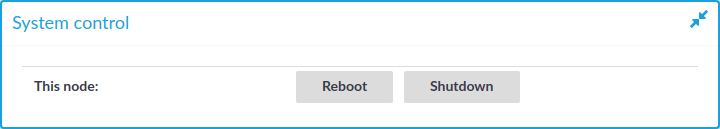
To reboot or shut down One Identity Safeguard for Privileged Sessions (SPS)
- Navigate to Basic Settings > System > System control > This node.
- Click the respective action button.
The Other node refers to the secondary node of a High Availability SPS cluster. For details on High Availability clusters, see Managing a High Availability One Identity Safeguard for Privileged Sessions (SPS) cluster.
|

|
Caution:
-
When rebooting the nodes of a cluster, reboot the other (secondary) node first to avoid unnecessary takeovers.
-
When shutting down the nodes of a cluster, shut down the other (secondary) node first. When powering on the nodes, start the primary node first to avoid unnecessary takeovers.
-
When both nodes are running, avoid interrupting the connection between the nodes: do not unplug the Ethernet cables, reboot the switch or router between the nodes (if any), or disable the HA interface of SPS. |
Figure 99: Basic Settings > System > System Control — Performing basic management
NOTE: Web sessions to the SPS interface are persistent and remain open after rebooting SPS, so you do not have to relogin after a reboot.
During the reboot process, SPS displays information about the progress of the reboot and any possible problems in the following places:
-
On the web interface of SPS, at any of the Listening addresses configured at Basic settings > Local Services > Web login (admin and user). (After booting, you are directed to the login screen of SPS.)
-
On the console, which you can monitor with IPMI (ILOM) or console access.
The information displayed in the browser and on the console is the same.
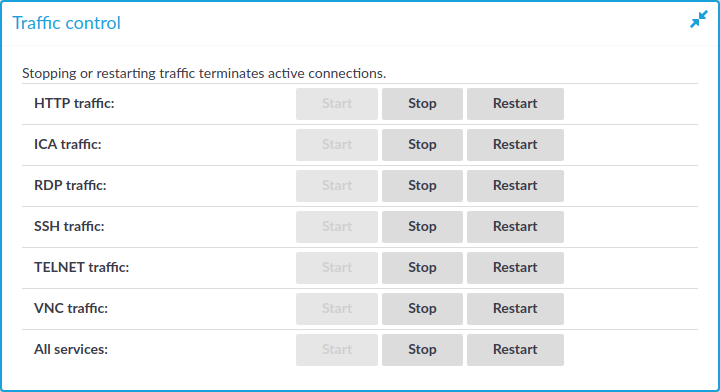
The following describes how to temporarily disable some or all of the controlled traffic to the protected servers.
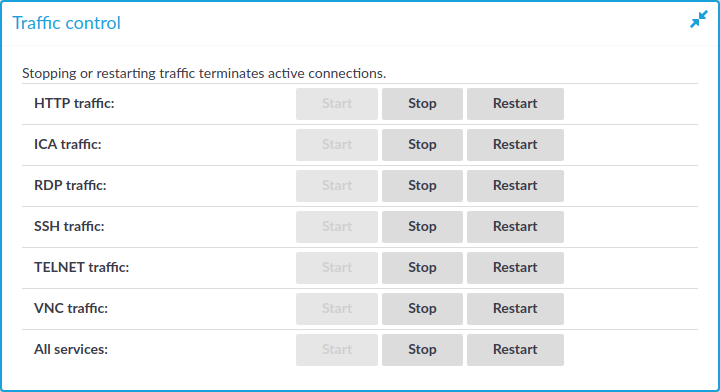
Figure 100: Basic Settings > System > Traffic control — Disabling the controlled traffic
|

|
Caution:
Disabling traffic that way is only temporary. Connections will be enabled again after committing any other change from the SPS web interface. For details on how to permanently disable a type of traffic, see Disabling controlled traffic permanently. |
NOTE: Disabling the traffic affects only the traffic configured in the Connection policies, other traffic can pass SPS even if the all traffic is disabled. For details on configuring Connection policies, see General connection settings.
To temporarily disable some or all of the controlled traffic to the protected servers
-
Navigate to the Basic Settings > System > Traffic control.
-
-
To disable SSH traffic, click Stop in the SSH traffic field. Note that this also stops all other traffic forwarded in SSH, for example X11.
-
To disable RDP traffic, click Stop in the RDP traffic field.
-
To disable Telnet and TN3270 traffic, click Stop in the Telnet traffic field.
-
To disable VNC traffic, click Stop in the VNC traffic field.
-
To disable all types of traffic, click Stop in the All services field.
The System monitor displays the status of all types of traffic.
NOTE: Disabling the traffic affects only the traffic configured in the Connection policies, other traffic can pass SPS even if the all traffic is disabled. For details on configuring Connection policies, see General connection settings.
To disable controlled traffic permanently
-
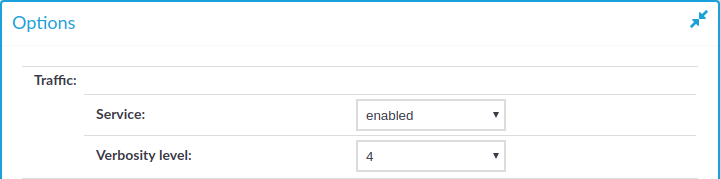
Figure 101: <Protocol name> Control > Global Options — Disabling the controlled traffic persistently
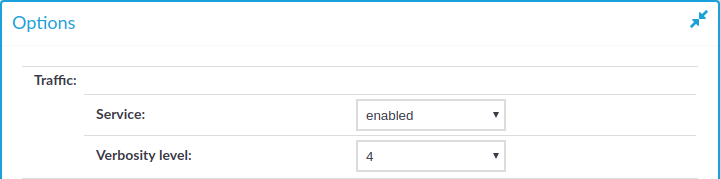
Navigate to the Global Options page of the traffic type you want to disable, for example to SSH Control > Global Options to disable SSH traffic.
-
Set the Traffic > Service field to disabled.
-
Click  .
.
When you have a set of two or more Safeguard for Privileged Sessions (SPS) instances in your deployment, you can join them into a cluster. This has several advantages. You can:
-
Manage the nodes from one central location.
-
Monitor their status and update their configuration centrally.
-
Search all session data recorded by all nodes in the cluster on a single node.
-
Scale the performance of the cluster by adding new nodes and joining them to the cluster easily.
-
Extend auditing to other networks by adding new nodes to the cluster and joining them to the cluster.
This is achieved by assigning roles to the individual nodes in your cluster: you can set one of your SPS nodes to be the Central management node and the rest of the nodes are managed from this central node.
NOTE: Consider the following:
-
All nodes in a cluster must run the same version of SPS.
-
One Identity recommends managing not more than a few tens of instances from the Central management node.
-
Nodes in the cluster connect to each other using IPsec.
You can configure your Safeguard for Privileged Sessions (SPS) cluster in the following ways:
-
Configuration synchronization without a central search: This method allows you to perform your configuration settings on your Central management node. Managed host nodes periodically fetch and merge the settings into their own: this is called "configuration synchronization". Central search is not configured in this method, so you can search for sessions on each node, including the Central management node.
For more information on this method, see Configuration synchronization without a central search.
-
Central search with configuration synchronization: This method allows you to use a Central management node with a Search master role to view session data recorded by the minion nodes of your cluster, as well as manage all the nodes in the cluster from one central location.
For more information on this method, see Central search with configuration synchronization.
IMPORTANT: One Identity does not recommend having a central search configuration without configuration synchronization.


 .
.