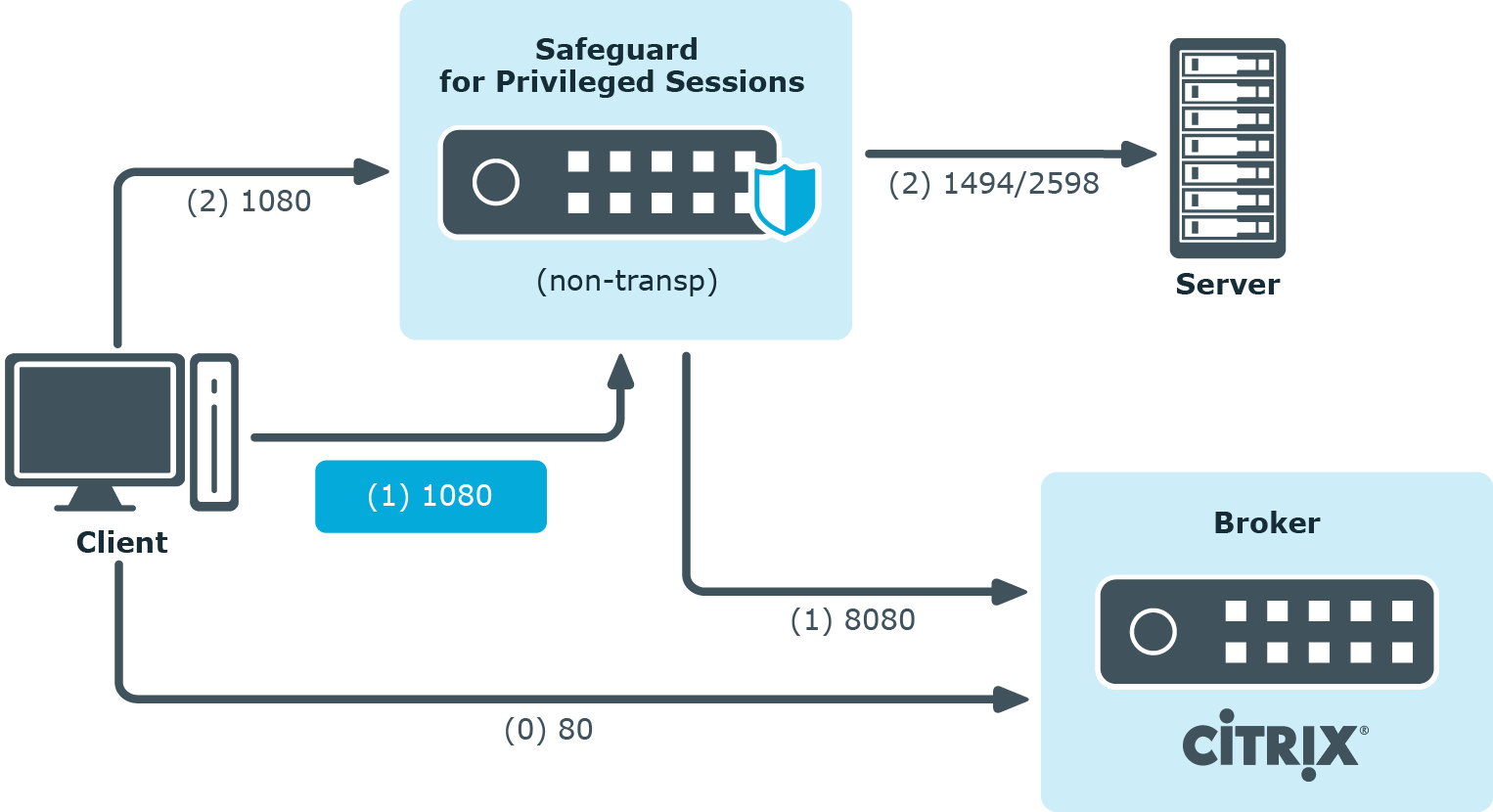
This section enlists the available One Identity Safeguard for Privileged Sessions (SPS) deployment scenarios in a Citrix environment. The text on the arrows are formatted in (<step number>) <target port> format. The target ports define the protocols used in the communication:
-
80: Web service, HTTP: the list of available resources fetched in an XML format from the broker (v12 and v11 with Citrix Virtual Apps (formerly known as Citrix XenApp) only). The broker sends all the necessary information, including secure gateway and server addresses to the client.
-
8080: XML service, HTTP+XML: application discovery, load balancing (v12 and v11 with Citrix Virtual Apps (formerly known as Citrix XenApp) only), used to fetch target to the application/desktop by the client from the broker (used for load balancing, and so on).
