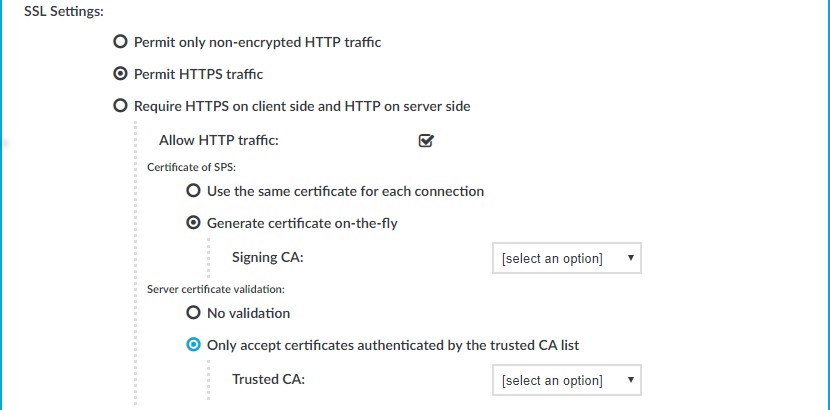
This setting either enforces TLS encryption or accepts both HTTP and HTTPS requests.
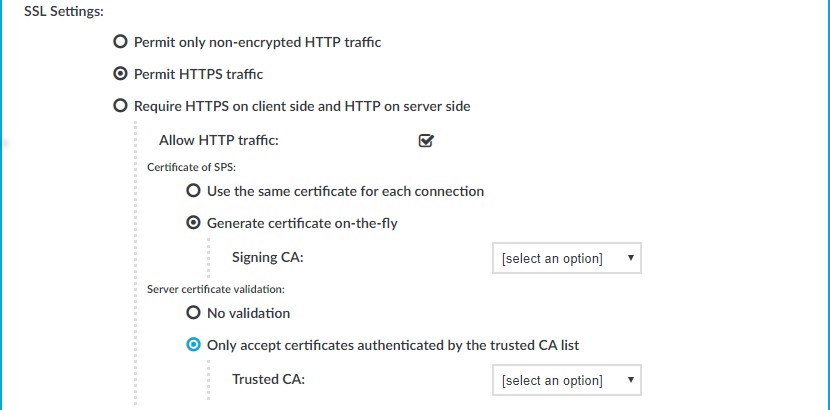
Figure 199: HTTP Control > Connections> SSL Settings — Enabling SSL encryption in HTTP
To enable SSL encryption
-
In SSL Settings, select Permit HTTPS traffic. To control plain HTTP traffic with the same connection policy, enable Allow HTTP traffic.
-
Select the certificate to show to the clients.
NOTE: When using the Use the same certificate for each connection option and the connection policy that allows access to multiple servers using HTTPS, the client browsers will display a warning because the certificate used in the connection will be invalid (namely, the Common Name of the certificate will not match the hostname or IP address of the server).
Limitations
NOTE: When Generate certificate on-the-fly is selected and the connection is in transparent setup, the CN field is filled in using Server Name Indication (SNI). If the client does not support SNI, the CN field will contain the target IP, which may cause certificate verification warning on the client browser.
NOTE: Import the certificate of the signing Certificate Authority to your clients. Otherwise, the client browsers will display a warning due to the unknown Certificate Authority.
-
Select how SPS should authenticate the server.
-
To permit connections to servers without requesting a certificate, select No validation.
-
To permit connections only to servers with a valid certificate that was signed by a specific CA, complete the following steps.
-
Create a list of trusted Certificate Authorities that will be used to validate the certificates of the servers. For details on creating a trusted CA list, see Verifying certificates with Certificate Authorities.
-
Select Only accept certificates authenticated by the trusted CA list.
-
In the Trusted CA field, select the certificate authority list to use.
