Creating and editing channel policies
The Channel policy lists the channels (for example, terminal session and SCP in SSH, or Drawing and Clipboard in RDP) that can be used in the connection, and also determines if the channel is audited or not. The Channel policy can also restrict access to each channel based on the IP address of the client or the server, a user list, user group, or a time policy. For example, all clients may access the servers defined in a connection via SSH terminal, but the channel policy may restrict SCP access only to a single client. The policies set in the channel policy are checked when the user attempts to open a particular channel type in the connection.
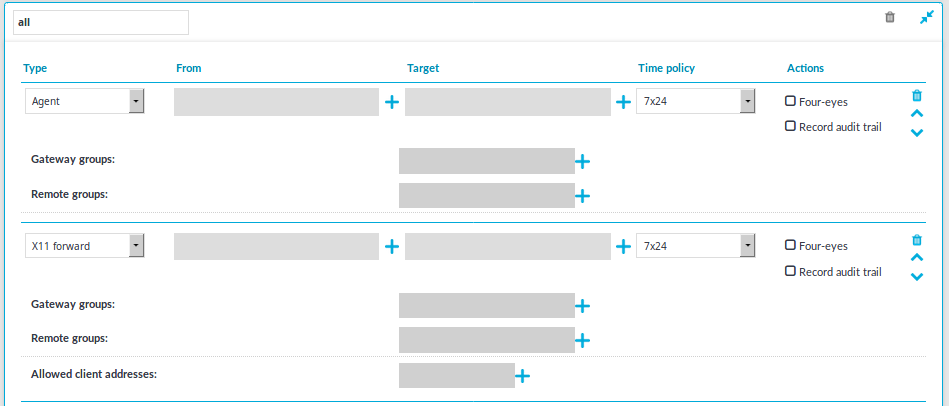
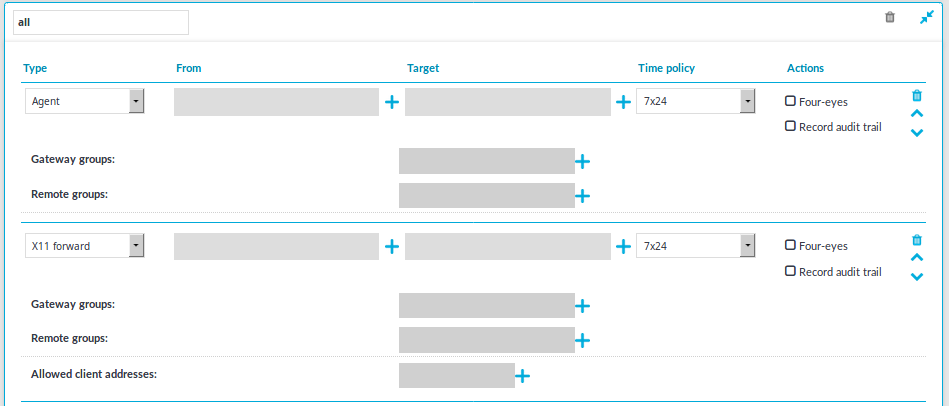
Figure 145: <Protocol name> Control > Channel Policies — Configuring channel policies
To create a new channel policy or edit an existing one
-
Channel policies are configured individually for every protocol. Navigate to the Channel Policies tab of the respective protocol (for example, SSH Control > Channel Policies) and click  to create a new channel policy. Enter a name for the policy (for example, shell_and_backup).
to create a new channel policy. Enter a name for the policy (for example, shell_and_backup).
-
Click  to add a new channel.
to add a new channel.
-
Select the channel to be enabled in the connection from the Type field. All restrictions set in the following steps will be effective on this channel type. The available channels are different for every protocol. For their descriptions, see the following sections:
-
The HTTP protocol has only one channel type with no special configuration options.
-
Supported ICA channel types for the Independent Computing Architecture protocol.
-
Supported RDP channel types for the Remote Desktop Protocol.
-
Supported SSH channel types for the Secure Shell protocol
-
The Telnet protocol has only one channel type with no special configuration options.
-
The VNC protocol has only one channel type with no special configuration options.
-
To restrict the availability of the channel only to certain clients, click  in the From field and enter the IP address of the client allowed to use this type of the channel. Repeat this step until all required client IPs are listed.
in the From field and enter the IP address of the client allowed to use this type of the channel. Repeat this step until all required client IPs are listed.
You can also enter a hostname instead of the IP address, and One Identity Safeguard for Privileged Sessions (SPS) automatically resolves the hostname to IP address. Note the following limitations:
-
SPS uses the Domain Name Servers set Basic Settings > Network > Naming > Primary DNS server and Secondary DNS server fields to resolve the hostnames.
-
If the Domain Name Server returns multiple IP addresses, SPS selects randomly from the list.
-
To restrict the availability of the channel only to certain servers, click  in the Target field and enter the IP address of the server allowed to use this type of the channel. Repeat this step until all required server IPs are listed.
in the Target field and enter the IP address of the server allowed to use this type of the channel. Repeat this step until all required server IPs are listed.
|

