You can use the Active Roles Configuration Center to delete an Azure AD tenant. This is typically required when an Azure tenant and its directory objects become obsolete because of organizational reasons.
To remove an Azure AD tenant
-
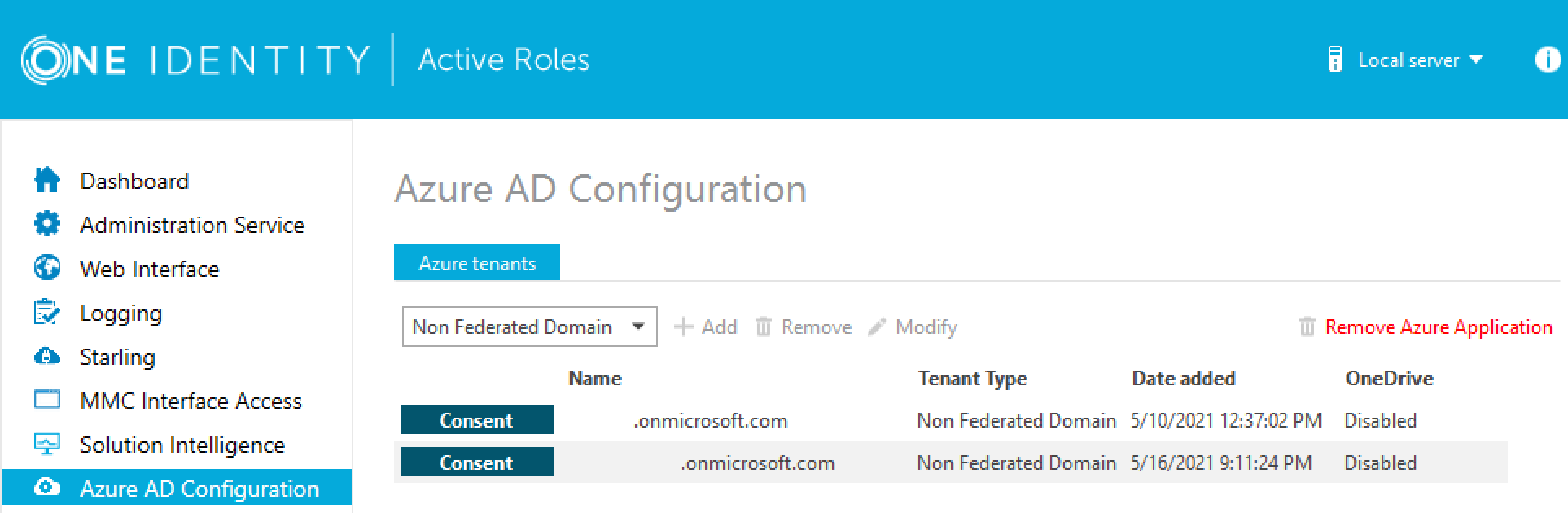
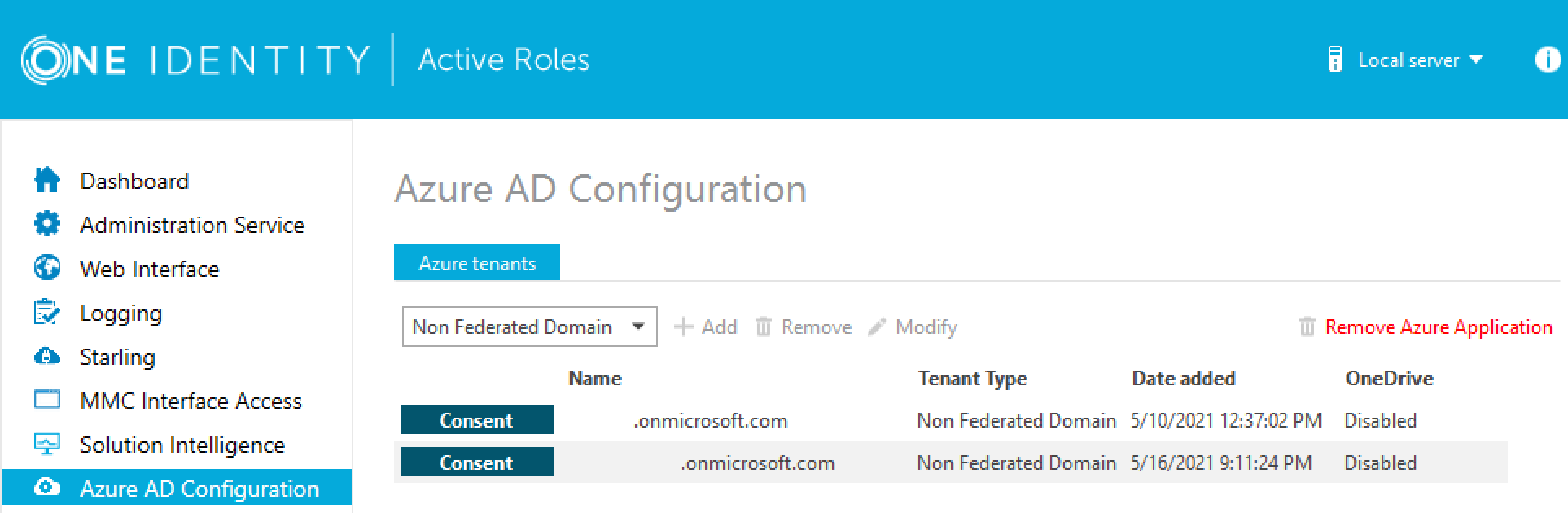
In the Active Roles Configuration Center, on the left