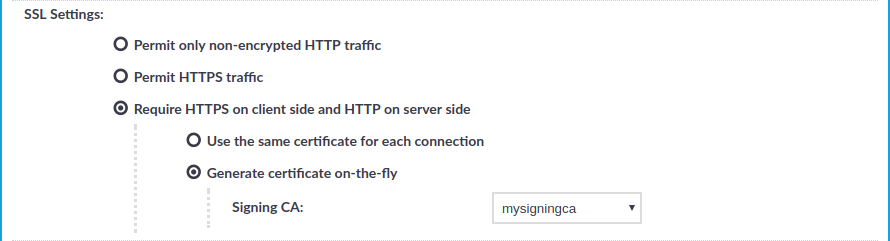
The following steps describe how to enable half-sided SSL encryption (which requires HTTPS on client side, and HTTP on server side).
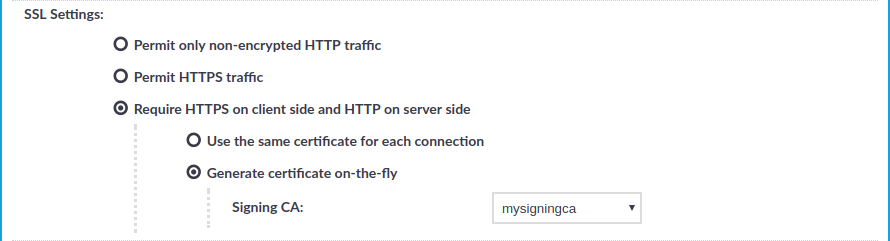
Figure 200: HTTP Control > Connections > SSL Settings — Enabling half-sided TLS encryption in HTTP
To enable half-sided TLS encryption, require HTTPS on client side, and HTTP on server side
-
In SSL Settings, select Require HTTPS on client side and HTTP on server side.
NOTE: If the connection is configured at Target to Use fixed address and the port number is set to 443, One Identity Safeguard for Privileged Sessions (SPS) will still automatically use port 80 to connect to the server, when Require HTTPS on client side and HTTP on server side is selected.
-
Select the certificate to show to the clients.
-
To use the same certificate for every peer, complete the following steps.
-
Generate and sign a certificate for SPS in your PKI system, and export the certificate and its private key.
-
Select Use the same certificate for each connection.
-
Select Private key for host certificate, click  and upload the private key.
and upload the private key.
-
Select X.509 host certificate, click  and upload the certificate.
and upload the certificate.
NOTE: When using the Use the same certificate for each connection option and the connection policy that allows access to multiple servers using HTTPS, the client browsers will display a warning because the certificate used in the connection will be invalid (namely, the Common Name of the certificate will not match the hostname or IP address of the server).
-
To use a separate certificate for every connection, complete the following steps.
-
Create a certificate authority that will be used to sign the certificates that SPS shows to the peer. For details, see Signing certificates on-the-fly.
-
Select Generate certificate on-the-fly.
-
Select the certificate authority to use in the Signing CA field.
Limitations
NOTE: When Generate certificate on-the-fly is selected and the connection is in transparent setup, the CN field is filled in using Server Name Indication (SNI). If the client does not support SNI, the CN field will contain the target IP, which may cause certificate verification warning on the client browser.
NOTE: Import the certificate of the signing Certificate Authority to your clients. Otherwise, the client browsers will display a warning due to the unknown Certificate Authority.
Communication over HTTP consists of client requests and server responses (also called exchanges). Unlike in other protocols, for example SSH, these request-response pairs do not form a well-defined, continuous connection. Therefore, One Identity Safeguard for Privileged Sessions (SPS) assumes that an HTTP request-response pair belongs to a specific session if the following points are true:
-
The IP address of the client is the same
-
The hostname of the target server (not the IP address) is the same
-
The username is the same (if the user has performed inband authentication)
-
The time elapsed since the last request-response pair between the same client and server is less then the session timeout value (15 minutes by default).