|
NOTE:
Use the real IP address of the server, which may be different from the one addressed by the clients, specified in the Target field of the connection policy. |
You can also enter a hostname instead of the IP address, and One Identity Safeguard for Privileged Sessions (SPS) automatically resolves the hostname to IP address. Note the following limitations:
-
SPS uses the Domain Name Servers set Basic Settings > Network > Naming > Primary DNS server and Secondary DNS server fields to resolve the hostnames.
-
If the Domain Name Server returns multiple IP addresses, SPS selects randomly from the list.
-
To restrict the availability of the channel only to certain users, click  in the Remote Group field and enter the name of the user group allowed to use this type of the channel. Repeat this step until all permitted groups are listed.
in the Remote Group field and enter the name of the user group allowed to use this type of the channel. Repeat this step until all permitted groups are listed.
To restrict the availability of the channel when using gateway authentication, click  in the Gateway Group field and enter the name of the user group allowed to use this type of the channel. Repeat this step until all permitted groups are listed.
in the Gateway Group field and enter the name of the user group allowed to use this type of the channel. Repeat this step until all permitted groups are listed.
You may list local user lists as defined in Creating and editing user lists, or LDAP groups (for details on accessing LDAP servers from SPS, see Authenticating users to an LDAP server). Note the following behavior of SPS:
-
If you list multiple groups, members of any of the groups can access the channel.
|

|
NOTE:
When listing both a whitelist and blacklist in the Remote Group section and a username appears on both lists, the user will be able to access the channel. |
-
If you do not list any groups, anyone can access the channel.
|

|
NOTE:
When the channel opens, there are certain cases when the remote group is not known yet. For example, in case of an RDP or ICA login screen, the drawing channel has to be opened first to properly display the logon screen. Only those channel rules will apply, where the Remote group field is empty. In case of network level authentication, all required information is present already so this limitation does not apply. |
-
If a local user list and an LDAP group has the same name and the LDAP server is configured in the connection that uses this channel policy, both the members of the LDAP group and the members of the local user list can access the channel.
-
Select a time policy to narrow the availability of the channel. If the time policy of the channel policy is set to 7x24, the channel is always available. For details, see Configuring time policies.
-
Some channel types require additional parameters, for example port forwarding in SSH needs the IP addresses and ports of the source and destination machines. Click  in the Details field and enter the required parameters. For a list of parameters used by the different channels, see Supported SSH channel types and Supported RDP channel types.
in the Details field and enter the required parameters. For a list of parameters used by the different channels, see Supported SSH channel types and Supported RDP channel types.
-
Select the Record audit trail option to record the activities of the channel into audit trails. Typically large file-transfers (for example system backups, SFTP channels) are not audited because they result in very large audit trails. Check regularly the free hard disk space available on SPS if you do audit such channels. You can also receive alerts about disk space fill-up if you set these. For details, see Preventing disk space fill-up and System related traps.
-
Select the 4 eyes option to require four-eyes authorization to access the channel. For details, see Configuring four-eyes authorization.
-
Repeat Steps 2-10 to add other channels to the policy.
|