-
443: XML service access or SOCKS/ICA or CGP/ICA wrapped in TLS. The client communicates with the secure gateway on this port for everything.
-
1080: SOCKS. The client can be configured to access the target server and the broker using a SOCKS proxy.
-
1494: Plain ICA.
-
2598: CGP/ICA (reliable mode enabled).
|
|
Caution:
Accessing Citrix Virtual Desktops (formerly known as Citrix XenDesktop) is supported only in the following scenarios. Only reliable connections (CGP) are supported. |
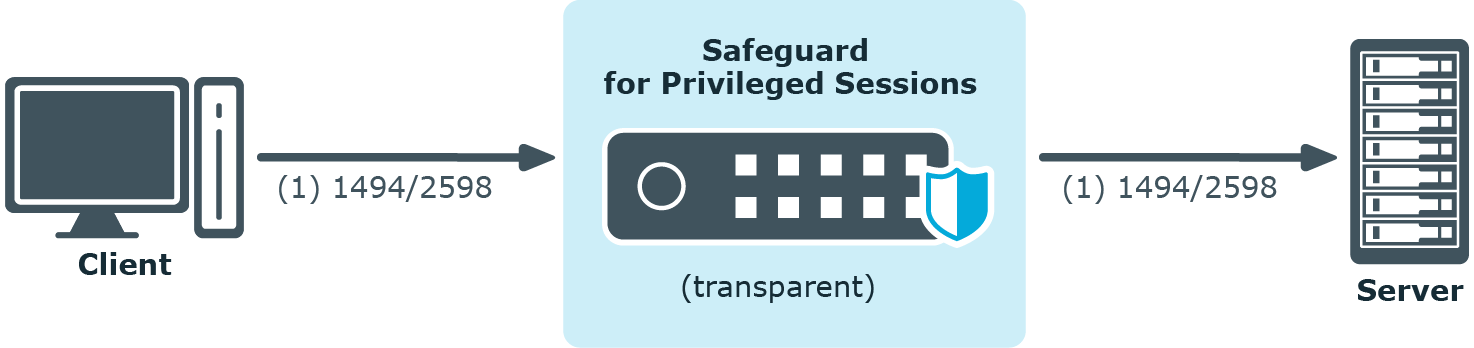
Client - SPS - Server (Transparent mode)
The SPS is deployed between the client and the server and the clients use predefined connection files or Program Neighbourhood, without a broker or secure gateway. The clients try to connect to their original ICA/CGP server.
Figure 210: Client - SPS - Server (Transparent mode)
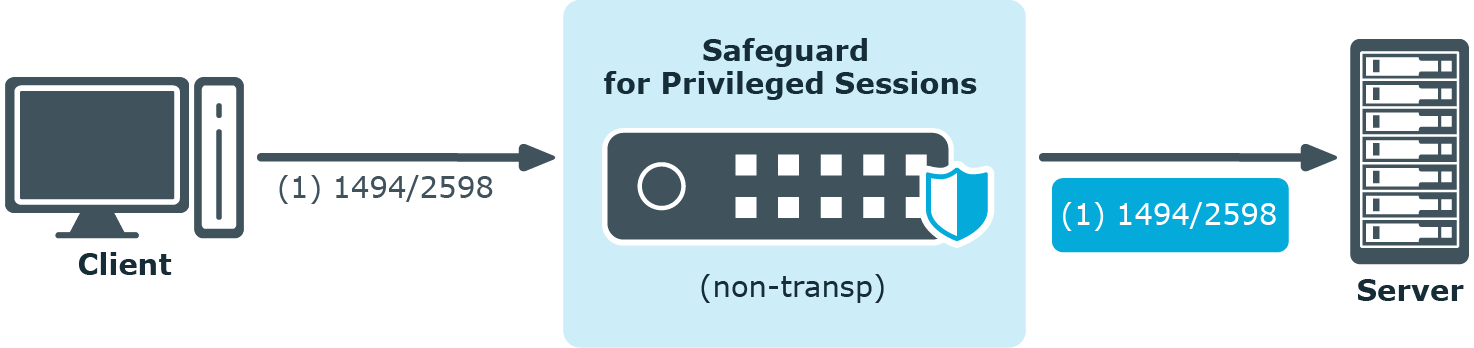
Client - SPS - Server (Non-transparent mode)
The SPS is deployed between the client and the server and the clients use predefined connection files or Program Neighbourhood, without a broker or secure gateway. The clients try to connect to SPS, which can distinguish between the potential targets for example by source IP, or by having multiple IP addresses itself.
