The available ICA channel types and their functionalities are described below. For a list of supported client applications, see Supported protocols and client applications.
-
Drawing (Thinwire): Enables access to the server's desktop (screen). This channel is for remoting graphics and user input (keyboard, mouse). This channel must be enabled for ICA to work.
-
Audio Mapping: Enable access to the sound device of the server.
-
Drive Mapping: Enable access to the client's hard drives on the server.
-
Clipboard: Enable access to the server's clipboard: the clipboard of the remote desktop can be pasted into local applications (and vice-versa). Note that One Identity Safeguard for Privileged Sessions (SPS) can audit the clipboard channel, but the Safeguard Desktop Player currently cannot search or display its contents.
-
Smartcard: Enable using client side installed smartcards in server-side applications.
-
Printer (COM1): Enable access to the serial port COM1.
-
Printer (COM2): Enable access to the serial port COM2.
-
Printer (LPT1): Enable access to the parallel port LPT1.
-
Printer (LPT2): Enable access to the parallel port LPT2.
-
Printer Spooler: Enable access to the client's printer from the remote desktops and applications.
-
HDX Mediastream: Some user widgets (for example Flash player) will not run on the server but on the client. These widgets are controlled from the server side using this channel. This is not supported by Safeguard Desktop Player and it is disabled by default.
-
USB: Enable using client side installed USB devices in server-side applications.
-
Seamless: Enable seamless channels that run a single application on the ICA server, instead of accessing the entire desktop. When disabled, the application window will be accessed along with an empty desktop.
-
Speedbrowse: Speeds up web browsing. Not currently supported by Safeguard Desktop Player, should be disabled by default.
-
Custom: Applications can open custom channels to the clients connecting remotely to the server. Enabling the Custom channel allows the clients to access all of these custom channels. To permit only specific channels, enter the unique names of the channel into the Details field.
NOTE: When the channel opens, there are certain cases when the remote group is not known yet. For example, in case of an RDP or ICA login screen, the drawing channel has to be opened first to properly display the logon screen. Only those channel rules will apply, where the Remote group field is empty. In case of network level authentication, all required information is present already so this limitation does not apply.
NOTE: Multi-stream ICA is not supported in SPS 7.1.
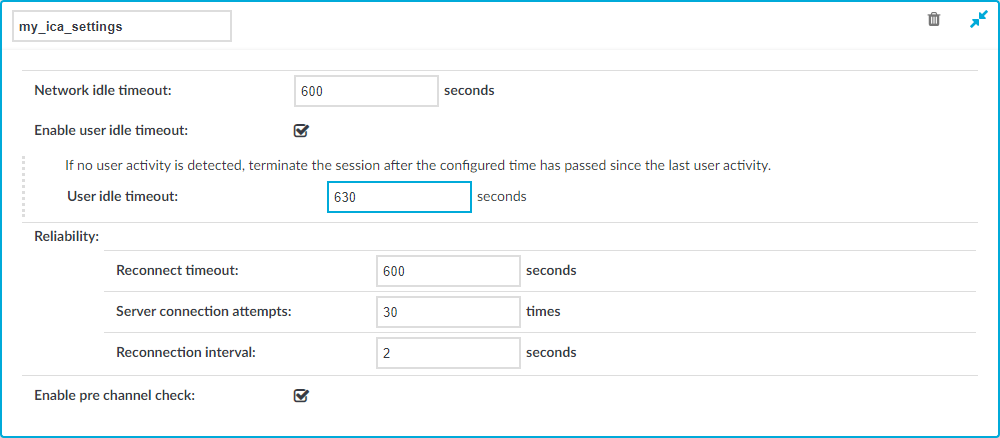
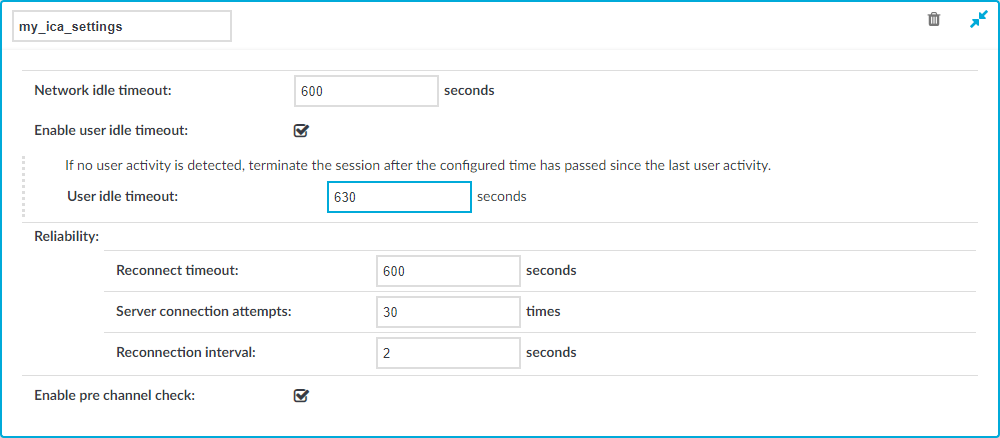
ICA settings determine the parameters of the connection on the protocol level, including timeout value, and so on.