-
The first session cookie SPS finds within the request is the same. Note that the cookie must be listed in the Session Cookie Settings option. For details, see Creating and editing protocol-level HTTP settings.
SPS creates a separate audit trail and records the accessed URLs for every session. These are displayed on the Search page. If any of the columns is not visible, click Customize columns....
For technical reasons, in authenticated sessions the login page where the user provides the credentials is not part of the session associated with the username. This means that even if the login page is the first that the user visits, SPS will record two sessions: the first does not include a username, the second one does. These two sessions are visible on the Active Connections page (until the unauthenticated session times out).
This section describes the HTTP settings that determine the parameters of the connection on the protocol level, including timeout value, session cookies, and TLS settings.
|

|
Caution:
Modifying timeout settings is recommended only for advanced users. Do not modify these settings unless you exactly know what you are doing. |
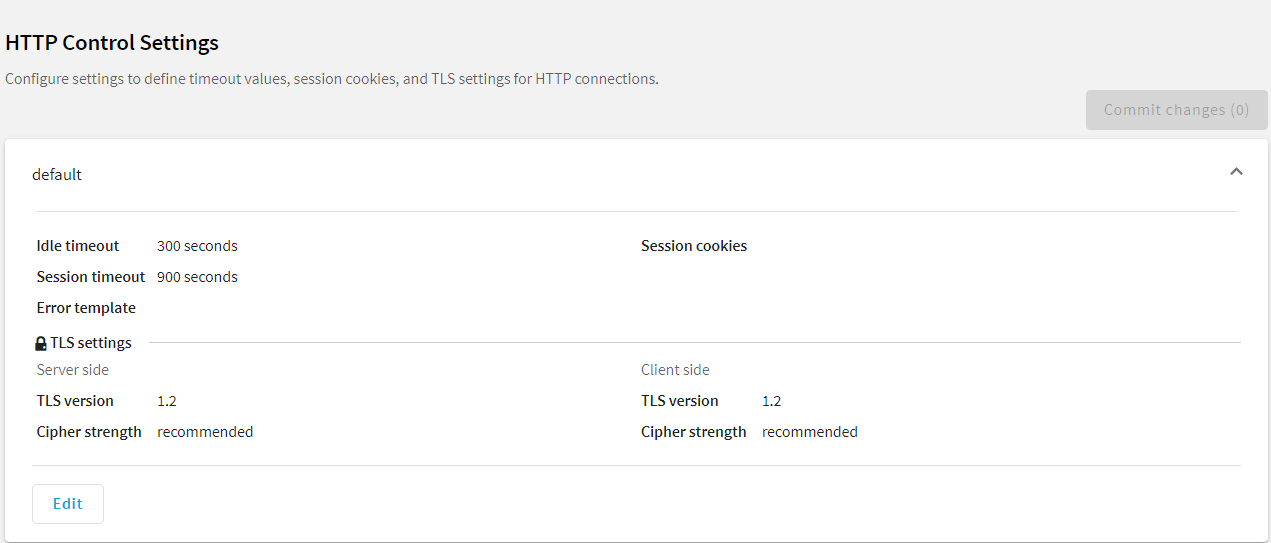
To create a new HTTP setting profile or edit an existing one
-
Navigate to the Settings tab of the HTTP Control menu item.
-
Click  to display the parameters of a profile.
to display the parameters of a profile.
