Chapter 13. Reliability and minimizing the loss of log messages
Reliable Log Transfer Protocol™ (RLTP™) interacts with flow control and disk buffering to ensure that the loss of log messages is minimized or is prevented completely. This section explains how each loss prevention method contributes to reliability and minimizing log message loss. Flow control, disk buffering, and RLTP™ are explained in detail elsewhere in the document. In this section, we present a high-level overview of all of these mechanisms and highlight considerations such as:
-
What best practices exist in various scenarios, how to set key parameters
-
When is a log message considered "delivered"
-
Under what circumstances can log loss occur
Each of the following sections discusses a different scenario and uses figures to aid comprehension.
|
|
NOTE:
Each figure depicts a scenario in which the volume of incoming messages makes it necessary to use all buffers and control windows at maximum capacity. |
Important information:
Any of the mechanisms that syslog-ng PE uses to prevent or minimize the loss of log messages only works if the hardware and operating system work normally. When there is an issue with the hardware or operating system that the application and syslog-ng PE run on, log loss may occur. Issues include operating system crash (for example, kernel panic), memory errors, disk errors, power outage, and so on.
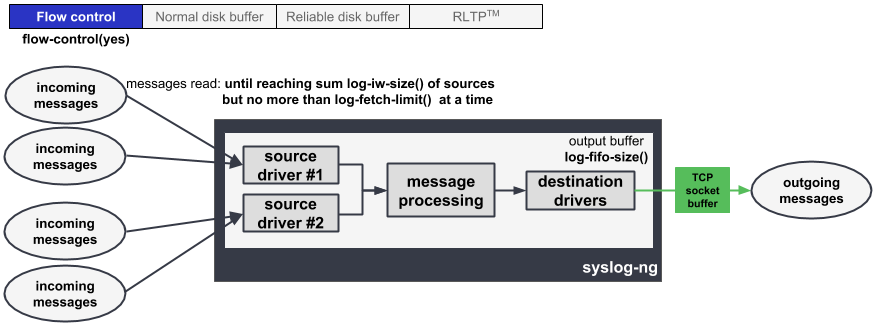
Flow control, no disk buffering, no RLTP™
How it works:
log-iw-size() sets a control window that tracks how many messages syslog-ng PE can accept. Every source has its own control window. If the window gets full, syslog-ng PE stops reading messages from the sources until some messages are successfully sent to the destination(s).
How to set key parameters:
Set flags(flow-control) in the log path.
The output buffer must be large enough to store the incoming messages of every connected source:
log-fifo-size() > sum of log-iw-size() of sources connected to this destination
Benefits:
This configuration minimizes the loss of log messages in the following situations:
-
Unreachable destination server(s): Only as many incoming log messages are read as can be "delivered". When flow control is used, those messages are considered delivered that have been written to the output buffer. When the output buffer is full, syslog-ng PE stops reading messages from the connected sources. This means that no log messages get lost.
NOTE: In case the application is sending its log messages through a blocking I/O socket, then it is the application that stops sending new log messages and waits until the previous batch has been delivered. If the application is not sending logs through a blocking I/O socket, then it will keep sending messages (regardless of whether or not the previous batch has been delivered), and this can result in the loss of log messages. For example, it is not possible to apply flow control in the case of a UDP source.
While this configuration gives you the fastest processing time, it has some limitations. It does not provide protection against the loss of log messages in the following situations:
-
TCP error: In the case of a TCP connection, when messages are sent from the destination drivers to the destination servers, messages are written to the TCP socket. The TCP socket sends an acknowledgement to the destination drivers once it has successfully processed messages. A message is considered "delivered" when no error occurs during the process of writing the data to the socket, and the acknowledgement is received. Note, however, that if something goes wrong after messages have been successfully written to the TCP socket, log messages can still get lost. Also note that TCP errors can occur on both the source and the destination side, and both can cause the loss of log messages.
-
Message loss outside of syslog-ng PE: Because syslog-ng PE stores only a small number of log messages in the memory, it is possible to lose messages outside of syslog-ng. For example, if the output buffer is full because the server is not reachable, syslog-ng PE will not read the source, meaning that the external application that generates the logs can drop the logs. If you want to minimize the risk, use disk buffering. For details, see the section called “Flow control, normal disk buffering, no RLTP™” and the section called “Flow control, reliable disk buffering, no RLTP™”.