Figure 208: ICA Control > Settings — ICA settings
|

|
Caution:
Modifying the ICA settings is recommended only to advanced users. Do not modify these settings unless you exactly know what you are doing. |
To create a new ICA settings profile or edit an existing one
-
Navigate to the Settings tab of the ICA Control menu item and click  to create an ICA setting profile. Enter a name for the profile (for example ica_special).
to create an ICA setting profile. Enter a name for the profile (for example ica_special).
-
Click  to display the parameters of the ICA connection.
to display the parameters of the ICA connection.
-
Modify the parameters as needed. The following parameters are available:
-
Network idle timeout: Connection timeout value in seconds. To avoid early timeout, set it to a larger value, for example a week (604800 seconds).
Even if the user is not active, the session can contain activity that must be audited (for example, the output of a script). The idle timeout period will start only after this activity has stopped.
|

|
Caution:
Determining if a connection is idle is based on the network traffic generated by the connection, not the activity of the user. For example, if an application or the taskbar of a graphical desktop displays the time which is updated every minute, it generates network traffic every minute, negating the effects of timeout values greater than one minute and preventing One Identity Safeguard for Privileged Sessions (SPS) from closing the connection. |
-
User idle timeout: If no user activity is detected, terminate the session after the configured time has passed since the last user activity.
This can be useful if only user-generated network traffic is important in a session. By using this option, situations described in the caution of Network idle timeout (such as a taskbar clock keeping the network traffic open indefinitely) can be avoided. To enable user idle timeout, select Enable user idle timeout and enter a value that is greater than or equal to the value of Network idle timeout.
-
Reconnect timeout: How many seconds SPS waits for reconnections when reliable connections are used. Reliable connections use the Common Gateway Protocol (CGP).
-
Server connection attempts: How many times SPS tries to connect to the target server.
-
Reconnection intervals: How many seconds SPS waits between two connection attempts on the server side.
-
Enable pre channel check: Select this option to evaluate the connection and channel policies before establishing the server-side connection. That way if the connection is not permitted at all, SPS does not establish the server-side connection.
NOTE: Reliability settings only apply if you have enabled Reliable connection in ICA Control > Connections.
-
Click  .
.
-
Select this settings profile in the ICA settings field of your connections.
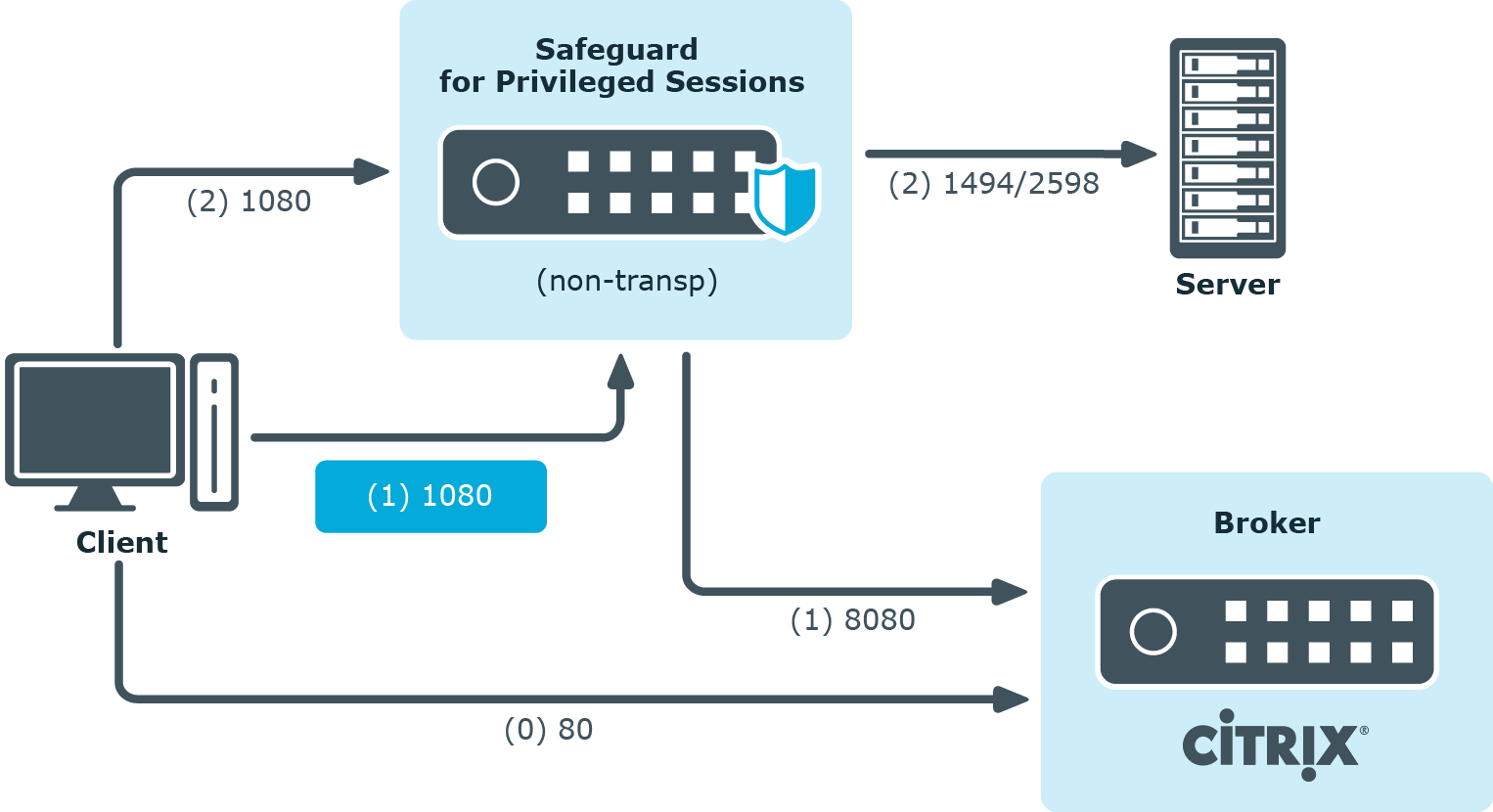
This section enlists the available One Identity Safeguard for Privileged Sessions (SPS) deployment scenarios in a Citrix environment. The text on the arrows are formatted in (<step number>) <target port> format. The target ports define the protocols used in the communication:
-
80: Web service, HTTP: the list of available resources fetched in an XML format from the broker (v12 and v11 with Citrix Virtual Apps (formerly known as Citrix XenApp) only). The broker sends all the necessary information, including secure gateway and server addresses to the client.
