You can Unix-enable Active Directory user accounts. A Unix-enabled user has a Unix User Name, UID Number, Primary GID Number, Comment (GECOS), Home Directory, and Login Shell. These attributes enable an Active Directory user to appear as a standard Unix user. Safeguard Authentication Services provides several tools to help you manage Unix account information in Active Directory.
Managing Unix user accounts
Managing Unix users with MMC
You can access Active Directory Users and Computers (ADUC) from the Control Center. Navigate to the Tools | Safeguard Authentication Services Extensions for Active Directory Users and Computers.
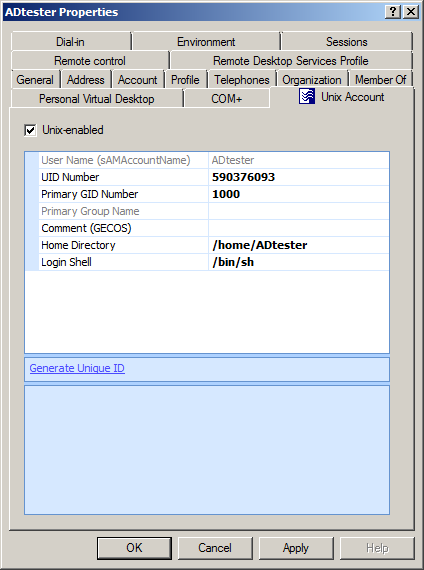
After installing Safeguard Authentication Services on Windows, a Unix Account tab appears in the Active Directory user's Properties dialog:
Note: If the Unix Account tab does not appear in the user's Properties dialog, review the installation steps outlined in the Safeguard Authentication Services Installation Guide to ensure that Safeguard Authentication Services was installed correctly. Refer to Unix Account tab is missing in ADUC for more information.
Select the Unix-enabled option to Unix-enable the user. Unix-enabled users can log in to Unix hosts joined to the domain. Selecting this option causes Safeguard Authentication Services to generate default values for each of the Unix attributes. You can alter the way default values are generated using Control Center.
| Unix attribute | Description |
|---|---|
| User Name | This is the Unix user name of the Windows account used to log in to a Unix host. |
| UID Number | Use this field to set the numeric Unix User ID (UID). This value must be unique in the forest. In some environments, users have a different UID number on each Unix host. In this case, you can use mapped user, local account overrides, or Ownership Alignment Tool (OAT) to ensure that the local Unix user is associated with the correct Windows user account and that local resources are still associated with the correct UID Number. |
| Primary Group ID | Use this field to set the Unix Primary Group ID. This field determines the group ownership of files that are created by the user. Click the Search button to search for Unix-enabled groups in Active Directory. This field defaults to 1000. You can modify the default in the Control Center | Preferences. |
| Primary Group Name | This read-only field displays the name of the group associated with the Primary Group ID. If the Primary Group ID is not associated with a Unix-enabled Active Directory group, then the field is blank. |
| Comment (GECOS) | Use this free-form field to store information that is found in the GECOS field in /etc/passwd. This information is typically used to record the user's full name and other information, such as phone number and office location. If this field contains a colon, the colon will be replaced by a _ on Unix. You can change the Comment (GECOS) default in the Control Center | Preferences. |
| Home Directory | Use this field to configure the user's Unix home directory. If the home directory does not exist when the user logs in to a machine for the first time, Safeguard Authentication Services creates it. The default value is /home/<User Name>. (/Users/<User Name> on macOS.) You can override the default home directory prefix in the Control Center | Preferences. |
| Login Shell | Use this field to configure the shell that is executed when the user logs in to Unix using a terminal-based login. If the specified shell does not exist, the user will not be allowed to log in. You can use a Symlink Policy to ensure that a particular shell path exists on all of your Unix hosts. This value defaults to /bin/sh. You can modify the default in the Control Center | Preferences. |
| Generate Unique ID | Click this link to generate a unique User ID number. If the ID is already unique, it will not be modified. By default you cannot save a non-unique ID number. You can modify this setting in the Control Center | Preferences. |
| Clear Unix Attributes | If a user is not Unix-enabled, you can click this link to clear all of the Unix attribute values. |
Managing user accounts from the Unix command line
Note: In the following examples, it is assumed that you have already logged in with a user that has sufficient permissions in Active Directory to perform the intended command. See Permissions matrix. If your present account is lacking necessary permissions, you may use either of the following methods to perform the desired administrative command:
- Use vastool kinit <elevated-permission-user> to obtain elevated permissions. For example, execute vastool kinit admin-user, and then perform the command as outlined in the examples.
