If you have previously managed an Azure AD deployment, but you are not upgrading from a previous version of Active Roles via in-place upgrade (for example, because the previous version of Active Roles has been uninstalled before installing the new version), you can import, reauthenticate and consent existing Azure tenants via the Active Roles Configuration Center.
NOTE: Consider the following if you have not used any Azure tenants earlier, or if you installed the latest version of Active Roles via in-place upgrade:
-
If you have installed Active Roles out-of-the-box, and no Azure AD environment has been used previously in your organization, you must specify a new Azure tenant to manage Azure directory objects (such as Azure users, guest users, contacts, O365 groups or Azure Security groups). For more information, see Configuring a new Azure tenant and consenting Active Roles as an Azure application.
-
If you perform an in-place upgrade of Active Roles (that is, you install the latest version without uninstalling the previous version of Active Roles first in one of the supported upgrade paths), you can reauthenticate the existing Azure tenants with the Upgrade configuration wizard upon launching the Active Roles Configuration Center after installation.
For more information on reauthenticating Azure tenants this way, see Reconfiguring Azure tenants during upgrade configuration in the Active Roles 7.5 Quick Start Guide. For more information on the supported upgrade paths, see Version upgrade compatibility chart in the Active Roles 7.5 Release Notes.
To import and reauthenticate an Azure tenant and set Active Roles as a consented Azure application
-
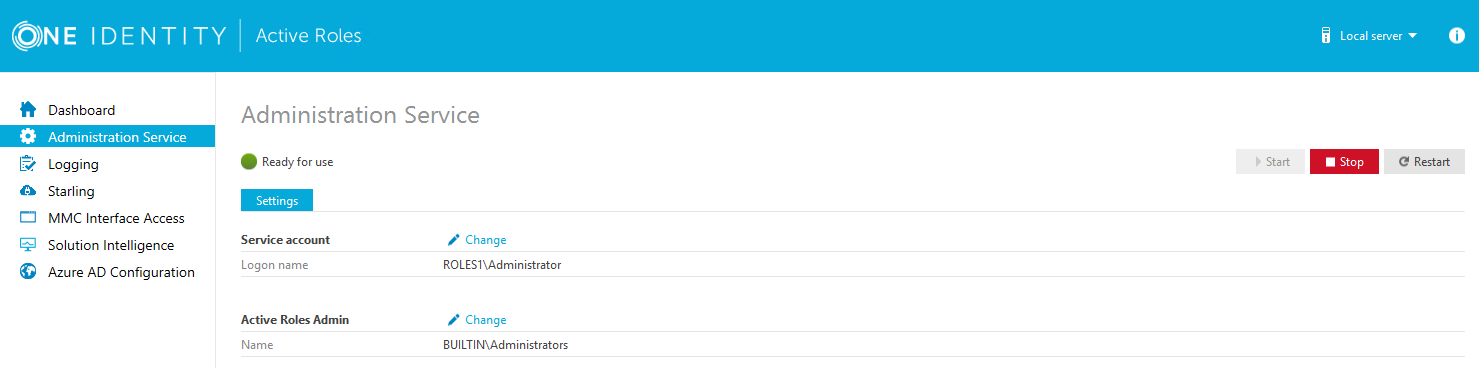
Stop the Active Roles Administration Service. To do so, in the Active Roles Configuration Center, on the left pane, navigate to Administration Service and click Stop.