-
8080: XML service, HTTP+XML: application discovery, load balancing (v12 and v11 with Citrix Virtual Apps (formerly known as Citrix XenApp) only), used to fetch target to the application/desktop by the client from the broker (used for load balancing, and so on).
-
443: XML service access or SOCKS/ICA or CGP/ICA wrapped in TLS. The client communicates with the secure gateway on this port for everything.
-
1080: SOCKS. The client can be configured to access the target server and the broker using a SOCKS proxy.
-
1494: Plain ICA.
-
2598: CGP/ICA (reliable mode enabled).
|

|
Caution:
Accessing Citrix Virtual Desktops (formerly known as Citrix XenDesktop) is supported only in the following scenarios. Only reliable connections (CGP) are supported.
|
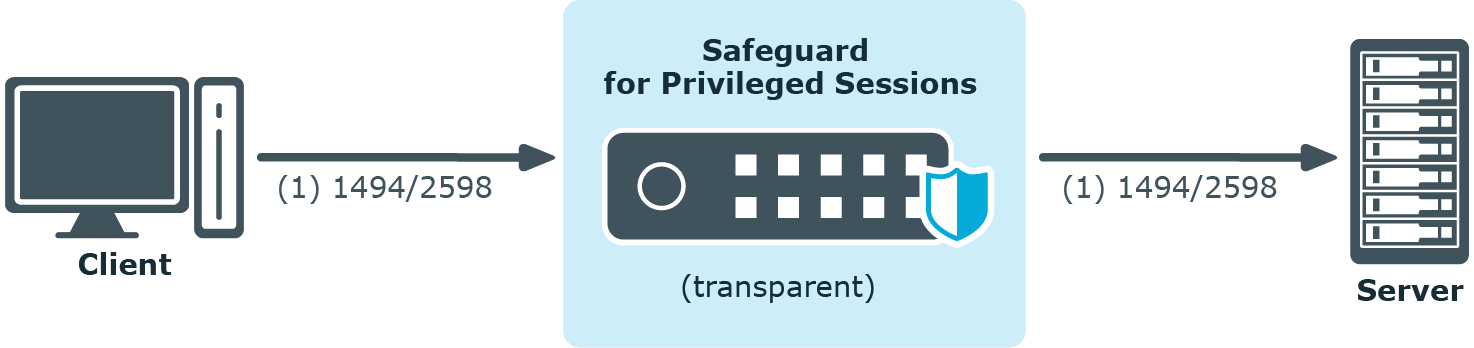
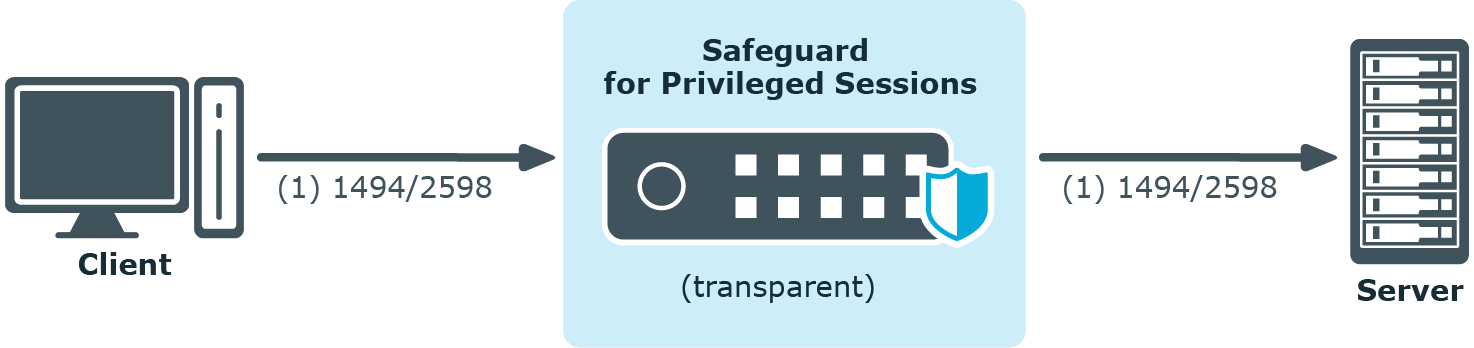
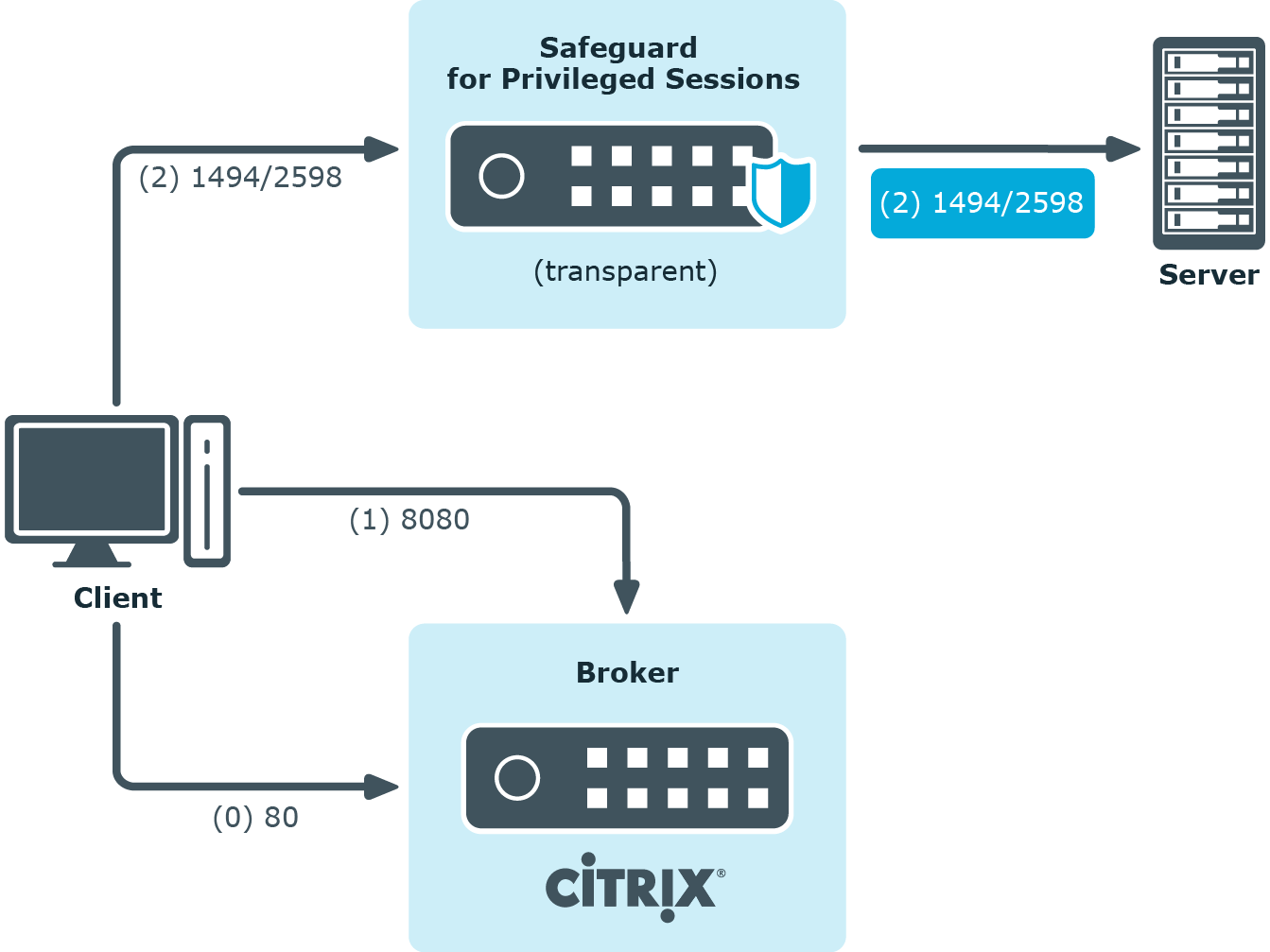
Client - SPS - Server (Transparent mode)
The SPS is deployed between the client and the server and the clients use predefined connection files or Program Neighbourhood, without a broker or secure gateway. The clients try to connect to their original ICA/CGP server.
