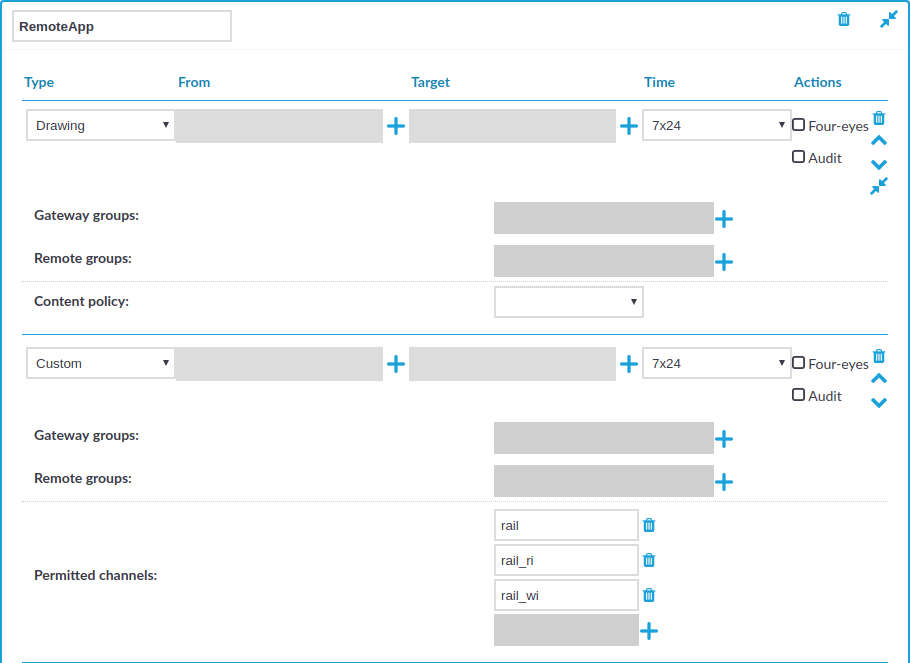
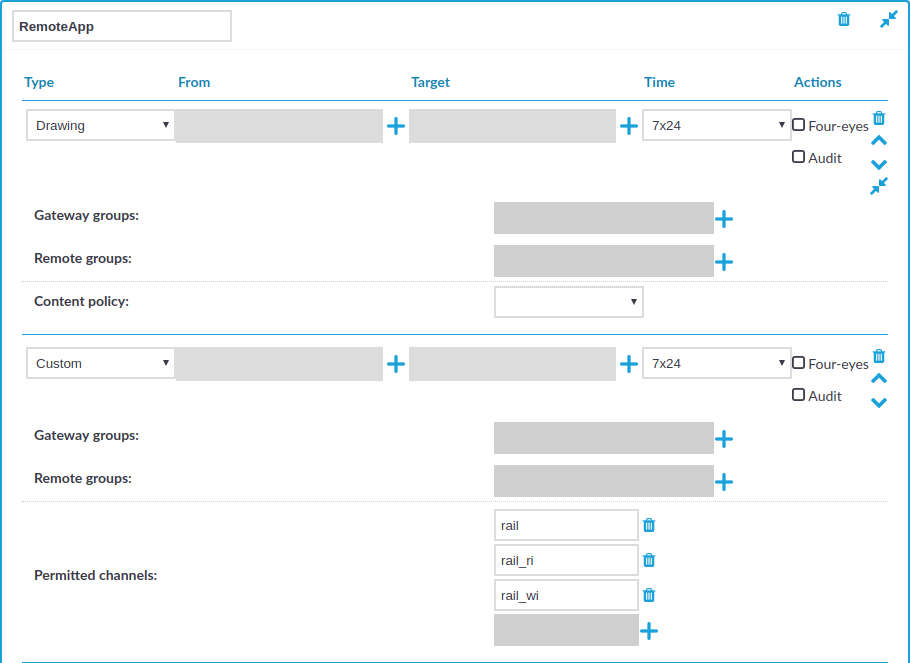
Configuring RemoteApps
Overview
RemoteApps use RDP channels that are denied by default. When configuring RDP connections for RemoteApps on One Identity Safeguard for Privileged Sessions (SPS), create a custom channel policy which enables the following channels:
-
Drawing
-
rail
-
rail_ri
-
rail_wi
Figure 224: RDP Control > Channel Policies — Configuring the required channels for RemoteApps
Prerequisites
-
You must disable the Use advanced RemoteFX graphics for RemoteApp group policy on the RDP server.