-
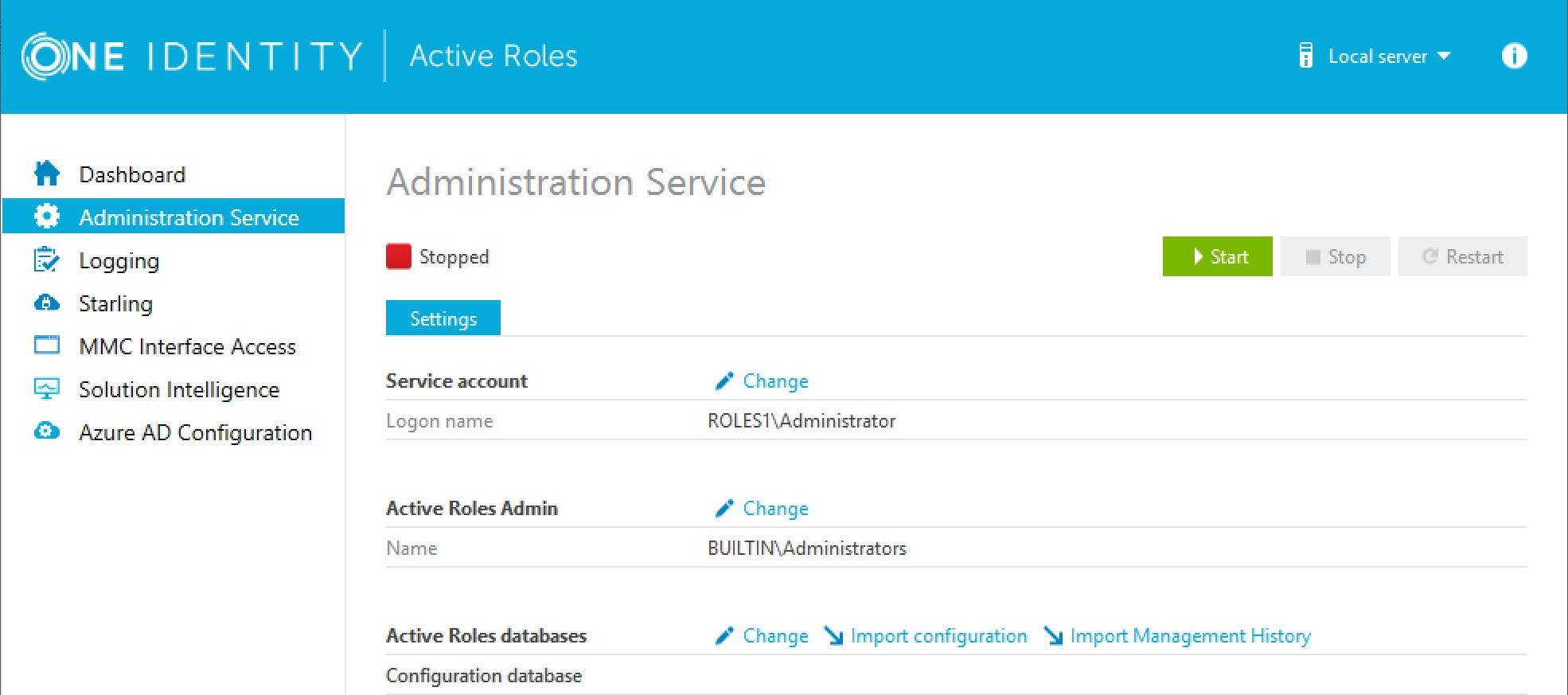
Once the Active Roles Administration Service stopped, open the Import configuration wizard by clicking Active Roles databases > Import configuration.
-
Perform the steps of the wizard. For more information, see Import configuration data or Steps to deploy the Administration Service in the Active Roles Quick Start Guide.
CAUTION: Importing a configuration will overwrite every Azure tenant currently listed in the Azure AD Configuration page with those included in the imported configuration.
-
Once the import procedure finished, start the Active Roles Administration Service by clicking Start in the Administration Service page.