Figure 209: Client - SPS - Server (Transparent mode)
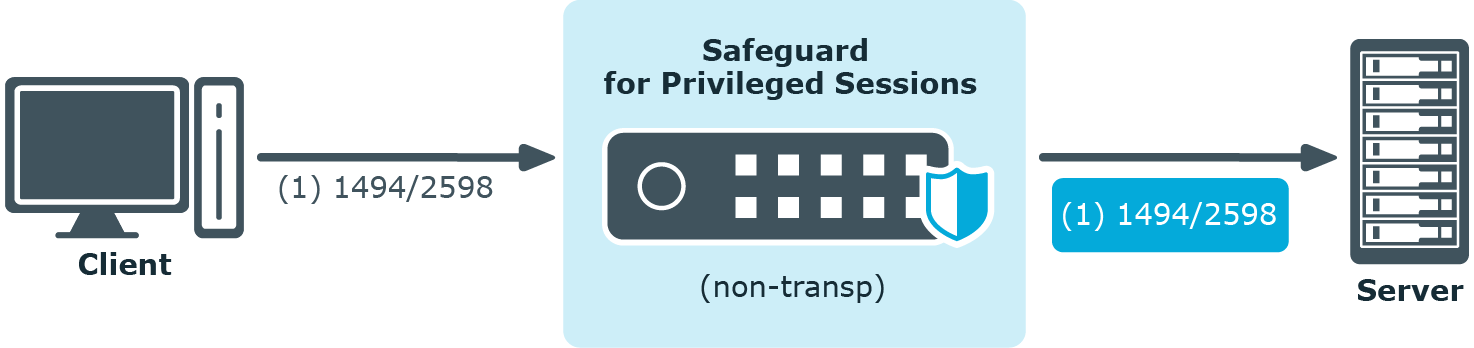
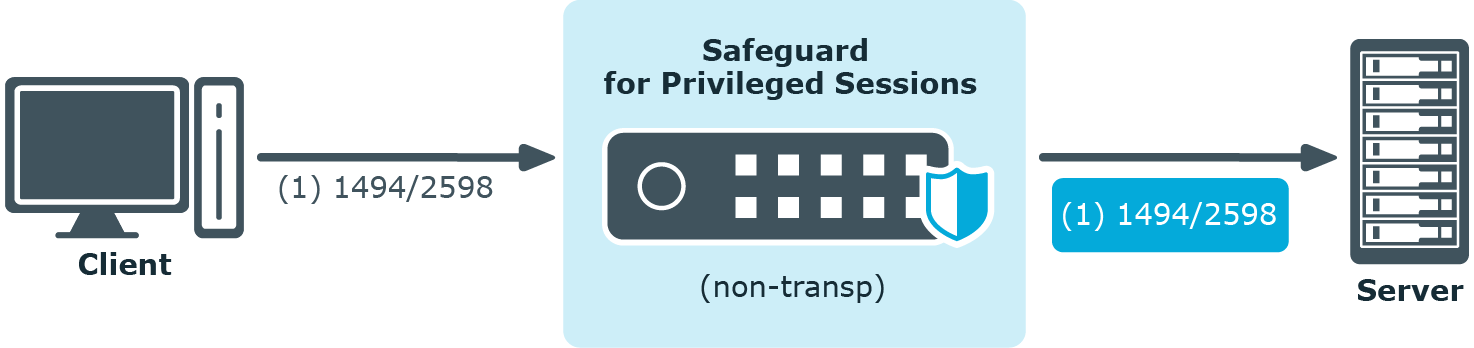
Client - SPS - Server (Non-transparent mode)
The SPS is deployed between the client and the server and the clients use predefined connection files or Program Neighbourhood, without a broker or secure gateway. The clients try to connect to SPS, which can distinguish between the potential targets for example by source IP, or by having multiple IP addresses itself.
Figure 210: Client - SPS - Server (Non-transparent mode)
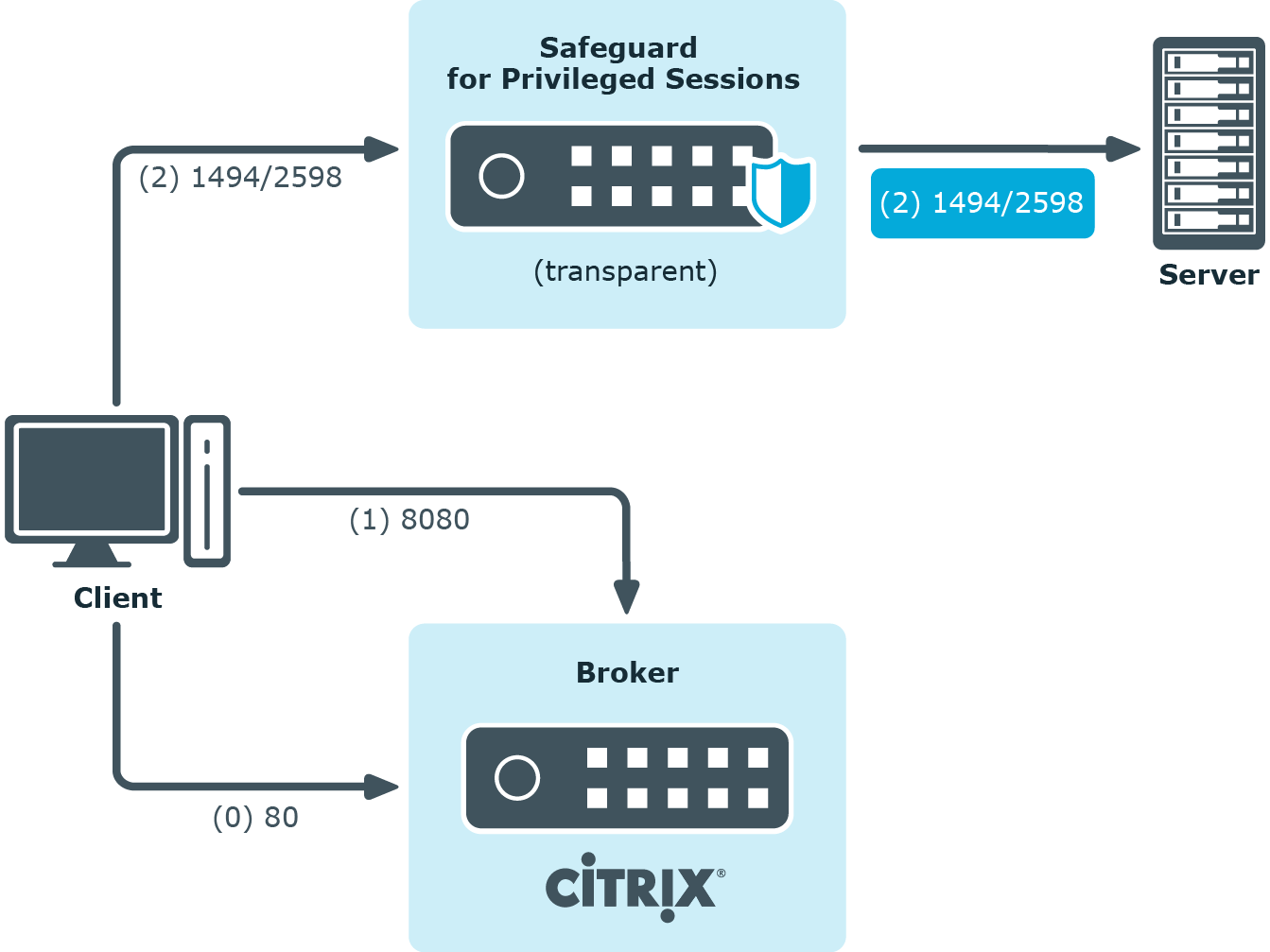
Client - Broker - SPS - Server (Transparent mode)