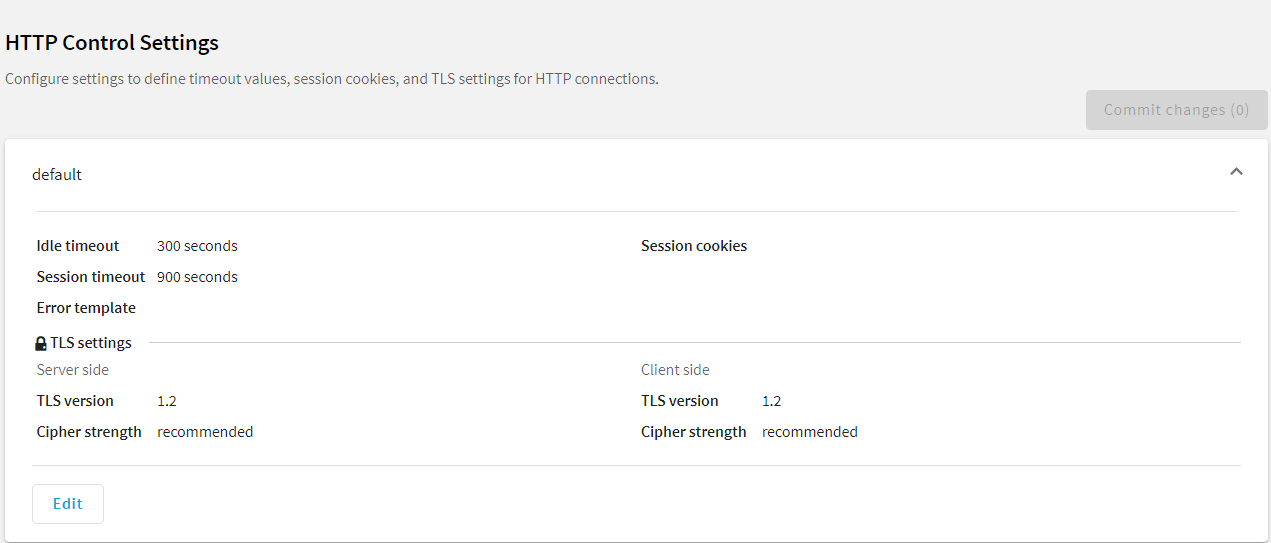
Figure 201: HTTP Control > Settings — Creating and editing protocol-level HTTP settings
-
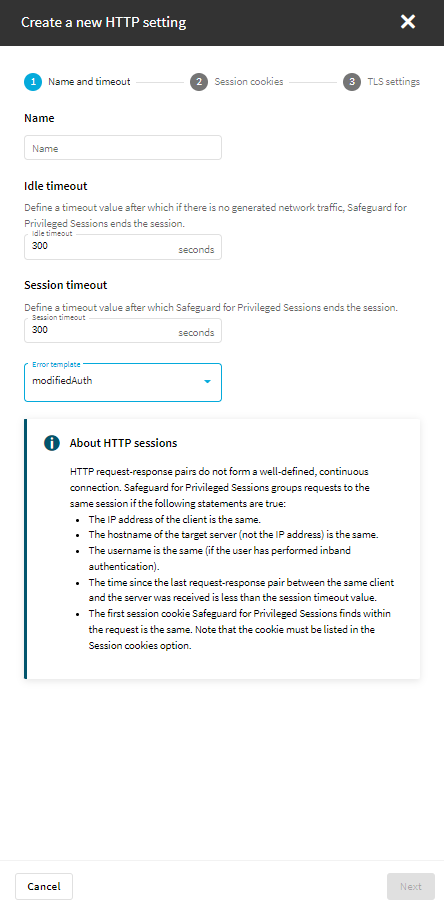
To create a new HTTP setting, click Create new.
