One Identity Safeguard for Privileged Sessions (SPS) uses a number of certificates for different tasks that can be managed from the Basic Settings > Management > SSL certificates menu.
|

|
Caution:
Starting from 6.10.0, SPS (SPS) has changed to hardened SSL settings. As a result, during TLS session establishment, the following items are not considered secure:
-
Private keys and X.509 certificates having RSA or DSA keys shorter than 2048 bits, or ECC keys shorter than 224 bits.
-
Certificates (other than Root CA certificates) with signatures that use the SHA-1 or the MD5 hashing algorithm.
With the hardened SSL settings, SPS will not connect to remote systems that are protected with weak certificates.
You cannot upgrade SPS if your configuration contains insecure certificates, keys or certificate chains in any of the following sections:
-
SPS web interface
-
internal CA certificate
-
connection policy TLS settings
-
client X.509 credentials for external LDAP, SMTP or Syslog connections
-
server X.509 certificates for external SMTP or Splunk servers
-
external indexer credentials (only writable over the REST API)
-
CA certificates in Trusted CA Lists and Trust Stores
Note that the certificates and keys that are used for signing, timestamping, encryption or decryption are not affected by this change. |
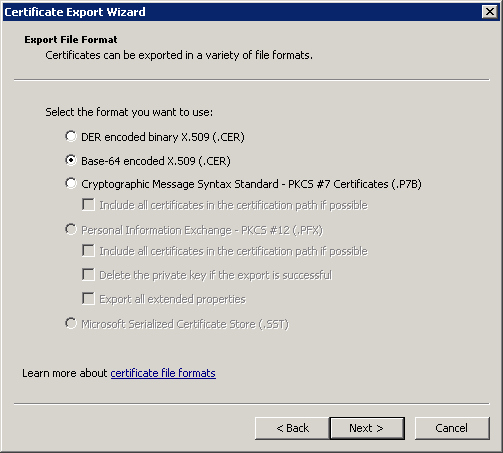
Figure 145: Basic Settings > Management > SSL certificates — Changing the web certificate of SPS
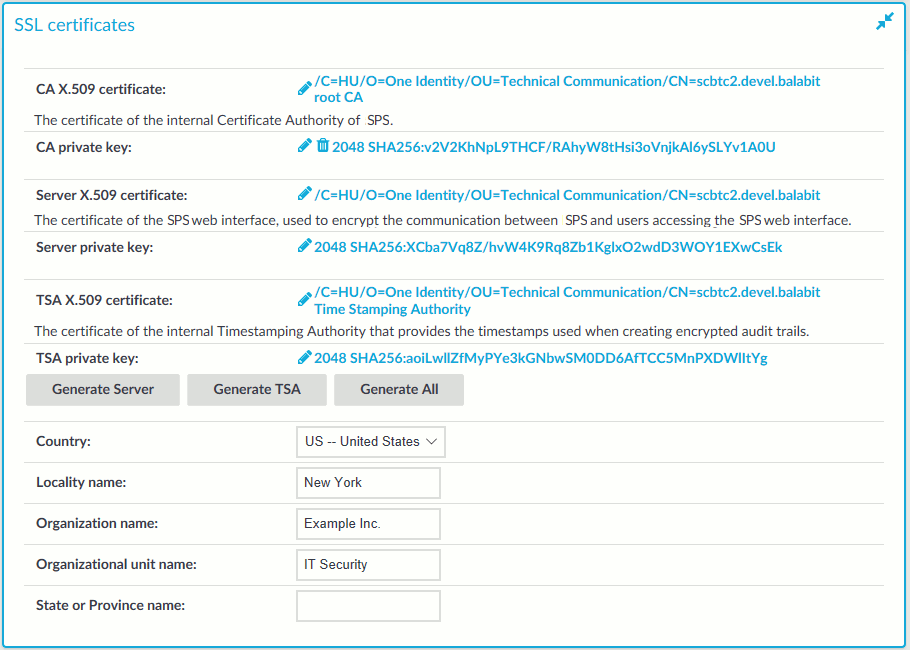
The following certificates can be modified here:
-
CA certificate: The certificate of the internal Certificate Authority of SPS.
