InTrust Plug-in requirements
InTrust for Active Directory supports Privilege Manager for Unix version 5.5 and above.
You can collect data from Privilege Manager for Unix hosts running on any of the UNIX platforms supported by InTrust.
To use the MSI installer for the InTrust Reporting Pack, your InTrust Server must use the WindowsSQL Server 2005 as its back-end database.
Installing InTrust Plug-in components
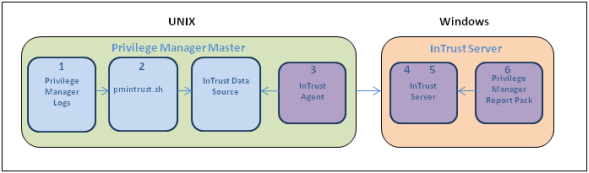
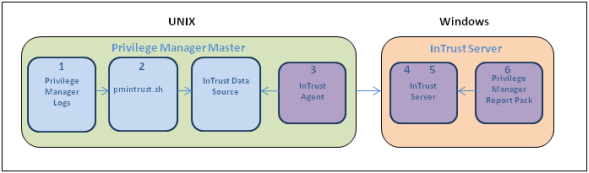
To configure InTrust for Privilege Manager for Unix you must install and configure several components separately. The diagram below shows the major components for the InTrust for Active Directory Plug-in.
Figure 11: InTrust Plug-in components
To install and configure the InTrust for Active Directory Plug-in components
- Install Privilege Manager for Unix and identify which logs you wish to audit.
- Install and configure the pmintrust.sh script to run as the root user to extract the relevant data.
One Identity recommends that you set up a daily cron job to run “pmrun pmintrust.sh” as the pmpolicy service user.
- Install an InTrust Agent on the Privilege Manager for Unix Policy Server.
- Configure the InTrust Server: Finding, Gathering, and Storing.
- Gather Data.
- Configure the InTrust Server: Reporting.
InTrust Plug-in installation prerequisites
Before you install the InTrust for Active Directory components:
Configuring the policy server for the InTrust Plug-in
Run the pmintrust.sh script as the root user.
You might need to edit pmintrust.sh to ensure it can find all relevant event log files.
The script outputs event log data in a format that the InTrust Agent can handle. When the script runs, it creates a separate file for InTrust called /tmp/pm_evlog.intrust containing a plain text version of the events stored in the event log files.
To configure the policy server for the InTrust Plugin
- Extract the pmintrust.tgz archive, located in the utilities directory of the Privilege Manager for Unix distribution media, to the /tmp directory.
# gzip –dc pmintrust.tgz | tar xvf - –C /tmp
pmintrust/
pmintrust/pmpolicy.crontab
pmintrust/root.crontab
pmintrust/pmintrust.profile
pmintrust/pmintrust.sh
- Copy the pmintrust.sh script to the /opt/quest/sbin directory of your policy server.
# cp /tmp/pmintrust/pmintrust.sh /opt/quest/sbin
- If necessary, edit the pmintrust.sh script and modify the EVDIRS and EVGLOB variables so that the script can locate the necessary event log files. For example, if your policy defines the eventlog variable as:
eventlog="/var/log/eventlogs/"+year+"/"+month+"/"+day+"/"+user+"_events.db";
Change the EVDIRS and EVGLOB variables in the pmintrust.sh script to:
EVDIRS=`find /var/log/eventlogs –type d`
EVGLOB="*_events.db"
- Configure the system to run the pmintrust.sh script as the root user.
One Identity recommends that you add a crontab entry as the pmpolicy service user, and configure the cronjob to run pmrun with root user privileges.
The crontab entry is a file called pmpolicy.crontab in the pmintrust.tgz archive.
-
The following crontab entry runs pmrun pmintrust.sh at 10:50 pm everyday:
50 22 * * * /opt/quest/bin/pmrun /opt/quest/sbin/pmintrust.sh
To add the crontab, login (or su) to the pmpolicy service account and run the following command:
$ crontab /tmp/pmintrust/pmpolicy.crontab
Alternatively, you can configure the script to run directly as the root user by creating a root cron job, and skip part b) of this step.
There is a root.cronjob file in the pmintrust.tgz archive.
- If you are using the default profile-based policy, add the pmintrust.profile to your policy to allow the pmpolicy service account to run the pmintrust.sh script as the root user.
To checkout, add, and commit the changes to the policy, run the following pmpolicy command:
# /opt/quest/sbin/pmpolicy checkout –d /tmp
# cp /tmp/pmintrust/pmintrust.profile /tmp/policy_pmpolicy/profiles/
# chown pmpolicy:pmpolicy /tmp/policy_pmpolicy/profiles/pmintrust.profile
# /opt/quest/sbin/pmpolicy add –p profiles/pmintrust.profile –d /tmp
# /opt/quest/sbin/pmpolicy commit –d /tmp –l ″add pmintrust profile″
- Run a new command with Privilege Manager for Unix to verify the change, such as:
# pmrun id
- Allow the cronjob to run at the scheduled time, then verify the InTrust event log file, /tmp/pm_evlog.intrust, was created and contains your test event.