-
Message loss when syslog-ng PE is stopped or restarted: When syslog-ng is stopped or restarted, the contents of the output buffers are lost. If you want to minimize the risk, use disk buffering. For details, see the section called “Flow control, normal disk buffering, no RLTP™” and the section called “Flow control, reliable disk buffering, no RLTP™”.
-
When syslog-ng PE is not able to operate normally (for example, when syslog-ng PE crashes due to some unforeseen event): Log messages that were in the output buffer when the issue occurred get lost because those messages are stored in the memory.
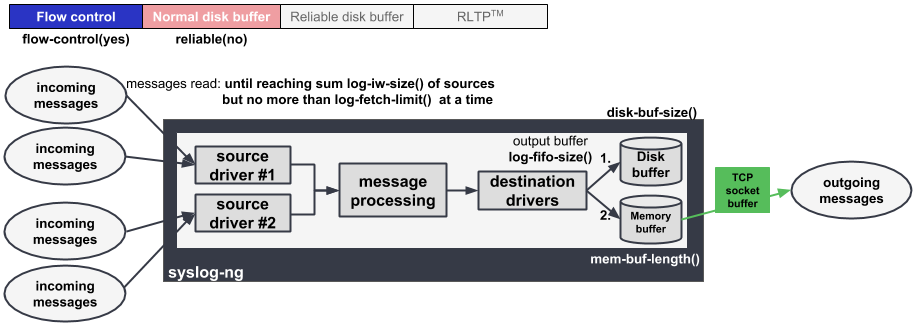
Flow control, normal disk buffering, no RLTP™
How it works:
-
syslog-ng PE puts messages into the disk buffer (set via
disk-buf-size()) when the destination becomes unavailable or when it is not able to process logs as fast as they arrive through the sources. -
When the disk buffer is full, syslog-ng PE puts messages into the memory buffer (set via
mem-buf-length()). When the memory buffer gets full too, then syslog-ng PE stops the source (flow-control mechanism).
How to set key parameters:
Set flags(flow-control) in the log path.
The memory buffer must be large enough to store the incoming messages of every source:
mem-buf-length() > sum of log-iw-size() of sources connected to this destination
Configure disk buffering. For details, see Example 13.1, “Example configuration of normal disk-based buffering”.
Example 13.1. Example configuration of normal disk-based buffering
disk-buffer(
mem-buf-length(20000) # storing 20000 messages in memory, sum log-iw-size of sources should be less than 20000 to use flow-control
disk-buf-size(2147483648) # storing 2 GB of messages on disk
reliable(no)
)Benefits:
This configuration minimizes the loss of log messages in the following situations:
-
Unreachable destination server(s): Only as many incoming log messages are read as can be "delivered". When flow control is used in combination with disk buffering, messages that have been written to the disk buffer and/or the memory buffer are considered delivered. When the memory buffer becomes full, syslog-ng PE stops reading messages from the configured sources. This means that no log messages get lost.
-
Message loss outside of syslog-ng PE: The greatest advantage of this configuration over when no disk buffering is used at all is that when the
log-iw-size()control window is full, the flow-control mechanism stops reading logs from the sources much later. This is because when it is not possible to send logs directly to the destinations, they are first written to the disk and then the memory buffer. It is only after both the disk buffer and the memory buffer have been filled to their full capacity that the sources are stopped. This enables you to minimize the loss of log messages during peak hours or when the network is temporarily down. -
Message loss when syslog-ng PE is stopped or restarted: When syslog-ng is stopped or restarted, the contents of the memory buffer and the disk buffer are flushed to disk, meaning that no log loss occurs.
NOTE: In rare cases, the buffers stored on the disk can become corrupted, in which case syslog-ng PE may not able to process all the logs stored in the disk buffer.
Drawbacks:
One drawback of using disk buffering is that the processing of log messages by syslog-ng PE is slower.
This configuration does not provide protection against the loss of log messages in the following situations:
-
TCP error: In the case of a TCP connection, when messages are sent from the destination drivers to the destination servers, messages are written to the TCP socket. The TCP socket sends an acknowledgement to the destination drivers once it has successfully processed messages. A message is considered "delivered" when no error occurs during the process of writing the data to the socket, and the acknowledgement is received. Note, however, that if something goes wrong after messages have been successfully written to the TCP socket, log messages can still get lost. Also note that TCP errors can occur on both the source and the destination side, and both can cause the loss of log messages.