-
Server certificate: The certificate of the SPS web interface, used to encrypt the communication between SPS and the administrators.
NOTE: If this certificate is changed, the browser of SPS users will display a warning stating that the certificate of the site has changed.
-
TSA certificate: The certificate of the internal Timestamping Authority that provides the timestamps used when creating encrypted audit-trails.
NOTE: SPS uses other certificates for different purposes that are not managed here, for example, to encrypt data stored on SPS. For details, see Encrypting audit trails.
Use every keypair or certificate only for one purpose. Do not reuse cryptographic keys or certificates (for example, do not use the certificate of the One Identity Safeguard for Privileged Sessions (SPS) webserver to encrypt audit trails, or the same keypair for signing and encrypting data).
For every certificate, the distinguished name (DN) of the X.509 certificate and the fingerprint of the private key is displayed. To display the entire certificate click on the DN. To display the public part of the private key, click on the fingerprint. It is not possible to download the private key itself from the SPS web interface, but the public part of the key can be downloaded in different formats (for example PEM, DER, or OpenSSH). Also, the X.509 certificate can be downloaded in PEM and DER formats.
During the initial configuration, SPS creates a self-signed CA certificate, and uses this CA to issue the certificate of the web interface (see Server certificate) and the internal Timestamping Authority (TSA certificate).
There are two methods to manage certificates of SPS:
-
Recommended: Generate certificates using your own PKI solution and upload them to SPS.
Generate a CA certificate and two other certificates signed with this CA using your PKI solution and upload them to SPS. For the Server and TSA certificates, upload the private key as well. One Identity recommends using 2048-bit RSA keys (or stronger), and to use certificates that have the appropriate keyUsage or extendedKeyUsage fields set (for example, extendedKeyUsage=serverAuth for the SPS web server certificate).
For details on uploading certificates and keys created with an external PKI, complete Uploading external certificates to One Identity Safeguard for Privileged Sessions (SPS).
|

|
Caution:
The Server and the TSA certificates must be issued by the same Certificate Authority. |
-
Use the certificates generated on SPS. In case you want to generate new certificates and keys for SPS using its self-signed CA certificate, or generate a new self-signed CA certificate, complete Generating certificates for One Identity Safeguard for Privileged Sessions (SPS).
NOTE: Generate certificates using your own PKI solution and upload them to SPS whenever possible. Certificates generated on SPS cannot be revoked, and can become a security risk if they are somehow compromised.
Create a new certificate for the One Identity Safeguard for Privileged Sessions (SPS) webserver or the Timestamping Authority using the internal CA of SPS, or create a new, self-signed CA certificate for the internal Certificate Authority of SPS.
TIP: One Identity recommends using 2048-bit RSA keys (or stronger).
To create a new certificate for the SPS webserver
-
Navigate to Basic Settings > Management > SSL certificates.
-
Fill the fields of the new certificate:
-
Country: Select the country where SPS is located (for example HU - Hungary).
-
Locality name: The city where SPS is located (for example Budapest).
-
Organization name: The company who owns SPS (for example Example Inc.).
-
Organization unit name: The division of the company who owns SPS (for example IT Security Department).
-
State or Province name: The state or province where SPS is located.
-
Select the certificate you want to generate.
-
To create a new certificate for the SPS web interface, select Generate Server.
-
To create a new certificate for the Timestamping Authority, select Generate TSA.
-
To create a new certificate for the internal Certificate Authority of SPS, select Generate All. Note that in this case new certificates are created automatically for the server and TSA certificates as well.
NOTE: When generating new certificates, the server and TSA certificates are signed using the certificate of the CA. If you have uploaded an external CA certificate along with its private key, it will be used to create the new server and TSA certificates. If you have uploaded an external CA certificate without its private key, use your external PKI solution to generate certificates and upload them to SPS.
|

|
Caution:
Generating a new certificate automatically deletes the earlier certificate. |
-
Click  .
.