Figure 211: Client - SPS - Server (Non-transparent mode)
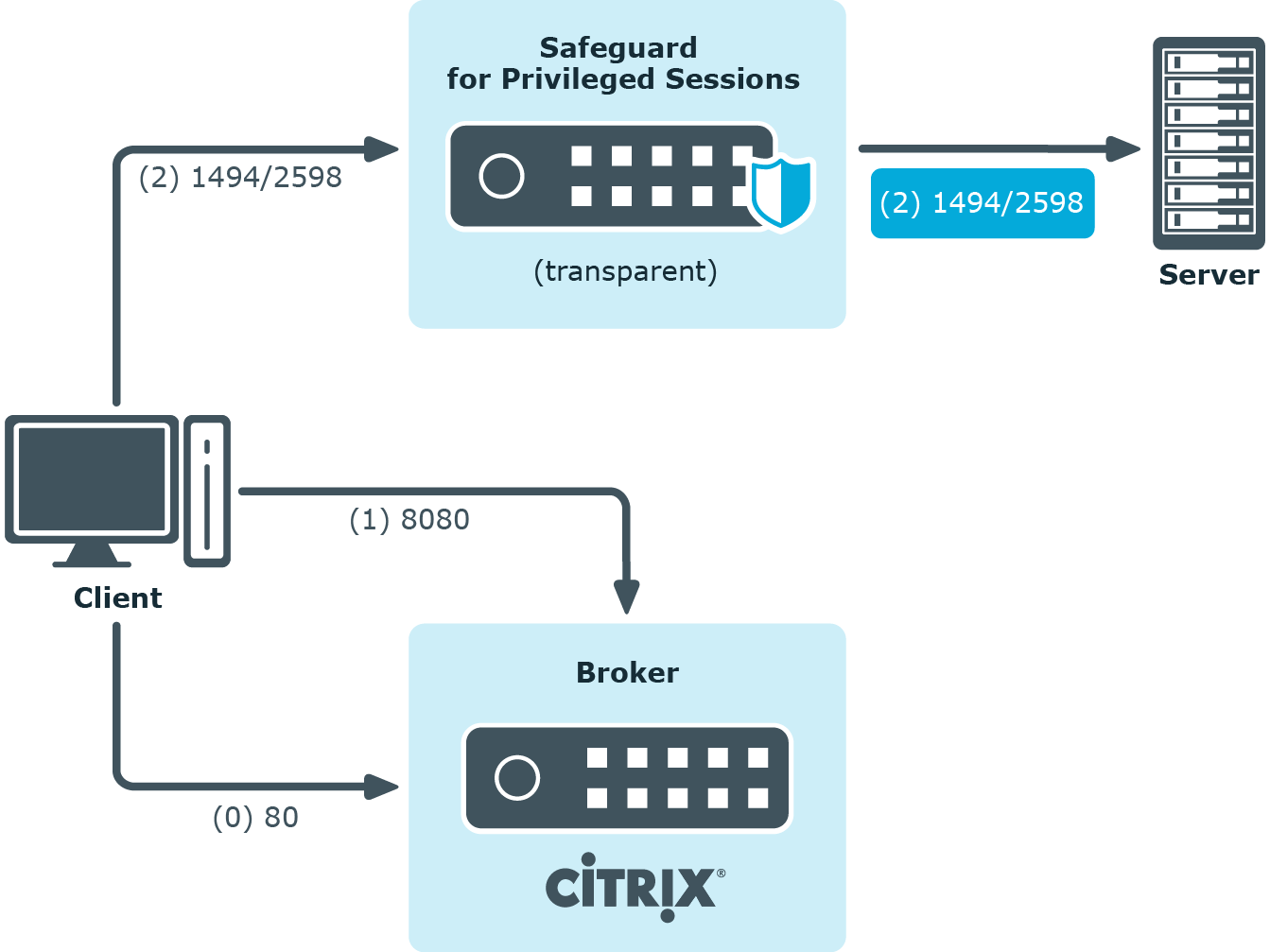
Client - Broker - SPS - Server (Transparent mode)
The clients are using a farm broker which gives them a list of the available applications and servers, but they do not use a secure gateway in the network. The SPS is placed between the clients and the servers in transparent mode, and it catches the connections when the clients try to connect to the server IP addresses they got from the broker.
