list of new OTPs.
6. Fill in the data fields as per your policy and click the Apply button.
7. Click the Mail Server button and enter the details of the mail server to use, including authentication details if necessary, and click the OK button. The mail server must allow relaying to the domains of the email addresses that will be receiving the tokens.
8. Test the configuration by clicking the "Test…" button and entering an email address to which you have access that is in the Policy’s domain. Check the email account to see if the email was received.
9. Click OK once the configuration is complete.
To issue the tokens:
1. Install the Defender Web Interface as per the Defender Token Deployment System Installation and Configuration Guide.
2. Log into the Web Interface as Administrator and select Token Deployment System | Configure.
3. Select the Software Tokens tab
4. In the E-Mail OTP field, enter the name of an AD group whose members are allowed to get E-Mail OTP tokens and click the Save button
5. Select the E-mail settings tab, enter the IP address, port, and from email address and click Save
6. For each user:a) Ensure that the AD user has a valid email address in whichever AD attribute was specified in the Policy configuration.
b) Ensure that the user is in the AD group who are entitled to request E-Mail OTP tokens.
c) Send the user to the Request page of the Defender Web Interface where they can log in with their AD credentials and click on the E-Mail OTP logo.
d) The user will receive an email with a link they can click to finish their registration and pick their PIN (if so configured in Token Deployment System settings)How the tokens are deployed:
1. The first time the user tries to log in, they will be asked for their credentials as usual.
2. If the user does not have any OTP passwords, they enter their username as usual but instead of using a token response enter the Keyword (defined under 4 above).
The DSS server will send them an email with a number of one-time passwords. (If configured the user may also need to use their PIN)3. The user may be prompted for their domain password, just for this initial setup, if the AD password is not one of the required authentication methods.
Each time the user logs in after that, they should use the next OTP from the email. When the password list is nearing full use, a new email with more passwords will be sent.
-
Additional Information
To use Email-OTP the Defender Security Servers all need to be using version 5.6 or above. This can be checked in ADUC | Defender OU | Security Servers | Double click on each server in turn checking that version on the "Security Server" tab 5.6.x.x or higher