-
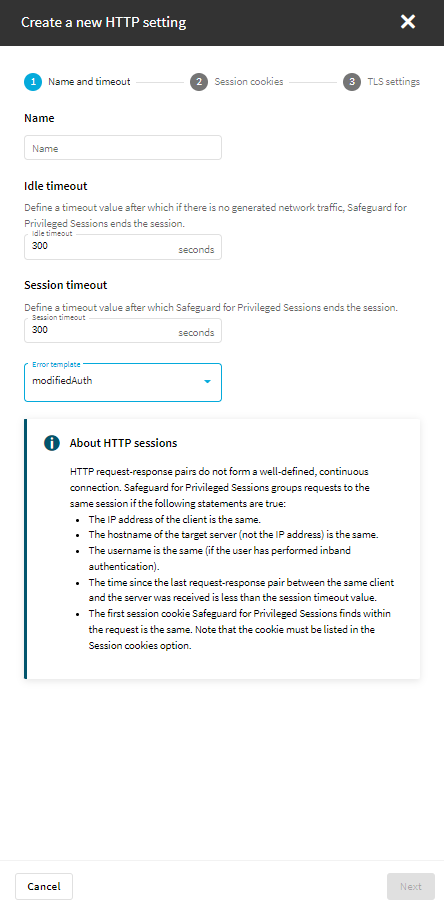
On Name and timeout, enter a name for the new profile and configure the timeout values. The following parameters are available:
-
Name: This is a required field. The name must be unique, and the accepted characters are the letters of the English alphabet (A-Z, and a-z) and the underscore (_) character.
-
Idle timeout: This is a required field. Timeout value for the session in seconds. The accepted values are positive integers. To avoid early timeout, set it to a larger value, for example a week (604800 seconds).
|

|
Caution:
Determining if a connection is idle is based on the network traffic generated by the connection, not the activity of the user. For example, if an application or the taskbar of a graphical desktop displays the time which is updated every minute, it generates network traffic every minute, negating the effects of timeout values greater than one minute and preventing One Identity Safeguard for Privileged Sessions (SPS) from closing the connection. |
-
Session timeout: This is a required field. Timeout value for the session in seconds. The accepted values are positive integers.
-
Error template: Use the error templates to send customized HTTP error messages to the users. The error templates, created on HTTP Control > Error templates, contain the following data:
For more information, see Customizing HTTP error templates.
Figure 202: HTTP Control > Settings > Create a new HTTP setting - Name and timeout
-
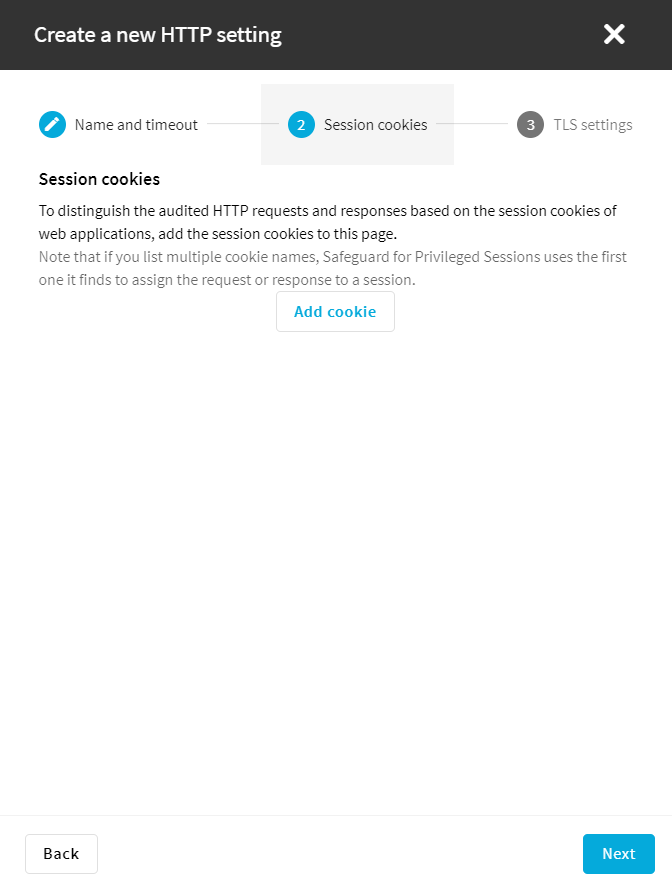
Proceed to Session cookies.
