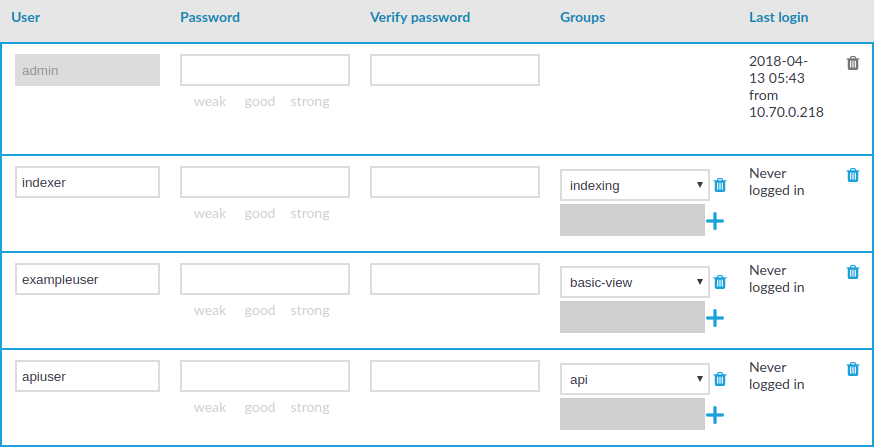
By default, One Identity Safeguard for Privileged Sessions (SPS) users are managed locally on SPS. To add local users in SPS, complete all steps of the following procedure:
-
Create users.
For detailed instructions on how to create local users, see Creating local users in One Identity Safeguard for Privileged Sessions (SPS).
-
Assign users to groups.
For details about how to add a usergroup, see Managing local user groups.
-
Assign privileges to groups.
For information on how to control the privileges of usergroups, see Managing user rights and usergroups.

 .
.
 next to the group.
next to the group.