An authentication policy is a list of authentication methods that can be used in a connection. Connection definitions refer to an authentication policy to determine how the client can authenticate to the target server. Separate authentication methods can be used on the client and the server-side of the connection.
Figure 233: Authentication policies

Topics:
The following describes how to create a new authentication policy.
To create a new authentication policy
-
Navigate to Traffic Controls > SSH > Authentication Policies, and click  .
.
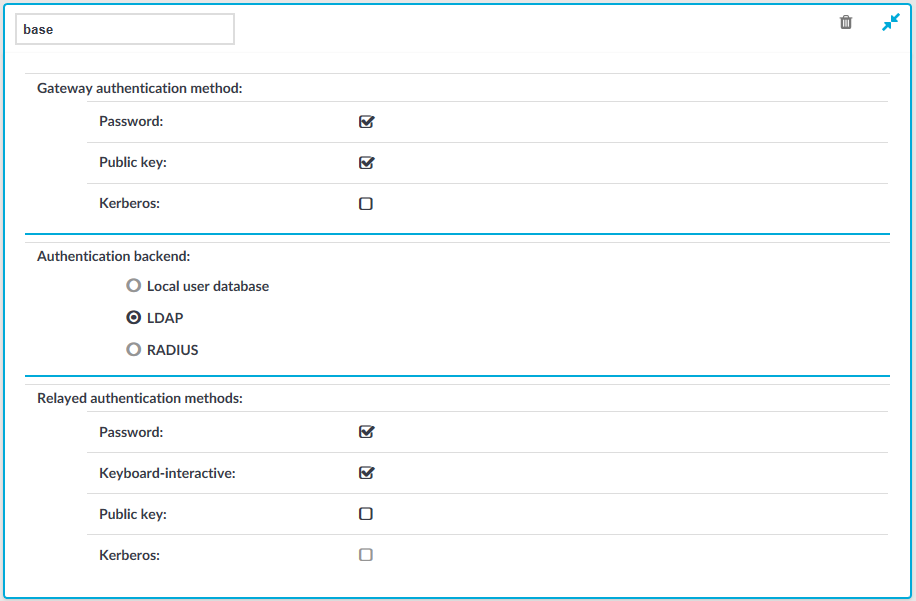
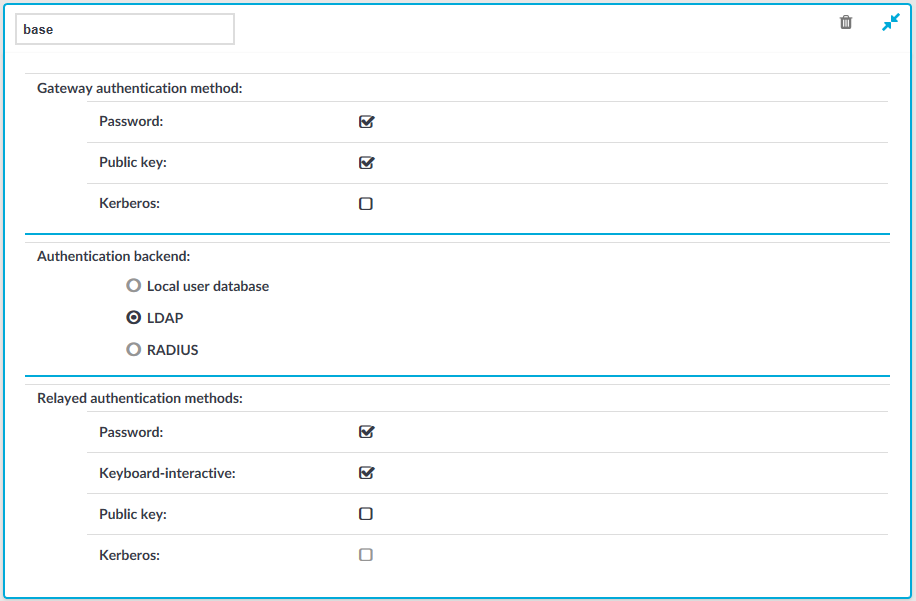
Figure 234: Traffic Controls > SSH > Authentication Policies — Configuring authentication policies
-
Enter a name for the policy.
-
Select the gateway authentication method to allow authentication on SPS. Note that this is an inband authentication that happens within the SSH protocol.
If you selected Kerberos as the gateway authentication method, SPS disables all other authentication backends and authentication methods.
-
Select the authentication database used on the client-side in the Authentication backend field. For details on the client-side authentication settings, see Client-side authentication settings.
If you selected Kerberos as the gateway authentication method, skip this step. For details, see Kerberos authentication settings.
-
Select the authentication method used on the server-side in the Relayed authentication methods field. For details on the relayed authentication settings, see Relayed authentication methods. Note the following:
-
If you selected Kerberos as the gateway authentication method, skip this step. For details, see Kerberos authentication settings.