The clients are using a farm broker which gives them a list of the available applications and servers, but they do not use a secure gateway in the network. The SPS is placed between the clients and the servers in transparent mode, and it catches the connections when the clients try to connect to the server IP addresses they got from the broker.
Figure 211: Client - Broker - SPS - Server (Transparent mode)
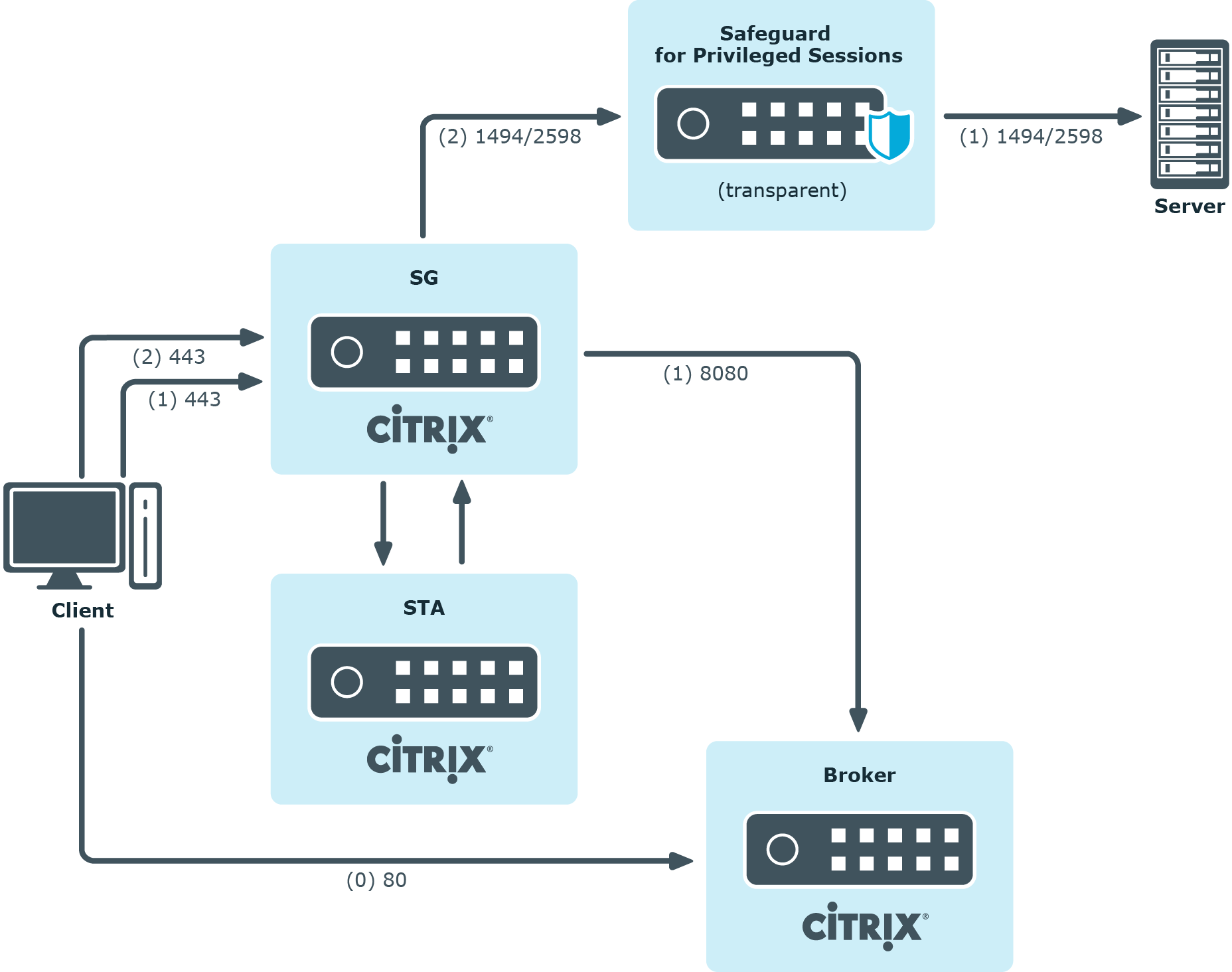
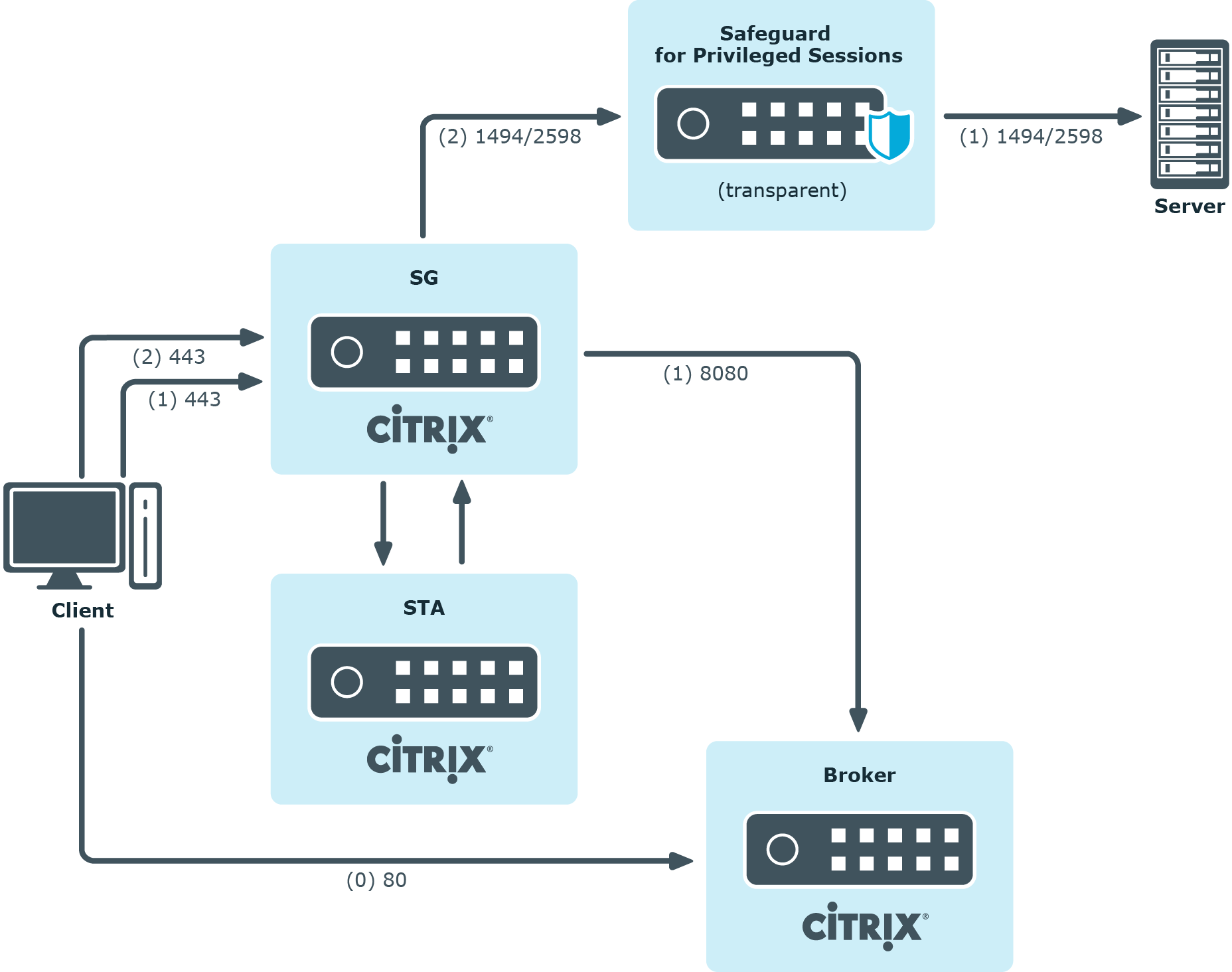
Client - Broker - original secure gateway - Secure Ticket Authority (STA) - SPS - Server
In this setup, a secure gateway is used in the network and the SPS is placed between this gateway and the servers in transparent mode. The clients connect to the broker for the list of available applications/servers and then make their further connections through the original secure gateway. That gateway forwards the connections either to the broker or to the CGP/ICA servers, which latter the SPS intercepts and audits/controls.
Figure 212: Client - Broker - original secure gateway - Secure Ticket Authority (STA) - SPS - Server
Client - Broker - SPS as socks proxy - Server
In this setup, the SPS acts as a SOCKS proxy for the client. It can be set either manually or specified by the broker. The client then makes all its connections to the broker or to the server using SPS as a proxy and hence it can audit/control these connections.