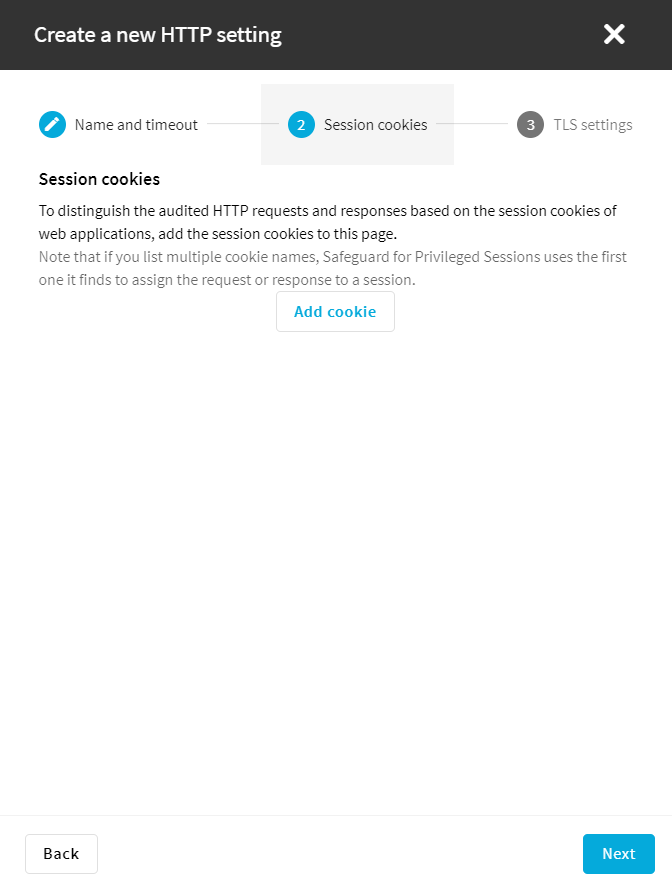
To distinguish the audited HTTP requests and responses based on the session cookies of web applications, click Add cookie, and enter the name of the session cookie, for example, PHPSESSID, JSESSIONID, or ASP.NET_SessionId. Note that the names of session cookies are case sensitive.
Repeat this step to add multiple cookie names. Note that if you list multiple cookie names, SPS will use the first one it finds to assign the requests to a session.
Figure 203: HTTP Control > Settings > Create a new HTTP setting - Session cookies
-
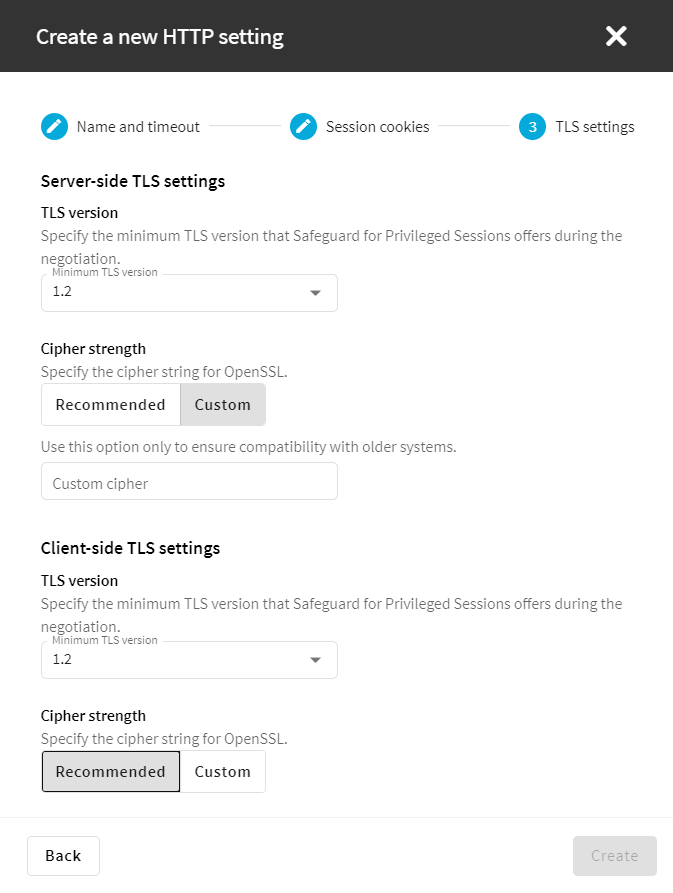
To configure TLS security settings on both the Client side and the Server side, proceed to TLS security settings.