pane, click Azure AD Configuration.
The list of existing Azure tenants appears.
-
On the Azure AD Configuration page, from the list of Azure tenants, select the tenant that you want to remove.
-
Click Remove.
-
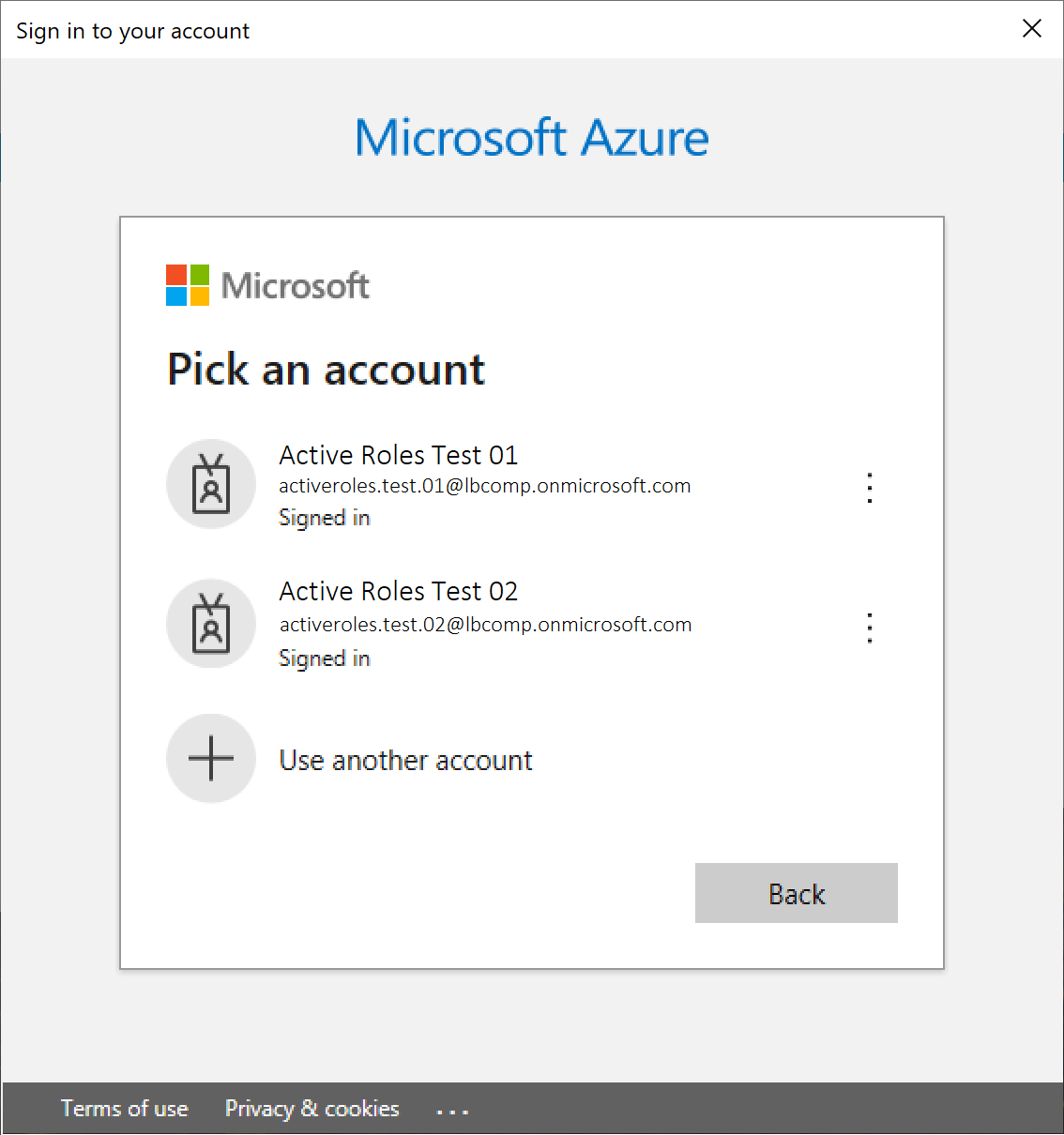
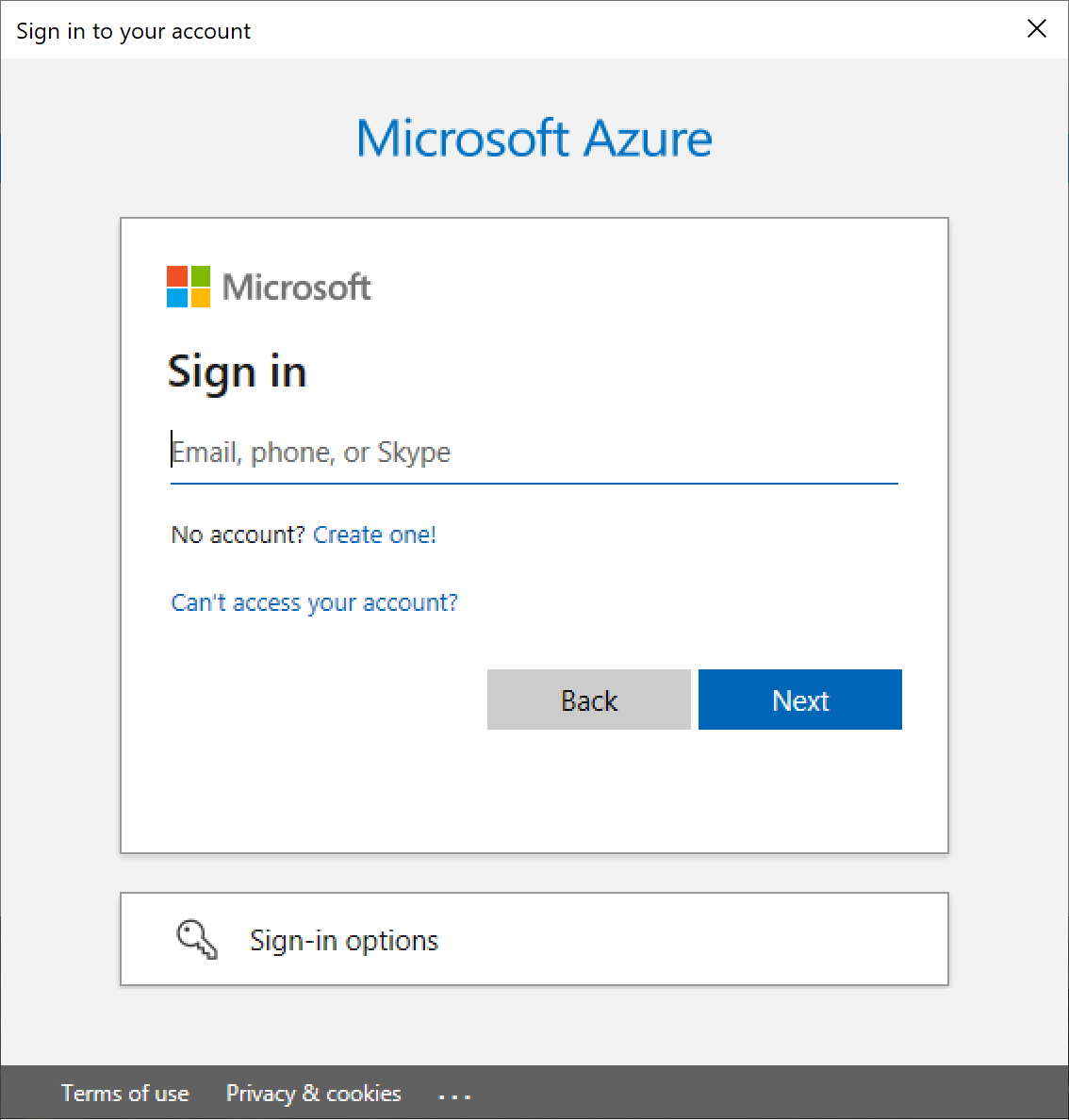
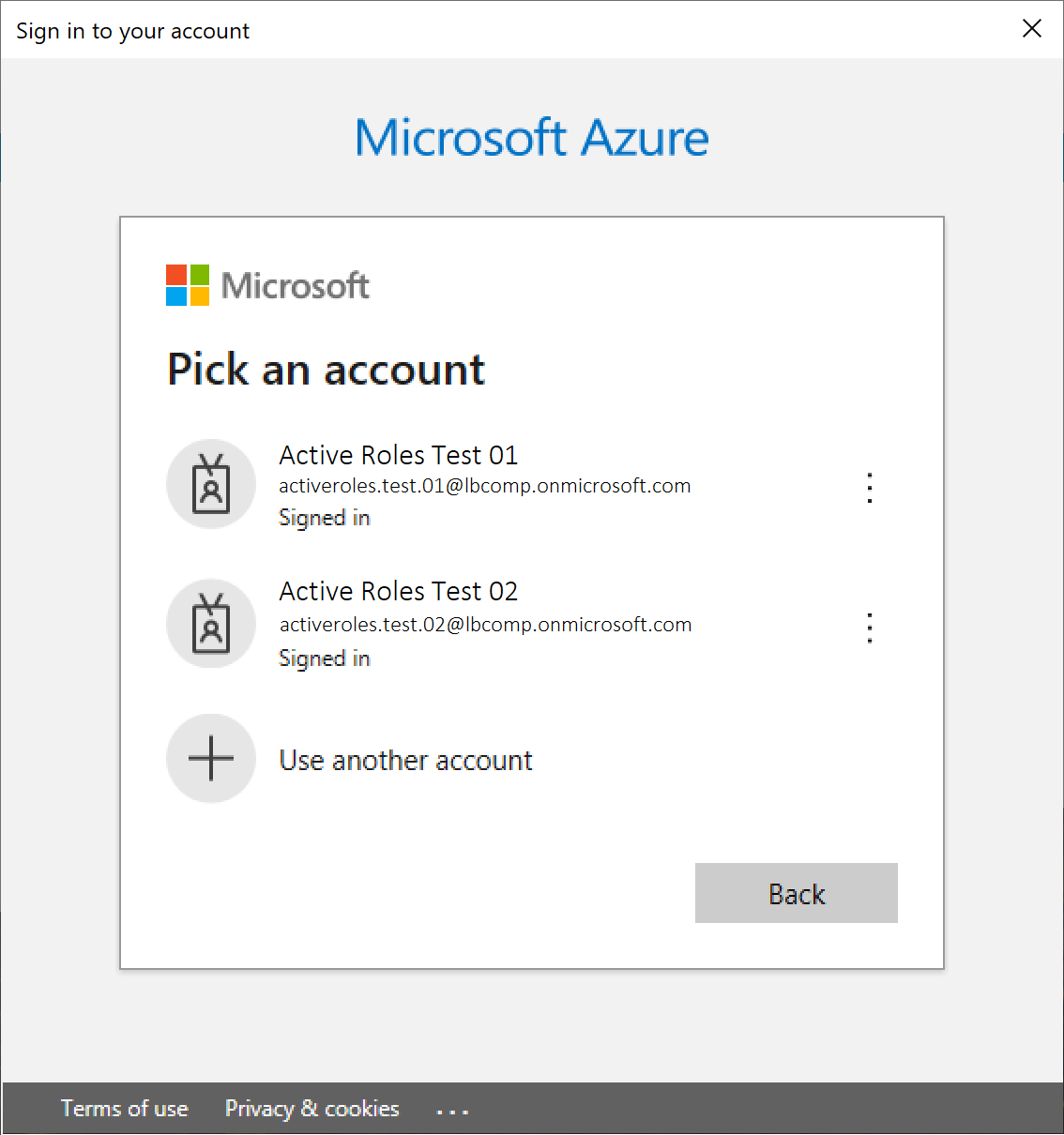
Authenticate your Azure AD administrator account.