-
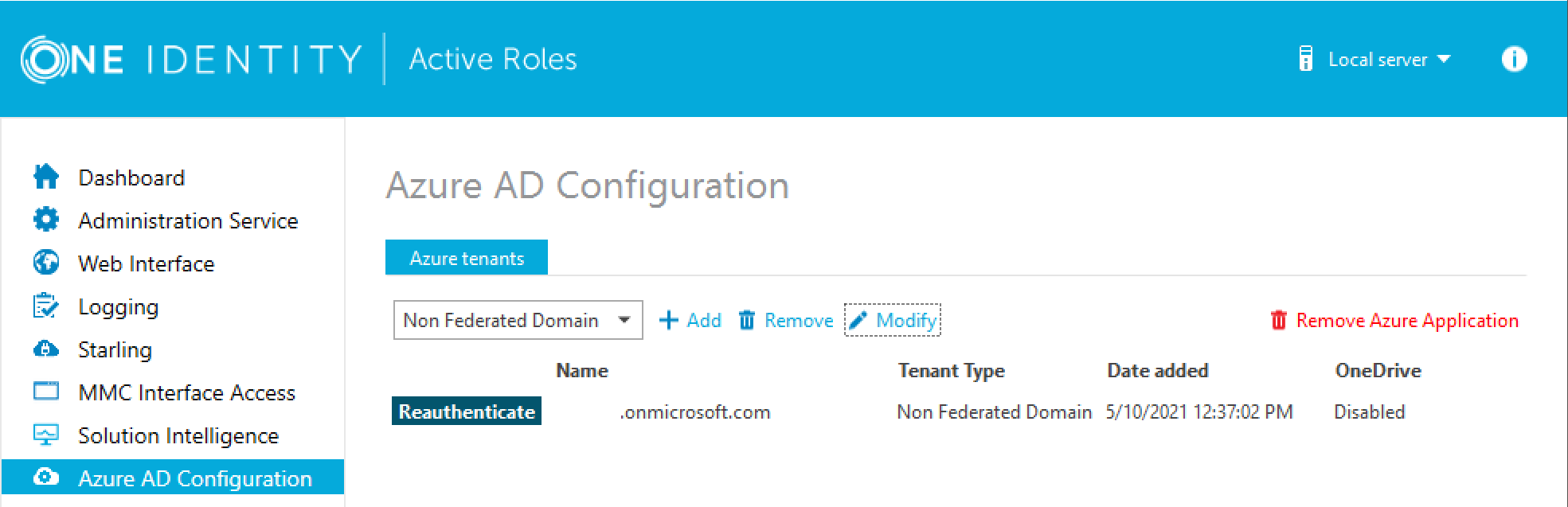
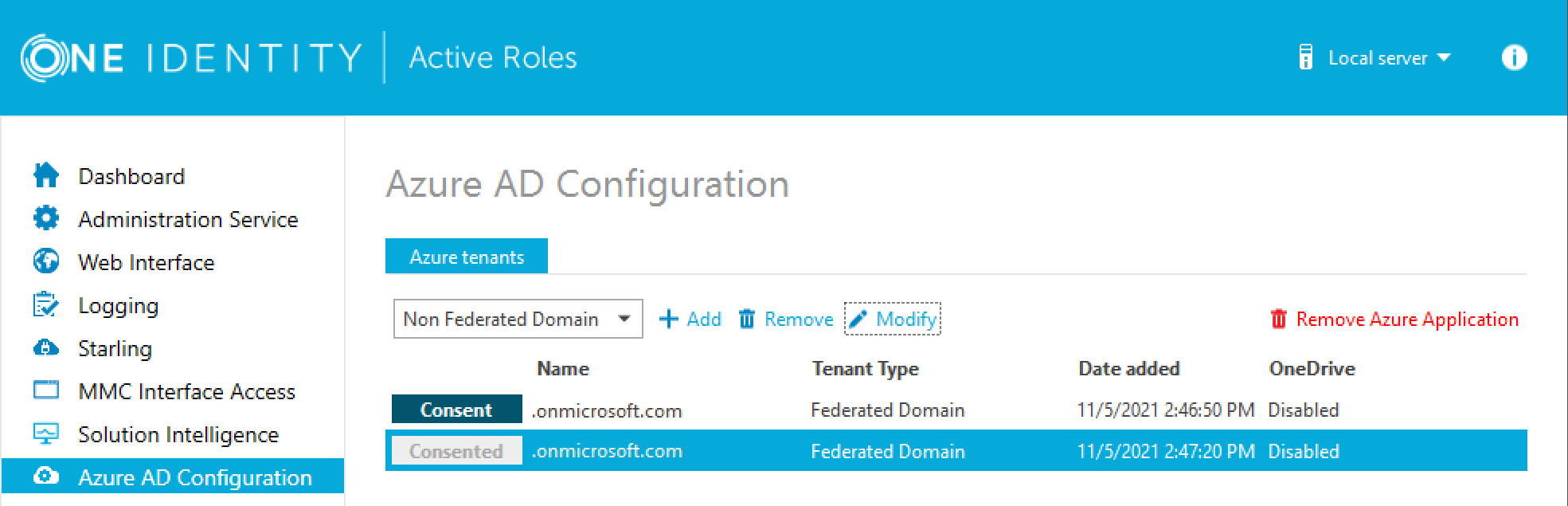
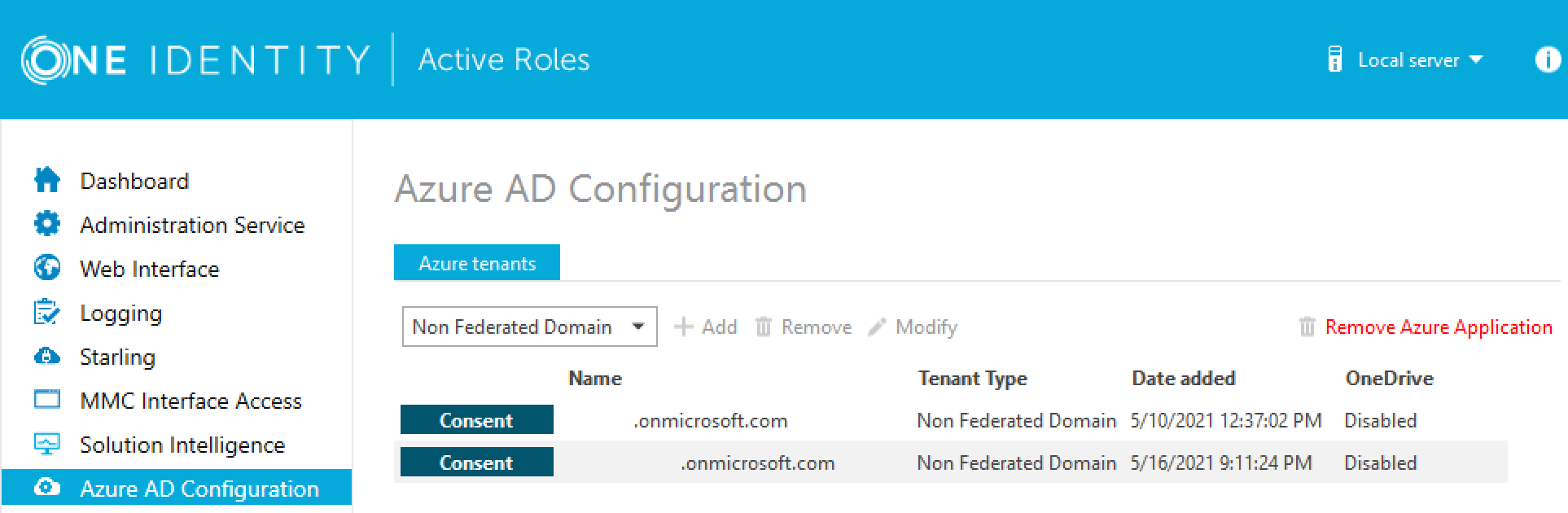
In the Active Roles Configuration Center, on the left pane, click Azure AD Configuration.
The list of imported Azure tenants appears.
-
To configure an imported Azure tenant, click Reauthenticate.
