One Identity Safeguard for Privileged Sessions (SPS) is configured through the web interface. Configuration changes take effect automatically after clicking  . Only the modifications of the current page or tab are activated — each page and tab must be committed separately.
. Only the modifications of the current page or tab are activated — each page and tab must be committed separately.
-
For details about the supported browsers, see Supported web browsers.
-
For details on how to use the web interface of SPS, see The structure of the web interface.
-
For details on how to configure the network interfaces, name resolution, and other networking-related settings, see Network settings.
-
For details on how to control (for example reboot) SPS, upload a new firmware or license, export the current configuration, or stop the incoming syslog traffic, see Network settings.
-
For details on how to set the system time and automatic time synchronization to an NTP server, see Configuring date and time.
-
For details on how to configure where SNMP and e-mail alerts are sent, see System logging, SNMP and e-mail alerts.
-
For details on how to configure system monitoring and alerts, see Configuring system monitoring on SPS.
-
For details on how to configure data and configuration backups, see Data and configuration backups.
-
For details on how to configure archiving, see Archiving.
Starting from version 6.13.0, SPS does not support Internet Explorer 11 (IE11). SPS version 6.12.0 and previous versions continue to support IE11.
Your browser must support:
SPS supports browsers as listed in the following table.
|
7.4.0 |
- |
✔ |
✔ |
✔ |
✔ |
- |
|
7.3.0 |
- |
✔ |
✔ |
✔ |
✔ |
- |
|
7.2.0 |
- |
✔ |
✔ |
✔ |
✔ |
- |
|
7.1.0 |
- |
✔ |
✔ |
✔ |
✔ |
- |
| 7.0 LTS |
- |
✔ |
✔ |
✔ |
✔ |
- |
| 6.13.0 |
- |
✔ |
✔ |
✔ |
✔ |
- |
| 6.12.0 |
✔ |
✔ |
✔ |
✔ |
✔ |
- |
| 6.11.0 |
✔ |
✔ |
✔ |
✔ |
✔ |
- |
| 6.10.0 |
✔ |
✔ |
✔ |
✔ |
✔ |
- |
| 6.9.0 |
✔ |
✔ |
✔ |
✔ |
✔ |
- |
| 6.8.0 |
✔ |
✔ |
✔ |
✔ |
✔ |
- |
Required applications and plugins
To use SPS, install and enable the following applications and plugins.
NOTE: To replay audit trails with SPS 6.9 or earlier versions with Internet Explorer 11 (IE11), install the Google WebM Video for Microsoft Internet Explorer plugin.
|
7.4.0 |
✔ |
- |
|
7.3.0 |
✔ |
- |
|
7.2.0 |
✔ |
- |
|
7.1.0 |
✔ |
- |
| 7.0 LTS |
✔ |
- |
| 6.13.0 |
✔ |
- |
| 6.12.0 |
✔ |
- |
| 6.11.0 |
✔ |
- |
| 6.10.0 |
✔ |
- |
| 6.9.0 |
✔ |
Required for IE11 |
| 6.8.0 |
✔ |
Required for IE11 |
Phased out browsers
SPS does not support anymore the browsers listed in the following table.
| IE10 |
SPS 4 F3 |
| IE9 |
SPS 4 F3 |
Starting from version 4 F3, SPS does not support Internet Explorer 9 and 10, because the official support for them ended in January, 2016.
SPS web UI
Opening the web UI of SPS in multiple browser windows or tabs is not supported.
NOTE: The minimum recommended screen resolution for viewing One Identity Safeguard for Privileged Sessions's (SPS's) web interface is 1366 x 768 pixels on a 14-inch widescreen (standard 16:9 ratio) laptop screen. Screen sizes and screen resolutions that are equal to or are above these values will guarantee an optimal display of the web interface.
NOTE: The minimum recommended screen resolution for viewing One Identity Safeguard for Privileged Sessions's (SPS's) web interface is 1366 x 768 pixels on a 14-inch widescreen (standard 16:9 ratio) laptop screen. Screen sizes and screen resolutions that are equal to or are above these values will guarantee an optimal display of the web interface.