-
If you already used one or more Azure AD administrator accounts on your PC, select your account from the Pick an account list, then provide the account password. If you do not find your account in the list, specify your account by clicking Use another account.
-
If you have not used any Azure AD administrator accounts yet on the PC (for example, because you are configuring a fresh Active Roles installation), specify your account user name in the Sign in field, then provide your password.
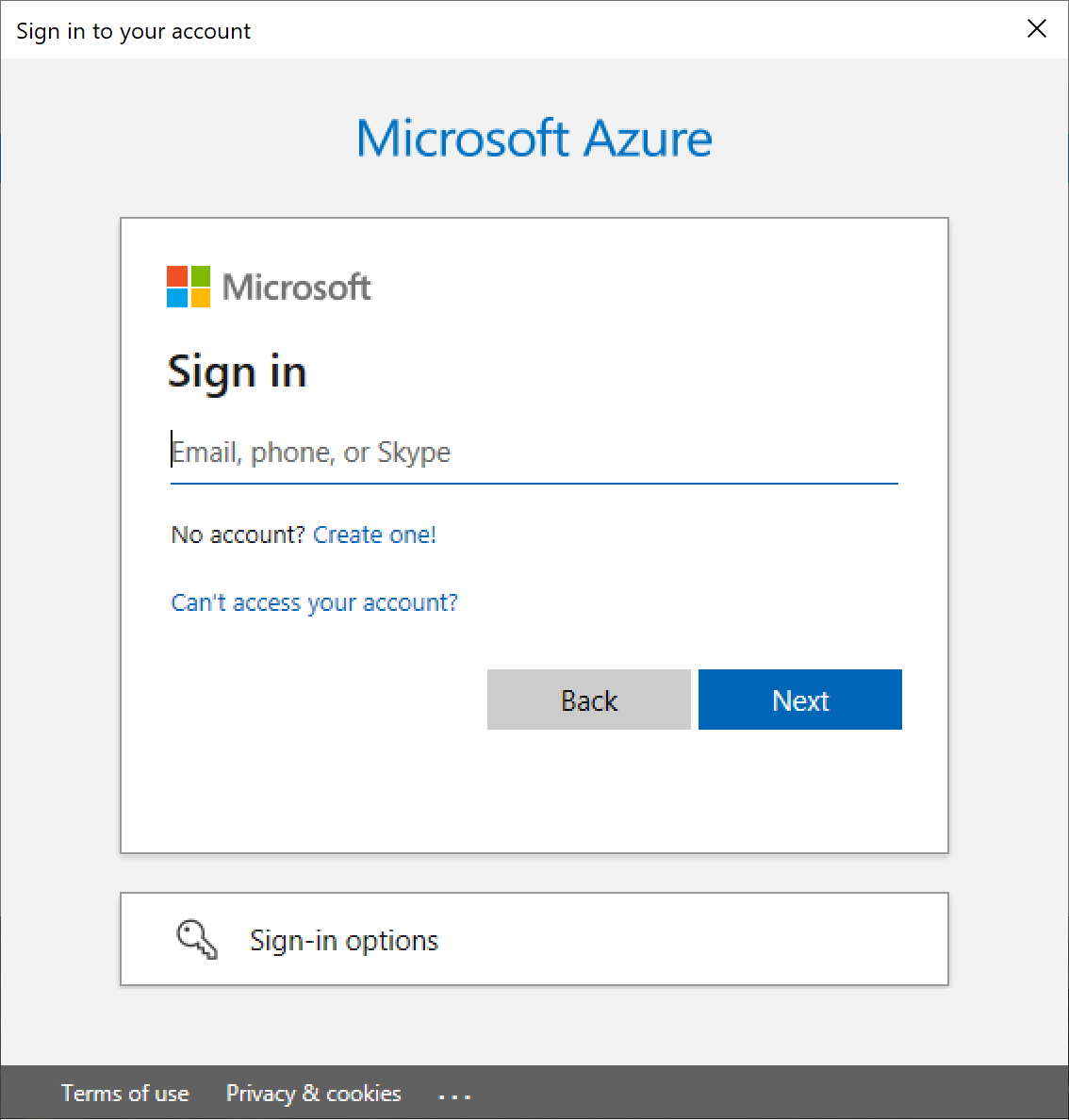
NOTE: Make sure to specify the account used for adding the Azure tenant (that is, the account name listed under the Name column of the Azure tenant). Authenticating with another account will result in an error.