-
If you selected Public key > Agent as the relayed authentication method:
If this option is used, SPS requests the client to use its SSH agent to authenticate on the target server. Therefore, you must configure your clients to enable agent forwarding, otherwise authentication will fail. For details on enabling agent forwarding in your SSH application, see the documentation of the application.
To be able to select Kerberos as the relayed authentication method, ensure that you also select Kerberos as the gateway authentication method.
-
Click  .
.
NOTE: Consider the following:
-
The client-side authentication settings apply for authenticating the user inband (that is, within the SSH protocol) to the One Identity Safeguard for Privileged Sessions (SPS) gateway, and is independent from the gateway authentication performed on the SPS web interface. The web-based gateway authentication is an out-of-band gateway authentication method that can be required by the connection policy. For details on out-of-band gateway authentication, see Configuring out-of-band gateway authentication.
Gateway authentication on the SPS web interface can be used together with authentication policies. In an extreme setting, this would mean that the user has to perform three authentications: a client-side gateway authentication within the SSH protocol to SPS, an out-of-band gateway authentication on the SPS web interface, and a final authentication on the target server.
-
The Connection Policy will ignore the settings for server-side authentication (set under Relayed authentication methods for SSH protocol) if a Credential Store is used in the Connection Policy.
For the client-side connection, One Identity Safeguard for Privileged Sessions (SPS) can authenticate the client inband (within the SSH protocol) using the following authentication methods:
Figure 235: Traffic Controls > SSH > Authentication Policies — Configuring client-side authentication methods
-
Local user database: Authenticate the client locally on the SPS gateway. For details, see Local client-side authentication.
-
LDAP: SPS will authenticate the client to the LDAP database set in the LDAP Server of the connection policy. To use LDAP authentication on the client side, select LDAP, and select the permitted authentication methods (Password, Public key). More than one method can be permitted.
NOTE:
-
SPS will authenticate the client-side connection to the LDAP server configured in the connection policy. This is not necessarily the same as the LDAP server used to authenticate the users accessing the SPS web interface.
-
The public keys of the users stored in the LDAP database must be in OpenSSH format.
-
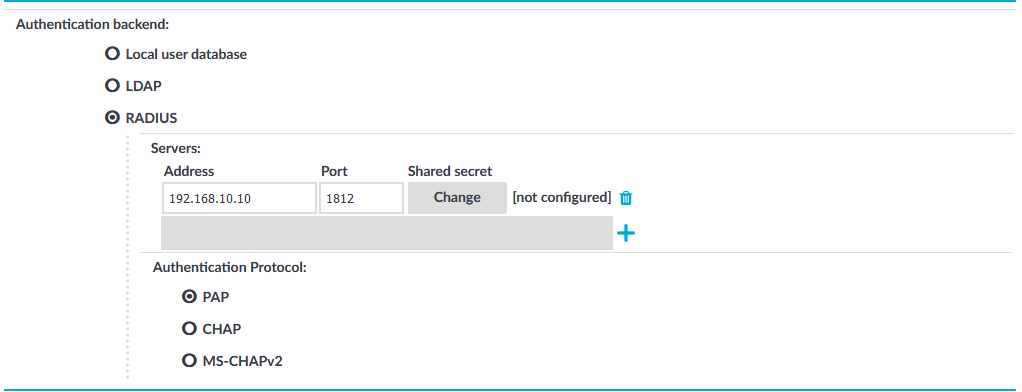
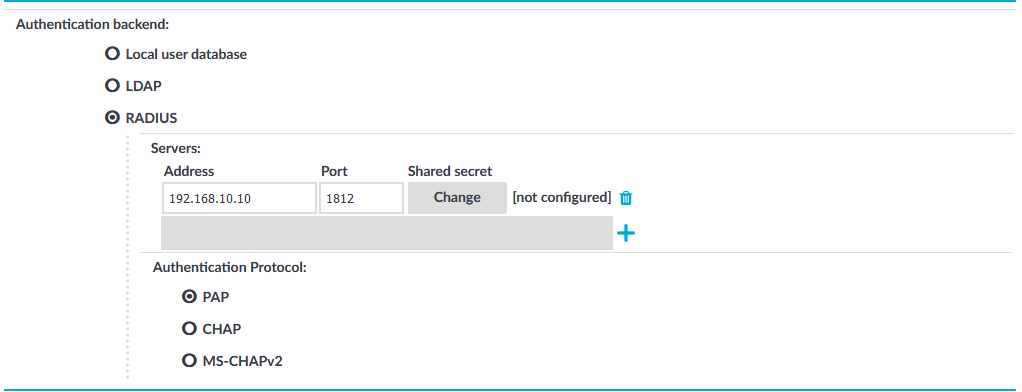
RADIUS: SPS will authenticate the client to the specified RADIUS server. Select RADIUS, enter the IP address or hostname of the RADIUS server into the Address field, the port number of the RADIUS server into the Port field, and the shared secret of the RADIUS server into the Shared secret field. Only password-authentication is supported (including one-time passwords), challenge-response based authentication is not.