Figure 204: HTTP Control > Settings > Create a new HTTP setting - TLS settings
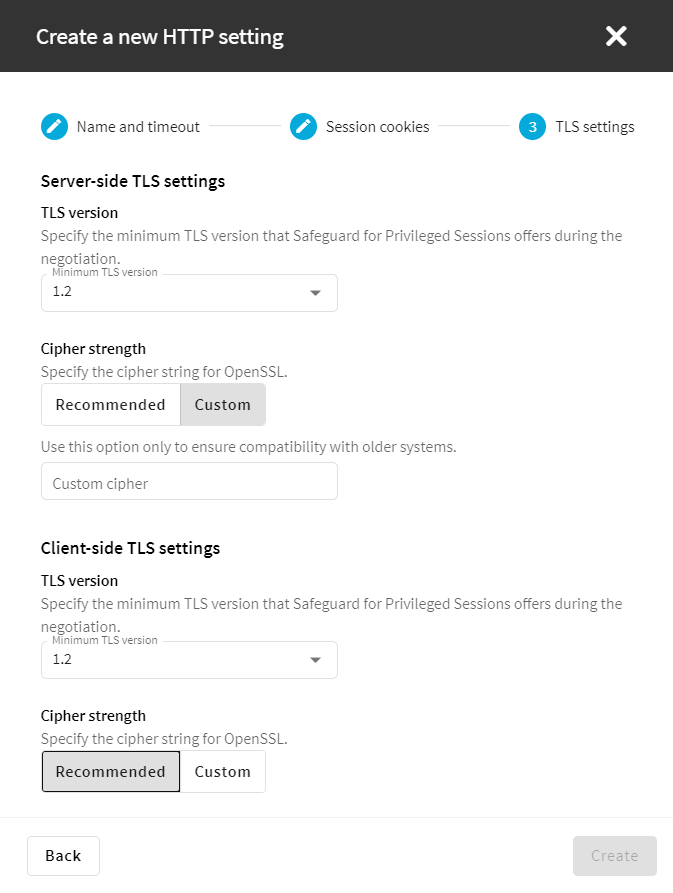
NOTE: Note that SPS only permits TLS-encrypted connections. SSLv3 is not supported.
-
Minimum TLS version specifies the minimum TLS version SPS offers during the negotiation. The following options are available:
-
TLS 1.2: this setting only offers TLS version 1.2 during the negotiation. This is the recommended setting.
-
TLS 1.1: this setting offers TLS version 1.1 and later versions during the negotiation.
-
TLS 1.0: this setting offers TLS version 1.0 and later versions during the negotiation.
-
Cipher strength specifies the cipher string for OpenSSL. The following options are available:
-
Recommended: this setting only uses ciphers with adequate security level.
-
Custom: this setting allows you to specify the list of ciphers you want to permit SPS to use in the connection. This setting is only recommended to ensure compatibility with older systems. For more details on customizing this list, check the 'openssl-ciphers' manual page on your SPS appliance.
For example: ALL:!aNULL:@STRENGTH
-
To create the new setting and to save it, click Create and after that, click Commit changes.
-
Select this profile in the HTTP settings field of your connections.
and upload the private key.
and upload the certificate.


 to display the parameters of a profile.
to display the parameters of a profile.