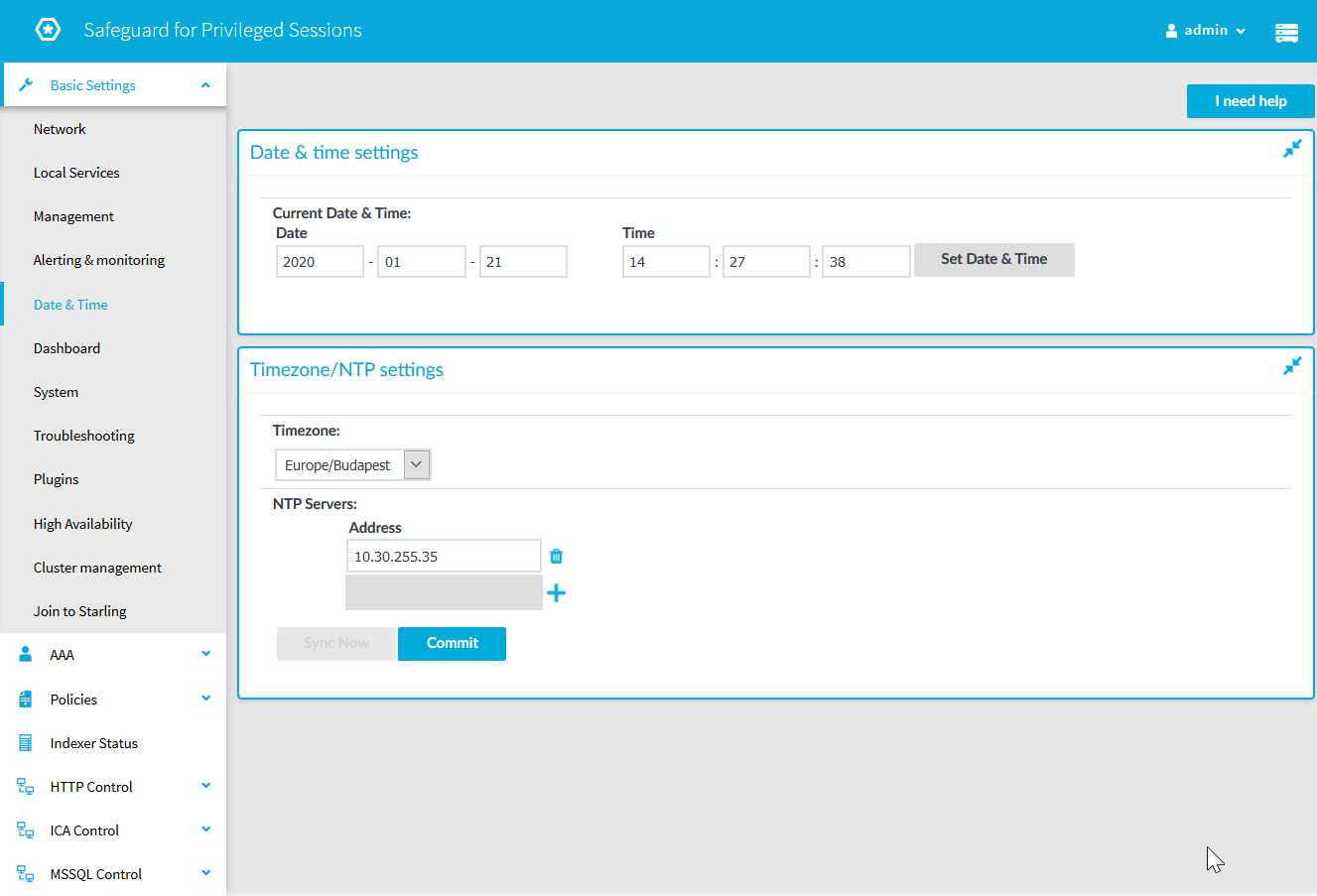
Figure 31: Structure of the web interface
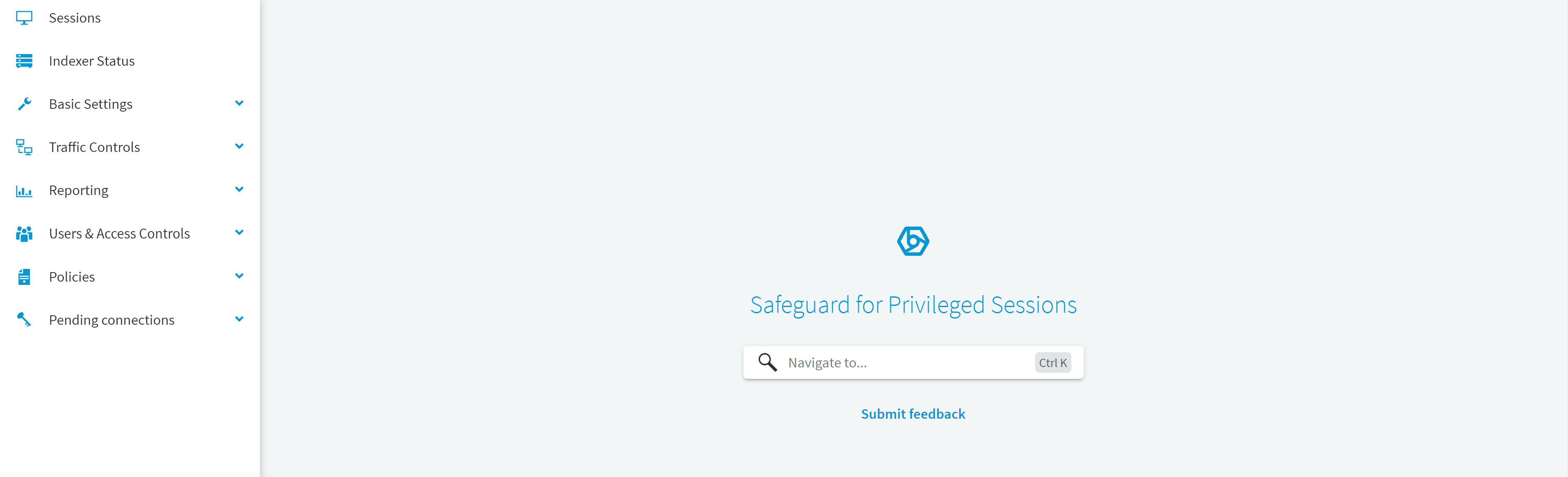
The web interface consists of the following main sections:
Main menu
Each menu item displays its options in the main workspace on one or more tabs. Click a Main menu item to display the list of tabs available under that particular menu item.