Upload a certificate generated by an external PKI system to One Identity Safeguard for Privileged Sessions (SPS).
Prerequisites
The certificate to upload. For the TSA X.509 Certificate and Server X.509 Certificate, the private key of the certificate is needed as well. The certificates must meet the following requirements:
-
SPS accepts certificates in PEM format. The DER format is currently not supported.
-
SPS accepts private keys in PEM format, using RSA, DSA, and EC private key algorithms. Password-protected private keys are also supported.
NOTE: SPS accepts passwords that are not longer than 150 characters and supports the following characters:
For the internal CA certificate of SPS, uploading the private key is not required.
-
For the TSA certificate, the X509v3 Extended Key Usage extension must be set to critical with the value Time Stamping. Also, the Key Usage extension must be non repudiation and digital signature (that is, without key encipherment or other key usage).
-
For the Server certificate, the X509v3 Extended Key Usage extension must be set to TLS Web Server Authentication. Also, the Common Name of the certificate must contain the domain name or the IP address of the SPS host. If the web interface is accessible from multiple interfaces or IP addresses, list every IP address using the Subject Alt Name extension.
-
For the certificate used to sign audit trails, the X509v3 Extended Key Usage extension must be set to Sign (downloadable) executable code.
TIP: One Identity recommends using 2048-bit RSA keys (or stronger).
To upload a certificate generated by an external PKI system to SPS
-
Navigate to Basic Settings > Management > SSL certificates.
-
Click  to upload the new certificate. A pop-up window is displayed.
to upload the new certificate. A pop-up window is displayed.
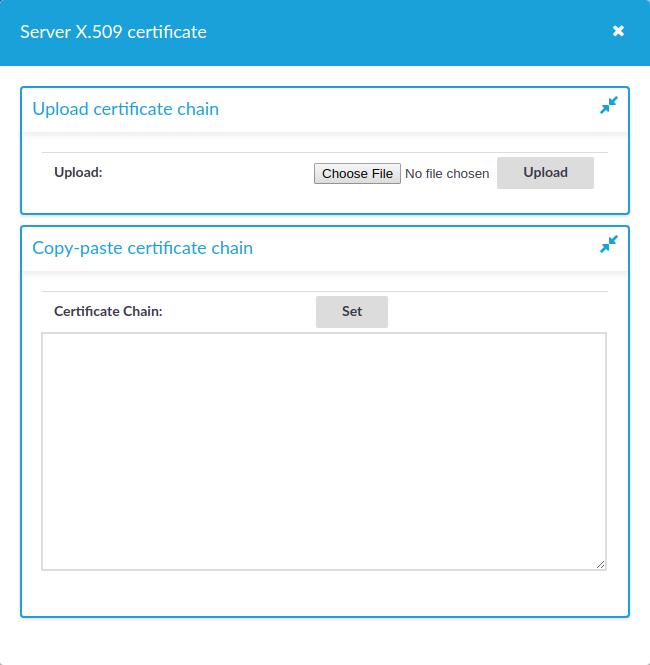
Figure 146: Basic Settings > Management > SSL certificates — Uploading certificates
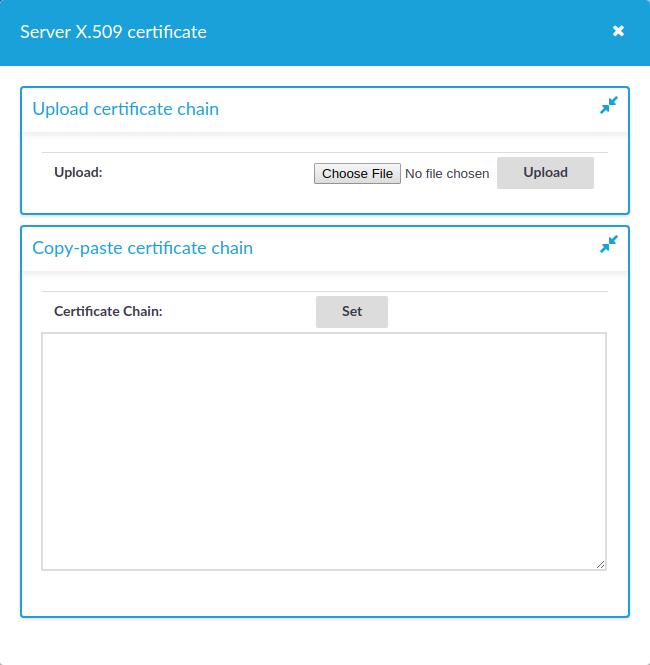
Select Browse, select the file containing the certificate, and click Upload.