-
The Azure tenant and all the related domains and applications are then deleted upon successful login.
-
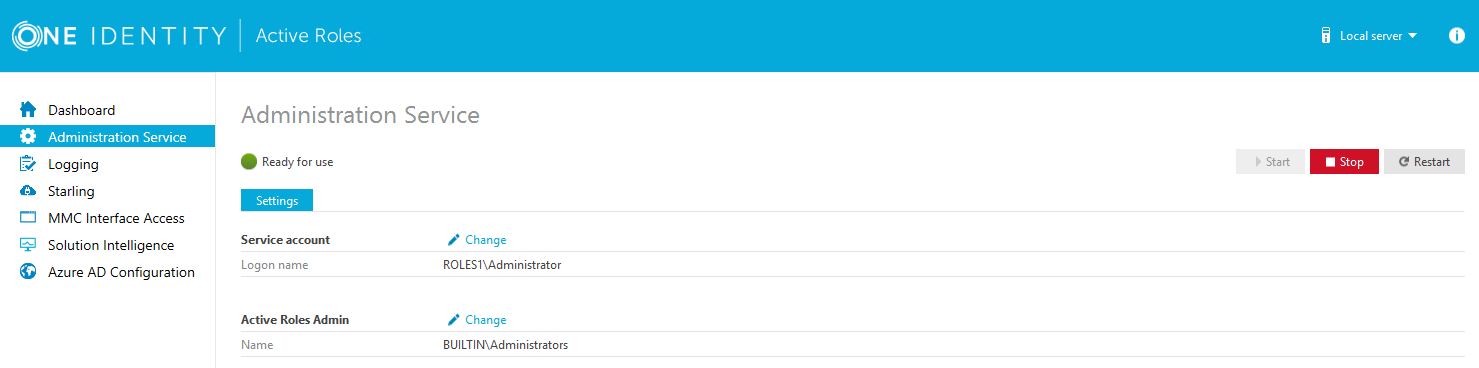
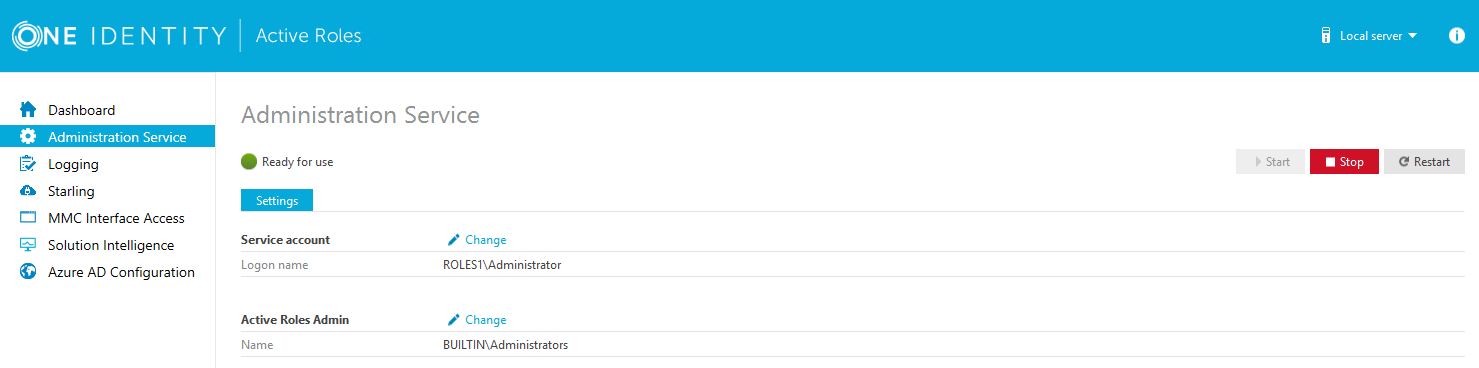
To apply the changes, you must restart the Administration Service, as indicated on the user interface. To restart the Administration Service, open the Configuration Center, click Administration Service on the left pane, then either click Restart, or first click Stop and then Start.
