This section provides information on how to delete a key in your audit keystore.
NOTE: The private keys are stored locally, in your browser.
To delete a key from your audit keystore
-
Navigate to User menu > Audit keystore.
-
Click Unlock private keystore.
The Unlock keystore dialog is displayed.
Enter your master password and click Unlock keystore.
The audit keystore is unlocked.
-
Click
next to the private key that you want to delete.
NOTE: If you delete the last private key from your audit keystore, the audit keystore is reset and next time you add a private key to your audit keystore, you must define a master password again.
Result
The private key is deleted from your audit keystore.

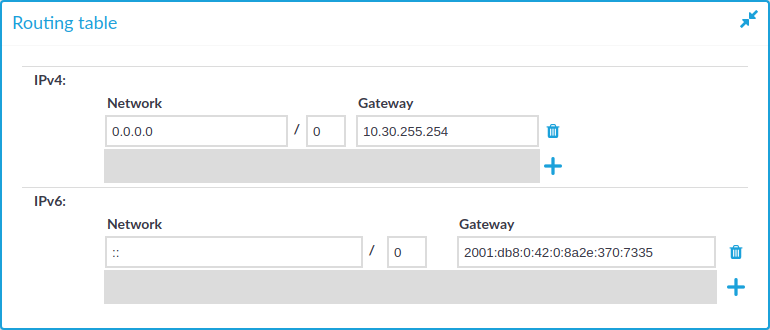
 and
and  icons to add new routes or delete existing ones. A route means that messages sent to the Address/Netmask network should be delivered to Gateway.
icons to add new routes or delete existing ones. A route means that messages sent to the Address/Netmask network should be delivered to Gateway.