For the Server X.509 Certificate
For the Server X.509 Certificate, you can also upload a certificate chain. For that, copy the certificates after each other in a single file. Alternatively, you can copy and paste the certificates one by one after each other into the Certificate field and click Set. The certificates do not have to be in order, SPS will order them and validate the chain: if a member of the chain is missing, an error message is displayed.
NOTE: Certificate chains are supported only for the Server X.509 Certificate.
-
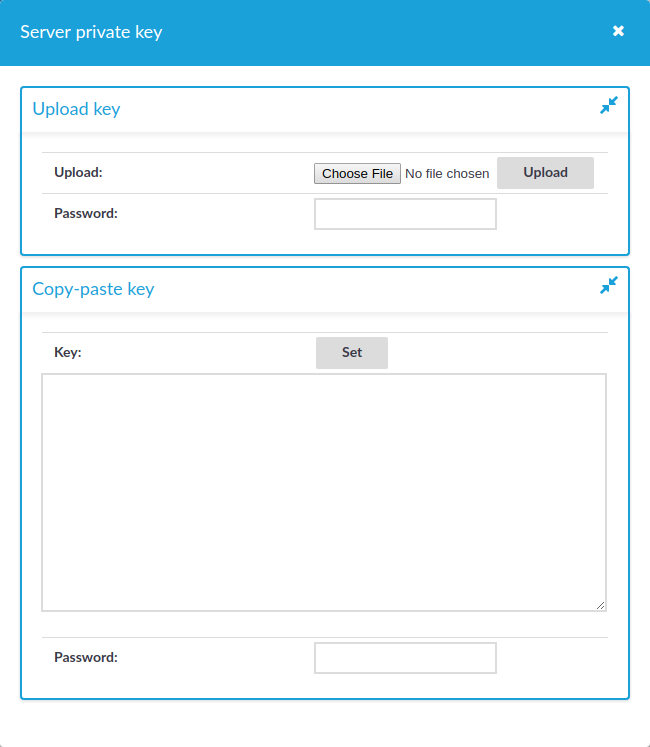
To upload the private key corresponding to the certificate, click  icon. A pop-up window is displayed.
icon. A pop-up window is displayed.
Figure 147: Basic Settings > Management > SSL certificates — Uploading the private key
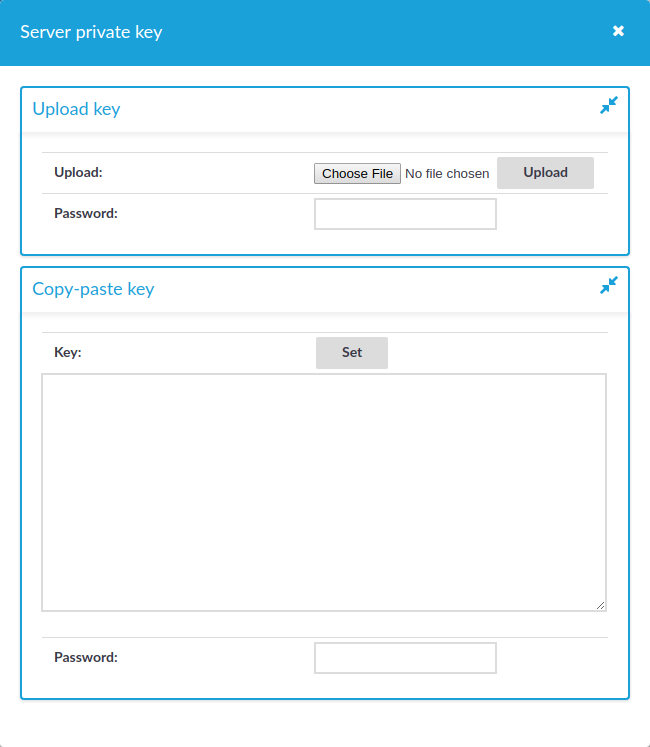
Select Browse, select the file containing the private key, provide the Password if the key is password-protected, and click Upload. Alternatively, you can also copy-paste the private key into the Key field, provide the Password there, and click Set.
