From SPS version 7.2, you can play back your session recordings with the Safeguard Desktop Player application started from the SPS UI. With this method, you do not have to start the Safeguard Desktop Player application outside SPS to start replaying your session recording. This method starts a streamable, on-demand playback. As a result, you do not have to wait for a potentially large file to completely download before you start replaying the recording.
NOTE: You can replay session recordings in your browser, or using the Safeguard Desktop Player application. Note that there are differences between these solutions.
For details on the Safeguard Desktop Player application, see Safeguard Desktop Player User Guide.
The following table details the differences between the solutions provided by the browser and the Safeguard Desktop Player application when replaying session recordings.
| Browser | Safeguard Desktop Player | |
|---|---|---|
| Works without installation | ✔ | - |
| Works on any operating system | ✔ | Windows, Linux, Mac |
| Replays session recordings recorded with SPS 5 F4 and newer | ✔ | ✔ |
| Replays TN5250 sessions | ✔ | ✔ |
| Extracts files from SCP, SFTP, HTTP and RDP sessions | - | ✔ |
| Replays HTTP sessions | - | Only exports raw files from the command line |
| Replays X11 sessions | ✔ | ✔ |
| Starts replay while rendering is in progress | ✔ | ✔ |
| Follows 4-eyes connections | - | ✔ |
| Replays live streams in follow mode | ✔ | ✔ |
| Exports to PCAP | - | ✔ |
| Exports audit trail as video | - | ✔ |
| Exports screen content text | - | ✔ |
| Searches in the contents of the session recordings | - | ✔ |
|
|
Caution:
From version 6.13.0, SPS does not support Internet Explorer 11 (IE11) anymore. SPS version 6.12.0 and previous versions continue to support IE11. From SPS version 6.10, the Google WebM Video for Microsoft Internet Explorer plugin is not required for replaying audit trails in your browser. The supported browsers are:
For SPS version 6.9 and earlier versions, even though the One Identity Safeguard for Privileged Sessions (SPS) web interface supports Internet Explorer and Microsoft Edge in general, to replay audit trails, you need to use Internet Explorer 11, and install the Google WebM Video for Microsoft Internet Explorer plugin. If you cannot install Internet Explorer 11 or another supported browser on your computer, use the the Safeguard Desktop Player application. For details, see "Replaying audit trails in your browser" in the Administration Guide and Safeguard Desktop Player User Guide. |
NOTE: From SPS version 6.10 and onwards, you can play video files of audit trails both in central and in cluster environments. Previously, you could play the video files only on the Search Master node in a cluster environment. From SPS version 6.10 and onwards, you can play video files on Search Minion nodes as well.
Prerequisites
-
The Safeguard Desktop Player application is installed and properly configured.
NOTE: Trying to open your session recording in Safeguard Desktop Player while the application is not installed or not properly configured opens a snackbar notification, taking you directly to the Installing Safeguard Desktop Player section in the One Identity Safeguard for Privileged SessionsSafeguard Desktop Player User Guide.
-
At least one recorded session is available on the Search page.
Replaying session recordings with Safeguard Desktop Player started from the SPS UI
With Safeguard Desktop Player installed, and at least one session recorded, you can start replaying started from the SPS UI.
To replay your session recordings with Safeguard Desktop Player started from the SPS UI
-
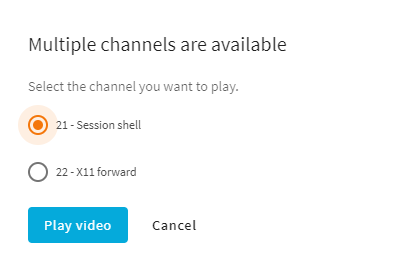
On the Search page, select the session recording you want to replay.
-
To display the details of a connection, click
. This page is called the details view.
-
Next to
, click the playback options (
) and choose
.
Depending on your browser, a confirmation window may appear. Verify that you want to open the Safeguard Desktop Player application.
TIP: You can set your browser to always allow your localhost:<port-number> to open session recordings in Safeguard Desktop Player.
-
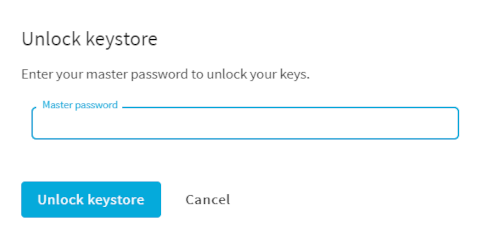
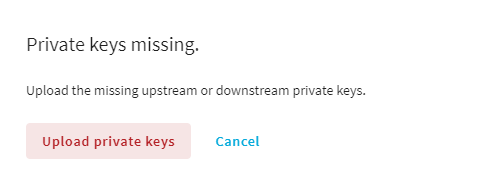
(Optional) For encrypted sessions, upload any missing private keys or certificates, then click
.
Safeguard Desktop Player opens in a separate window.
NOTE: SPS saves your most recently selected replay method for recorded sessions. Depending on which method you used before logging out previously, the SPS UI will display
or
when you next log in to SPS and navigate to the details view of your sessions. You can use replay options (
) to switch between replay methods.
-
Authenticate with your SPS username and password.
The recorded session starts replaying.
For more information about using the Safeguard Desktop Player, see the One Identity Safeguard for Privileged SessionsSafeguard Desktop Player User Guide.


 .
.
 .
. label is displayed in the session details window and you can follow or terminate active sessions.
label is displayed in the session details window and you can follow or terminate active sessions. .
. .
.