-
When syslog-ng PE is not able to operate normally (for example, when syslog-ng PE crashes due to some unforeseen event): Log messages that were in the output buffer when the issue occurred get lost because those messages are stored in the memory.
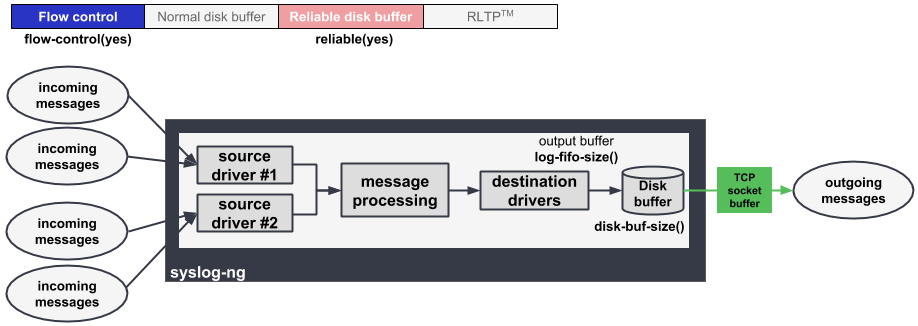
Flow control, reliable disk buffering, no RLTP™
How it works:
syslog-ng puts messages into the disk buffer, until disk-buffer size reaches disk-buf-size(). Above that size, flow control is triggered. syslog-ng PE completely stops reading incoming messages from the source, making the control window (governed by log_iw_size()) fill up and blocking the sources.
In this configuration, log messages are stored on the disk (and not in the memory), which increases reliability.
How to set key parameters:
Set flags(flow-control) in the log path.
Configure disk buffering. For details, see Example 13.2, “Example configuration of reliable disk-based buffering”.
Example 13.2. Example configuration of reliable disk-based buffering
disk-buffer(
mem-buf-size(10485760) # storing 10 MB of messages in memory and on disk
disk-buf-size(2147483648) # storing 2 GB of messages only on disk
reliable(yes)
)Benefits:
This configuration minimizes the loss of log messages in the following situations:
-
Unreachable destination server(s): Only as many incoming log messages are read as can be "delivered". When flow control is used in combination with disk buffering, those messages are considered delivered that have been written to the disk buffer. As soon as the disk buffer is full, syslog-ng PE stops reading messages. This means that no log messages get lost.
-
Message loss outside of syslog-ng PE: One of the advantages of this configuration over when no disk buffering is used at all is that when the
log-iw-size()control window is full, the flow-control mechanism stops reading logs from the sources much later. This is because when it is not possible to send logs directly to the destinations, they are written to the disk. It is only after the disk buffer has been filled to its full capacity that the sources are stopped. This enables you to minimize the loss of log messages during peak hours or when the network is temporarily down. -
Message loss when syslog-ng PE is stopped or restarted: When syslog-ng is stopped or restarted, the contents of the disk buffer do not get lost, greatly increasing reliability.
Also note that the memory buffer is only used as a cache in this configuration. Any data stored in the memory has already been written to the disk buffer, which, again, results in more reliability.
NOTE: In rare scenarios, the buffers stored on the disk can become corrupted, in which case syslog-ng PE may not able to process all the logs stored in the disk buffer.
-
When syslog-ng PE is not able to operate normally (for example, when syslog-ng PE crashes due to some unforeseen event): No messages get lost because the disk buffer is persistent and when the disk buffer is full, syslog-ng PE stops reading messages from the sources. When syslog-ng PE is restarted after a crash, it automatically recovers any unsent messages from the disk buffer and the output buffer. After the restart, syslog-ng PE sends the saved messages to the destination.
Drawbacks:
One drawback of using reliable disk buffering is that the processing of log messages by syslog-ng PE is slower than when messages are stored in the output buffer only, or when using normal disk buffering.
This configuration does not provide protection against the loss of log messages in the following situations:
-
TCP error: In the case of a TCP connection, when messages are sent from the destination drivers to the destination servers, messages are written to the TCP socket. The TCP socket sends an acknowledgement to the destination drivers once it has successfully processed messages. A message is considered "delivered" when no error occurs during the process of writing the data to the socket, and the acknowledgement is received. Note, however, that if something goes wrong after messages have been successfully written to the TCP socket, log messages can still get lost. Also note that TCP errors can occur on both the source and the destination side, and both can cause the loss of log messages.