[starling_auto_provision]
This section contains the options related to auto-provisioning your Starling 2FA account. To turn on auto-provisioning, you have to specify both attributes.
To be able to use auto-provisioning, you must configure the [ldap_server] section.
NOTE: Prerequisite for end-users: Starling 2FA Android Application installed on the end-user's phone. If the Application is not yet installed, at the first authentication attempt, the end-user will receive instructions through text message about installing the Application. After finishing the installation, they can re-initiate the authentication process.
Declaration
[starling_auto_provision] email_attribute=<LDAP-attribute-of-user-email-address> phone_attribute=<LDAP-attribute-of-user-phone-number>
email_attribute
| Type: | string |
| Required: | no |
| Default: | N/A |
Description: The LDAP attribute name of the user's email address.
phone_attribute
| Type: | string |
| Required: | no |
| Default: | N/A |
Description: The LDAP attribute name of the user's phone number. Make sure that the phone numbers in LDAP adhere to the following formatting rules:
-
The phone number must start with the + character and the country code, for example, +11234567890.
-
The phone number must not include any other characters, that is, must not include hyphen (-), space, or any other separator characters.
Otherwise, SPS cannot parse the phone number and therefore authentication will be unsuccessful (the log will contain an error indicating issues with invalid user).
[auth]
This section contains the options related to authentication.
Declaration
[auth] prompt=Press Enter for push notification or type one-time password: disable_echo=yes
prompt
| Type: | string |
| Required: | no |
| Default: | Press Enter for push notification or type one-time password: |
Description: SPS displays this text to the user in a terminal connection to request an OTP interactively. The text is displayed only if the user uses an OTP-like factor, and does not send the OTP in the connection request.
disable_echo
| Type: | boolean (yes|no) |
| Required: | no |
| Default: | no |
Description: For better security, you can hide the characters (OTP or password) that the user types after the prompt. To hide the characters (replace them with asterisks), set disable_echo to yes.
[connection_limit by=client_ip_gateway_user]
This section contains the options related to limiting parallel sessions.
limit
| Type: | integer |
| Required: | no |
| Default: | 0 |
Description: To limit the number of parallel sessions the gateway user can start from a given client IP address, configure limit. For an unlimited number of sessions, type 0.
[authentication_cache]
This section contains the settings that determine how soon after performing a 2FA/MFA authentication the user must repeat the authentication when opening a new session.
After the first
In other words, after opening the first session and authenticating on
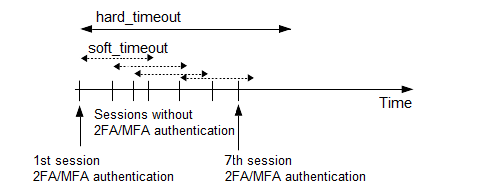
soft_timeout
| Type: | integer [in seconds] |
| Required: | yes, if you want caching |
| Default: | N/A |
| Min value: | 0 |
| Max value: | 2147483647 |
Description: The time in seconds after which the SPS plugin requires a new
hard_timeout
| Type: | integer [in seconds] |
| Required: | yes, if you want caching |
| Default: | N/A |
| Min value: | 0 |
| Max value: | 2147483647 |
Description: The time in seconds after which the SPS plugin requires a new
reuse_limit
| Type: | integer [number of] |
| Required: | Optional |
| Default: | 0 |
| Min value: | 0 |
| Max value: | 2147483647 |
Description: The number of times that you can reuse the authentication cache before the SPS plugin requires from you a new authentication for the next session. The default is 0, which means that the authentication cache is not unlimited, but it is turned off.
In the example, if reuse_limit is set to 5, and you successfully authenticated with multi-factor authentication, the next 5 authentications are bypassed in the next 90 seconds (hard_timeout), if there is no gap bigger than 15 seconds (soft_timeout) between the authentications.
If any of the hard_timeout, soft_timeout, or reuse_limit parameters, which operate independently from one another, exceed the configured limit, the SPS plugin requires you to authenticate for the new session.