To use the:
-
Password Authentication Protocol, select PAP.
-
Challenge-Handshake Authentication Protocol, select CHAP.
-
Microsoft version of the Challenge-Handshake Authentication Protocol, select MS-CHAPv2.
Use an IPv4 address.
To add more RADIUS servers, click  and fill in the respective fields.
and fill in the respective fields.
To use certificates to authenticate the client, you can use the LDAP and the Local user database backends.
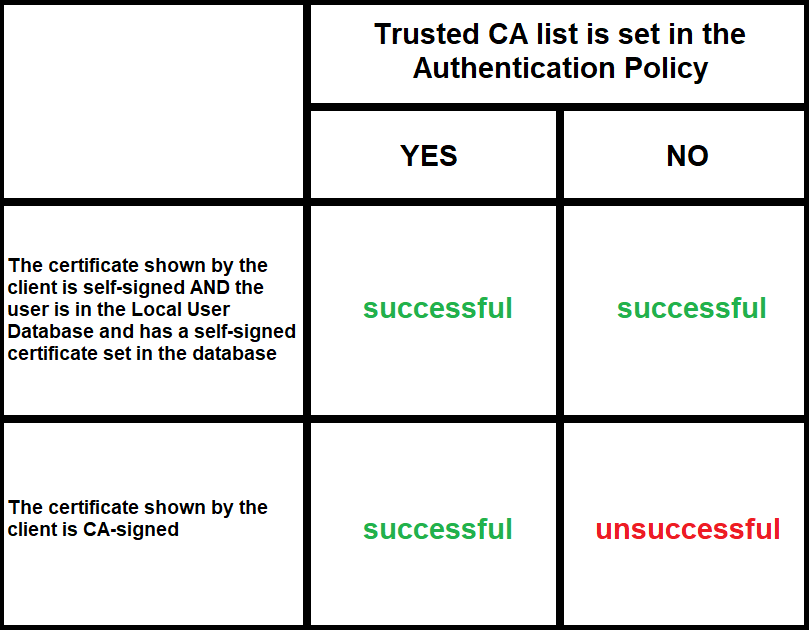
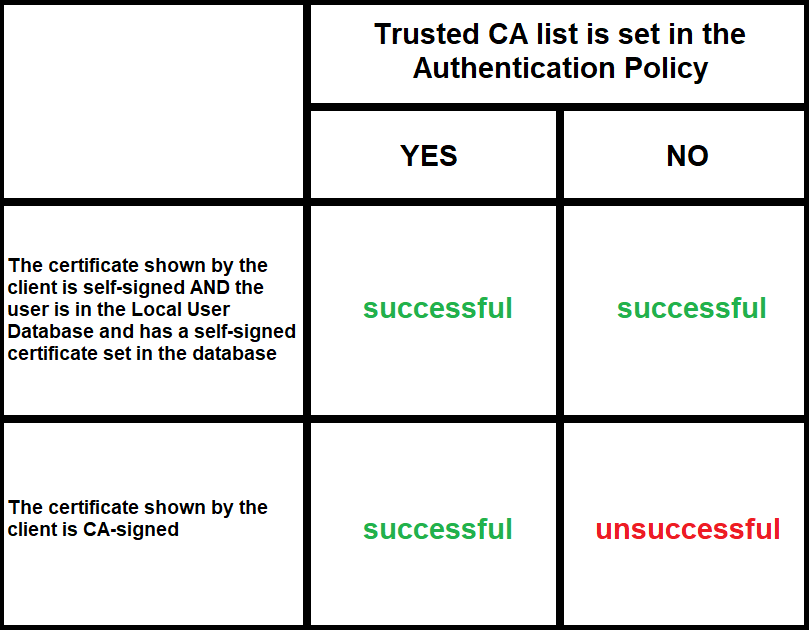
Figure 236: Client-side inband gateway authentication with different certificates
The following describes how to perform authentication locally on One Identity Safeguard for Privileged Sessions (SPS) for client-side connections.
NOTE: The users can be authenticated to their passwords or public-keys uploaded to SPS.
The accounts created to access the SPS web interface cannot be used to authenticate SSH connections.
Prerequisites
To perform authentication locally on SPS for client-side connections, an existing Local User Database is needed. To create a Local User Database, complete the following procedure: Creating a Local User Database.
To perform authentication locally on SPS for client-side connections
-
Navigate to Traffic Controls > SSH > Authentication Policies, and select the authentication policy to modify.
- Select the permitted authentication methods (Password, Public key).
-
Select Local user database.
-
Select the Local user database from the list that defines the users who can access the server.
-
Click  .
.


 .
.
 .
.