Removing members from an Office 365 Group with the Management Shell
You can use the Remove-QADO365GroupMember cmdlet on the Active Roles Management Shell interface to remove members from an Office 365 (O365) Group.
For more information on removing a member from an O365 Group using the Management Shell interface, see the Active Roles PowerShell Reference Guide.
Scheduling an Azure object synchronization task
You can use the Sync Azure O365 Objects scheduled task of the Active Roles Console (also known as the MMC interface) to synchronize the following Azure objects and Azure tenant information between the Azure Portal and the Active Roles database:
-
Azure users
-
Azure guest users
-
Azure contacts
-
M365 groups
-
The Azure tenant ID and environment information (that is, whether the tenant is set to a Non-federated, Synchronized identity, or Federated environment configuration.
To configure a scheduled Azure object synchronization task
-
In the Active Roles Console, in the Active Directory (AD) tree, navigate to Configuration > Server Configuration > Scheduled Task > Builtin.
-
Open the scheduling properties of the Sync Azure O365 Objects built-in scheduled task. To do so, either:
-
Double-click Sync Azure O365 Objects, then in the Properties window, open the Schedule tab.
-
Right-click Sync Azure O365 Objects, then click Properties > Schedule.
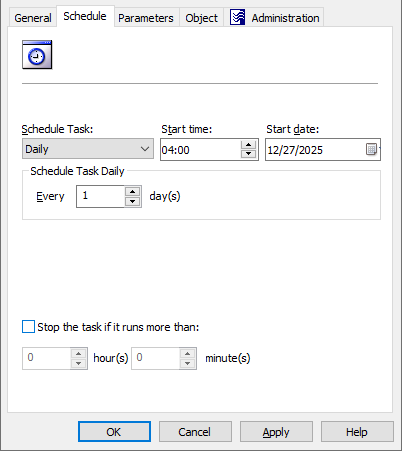
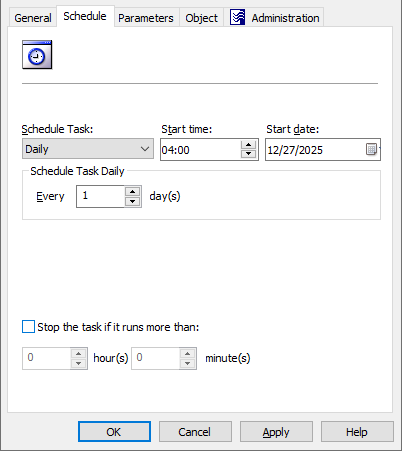
Figure 164: Active Roles Console – Scheduling properties of the scheduled task
-
To customize the scheduling settings of the task, open the Properties > Schedule tab.
-
To change the default scheduling settings of the task for your needs, modify the options of the Schedule tab accordingly:
-
Schedule Task: Specifies how frequently Active Roles runs the task (each hour, every day, or on a weekly/monthly basis). By default, tasks are run on a daily basis.
-
Start time and Start date: These settings specify the time and date of the first scheduled task run. These settings are not available if Schedule Task is set to Once or When Service starts.
-
Schedule Task Hourly / Daily / Weekly / Monthly: These settings specify the time interval of repeating the configured task.
For example, setting Schedule Task to Hourly lets you specify the time interval between two task runs in hours and minutes, while setting it to Weekly lets you specify not just the number of weeks between two task runs, but also the days of the week on which Active Roles must run the task.
NOTE: This setting is not available if Schedule Task is set to Once or When Service starts.
-
Stop the task if it runs more than: When selected, this setting sets a timeout (in hours and minutes) after which the task stops if it runs longer than the specified interval.
TIP: If the contents of the Members and/or Azure Properties actions in the Active Roles Web Interface for an Azure object differ from the object information available on the Azure Portal, One Identity recommends running the scheduled Sync Azure O365 Objects task manually to synchronize the Azure objects and Azure tenant information.
Managing Azure Security Groups
Active Roles supports CRUD (create, read, update and delete) operations for Azure AD Security groups and also lets you specify owners and add/remove members to or from existing Azure AD Security groups in your organization.
Azure Security groups are security principals used to secure objects (such as Azure users, Azure guest users, devices, applications, or other Azure Security groups) in Azure AD. Typically, Azure Security groups are set up to delegate application licenses or other resource permissions to users based on their group membership. For more information on Azure Security groups, see Groups in Microsoft 365 and Azure in the Microsoft 365 community documentation.