-OR-
- Use vastool -u <elevated-permission-user>. For example, vastool create user test-account becomes vastool -u admin-user create user test-account.
You can use the vastool command from the command line to create and delete users, as well as list user information.
To create a user, use the vastool create command. The following command creates a non-Unix-enabled user, bsmith, in Active Directory:
vastool create bsmith
To create a user that has its Unix account enabled, pass in an /etc/passwd formatted string using the -i option, as follows:
vastool create -i "bsmith:x:1003:1000:Bob:/home/bsmith:/bin/bash" bsmith
By default, all users created with vastool create are created in the Users container. To create a user in a different organizational unit, use the -c command line option.
The following command creates a Unix-enabled user, bsmith, in the OU=sales,DC=example,DC=com organizational unit:
vastool create -i \ "bsmith:x:1003:1000:Bob:/home/bsmith:/bin/bash" \ -c "OU=sales,DC=example,DC=com" bsmith
To delete a user, use vastool delete. The following command deletes the bsmith user:
vastool delete bsmith
To list users, use vastool list users. The vastool list users command returns information from the local account cache. The following command lists all the users with Unix accounts enabled:
vastool list users
This command produces output similar to the following:
pspencer:VAS:1000:1000:Pat Spencer:/home/pspencer:/bin/bash djones:VAS:1001:1000:Dave Jones:/home/djones:/bin/bash molsen:VAS:1002:1000:Mary Olsen:/home/molsen/bin/bash bsmith:VAS:1003:1000:Bob Smith:/home/bsmith:/bin/bash
Managing users with Windows PowerShell
Safeguard Authentication Services includes PowerShell modules that provide a "scriptable" interface to many Safeguard Authentication Services management tasks.
Using Safeguard Authentication Services PowerShell commands you can Unix-enable, Unix-disable, modify, report on, and clear Unix attributes of Active Directory users.
Note: You can access a customized PowerShell console from Control Center | Tools. To add Safeguard Authentication Services cmdlets to an existing PowerShell session, run Import-Module Quest.AuthenticationServices. See PowerShell Cmdlets for a complete list of available commands.
To Unix-enable a user, use the Enable-QasUnixUser command. The following command Unix-enables the user, bsmith, in Active Directory:
Enable-QasUnixUser -Identity <domain>\bsmith
To disable a user for Unix access use the Disable-QasUnixUser command:
Disable-QasUnixUser -Identity <domain>\bsmith
To set a particular Unix attribute use the Set-QasUnixUser command. The following command sets the Comment (GECOS) field of the bsmith user to Bob Smith:
Set-QasUnixUser -Identity <domain>\bsmith -Gecos "Bob Smith"
To report on a user, use the Get-QASUnixUser command. The following command shows all users that start with "bsm".
Get-QasUnixUser -Identity bsm
The Safeguard Authentication Services PowerShell commands are designed to work with the Active Directory commands from Microsoft (Get-ADUser) and One Identity (Get-QADUser). You can pipe the output of these commands to any of the Safeguard Authentication Services PowerShell commands that operate on users. For example, the following command clears the Unix attributes from the bsmith user.
Get-QADUser -Identity <domain>\bsmith | Clear-QasUnixUser
The Safeguard Authentication Services PowerShell commands are aware of the options and schema settings configured in Control Center. Scripts written using the Safeguard Authentication Services PowerShell commands work without modification in any Safeguard Authentication Services environment.
