Client-side authentication settings
For the client-side connection, One Identity Safeguard for Privileged Sessions (SPS) can authenticate the client inband (within the SSH protocol) using the following authentication methods:
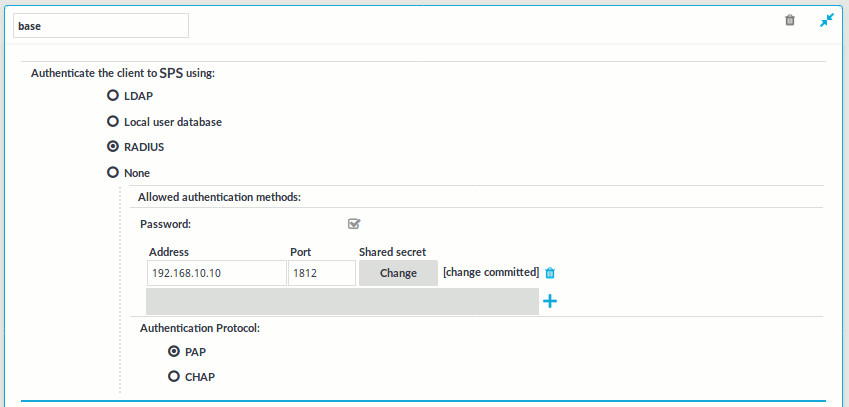
Figure 192: SSH Control > Authentication Policies — Configuring client-side authentication methods
-
LDAP: SPS will authenticate the client to the LDAP database set in the LDAP Server of the connection policy. To use LDAP authentication on the client side, select Authenticate the client to SPS using > LDAP, and select the permitted authentication methods (Password, Public key). More than one method can be permitted.
NOTE: -
SPS will authenticate the client-side connection to the LDAP server configured in the connection policy. This is not necessarily the same as the LDAP server used to authenticate the users accessing the SPS web interface.
-
The public keys of the users stored in the LDAP database must be in OpenSSH format.
-
-
Local user database: Authenticate the client locally on the SPS gateway. For details, see Local client-side authentication.
-
RADIUS: SPS will authenticate the client to the specified RADIUS server. Select Authenticate the client to SPS using > RADIUS, enter the IP address or hostname of the RADIUS server into the Address field, the port number of the RADIUS server into the Port field, and the shared secret of the RADIUS server into the Shared secret field. Only password-authentication is supported (including one-time passwords), challenge-response based authentication is not.
To use the Password Authentication Protocol, select PAP. To use the Challenge-Handshake Authentication Protocol, select CHAP.
Use an IPv4 address.
To add more RADIUS servers, click
and fill in the respective fields.
-
None: Do not perform client-side authentication, the client will authenticate only on the target server.
Caution: Hazard of security breach. If the None authentication option is selected on the client side and SPS is configured to use public-key or certificate based authentication on the server, the user will not be authenticated at all unless gateway authentication is required for the connection.
To use certificates to authenticate the client, you can use the LDAP and the Local user database backends.
Figure 193: Client-side inband gateway authentication with different certificates
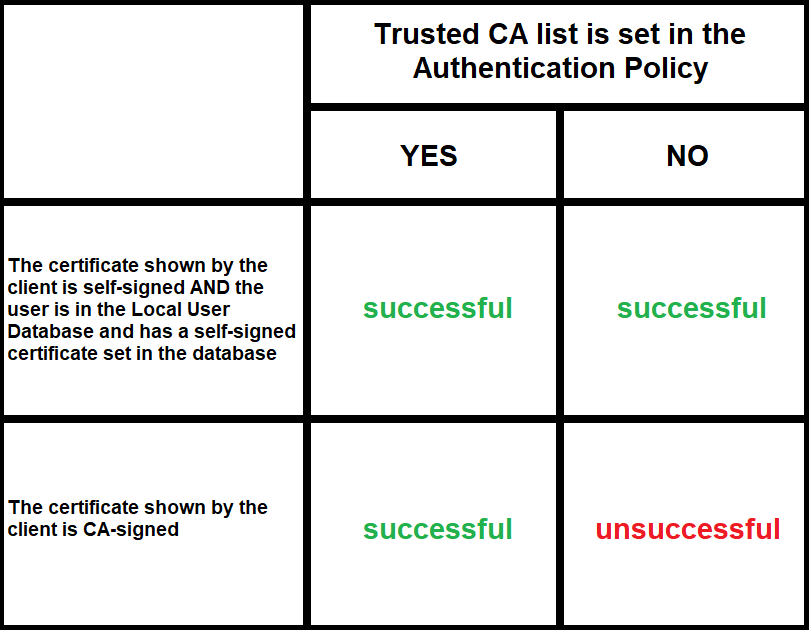
| Trusted CA list is set in the Authentication Policy | ||
|---|---|---|
| YES | NO | |
| The certificate shown by the client is self-signed AND the user is in the Local User Database and has a self-signed certificate set in the database | successful | successful |
| The certificate shown by the client is CA-signed | successful | unsuccessful |


