Sessions-initiated (SPS-initiated) workflow
In the Sessions-initiated workflow, the users initiate sessions from SPS. In this workflow SPS uses SPP as a credential store.
This workflow is transparent in the sense that you can connect to the target server or to SPS directly using your SSH or RDP client application. SPS authenticates these clients and communicates with SPP to get the password for the target server. It then uses that password to open the connection. Authentication happens on SPS, while authorization happens on SPP based on the user's entitlements.
This is what old and new users of standalone SPS are likely to prefer.
The usual SPP Access Requests workflows that SPP provides are supported:
-
Auto-approved access request
-
Approved/denied access request (similar to the four-eyes authorization feature of SPS)
To configure the Sessions-initiated (SPS-initiated) workflow
-
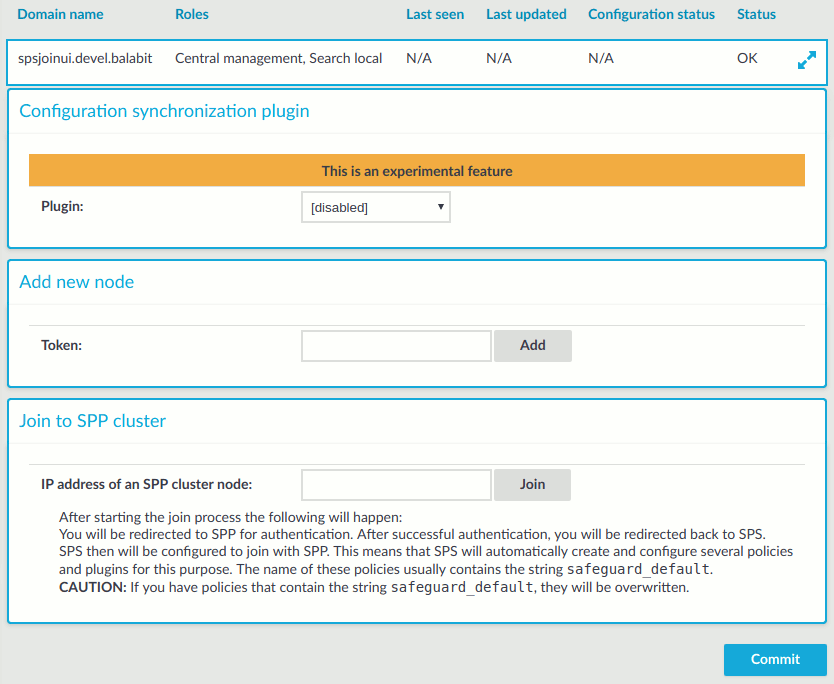
On SPS, link SPP and SPS as described in Joining SPS to SPP.
-
Configure SPP to allow SPS to request passwords from SPP as described in Configuring SPP for Sessions-initiated workflow.
-
Configure SPS to use the linked SPP as a Credential Store as described in Configuring SPS for Sessions-initiated workflow.
-
Optionally, customize monitoring settings as follows: