Adding a preference manifest
You can add a preference manifest file to the Preference Manifests node in Group Policy Object Editor (GPOE)
To add a preference manifest
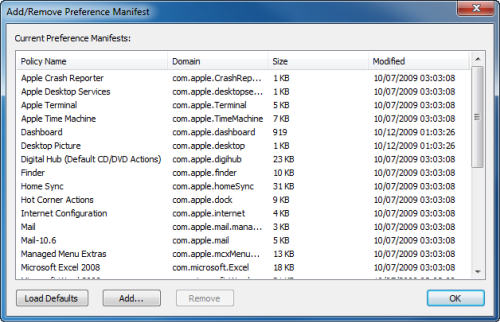
- Right-click on the Preference Manifests node and select Add/Remove Preference Manifests from the menu.
The Add/Remove Preference Manifest dialog is displayed.
- Click Add to browse for the preference manifest file that you want to load.
- Click Load Defaults to reset the list to the default set of preference manifests.
- Click Remove to remove the selected preference manifests.
- Click OK to save changes and close the Add/Remove Preference Manifest dialog.
The Preference Manifest view is updated to reflect the changes.
Certificate Autoenrollment
Certificate Autoenrollment on macOS
Certificate Autoenrollment requirements and setup
Java requirement: Unlimited Strength Jurisdiction Policy Files
Installing certificate enrollment web services
Configuring Certificate Services Client - Certificate Enrollment Policy Group Policy
Configuring Certificate Services Client - Auto-Enrollment Group Policy
Configuring Certificate Templates for autoenrollment
Using Certificate Autoenrollment
Configuring Certificate Autoenrollment manually
Trigger machine-based Certificate Autoenrollment
Troubleshooting Certificate Autoenrollment
Certificate Autoenrollment process exited with an error
Certificate Autoenrollment is a feature of Safeguard Authentication Services based on Microsoft Open Specifications. Certificate Autoenrollment allows macOS/macOS® clients to take advantage of existing Microsoft infrastructure to automatically enroll for and install certificates. Certificate policy controls which certificates are enrolled and what properties those certificates will have.
With Certificate Autoenrollment, a public/private key pair is automatically generated according to certificate template parameters defined in Group Policy. The public key is sent to the Certification Authority (CA), and the CA responds with a new certificate corresponding to the public key, which is installed along with the private key into the appropriate system or user keychain on the Mac client.
You can use Group Policy to automatically configure which certificate enrollment policy servers to use for Certificate Autoenrollment and to periodically run Certificate Autoenrollment.
This section explains the system requirements for Certificate Autoenrollment and walks you through policy setup as well as client-side usage and troubleshooting.
Certificate Autoenrollment on macOS
Most of the Certificate Autoenrollment code is implemented in Java. After this code has successfully requested a certificate from a CA, it invokes platform-specific code to store the private key and certificate in a suitable way for the operating system or for particular applications. This platform-specific code is implemented as a shell script, certstore.sh, in the /var/opt/quest/vascert/script directory.
The certstore.sh script is a platform-agnostic front end that chooses and loads a platform-specific back end script. For macOS, the back end script is certstore-mac.sh. This script provides a fully functional implementation that uses the /usr/bin/security tool to integrate with macOS keychains.
Certificate Autoenrollment requirements and setup
Prior to installing One Identity Certificate Autoenrollment, ensure your system meets the following minimum hardware and software requirements.
| Component | Requirements |
|---|---|
| Operating system |
macOS 10.13 (or later) |
| Java unlimited strength policy files | For more information, see Java requirement: Unlimited Strength Jurisdiction Policy Files. |
| Authentication Services |
One Identity Authentication Services version 4.1.2 (or later). |
| Additional software |
Certificate Autoenrollment depends on services provided by a Microsoft Enterprise Certificate Authority (CA) in your environment. In addition to Active Directory and an Enterprise CA, you must install the following software in your environment:
In order for Certificate Autoenrollment to function on client computers, you must configure the following policies:
Additionally, you must configure Java 1.6 (or later) as the default JVM for your system. NOTE: Install JRE (Java Runtime Environment) on all platforms other than macOS; macOS requires JDK (Java Development Kit). Typing java on the command line provides instructions.
|
| Rights |
Enterprise Administrator rights to install software and configure Group Policy and Certificate Template policy (only if Certificate Autoenrollment is not already configured for Windows hosts in your environment.) |