You can administer Azure Security groups via the Active Roles Web Interface.
Creating an Azure Security Group with the Web Interface
You can use the Active Roles Web Interface to create and enable new Azure security groups.
For more information on Azure Security groups, see Groups in Microsoft 365 and Azure in the Microsoft 365 community documentation.
To create a new Azure Security group
-
Navigate to Directory Management > Tree > Azure > <azure-tenant-name> > Security Groups.
The list of existing Azure Security groups in the selected Azure tenant appears.
-
In the right-side pane, click New Group.
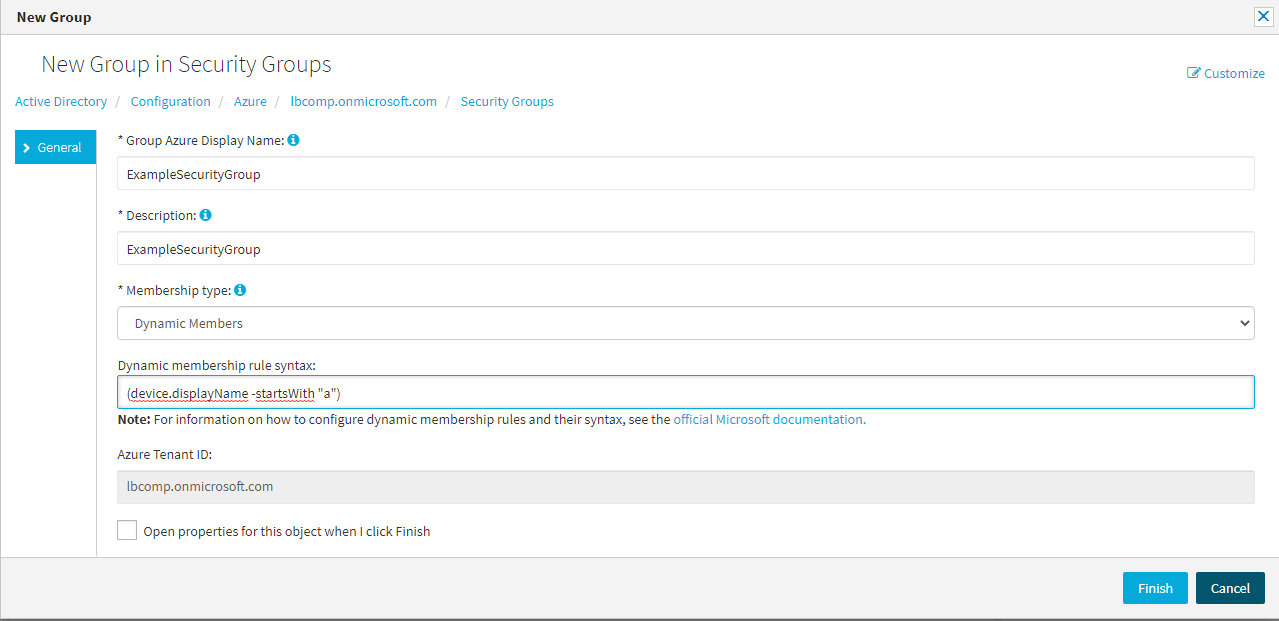
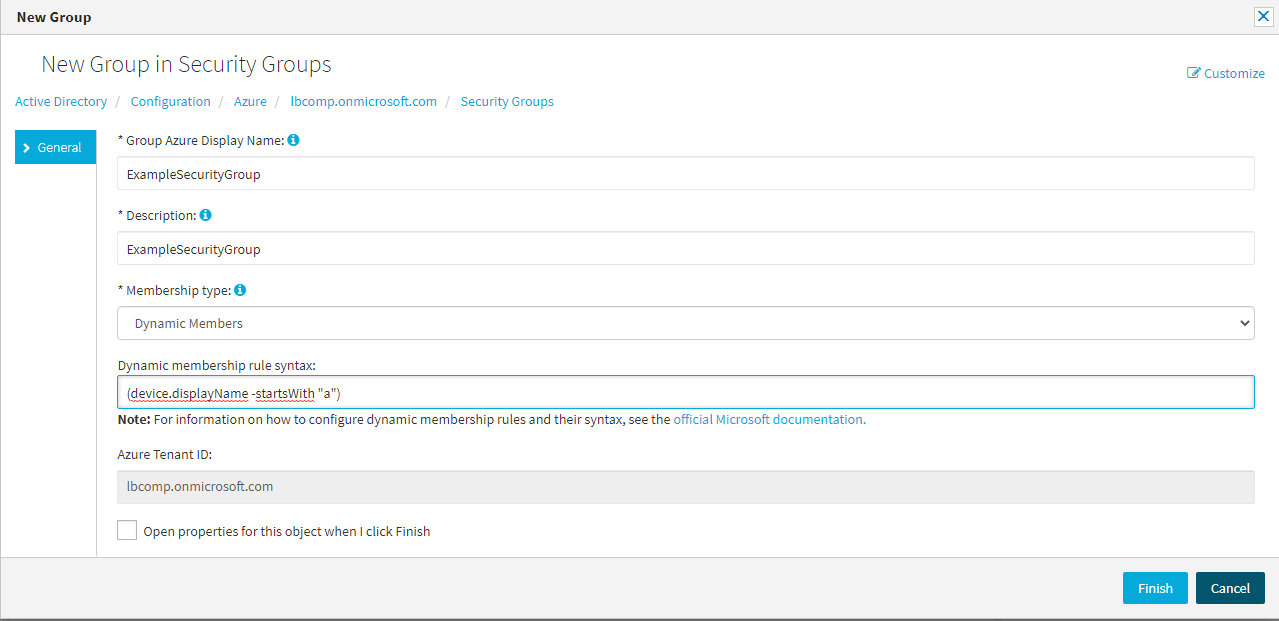
The New Group in Security Groups window appears.
-
Specify the Group Azure Display Name of the configured group.
TIP: You can configure multiple groups with the same Group Azure Display Name in the same Azure tenant.
-
Provide a short Description for the group.
-
Configure the Membership type of the group:
-
Assigned: When selected, you can add or remove members to or from the group manually later. For more information, see Adding or removing members from an Azure Security Group with the Web Interface.
-
Dynamic Members: When selected, Active Roles sets up the group as a dynamic membership group, and will automatically update group membership based on the configured Dynamic membership rule syntax.
TIP: Consider the following when configuring the Membership type:
-
Select Dynamic Members to quickly configure a group based on a certain membership logic. For example, if you need to set up a group for employees from the same geographical location, business unit, or functional area, One Identity recommends configuring the group with Dynamic Members.
-
If you select Dynamic Members, you will not be able to manually add or remove members to or from the Azure Security group, unless you change its Membership type to Assigned later. However, you can still manually configure the owner(s) for a dynamic Azure Security group, as described in Adding or removing owners from an Azure Security Group with the Web Interface.