-
(Optional) If you want to force the deletion of the Active Roles Azure application on the Azure Portal for the removed Azure tenant, click Remove Azure Application and log in with the credentials of the removed Azure tenant.
This is typically recommended as an extra housekeeping and security measure if the removed Azure tenant has been previously managed either in earlier Active Roles versions or on other machines as well, but the Azure tenant has not been removed from those Active Roles installations prior to uninstalling them (leaving their client secret intact on the Azure Portal).
|

|
CAUTION: Using the Remove Azure Application option will result in all Active Roles installations losing access to the specified Azure tenant. If this happens, users managing the Azure tenant in another Active Roles installation (for example, on another machine) can regain access to the Azure tenant if they:
-
Remove the Azure tenant in the Azure AD Configuration tab of their Active Roles Configuration Center.
-
Add the Azure tenant again, as described in Configuring a new Azure tenant and consenting Active Roles as an Azure application. |
-
To confirm removal, check if the removed Azure tenant has disappeared from the list of Azure tenants in the Azure AD Configuration page of the Active Roles Configuration Center, and from the Directory Management > Tree > Azure node of the Active Roles Web Interface.
Active Roles Management Shell enables you to perform the following configuration tasks to manage Hybrid AD:
Use the Active Roles Management Shell to add an Azure AD tenant. To do so, run the New-QADAzureConfigObject cmdlet on the Management Shell interface.
Description
New-QADAzureConfigObject lets you add an Azure AD tenant to Active Directory.
Usage Recommendations
Use New-QADAzureConfigObject to add an Azure AD tenant using the tenant ID provided by Microsoft for the default tenant (created at the time of the Microsoft Azure subscription).
Syntax
New-QADAzureConfigObject -type 'AzureTenant' -name 'Azuretenantname' -AzureTenantId 'AzureTenantGUID' -AzureTenantDescription 'AzureTenantDescription' -AzureAdminUserID 'AzureGlobalAdminUserID' -AzureAdminPassword 'AzureGlobalIDPassword' -AzureADTenantType 'AzureTenantType'
Parameters
The New-QADAzureConfigObject cmdlet has the following parameters.
-
type (string): Specifies the object class of the directory object to be created (such as User or Group). The cmdlet creates a directory object of the object class specified with this parameter.
Table 6: Parameter: type (string)
|
Required |
true |
|
Position |
named |
|
Accepts pipeline input |
false |
|
Accepts wildcard characters |
false |
-
name (string): Sets the name attribute to the value of this parameter on the new object created by New-QADAzureConfigObject in the directory.
Table 7: Parameter: name (string)
|
Required |
true |
|
Position |
named |
|
Accepts pipeline input |
false |
|
Accepts wildcard characters |
false |
-
AzureTenantId (string): Specifies the Azure AD tenant ID obtained from the default tenant (created after subscribing to Microsoft Azure).
NOTE: The Azure AD ID value configured for this parameter must match the tenant ID configured on the Azure AD side. Otherwise, attempts to create an Azure AD application or manage Azure AD objects will fail.
Table 8: Parameters: AzureTenantId (string)
|
Required |
true |
|
Position |
named |
|
Accepts pipeline input |
false |
|
Accepts wildcard characters |
false |
-
AzureTenantDescription: Specifies the required description of the Azure AD tenant.
Table 9: AzureTenantDescription
|
Required |
false |
|
Position |
named |
|
Accepts pipeline input |
false |
|
Accepts wildcard characters |
false |
-
AzureAdminUserID: Specifies the administrative user name for Microsoft Azure AD.
NOTE: The administrative user must have the required privileges (for example, License Administrator, User Administrator or Groups Administrator roles) to perform license management or Azure user, guest user, and group management.
For more information on the available privileges and for an overview of the various Azure and Azure AD administrative roles, see Azure AD built-in roles and Classic subscription administrator roles, Azure roles, and Azure AD roles in the official Microsoft documentation.
