| Caution:
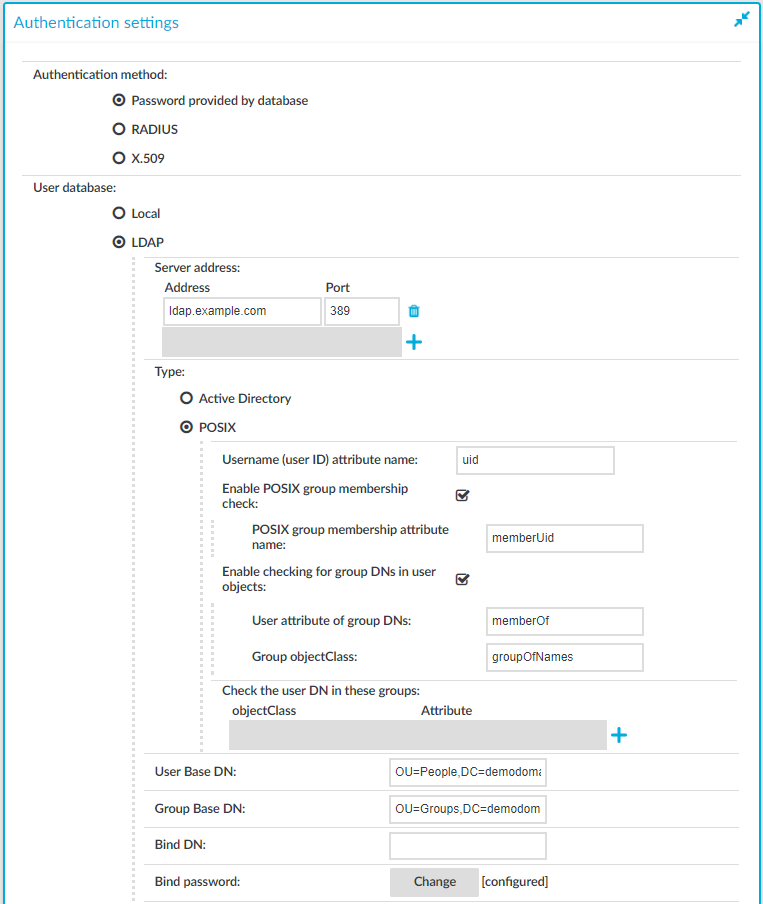
According to recent cryptographic research, SHA-1 algorithm cannot be trusted as secure anymore, because signatures can be forged with reasonable costs. As a result, SHA-1 algorithm is not supported in SPS for X.509 certificate chains. Starting from SPS versions 6.0.4 and 6.5.0, certificates with SHA1-based signatures are no longer trusted for Active Directory or LDAP authentication, and future versions might refuse to validate SHA-1 signatures altogether.
Note that Root CA certificates may still contain SHA-1 signatures, because the signature is not validated for self-signed certificates. It is expected that other software such as clients and servers connected to SPS might reject SHA-1 signatures in a similar fashion.
Signing CAs in SPS generate certificates with SHA-256 since versions 4.3.4 and 5.0.0.
SPS checks if the certificate revocation list (CRL) has expired and that the CRL has been signed by the same certificate authority (CA). | next to the user, at the right edge of the screen.
.

 .
.

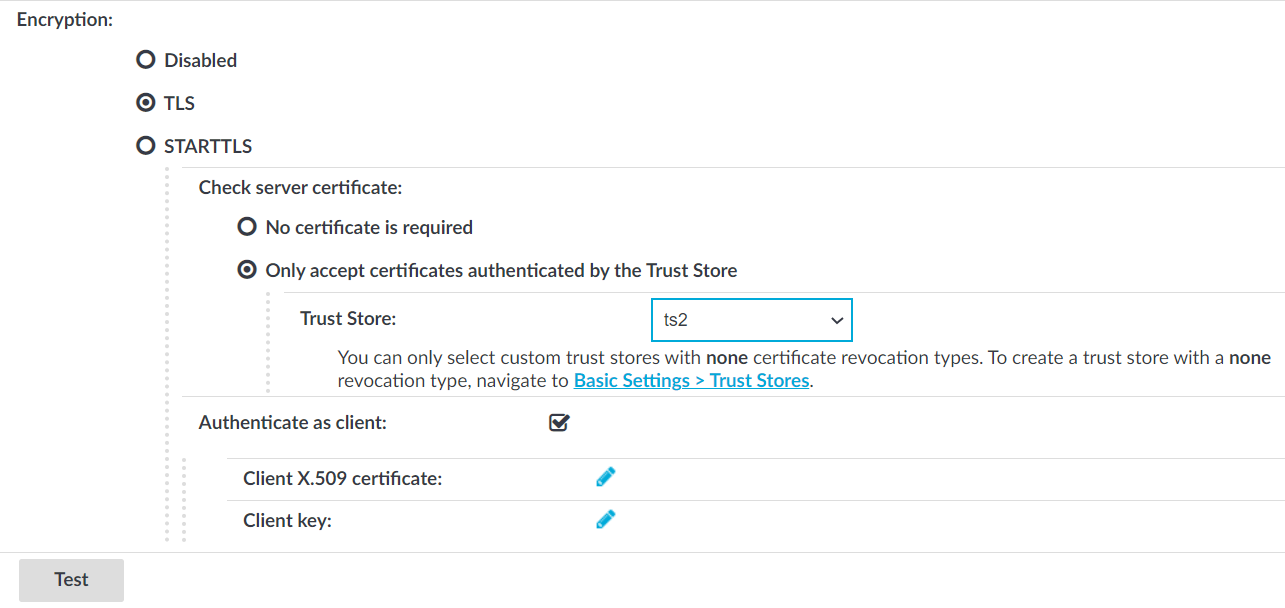
 in the Client X.509 certificate field to upload the certificate. After that, click
in the Client X.509 certificate field to upload the certificate. After that, click