In the case of a certificate chain, the private key has to be the same as the bottom level certificate.
Expected result
The new certificate is uploaded. If you receive the Certificate issuer mismatch error message after importing a certificate, you must import the CA certificate which signed the certificate as well (the private key of the CA certificate is not mandatory).
NOTE: To download previously uploaded certificates, click on the certificate and either download the certificate (or certificate chain) in one single PEM or DER file, or you can download single certificate files separately (if it is a certificate chain).
To generate a TSA certificate with Windows Certificate Authority (CA) that works with One Identity Safeguard for Privileged Sessions (SPS), generate a CSR (certificate signing request) on a computer running OpenSSL and sign it with Windows CA, then import this certificate into SPS for timestamping.
Prerequisites
A valid configuration file for OpenSSL with the following extensions:
[ tsa_cert ]
extendedKeyUsage = critical,timeStamping
TIP: You can copy /etc/xcb/openssl-ca.cnf from SPS to the computer that will be used for signing. Rename the file to openssl-temp.cnf.
The TSA certificate is considered valid, in terms of compatibility with SPS, if the following conditions are met:
-
The X509v3 Extended Key Usage extension of the TSA certificate is set to critical with the value Time Stamping.
-
The Key Usage extension is non repudiation and digital signature (that is, without key encipherment or other key usage).
|

|
Caution:
In Encryption, do not select Allow key exchange only with key encryption (key encipherment), because it will result in errors. |
The following X509v3 extensions are supported:
-
Hard requirement:
X509v3 Extended Key Usage must be critical, and must only contain Time Stamping.
-
Optional:
X509v3 Key Usage, if present, must be digitalSignature and/or nonRepudiation.
To generate TSA certificate with Windows Certificate Authority on Windows Server 2008
-
Create CSR using the new configuration file: openssl req -set_serial 0 -config openssl-temp.cnf -reqexts tsa_cert -new -newkey rsa:2048 -keyout timestamp.key -out timestamp.csr -nodes
-
Complete the required fields according to your environment:
Generating a 2048 bit RSA private key
........................+++
......................................+++
writing new private key to 'timestamp.key'
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:US
State or Province Name (full name) []:New York
Locality Name (eg, city) []:New York
Organization Name (eg, company) [Internet Widgits Pty Ltd]:Examplecompany IT Security
Organizational Unit Name (eg, section) []:Service Delivery
Common Name (eg, YOUR name) []:scb35-1-i1.tohuvabohu.examplecompany
Email Address []:vlad@examplecompany.com
-
Sign the generated CSR with your Windows CA. Make sure that the CSR file is accessible from your Windows CA server.
-
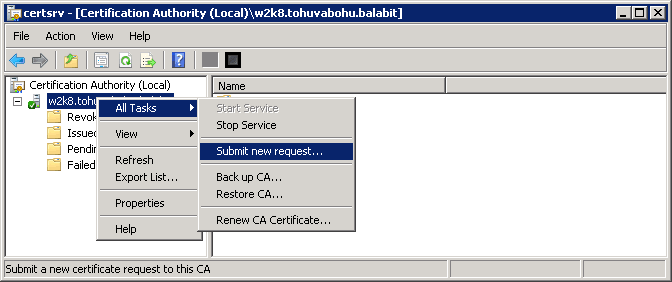
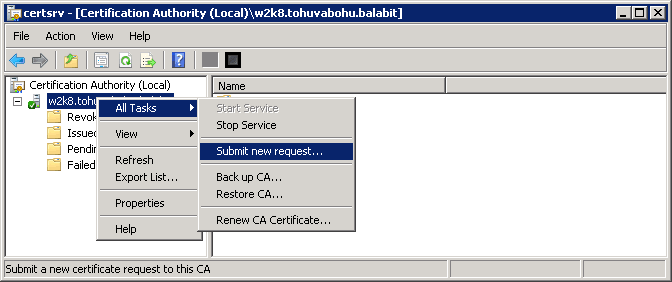
To issue and sign the new certificate request, open the Microsoft Certification Authority Management Console: Start > Run and run certsrv.msc.