|
NOTE:
The order of the rules matters. The first matching rule will be applied to the connection. Also, note that you can add the same channel type more than once, to fine-tune the policy. |
-
Click  to save the list.
to save the list.
Real-time content monitoring with Content Policies
You can monitor the traffic of certain connections in real time, and execute various actions if a certain pattern (for example, a particular command or text) appears in the command line or on the screen, or if a window with a particular title appears in a graphical protocol. Since content-monitoring is performed real-time, One Identity Safeguard for Privileged Sessions (SPS) can prevent harmful commands from being executed on your servers. SPS can also detect numbers that might be credit card numbers. The patterns to find can be defined as regular expressions. In case of ICA, RDP, and VNC connections, SPS can detect window title content.
The following actions can be performed:
-
Log the event in the system logs.
-
Immediately terminate the connection.
-
Send an e-mail or SNMP alerts about the event.
-
Store the event in the connection database of SPS.
SPS currently supports content monitoring in SSH session-shell connections, Telnet connections, RDP and Citrix ICA Drawing channels, and in VNC connections.
|

|
NOTE:
Command, credit card and window detection algorithms use heuristics. In certain (rare) situations, they might not match the configured content. In such cases, contact our Support Team to help analyze the problem.
Real-time content monitoring in graphical protocols is not supported for Arabic and CJK languages. |
Creating a new content policy
The following describes how to create a new content policy that performs an action if a predefined content appears in a connection.
|

|
NOTE:
Using content policies significantly slows down connections (approximately 5 times slower), and can also cause performance problems when using the indexer service. |
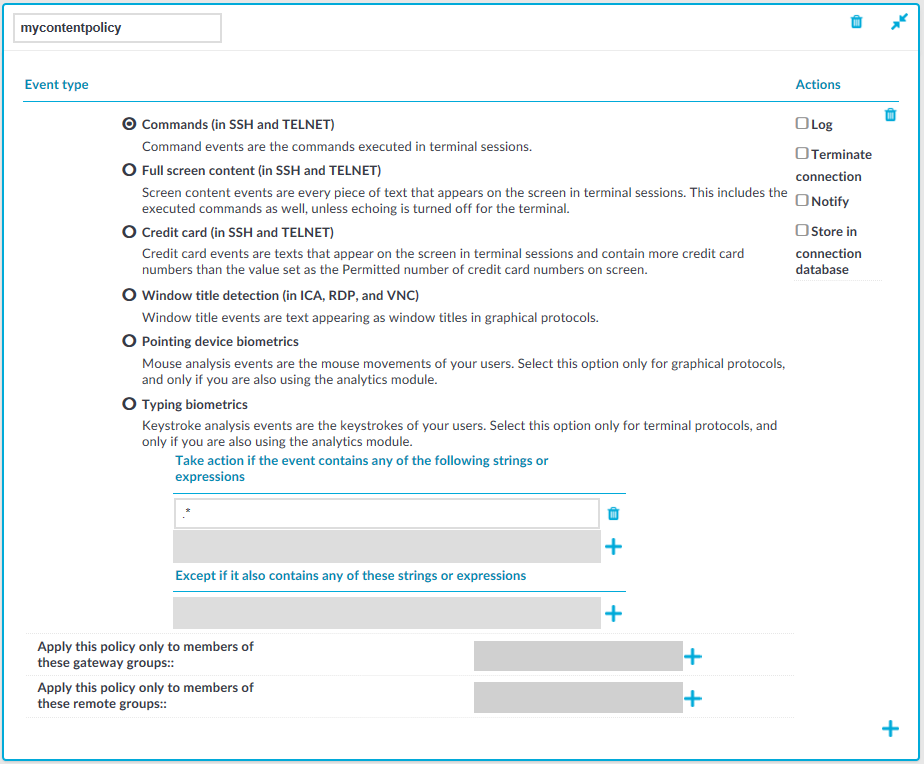
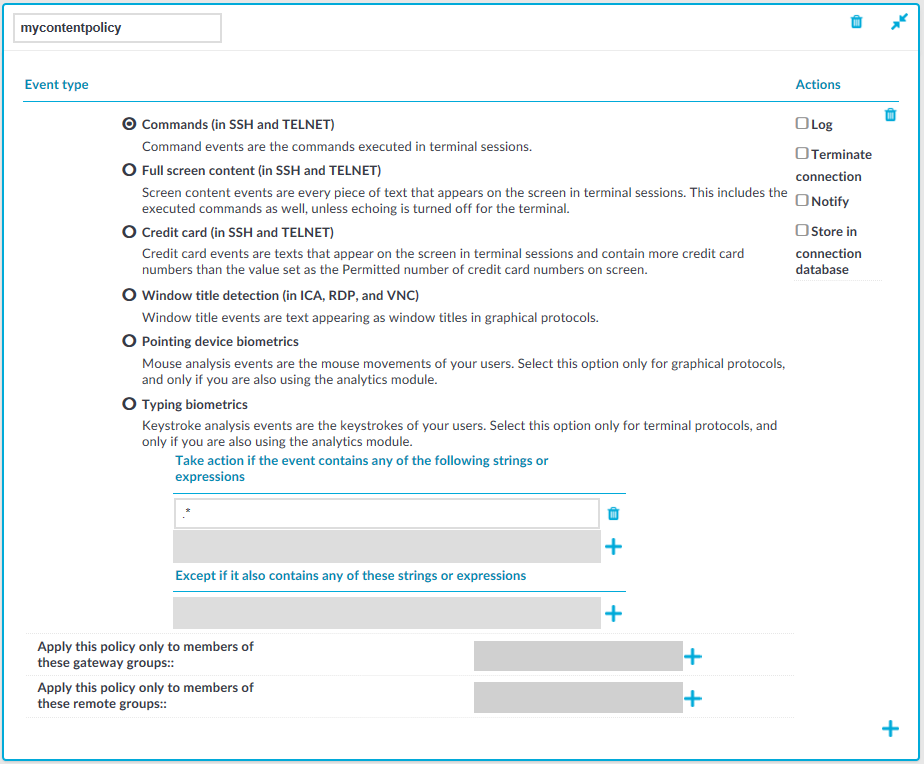
Figure 146: Policies > Content Policies — Content policies
To create a new content policy that performs an action if a predefined content appears in a connection
-
Navigate to Policies > Content Policies, click  and enter a name for the policy.
and enter a name for the policy.
-
Select the type of event that you want to monitor:
-
Commands: The commands executed in the session-shell channel of SSH connections, or in Telnet connections.
|

