Encrypting audit trails
To prevent unauthorized access to the audit trail files, One Identity Safeguard for Privileged Sessions (SPS) can encrypt:
-
The entire trail.
-
The entire trail, and the upstream part with an additional (set of) certificate(s).
-
Only the upstream part.
With upstream encryption, the passwords are visible only with the private key of the certificate used for encrypting the upstream traffic.
|
|
NOTE:
Even if the upstream traffic is encrypted with a separate certificate, only one audit trail file is created for a session. |
|
|
Caution:
One Identity Safeguard for Privileged Sessions (SPS) 5 F4 and later versions use a new encryption algorithm to encrypt the recorded audit trails (AES128-GCM). This change has the following effects:
|
Encrypting the upstream part has the following limitations:
-
During indexing, command detection does not work without the upstream encryption keys.
|
|
TIP:
For more information on uploading certificates for indexing and replaying audit trails, see:
|
Encrypting audit trails requires one or more X.509 certificate in PEM format that uses an RSA key, depending on the configuration.
|
|
NOTE:
Certificates are used as a container and delivery mechanism. For encryption and decryption, only the keys are used. |
One Identity recommends using 2048-bit RSA keys (or stronger).
Use every keypair or certificate only for one purpose. Do not reuse cryptographic keys or certificates (for example, do not use the certificate of the One Identity Safeguard for Privileged Sessions (SPS) webserver to encrypt audit trails, or the same keypair for signing and encrypting data).
The following encryption options are available:
-
Encrypt with a single certificate. This is the most simple approach: SPS uses one certificate to encrypt the audit trails, and anyone who has the private key of that certificate can replay the audit trails. If that key is lost, there is no way to open the audit trails.
-
Encrypt separately with multiple certificates. SPS uses two or more certificates separately to encrypt the audit trails, and anyone who has the private key of one of the encryption certificates can replay the audit trails.
-
Encrypt jointly with two certificates. SPS uses two certificates together (a certificate-pair) to encrypt the audit trails. The private keys of both encryption certificates are needed to replay the audit trails. This is a kind of "four-eyes in auditing".
You can combine the different encryption methods. For example, you can encrypt the audit trails with multiple certificate-pairs, and replay the trails only if the private keys of a certificate-pair are available. This is true for encrypting the upstream traffic as well. At the extreme, you will need four private keys to fully replay an audit trail: two to open the normal traffic, and two more to display the upstream traffic.
Note that SPS itself cannot create the certificates used to encrypt the audit trails.
|
|
TIP:
If two certificates are displayed in a row, they are a certificate-pair and you need the private key of both to replay the audit trails. If two certificates are displayed in separate rows, you need the one of the private keys to replay the audit trails. If there are multiple rows containing two certificates, you need the private keys of the certificate(s) listed in any of the rows. |
Figure 150: Policies > Audit Policies — Encrypting audit trails: joint encryption with a certificate pair
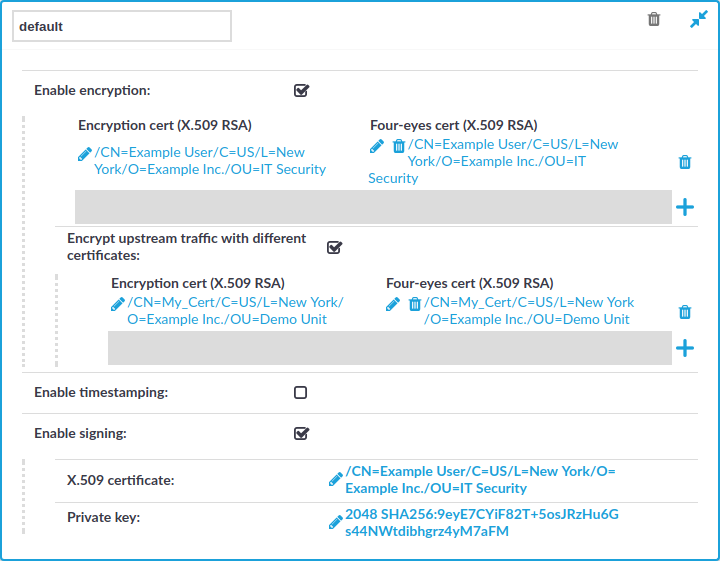
Each audit policy can have up to 8 lines of certificate pairs.
To encrypt audit trails
-
Navigate to Policies > Audit Policies and select the audit policy you will use in your connections.
TIP: By default, every connection uses the built-in default audit policy. Unless you use a custom audit policy, modifying the default audit policy will affect every audited channel of the connections passing through One Identity Safeguard for Privileged Sessions (SPS).
-
Select the Enable encryption option.
-
To upload a certificate for encrypting the entire trail:
-
Click the
icon under the Encryption cert (X.509 RSA) 4-eyes cert (X.509 RSA) row.
-
Click on the left
icon and upload a certificate to SPS. This certificate will be used to encrypt the audit trails, and it must not include the private key.
NOTE: To replay the audit trails, you need the private key of the certificate on the computer running the Safeguard Desktop Player application.
-
(Optional) To encrypt the audit trails jointly with another certificate, click on the right
icon and upload a certificate to SPS. Note that the private key of both certificates will be required to replay the audit trails.
-
Repeat these steps to encrypt the audit trails separately with additional certificates.
-
-
To upload a certificate for encrypting the upstream traffic:
-
Select Encrypt upstream traffic with different certificates.
-
Click the
icon under the Encryption cert (X.509 RSA) 4-eyes cert (X.509 RSA) row.
-
Click on the left
icon and upload a certificate to SPS. This certificate will be used to encrypt the audit trails, and it must not include the private key.
NOTE: To replay the upstream part of the audit trails, you need the private key of the certificate on the computer running the Safeguard Desktop Player application.
-
(Optional) To encrypt the audit trails jointly with another certificate, click on the right
icon and upload a certificate to SPS. Note that the private key of both certificates will be required to replay the audit trails.
-
Repeat these steps to encrypt the upstream separately with additional certificates.
-
-
Click
.