Figure 213: Client - Broker - SPS as socks proxy - Server
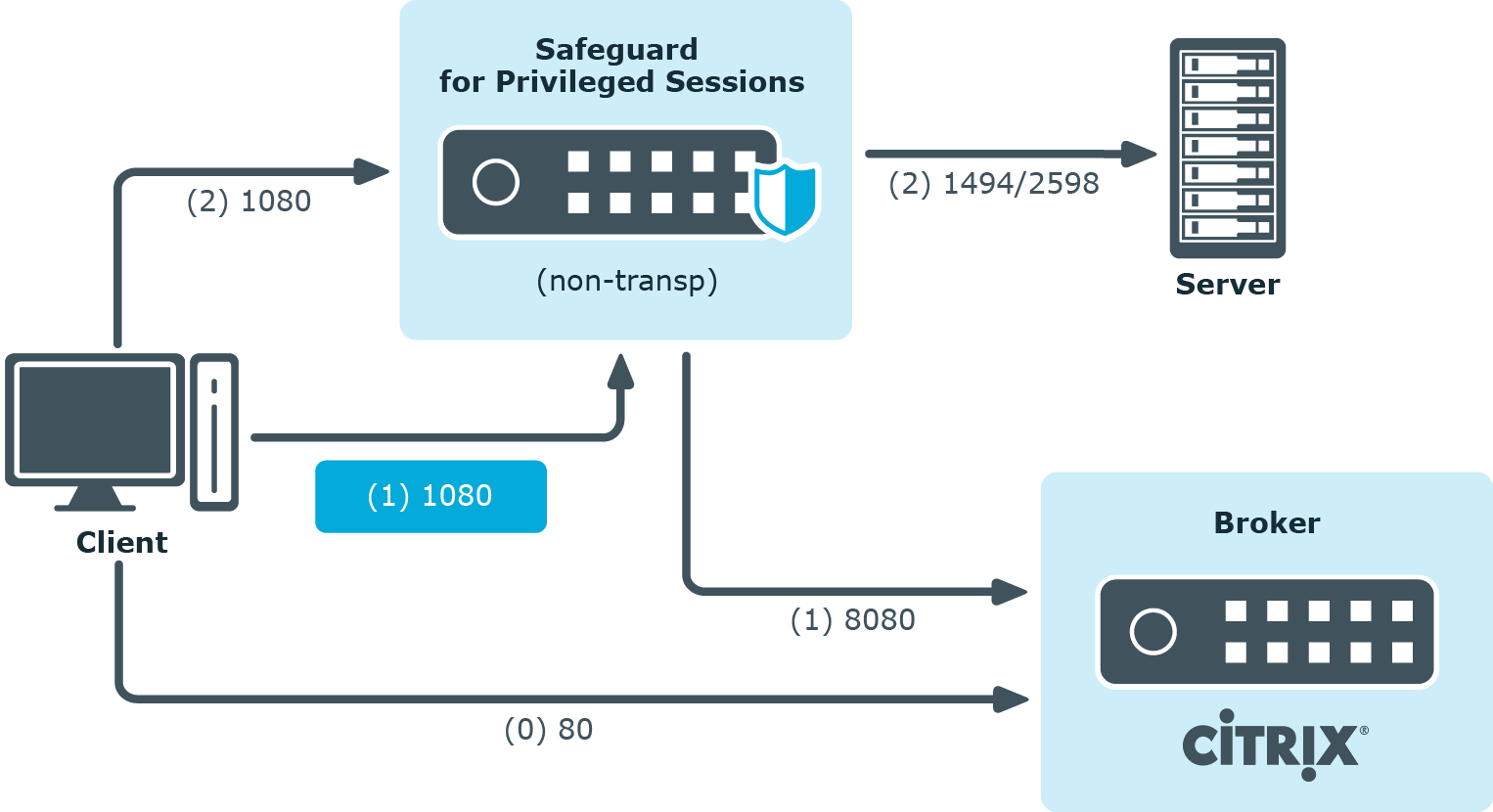
To configure such a scenario, you must set the ICA Connection Policy as follows:
-
Enter the IP address of SPS into the To field. This must be the public IP address that the clients will target.
-
Select Inband destination selection, and list the IP addresses or networks of target servers in the Targets field. (For details, see Configuring inband destination selection.)
-
Select Act as a SOCKS proxy.
-
Add the IP addresses of your brokers to the Brokers field.
Accessing Citrix servers using the Remote Desktop Protocol
Accessing Citrix servers using the Remote Desktop Protocol may fail in certain situations, and the connection is terminated with the ERROR: error while decompressing packet error message on the client, or with the Event56, TermDD, The Terminal Server security layer detected an error in the protocol stream and has disconnected the client. message on the server.
To overcome this problem, modify the settings of the network card of the server, and disable the Large Send Offload option.
NOTE: The problem is not related to using One Identity Safeguard for Privileged Sessions (SPS) in your environment.


 to create an ICA setting profile. Enter a name for the profile (for example ica_special).
to create an ICA setting profile. Enter a name for the profile (for example ica_special). to display the parameters of the ICA connection.
to display the parameters of the ICA connection. .
.