|
Caution:
During indexing, if a separate certificate is used to encrypt the upstream traffic, command detection works only if the upstream key is accessible on the machine running the indexer. |
|

|
NOTE:
Command detection is case-insensitive. |
-
Screen content: Every text that appears on the screen. For example, every text that is displayed in the terminal of SSH or Telnet connections. This includes the executed commands as well, unless echoing is turned off for the terminal.
-
Credit card: Process every text that appears on the screen and attempt to detect credit card numbers in SSH or Telnet connections. One Identity Safeguard for Privileged Sessions (SPS) performs an action if the number of detected credit card numbers exceeds the value set as Permitted number of credit card numbers.
Credit card number detection is based on the Luhn algorithm and lists of known credit card number prefixes.
-
Window title detection: Text appearing as window titles in case of RDP, Citrix ICA, and VNC connections. Note the following points.
Supported themes
-
Windows Classic at 96 and 120 DPI
-
Windows 2012 at 96 and 120 DPI (metro)
-
Windows 7 Normal at 96 and 120 DPI (not aero)
-
Windows 8 at 96 and 120 DPI (metro)
Limitations
-
Windows 10, Windows 2016 Server, and Windows 2019 Server themes are not supported
-
Windows Aero themes are not supported.
-
Windows that do not have an X (close window) button in the top-right corner (or it is not visible) are not detected.
-
Use window title detection for sessions that use a single monitor. The feature works in multi-monitor environments as well, but becomes very slow, therefore it is not recommended.
The configuration JSON file contains the most common window title color schemes.
|