-
Right-click on the server name and navigate to All Tasks > Submit new request....
Figure 148: Submitting a new request
-
Select the CSR created in the second step.
-
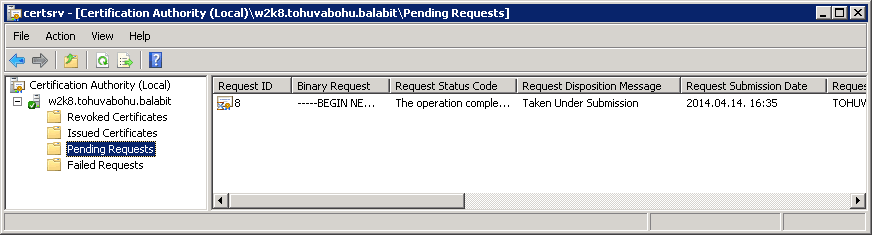
On the left pane, click Pending Requests. The new certificate request is displayed in the right pane.
Figure 149: Issuing a new certificate
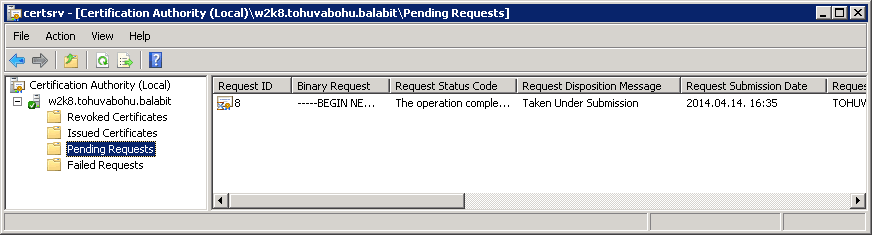
-
To issue the new SSL certificate, right-click on the pending certificate request, select “All Tasks” and click on “Issue”.
-
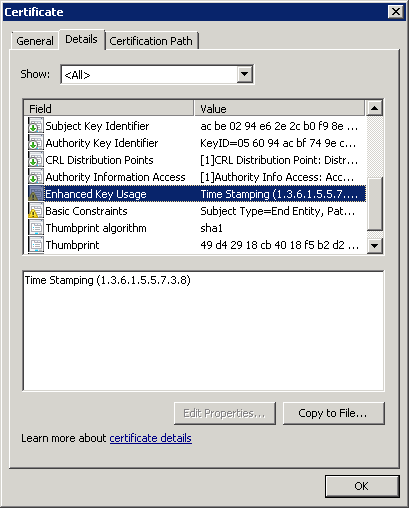
Select "Issued Certificates" and double-click on the certificate issued in the previous step.
-
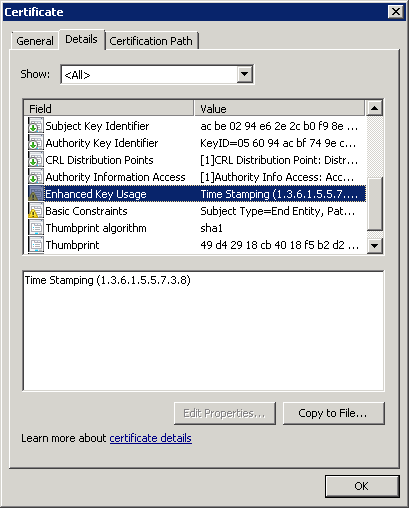
The CA Certificate window opens. Navigate to the Details tab. Ensure that the required Enhanced Key Usage field is visible and contains the Time Stamping value.
