Prompts tab
This tab allows you to view and modify the messages displayed to the user during the authentication process. If you have modified a message in the list, you can always return to the default version of the message that existed before your modifications.
To edit a message
- In the list, click the message you want to edit.
- Edit the message as necessary in the text box below the list.
- Click the Update button to apply your changes.
To roll back to the default version of a message
- In the list, click the message you have modified earlier.
- Click the Default button, and then click the Update button.
Policy tab
This tab allows you to view the current and assign a new Defender Security Policy to the Defender Security Server object.
On this tab, you can use the following elements:
- Policy Shows the Defender Security Policy that is currently assigned to the Defender Security Server object. When there is no Defender Security Policy assigned to the Defender Security Server object, this option displays <undefined>.
- Select Allows you to select a Defender Security Policy to assign to the Defender Security Server object.
- Clear Unassigns the current Defender Security Policy from the Defender Security Server object.
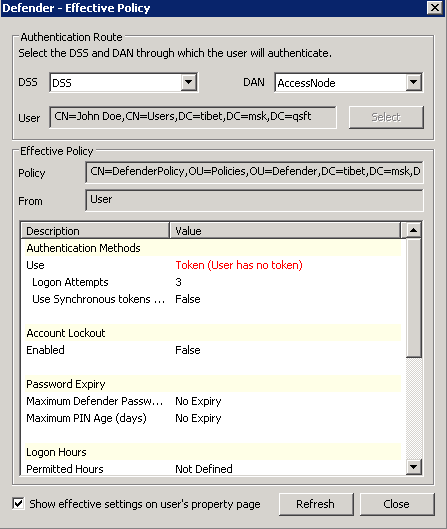
- Effective Click this button to view the Defender Security Policy settings that will apply to a specific user for a particular Defender Security Server/Access Node combination. The window that opens looks similar to the following:
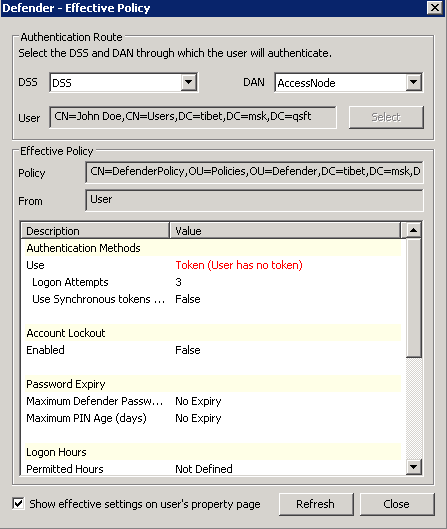
Click the Select button to select the user for whom you want to view the Defender Security Policy that will apply.
The DSS list shows the Defender Security Server that is currently selected for the user. If necessary, select any other Defender Security Server.
The DAN list shows the Access Node that is currently selected for the user. If necessary, select any other Access Node.
The Effective Policy area displays the Defender Security Policy details and authentication settings that will be effective when the user authenticates via Defender.
RADIUS Payload tab
This tab allows you to view the current and assign a new RADIUS payload to the Defender Security Server object.
On this tab, you can use the following elements:
- Payload Shows the RADIUS payload that is currently assigned to the Defender Security Server object. When there is no RADIUS payload assigned to the Defender Security Server object, this option displays <undefined>.
- Select Allows you to select a RADIUS payload to assign to the Defender Security Server object.
- Clear Unassigns the current RADIUS payload from the Defender Security Server object.
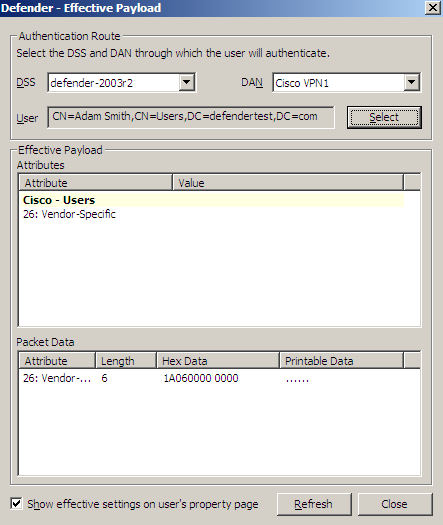
- Effective Click this button to view the RADIUS payload that will apply to a specific user for a particular Defender Security Server/Access Node combination. The windows that opens looks similar to the following:
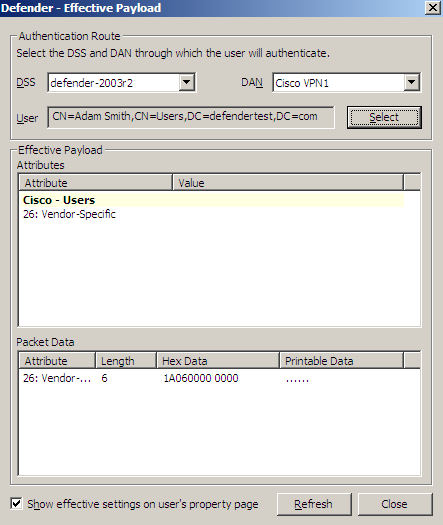
Click the Select button to select the user for whom you want to view the RADIUS payload that will apply.
The DSS list shows the Defender Security Server that is currently selected for the user. If necessary, select any other Defender Security Server.
The DAN list shows the Access Node that is currently selected for the user. If necessary, select any other Access Node.
The Effective Payload area displays the details of the RADIUS payload that will be effective when the selected user authenticates via Defender.
Creating a RADIUS payload object
Remote Access Dial in User Service (RADIUS) is an access-control protocol that verifies and authenticates users based on challenge-response method. This protocol allows a computer to verify your identity, find out what you are allowed to access, and then tell you all of this.
The RADIUS protocol is built around the AAA concept, which stands for authentication (the process of verifying identity), authorization (the process of defining what you are allowed to do), and accounting (the process of monitoring logging statistics and usage information).
The purpose of RADIUS payload is to have the Defender Security Server send information back to the NAS device for reasons such as extra security or for accounting or other reasons specific to the NAS.
To create a RADIUS payload object
- On the computer where the Defender Administration Console is installed, open the Active Directory Users and Computers tool (dsa.msc).
- In the left pane (console tree), expand the appropriate domain node, and then expand the Defender container.
- Right-click the RADIUS Payload container, point to New, and then click Defender RADIUS Payload.
A wizard starts.
- In the Enter a name and description for this RADIUS Payload step, type a name and description for the payload being created. Click Next.
- On the Select the attributes to return when access is approved step, use the Add button to add the attributes you want the RADIUS payload to return, and assign values to those attributes. For more information, see RADIUS payload attributes.