|
NOTE:
Window title detection is case-insensitive. |
|

|
NOTE:
Do not adjust or modify the following settings unless you know exactly what you are doing. Misconfiguring them will severely decrease the performance of SPS.
-
If a special color is used, open /opt/scb/etc/window-title-default on the server, and add the color scheme in RGB. In case of a single color, enter "to": null. After adding a new color, temporarily disable all traffic going through SPS. Navigate to Basic Settings > System > Traffic control and click Stop in the All services field. Login to SPS as root locally (or remotely using SSH) to access the Console menu. Select Shells > Core Shell, and issue the systemctl restart zorp-core.service command.
-
The minimum and maximum height and the minimum width of the window title are determined in pixels, as "minheight", "maxheight" and "minwidth". |
-
Pointing device biometrics: Select this option only for graphical protocols, and only if you are also using One Identity Safeguard for Privileged Analytics (SPA). SPA can analyze mouse movement patterns of your users as a biometric identity verification method to protect against account theft. For details, see the One Identity Safeguard for Privileged Analytics website.
-
Typing biometrics: Select this option only for terminal-based protocols, and only if you are also using One Identity Safeguard for Privileged Analytics (SPA). SPA can analyze the typing patterns of your users as a biometric identity verification method to protect against account theft. For details, see the One Identity Safeguard for Privileged Analytics website.
-
Select Take action if the event contains any of the following strings or expressions, click  and enter a string or regular expression. SPS will perform an action if this expression is found in the connection, unless it is listed in the Except if it also contains any of these strings or expressions list. For example, SPS can terminate the connection if the user issues the rm -rf * in an SSH connection. Repeat this step to add further expressions if needed.
and enter a string or regular expression. SPS will perform an action if this expression is found in the connection, unless it is listed in the Except if it also contains any of these strings or expressions list. For example, SPS can terminate the connection if the user issues the rm -rf * in an SSH connection. Repeat this step to add further expressions if needed.
-
Use Perl Compatible Regular Expressions (PCRE).
-
The following characters must be escaped using a backslash character: '(single-quote). For example, instead of .*' use .*\'
-
SPS uses substring search to find the expression in the content. That is, SPS finds the expression even if there is more content before or after the matching part. For example, the conf pattern will match the following texts: conf, configure, reconfigure, arcconf, and so on.
-
Using complicated regular expressions or using many regular expressions will affect the performance of SPS.
-
If the multiple expressions are set, SPS processes them one after the other, and stops processing the content if the first match is found, even if other expressions would also match the content. Therefore, when using multiple expressions, start with the most specific one, and add general expressions afterward.
Example: Sample regular expressions for content policies
The following simple regular expressions are samples to demonstrate what kinds of events that can be detected using content policies.
-
The enable command on Cisco devices: the user enters privileges mode.
-
The conf term command on Cisco devices: the user configures the networking parameters of the device.
-
The sudo and su - commands: the user enters privileged mode Linux and other UNIX platforms.
-
To add an exception to the Take action if the event contains any of the following strings or expressions rule, select Except if it also contains any of these strings or expressions, click  and enter a string or regular expression. SPS will not perform any action if this expression is found in the connection. For example, to permit the users to delete only the /tmp directory in an SSH connection, enter rm -rf /tmp. Repeat this step to add further expressions if needed.
and enter a string or regular expression. SPS will not perform any action if this expression is found in the connection. For example, to permit the users to delete only the /tmp directory in an SSH connection, enter rm -rf /tmp. Repeat this step to add further expressions if needed.
Example: Sample content policies using Ignore rules
The following expressions can be used to perform an action if any SQL command is used in MySQL, except for the select and help commands:
-
Into the Take action if the event contains any of the following strings or expressions expression, enter mysql>.*
-
Add two Except if it also contains any of these strings or Except if it also contains any of these strings or Except if it also contains any of these strings or expressions expressions: mysql> select.* and mysql> help.*
-
Select the action to perform.
-
Log: Send a log message into the system logs. The log message includes the expression that matched the content. On log level 6, the message includes the matching content as well.
-
Terminate connection: Immediately terminate the connection. When using the Terminate connection action for the Command event type, and a command matches an expression, the connection is terminated before the command is executed. When using the Terminate connection action, note the following points.
-
Select the Log or Notify action as well so that it is easy to find out why a connection was terminated.
-
If the connection is terminated by a content policy, the Verdict of the connection becomes ACCEPT-TERMINATED.
-
Notify: Send an e-mail or SNMP alert about the event. To configure the alerts, navigate to Basic Settings > Alerting & Monitoring and set the required alerts for the Real time audit event detected (scbAuditRealTime) event.
-
Store in connection database: Add the event to the SPS connection database. These events are displayed in the Alerts column of the Search page. If the column is not visible, click Customize columns....
-
To apply the content policy only for users belonging to specific groups, select Apply this policy only to members of these gateway groups or Apply this policy only to members of these remote groups,  and specify the usergroups as needed. If Apply this policy only to members of these gateway groups or Apply this policy only to members of these remote groups is set, the content policy is applied only to connections of these usergroups.
and specify the usergroups as needed. If Apply this policy only to members of these gateway groups or Apply this policy only to members of these remote groups is set, the content policy is applied only to connections of these usergroups.
-
To add a new rule to the policy, click  and repeat Steps 2-6.
and repeat Steps 2-6.
Note that if you have more than one rules in a policy, SPS evaluates them as follows.
-
SPS evaluates the first (top) rule.
-
If the rule contains Apply this policy only to members of these gateway groups or Apply this policy only to members of these remote groups restrictions, SPS checks if the current user belongs to any of the specified groups. If the groups do not match, SPS skips the rule.
-
If the content matches any entry of the Except if it also contains any of these strings or expressions list, SPS skips the rule.
-
If the content matches any entry of the Take action if the event contains any of the following strings or expressions list, SPS performs the action configured for the rule. Otherwise, SPS skips the rule.
-
If the current rule did not match the content, SPS evaluates the next rule of the policy (if any).
-
Click  . A new content policy is created.
. A new content policy is created.
-
To use the content policy created in the previous steps, select the policy in the channel policy that is used to control the connections.
|