Figure 150: Verifying certificate details
-
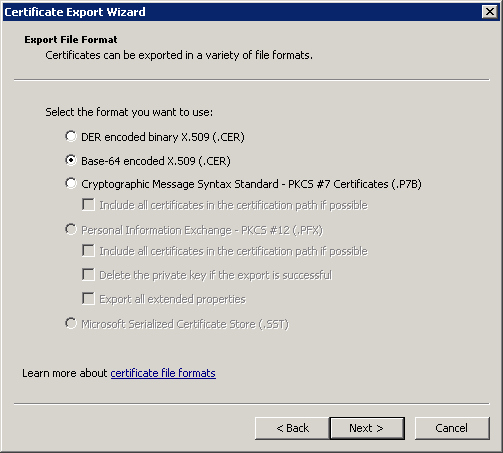
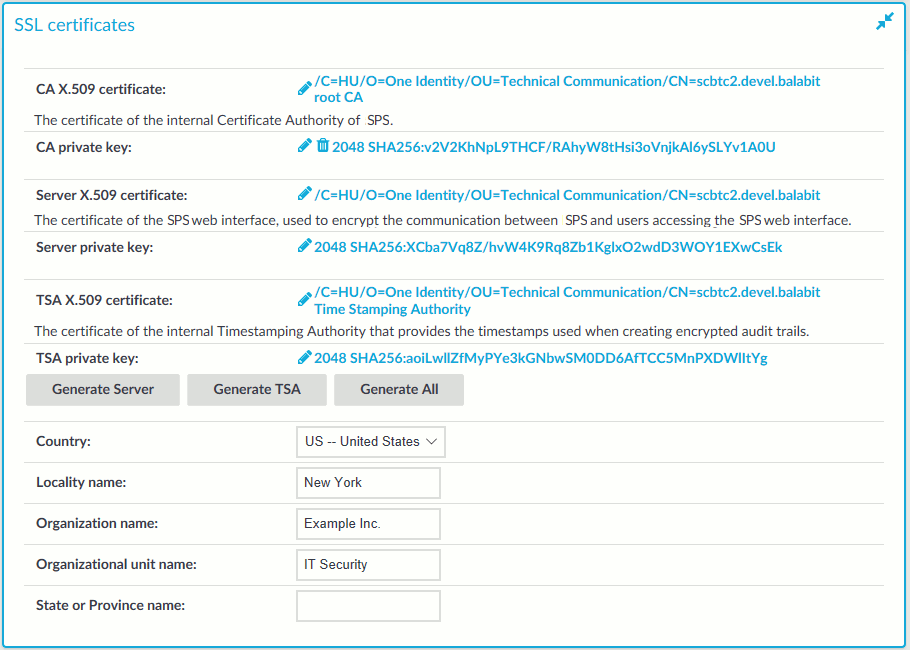
Click Copy to File. The Certificate Export Wizard launches. Click Next.
-
Select the format of the certificate: Base-64 encoded X.509 (.CER). Click Next.
Figure 151: Selecting certificate file format
-
Select location to save the certificate, and save it.
-
The Completing the Certificate Export Wizard screen is displayed. Click Finish.
-
In SPS, navigate to Basic Settings > Management > SSL certificates.
-
Click  next to TSA X.509 certificate, browse for the previously generated certificate, and click Upload.
next to TSA X.509 certificate, browse for the previously generated certificate, and click Upload.
-
Click  next to TSA private key, browse for the previously generated key, and click Upload.
next to TSA private key, browse for the previously generated key, and click Upload.
NOTE: If the root CA (the CA X.509 certificate field under Basic Settings > Management > SSL certificates) that is used for other certificates on SPS is different from the CA that was used to sign the TSA certificate, a warning is displayed. In this scenario, ignore this warning.


 .
. to upload the new certificate. A pop-up window is displayed.
to upload the new certificate. A pop-up window is displayed.