The policy is available at Computer Configuration > Policies > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host > Remote Session Environment > Use advanced RemoteFX graphics for RemoteApp.
-
You must have the Remote Desktop (RD) Licensing role installed.
To configure RemoteApps
-
Navigate to RDP Control > Channel Policies.
-
Click  to create a new channel policy.
to create a new channel policy.
-
Enter the name for the channel policy.
-
Choose Drawing as the channel type.
-
Click  to add an additional channel type.
to add an additional channel type.
-
Choose Custom as the second channel type.
-
In Permitted channels, click  to add the following channels:
to add the following channels:
(You have to click  for each channel.)
for each channel.)
-
Click  to save the channel policy.
to save the channel policy.
-
You have created a channel policy for RemoteApps.
When you configure a connection that uses RemoteApps in RDP Control > Connections, select this channel policy as the Channel policy of the connection.
Configuring the RemoteApp Launcher
The RemoteApp Launcher enables users the access they need to an application without revealing credentials and passwords. By using the RemoteApp Launcher, you can protect shared credentials and limit an end user’s access to an allowed or required application.
To configure RemoteApp Launcher-specific settings on the SPS side
-
In SPS, configure a credential store plugin with the get_remote_app_credentials method implemented. This is required for negotiating application credentials with SPS.
Ensure that you specify the asset parameter. If your SPS is linked to SPP, you must also specify the connection name parameter.
Example: do_get_remote_app_credentials configuration
def do_get_remote_app_credentials(self):
try:
credential = self._get_credential_for_asset("password", self.remote_app_asset, self.remote_app_account)
return {"passwords": [credential]}
except SafeguardException as exc:
self.logger.error("Error checking out %s for %s@%s: '%s'", "password", self.remote_app_account, self.remote_app_asset, exc)
return None
For more information on how to configure a custom credential store plugin, see Creating custom Credential Store plugins.
-
Optionally, to enable automatic password handling by the RemoteApp Launcher, configure a custom AA plugin.
By specifying the asset and account name parameters in an AA plugin, the RemoteApp Launcher will not prompt the user for these credentials and will start the configured application without the user having to know any credentials.
For more information on how to configure a custom AA plugin, see Creating custom Authentication and Authorization plugins.
-
Configure RemoteApps in SPS.
For more information, see Configuring RemoteApps.
-
Configure an RDP connection that uses RemoteApps in RDP Control > Connections and select the created RemoteApps channel policy as the Channel policy of the connection.
To configure RemoteApp Launcher-specific settings on the Windows side
-
Download the RemoteApp Launcher.
-
Install Remote Desktop Services (RDS).
-
Create a RemoteApp program and make the following settings:
-
For the RemoteApp program location, enter the path to your RemoteApp Launcher, for example, C:\Program Files\OneIdentity\RemoteApp Launcher\OI-SG-RemoteApp-Launcher.exe.
-
Specify to always use command-line parameters as shown in the example below:
"C:\Program Files\DBeaver\dbeaver.exe" --args "-con user={username}|password={password}|host=localhost|driver=PostgreSQL|database={asset}|name=work|connect=true" --enable-debug
Table 10: List of parameters
| help |
No |
Create the help message. |
| cmd |
Yes |
Specifies the application to launch. Either the path to an executable or command alias. |
|
args |
Yes |
Specifies the CLI args to pass to <cmd>. It must contain the {username}, {password} and {asset} template options, which will be expanded with the corresponding information. |
|
use-path |
No |
Specifies whether to look up the cmd argument in the $PATH variable. The default setting is false. When this flag is set to false, you need to specify the full path to the executable. |
|
enable-debug |
No |
Specifies whether to write debug logs. The default setting is false.