-
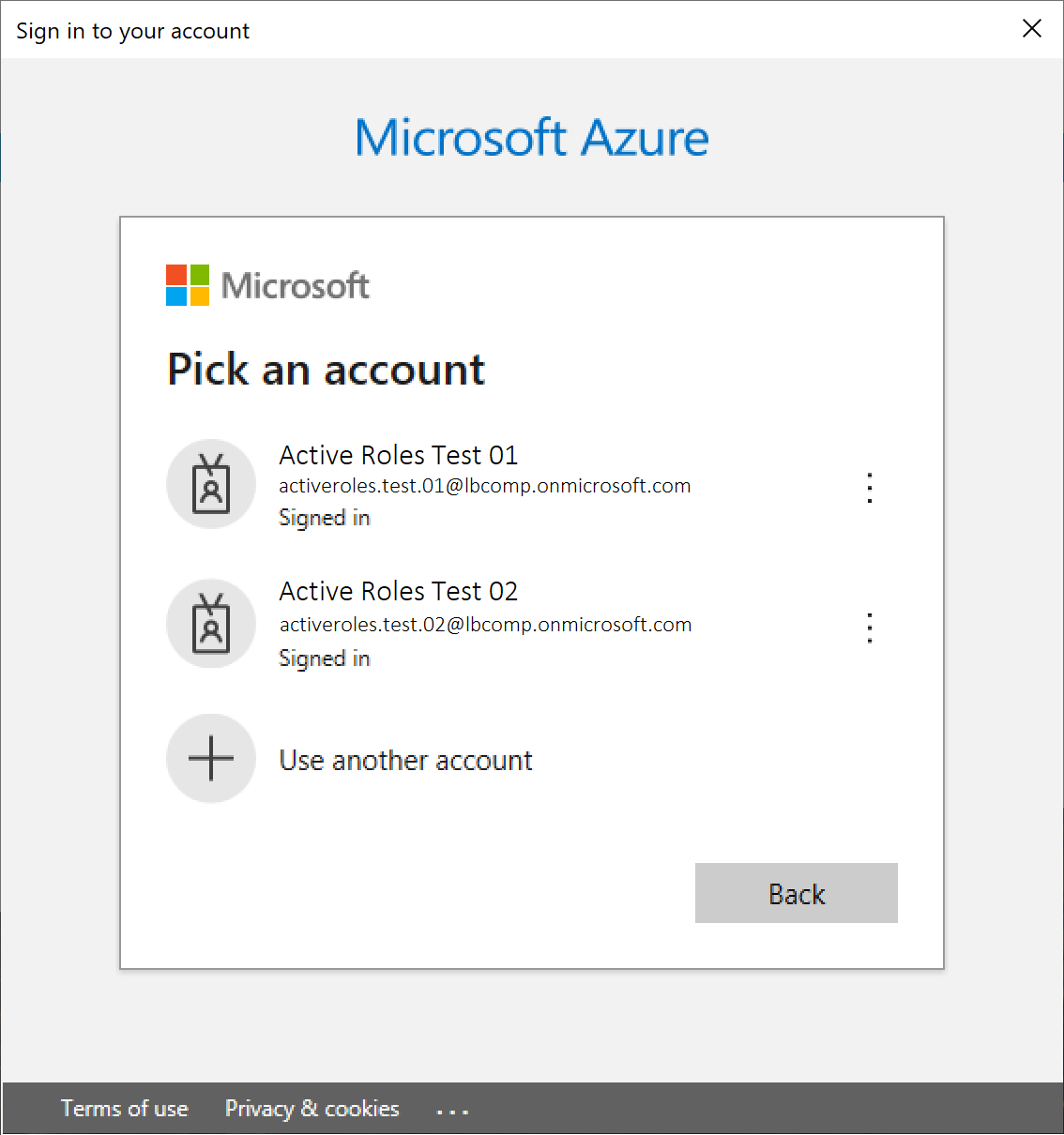
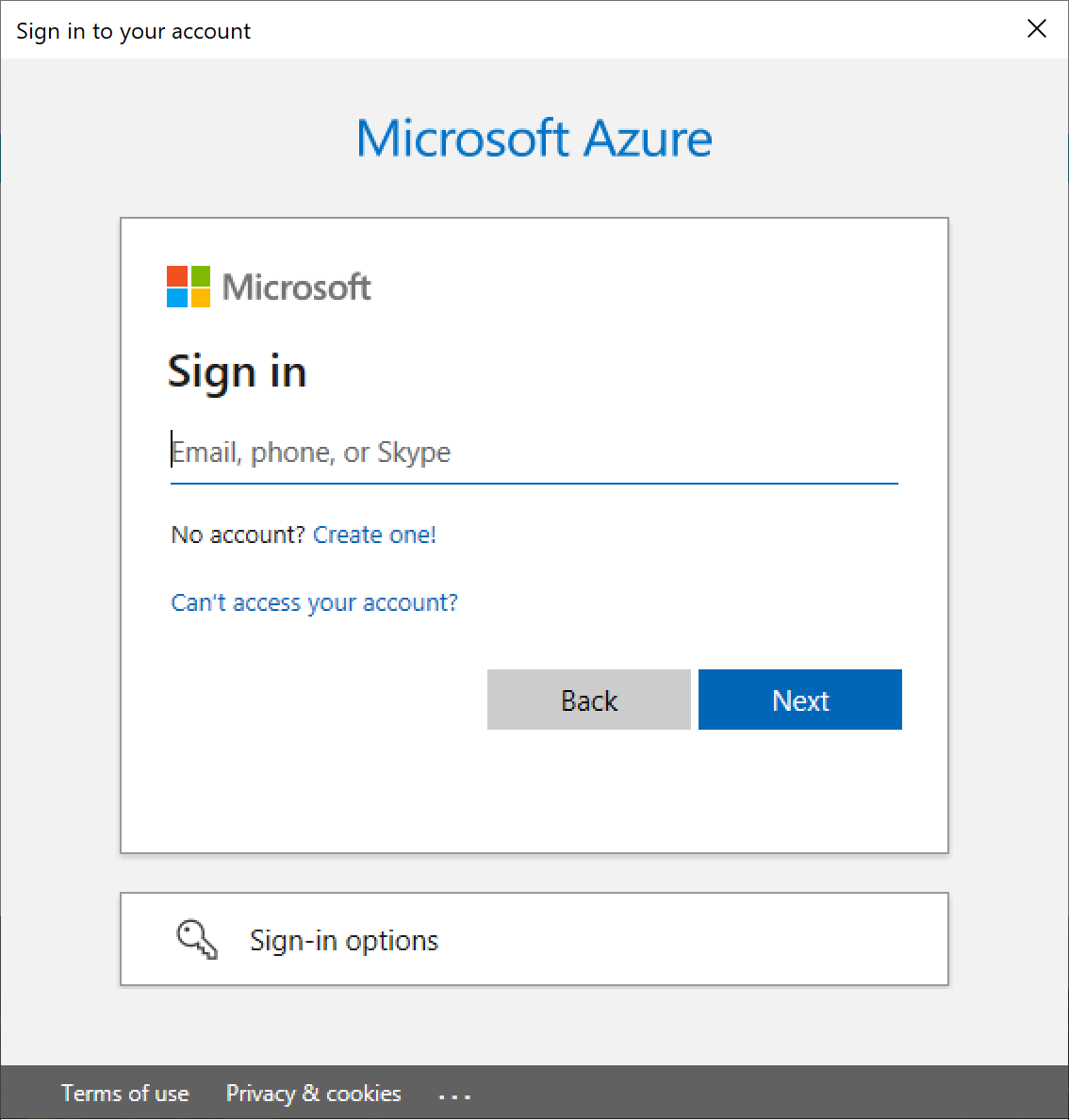
Authenticate your Azure AD administrator account.
-
If you already used one or more Azure AD administrator accounts on your PC, select your account from the Pick an account list, then provide the account password. If you do not find your account in the list, specify your account by clicking Use another account.