|
NOTE:
It is not required to enable auditing to use content policies. |
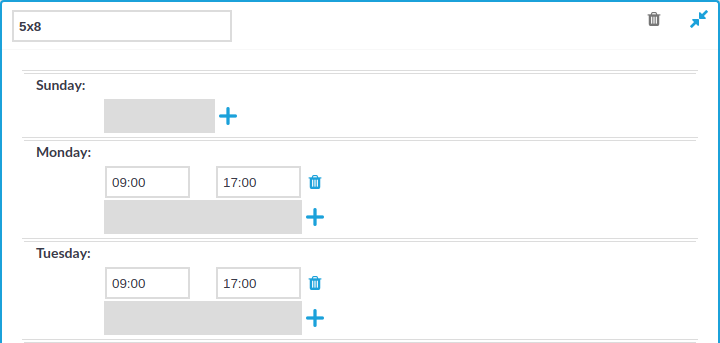
Configuring time policies
The time policy determines the timeframe when the users are permitted to access a particular channel. By default, there is no time-based restriction, all channels are available 7x24.
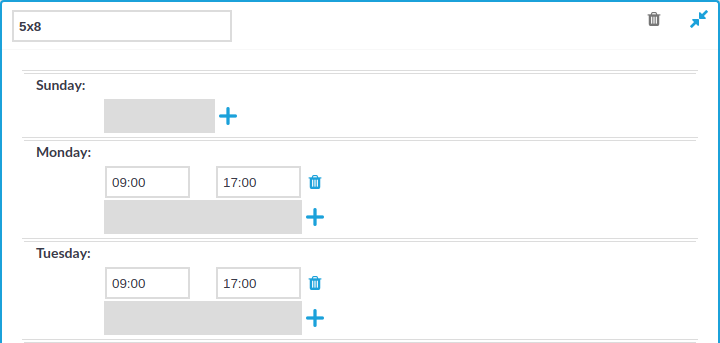
Figure 147: Policies > Time Policies — Configuring time policies
To create a time policy or edit an existing one
-
Navigate to the Time Policies tab of the Policies menu item and click  to create a new time policy. Enter a name for the policy (for example workhoursonly).
to create a new time policy. Enter a name for the policy (for example workhoursonly).
-
Click  to display the days of the week and the allowed intervals.
to display the days of the week and the allowed intervals.
-
Enter the intervals for each day when the users are allowed to access the connection. Use the hh:mm format (for example from 08:00 to 16:00).
-
To add multiple intervals for a day, click  .
.
-
Click  .
.
-
To actually restrict access to a connection or a channel based on the policy created in the previous steps:
to create a new channel policy. Enter a name for the policy (for example, shell_and_backup).
to add a new channel.
in the From field and enter the IP address of the client allowed to use this type of the channel. Repeat this step until all required client IPs are listed.
in the Target field and enter the IP address of the server allowed to use this type of the channel. Repeat this step until all required server IPs are listed.
in the Remote Group field and enter the name of the user group allowed to use this type of the channel. Repeat this step until all permitted groups are listed.
in the Gateway Group field and enter the name of the user group allowed to use this type of the channel. Repeat this step until all permitted groups are listed.
in the Details field and enter the required parameters. For a list of parameters used by the different channels, see Supported SSH channel types and Supported RDP channel types.
to save the list.



 to display the days of the week and the allowed intervals.
to display the days of the week and the allowed intervals.