The logs are available in the C:\Users\<username>\AppData\Roaming\OneIdentity\OI-SG-RemoteApp-Launcher folder.
The logs are rotated daily and the file name format is oi_sg_rci_<yyyymmdd>. |
The process and the arguments template is defined by the --cmd and --args command line arguments. In the arguments template, the RemoteApp Launcher replaces the {username} {password} and {asset} with data read from the dynamic virtual channel.
Example: RemoteApp Launcher configuration to start the DBeaver application
C:> C:\Program Files\OneIdentity\RemoteApp Launcher\OI-SG-RemoteApp-Launcher.exe --cmd "C:\Program Files\DBeaver\dbeaver.exe" --args "-con user={username}|password={password}|host=localhost|driver=PostgreSQL|database={asset}|name=work|connect=true" --enable-debug
-
Disable the Use advanced RemoteFX graphics for RemoteApp group policy on the RDP server.
The policy is available at Computer Configuration > Policies > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host > Remote Session Environment > Use advanced RemoteFX graphics for RemoteApp.
You must have the Remote Desktop (RD) Licensing role installed.
Expected result
An end user can open a required application without any credentials by simply starting the RemoteApp Launcher.
Configuring SPS to enable exporting files from audit trails after RDP file transfer through clipboard or disk redirection
RDP-specific settings > Configuring SPS to enable exporting files from audit trails after RDP file transfer through clipboard or disk redirection
In SPS versions 6.2 and later, you can export files from audit trails after RDP file transfer through clipboard.
In SPS versions 6.5 and later, you can export files from audit trails after RDP file transfer through disk redirection too.
NOTE: You can export files from audit trails that were recorded before the SPS versions described above, if the Clipboard or Disk redirect channel was recorded.
To export files from these audit trails, make sure that you have the appropriate version of the Safeguard Desktop Player installed.
For more information on the process in the Safeguard Desktop Player application, see Exporting files from an audit trail.
To configure SPS to enable extracting files from audit trails after RDP file transfer through clipboard or disk redirection
- Navigate to RDP Control > Connections and open an existing connection (or create and configure a new connection).
- Expand the connection tab, scroll down to the Channel policy drop-down list, and select a channel policy of your choice from the drop-down list options.
- Navigate to RDP Control > Channel Policies and open the channel policy that you selected from the Channel policy drop-down list under RDP Control > Connections.
- Ensure that the Clipboard or Redirect drop-down list option under Type and the Record audit trail checkbox are both selected.
- (Optional) Click
 to save your configuration.
to save your configuration.
Configuring SPS to enable exporting sound from audit trails
From SPS version 6.11, you can enable auditing the sound that is transferred between an RDP client and the server.
Using the Safeguard Desktop Player application, you can export the input and output sound recorded on the side of the audited user to a .wav file.
NOTE: To export audio files from the audit trails, make sure that you have the appropriate version of Safeguard Desktop Player installed.
For more information on the sound export process in Safeguard Desktop Player, see Exporting files from an audit trail.
To configure SPS to enable extracting sound from audit trails
-
Navigate to RDP Control > Channel Policies and open the policy that you want to use for sound auditing or create and configure a new connection for this purpose.
For example, you can use the all policy for sound auditing as well.
-
From the Type drop-down, open Sound and Dynamic virtual channel and make sure that the Record audit trail checkbox is selected for both of these channel types.
NOTE: If the Record audit trail checkbox is selected only for the Sound channel, only the output sound (the one that is received by the audited user) is recorded in the audit trail.
If the Record audit trail checkbox is selected for the Dynamic virtual channel, both the input sound (the one that comes from the audited user) and output sound (the one that is received by the audited user) are recorded.
TIP: To play back the video file of the recorded audit trails with sound, enable the Record audit trail checkbox for the Drawing channel as well.
-
Click  to save your configuration.
to save your configuration.
to create a new channel policy.
to add an additional channel type.
to add the following channels:
for each channel.)
to save the channel policy.
