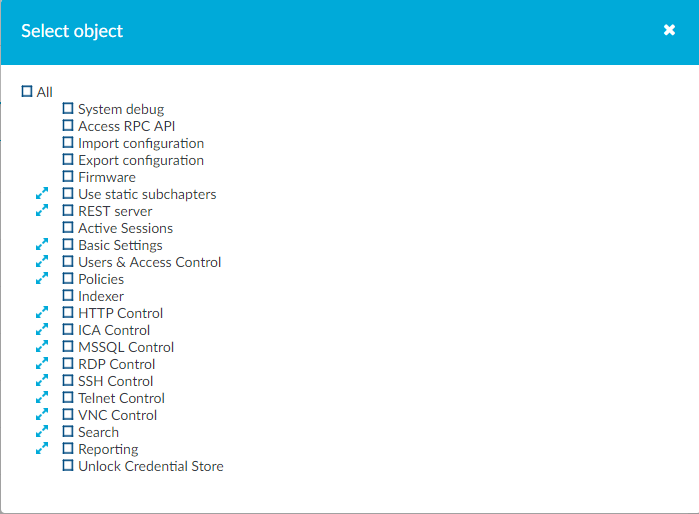
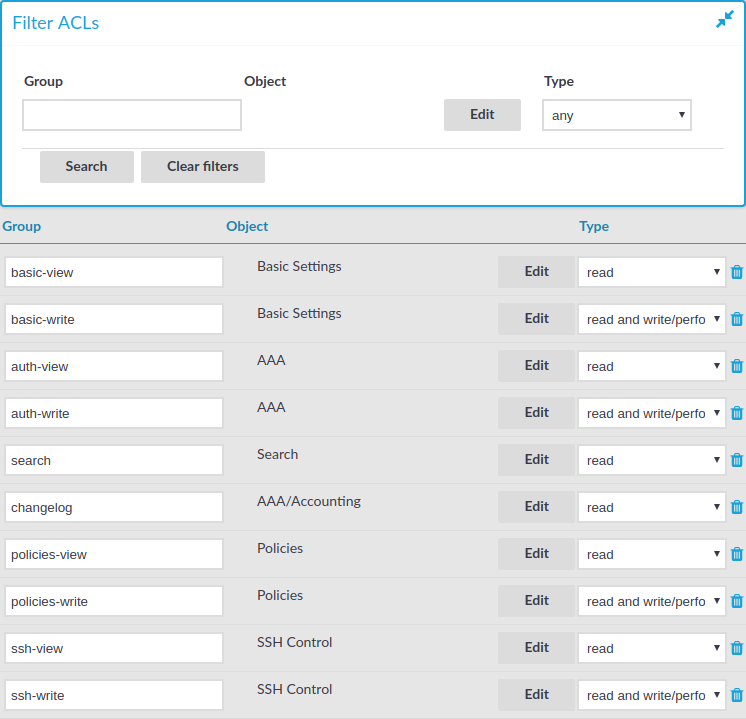
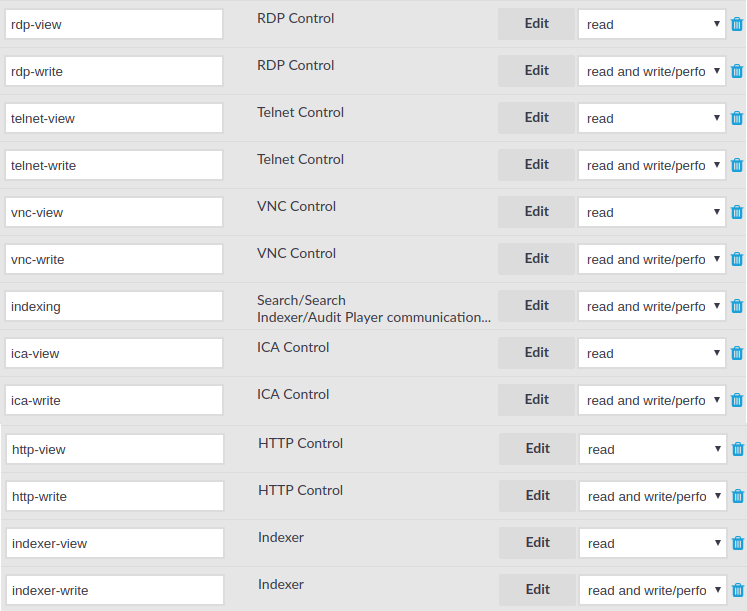
In One Identity Safeguard for Privileged Sessions (SPS), user rights can be assigned to usergroups. SPS has numerous usergroups defined by default, but custom user groups can be defined as well. Every group has a set of privileges: which pages of the SPS web interface it can access, and whether it can only view (read) or also modify (read & write/perform) those pages or perform certain actions.
NOTE: Every group has either read or read & write/perform privileges to a set of pages.
-
For details on assigning privileges to a new usergroup, see Assigning privileges to user groups for the One Identity Safeguard for Privileged Sessions (SPS) web interface.
-
For details on modifying existing groups, see Modifying group privileges.
-
For details on finding usergroups that have a specific privilege, see Finding specific usergroups.
-
For tips on using usergroups, see Using usergroups.
-
For a detailed description about the privileges of the built-in usergroups, see Built-in usergroups of One Identity Safeguard for Privileged Sessions (SPS).
Figure 89: Users & Access Control > Appliance Access — Managing SPS users

 .
. .
.