-
If you have not used any Azure AD administrator accounts yet on the PC (for example, because you are configuring a fresh Active Roles installation), specify your account user name in the Sign in field, then provide your password.
-
-
To manage the Azure tenant and its contents in the Active Roles Web Interface, you must consent Active Roles as an Azure application. To do so, click Consent next to the Azure tenant.
-
Authenticate your Azure AD administration account again. Depending on the type of Microsoft pop-up that appears (Pick an account or Sign in), either select the Azure AD account you used for adding the Azure tenant, or specify its user name and password again.
NOTE: Make sure to specify the account used for adding the Azure tenant (that is, the account name listed under the Name column of the Azure tenant). Authenticating with another account will result in an error.
-
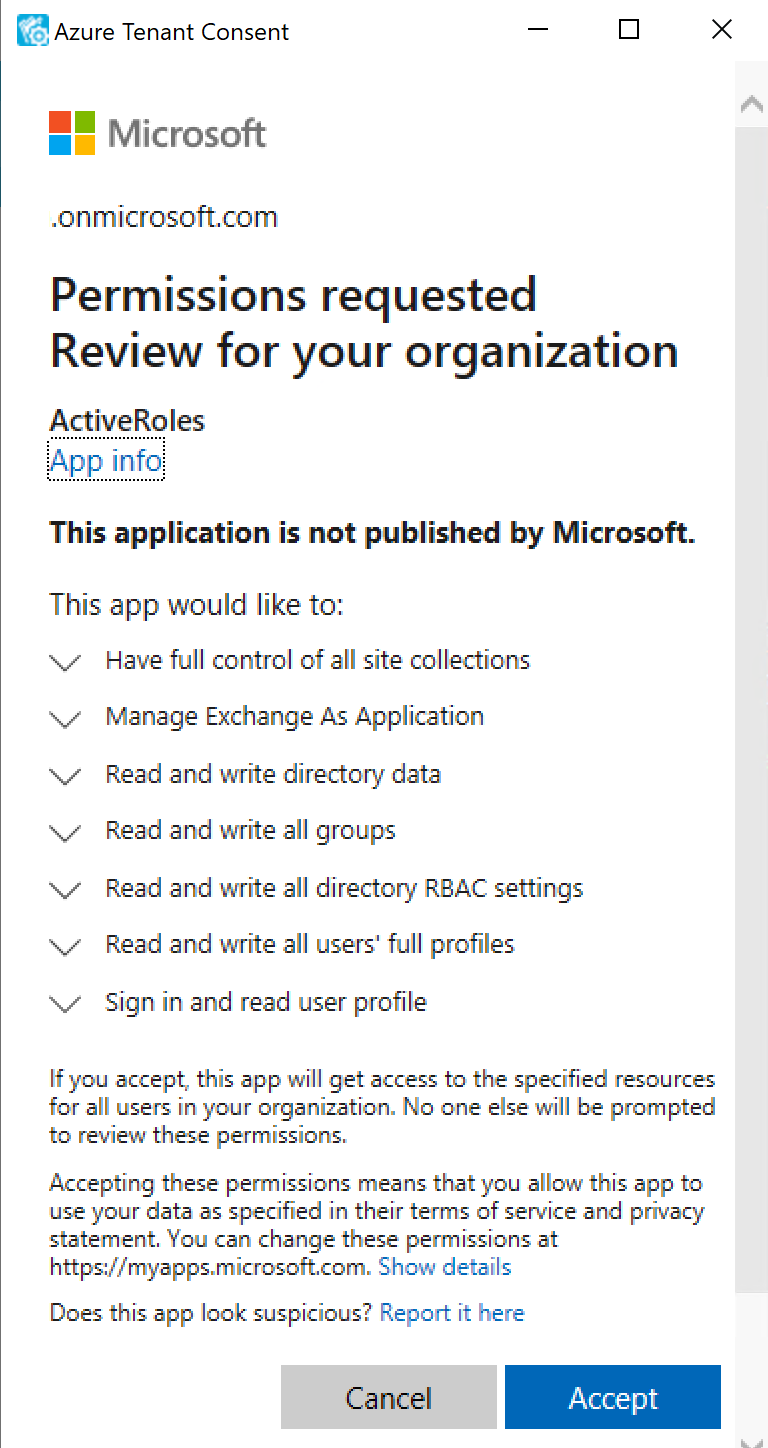
The standard Microsoft Permissions requested pop-up appears, listing all the permissions required for configuring Active Roles as an Azure application. To finish creating the Azure application, click Accept.