-
Although the Membership type drop-down setting does not offer a separate Dynamic Devices option, you can actually set up dynamic Azure Security groups in Active Roles with the appropriate dynamic device membership rules (such as device.displayName). However, the Active Roles Web Interface cannot display member devices and applications.
-
You can always change the Membership type later by navigating to the following option of the Active Roles Web Interface:
Directory Management > Tree > Azure > <azure-tenant-name> > Security Groups > <azure-security-group-name> > Azure Properties > General.
-
Changing the Membership type from Dynamic Members to Assigned later will keep the last set of members that were dynamically assigned to the group.
-
If you set the Membership type to Dynamic Members, specify the Dynamic membership rule syntax. Active Roles will send the logic configured in this field to Azure to automatically assign or remove members to or from the group later.
NOTE: Consider the following when using the Dynamic membership rule syntax setting:
-
This setting is enabled only if Membership type is set to Dynamic Members. However, in that case, it is mandatory and cannot be empty.
-
The specified dynamic membership rule must meet all rule syntax requirements, otherwise the window will return an error. For more information on the available membership rule properties, operators and values, see Dynamic membership rules for groups in Azure Active Directory in the Microsoft 365 documentation.
-
Whenever you modify the dynamic membership rule of a dynamic O365 group, it can take several minutes for Azure to update the list of group members in the Directory Management > Tree > Azure > <azure-tenant-name> > Security Groups > <azure-security-group-name> > Dynamic Members window.
-
To complete the configuration of the new Azure Security group, click Finish.
The new Azure Security group will appear under the Directory Management > Tree > Azure > <azure-tenant-name> > Security Groups node.