Table 10: Parameters: AzureAdminUserID
|
Required |
true |
|
Position |
named |
|
Accepts pipeline input |
false |
|
Accepts wildcard characters |
false |
-
AzureAdminPassword: Specifies the administrative user password for Microsoft Azure AD.
Table 11: Parameters: AzureAdminPassword
|
Required |
true |
|
Position |
named |
|
Accepts pipeline input |
false |
|
Accepts wildcard characters |
false |
-
AzureADTenantType: Specifies the Azure AD tenant type (Federated, Non-Federated, or Synchronized Identity).
NOTE: Make sure that you select the tenant type corresponding to your organization environment.
Table 12: Parameters: AzureADTenantType
|
Required |
true |
|
Position |
named |
|
Accepts pipeline input |
false |
|
Accepts wildcard characters |
false |
| Accepts value |
- Federated
- NonFederated
- SynchronizedIdentity
|
Examples
See the following use cases for examples on how to use this cmdlet.
Example: Creating a new Azure AD tenant with a local user
To create a new Azure AD tenant with a locally logged on user
-
Connect to any available domain controller with the credentials of your local user.
-
Create a new Azure AD tenant with the following New-QADAzureConfigObject cmdlet:
C:\PS> New-QADAzureConfigObject -type 'AzureTenant' -name 'CompanyAzuretenant' -AzureTenantId 'CompanyAzureTenantID' -AzureTenantDescription 'Azure tenant for Company' -AzureAdminUserID 'AzureAdminUser1' -AzureAdminPassword 'AzureAdminPassword1’ -AzureADTenantType 'AzureTenantType'
Example: Creating a new Azure AD tenant with a specific user and then disconnecting
To create a new Azure AD tenant with a specific user and then disconnect
-
Connect to any available domain controller:
C:\PS> $pw = read-host "Enter password" -AsSecureString
-
Connect to the local Administration Service with a specific user of your choice:
C:\PS> connect-qadService -service 'localhost' -proxy -ConnectionAccount 'company\administrator' -ConnectionPassword $pw
-
Create the new Azure AD tenant:
C:\PS> New-QADAzureConfigObject -type 'AzureTenant' -name 'CompanyAzuretenant' -AzureTenantId 'CompanyAzureTenantID' -AzureTenantDescription 'Azure tenant for Company' -AzureAdminUserID 'AzureAdminUser1' -AzureAdminPassword 'AzureAdminPassword1’ -AzureADTenantType 'AzureTenantType'
-
Once the Azure AD tenant is created, disconnect your user:
C:\PS> disconnect-qadService
Add an Azure AD Application
You can use the Active Roles Management Shell to add an Azure AD application to the Azure AD tenant.
To add an Azure AD application
On the Management Shell interface, run the New-QADConfigObject cmdlet.
Synopsis
This cmdlet enables you to add an Azure AD application to the Azure AD tenant.
Syntax
New-QADAzureConfigObject -type 'AzureApplication' -name 'AzureApplication' -DisplayName 'ApplicationDisplayName' -AzureTenantId 'AzureTenantGUID' -AzureAppPermissions 'ApplicationPermission'
Description
Use this cmdlet to add an Azure AD application.
Parameters
Table 15: Parameters: AzureTenantId (string)
|
Required |
true |
|
Position |
named |
|
Accepts pipeline input |
false |
|
Accepts wildcard characters |
false |
Example
Connect to any available domain controller with the credentials of the locally logged on user, and create a new Azure AD application:
C:\PS> New-QADAzureConfigObject -type 'AzureApplication' -name 'AzureApplication' -DisplayName 'ApplicationDisplayName' -AzureTenantId 'AzureTenantGUID' -AzureAppPermissions 'ApplicationPermission'
Example
Connect to the local Administration Service with the credentials of a specific user, create a new Azure AD tenant and then disconnect:
C:\PS> $pw = read-host "Enter password" -AsSecureString
C:\PS> connect-qadService -service 'localhost' -proxy -ConnectionAccount 'company\administrator' -ConnectionPassword $pw
C:\PS> New-QADAzureConfigObject -type 'AzureApplication' -name 'AzureApplication' -DisplayName 'ApplicationDisplayName' -AzureTenantId 'AzureTenantGUID' -AzureAppPermissions 'ApplicationPermission'
C:\PS> disconnect-qadService