Active Roles then authenticates every Azure AD administrative operation performed in the Azure tenant with a set of generated client ID and client secret.
NOTE: Once you click Accept, Windows may show a Security Warning pop-up with the following message:
The current webpage is trying to open a site on your intranet. Do you want to allow this?
In such cases, clicking either Yes or No could freeze the pop-up dialog, but consenting the Azure tenant will finish without problem.
This issue can occur in case the computer running Active Roles has incorrect browser settings. As a workaround, to get an up-to-date status of the state of the Azure tenant, close and restart the Active Roles Configuration Center after clicking Yes in the Security Warning pop-up.
-
To make the configured Azure tenant(s) appear in the Active Roles Web Interface, you must restart the Administration Service, as indicated on the user interface. Click Administration Service on the left pane, then either click Restart, or first click Stop and then Start.
TIP: Once the Azure tenant or tenants are configured, and Active Roles is also set as a consented Azure AD application for it, you can view and modify the configured tenant(s) and their settings at the following locations:
-
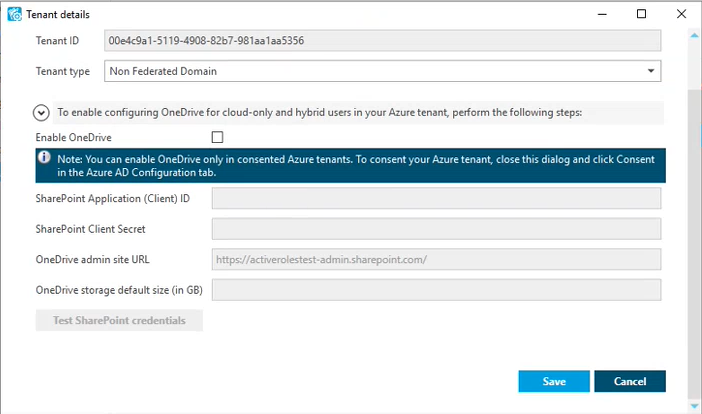
To change the domain type or OneDrive provisioning settings of an Azure tenant, in the Active Roles Configuration Center, navigate to Azure AD Configuration, select the Azure tenant, and click Modify. For more information, see Viewing or modifying the Azure AD tenant type.
-
To check the connectivity status of the Azure configuration, in the Active Roles Web Interface, navigate to Directory Management > Tree > Azure > Azure Configuration > Azure Health Check. For more information, see View Azure Health for Azure AD tenants and applications .
-
To check the Azure Licenses Report, in the Active Roles Web Interface, navigate to Directory Management > Tree > Azure > Azure Configuration > Azure Licenses Report. For more information, see View Azure Licenses Report .
-
To check the Office 365 Roles Report, in the Active Roles Web Interface, navigate to Directory Management > Tree > Azure > Azure Configuration > Office 365 Roles Report. For more information, see View Office 365 Roles Report .
NOTE: Consider the following when configuring an Azure tenant:
-
When Active Roles is registered as a consented Azure AD application, minimal permissions are assigned to it by default. To add additional permissions to the Azure application, sign in to the Azure Portal and add your required permissions there.
-
Azure Multi-Factor Authentication (MFA) is automatically enforced for Azure users and Azure guest users added to the configured Azure tenant. To disable Azure MFA for the Azure tenant, sign in to the Azure Portal and navigate to Tenant > Properties > Manage Security defaults and set Enable Security defaults to No.