Figure 212: Client - Broker - SPS - Server (Transparent mode)
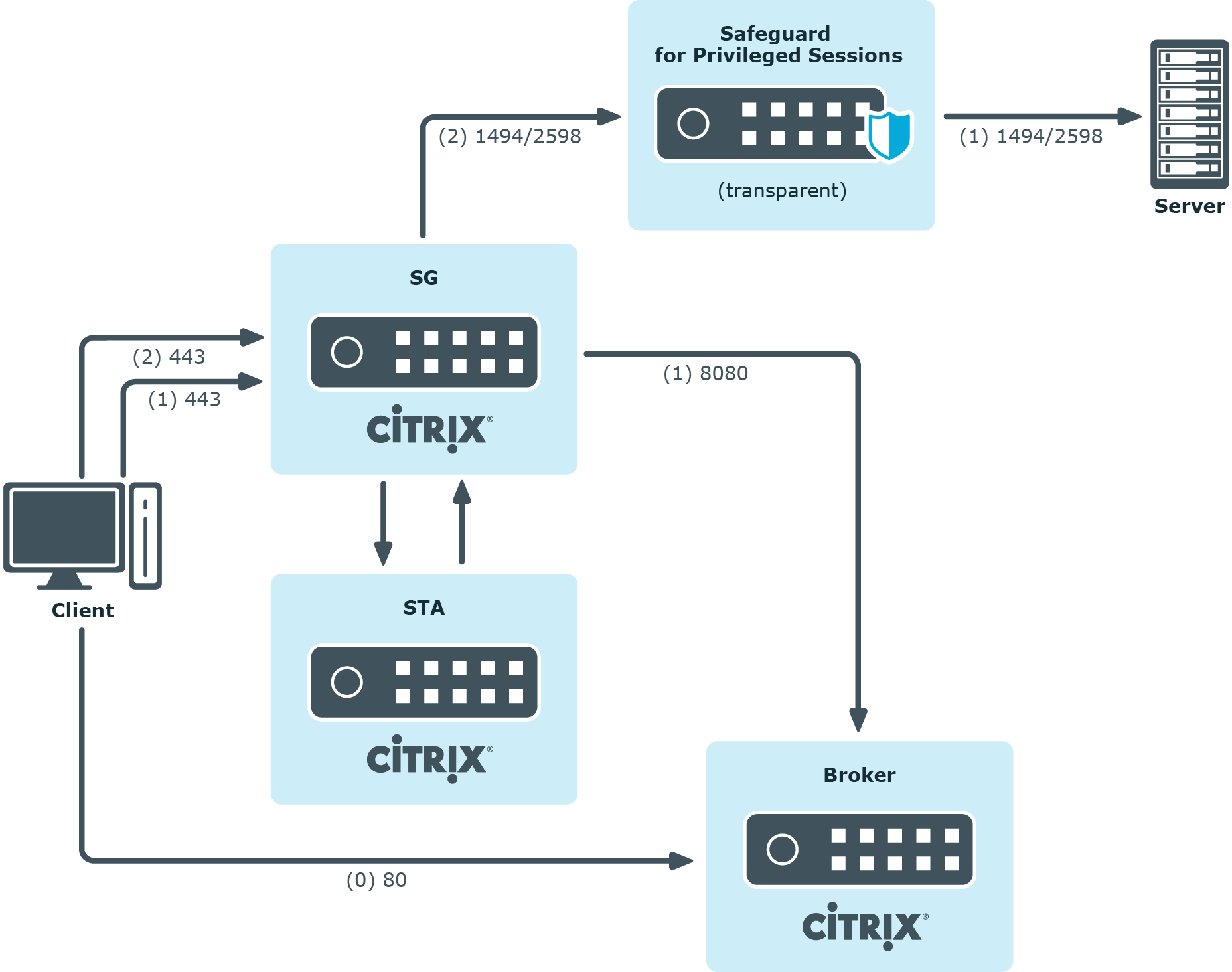
Client - Broker - original secure gateway - Secure Ticket Authority (STA) - SPS - Server
In this setup, a secure gateway is used in the network and the SPS is placed between this gateway and the servers in transparent mode. The clients connect to the broker for the list of available applications/servers and then make their further connections through the original secure gateway. That gateway forwards the connections either to the broker or to the CGP/ICA servers, which latter the SPS intercepts and audits/controls.
Figure 213: Client - Broker - original secure gateway - Secure Ticket Authority (STA) - SPS - Server
Client - Broker - SPS as socks proxy - Server
In this setup, the SPS acts as a SOCKS proxy for the client. It can be set either manually or specified by the broker. The client then makes all its connections to the broker or to the server using SPS as a proxy and hence it can audit/control these connections.
Figure 214: Client - Broker - SPS as socks proxy - Server
To configure such a scenario, you must set the ICA Connection Policy as follows:
-
Enter the IP address of SPS into the To field. This must be the public IP address that the clients will target.
-
Select Inband destination selection, and list the IP addresses or networks of target servers in the Targets field. (For details, see Configuring inband destination selection.)
-
Select Act as a SOCKS proxy.
-
Add the IP addresses of your brokers to the Brokers field.