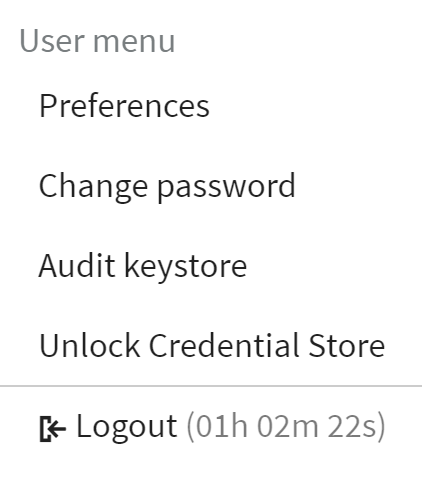
User menu
Figure 32: User menu
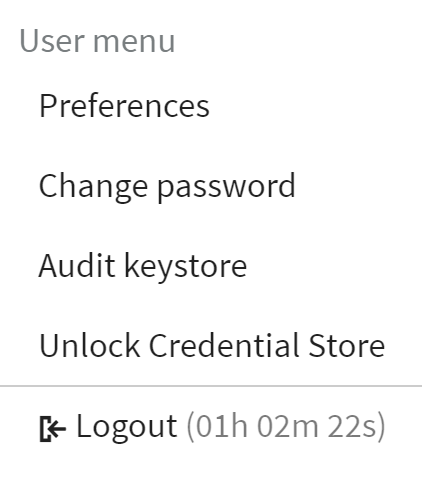
The User menu allows you to:
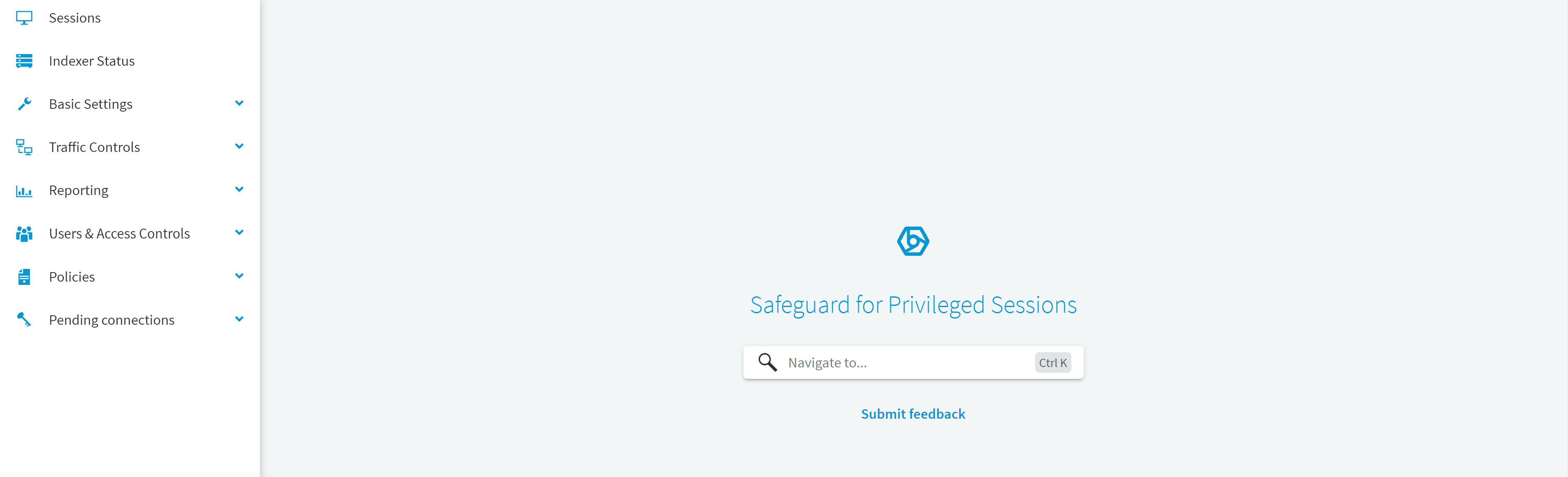
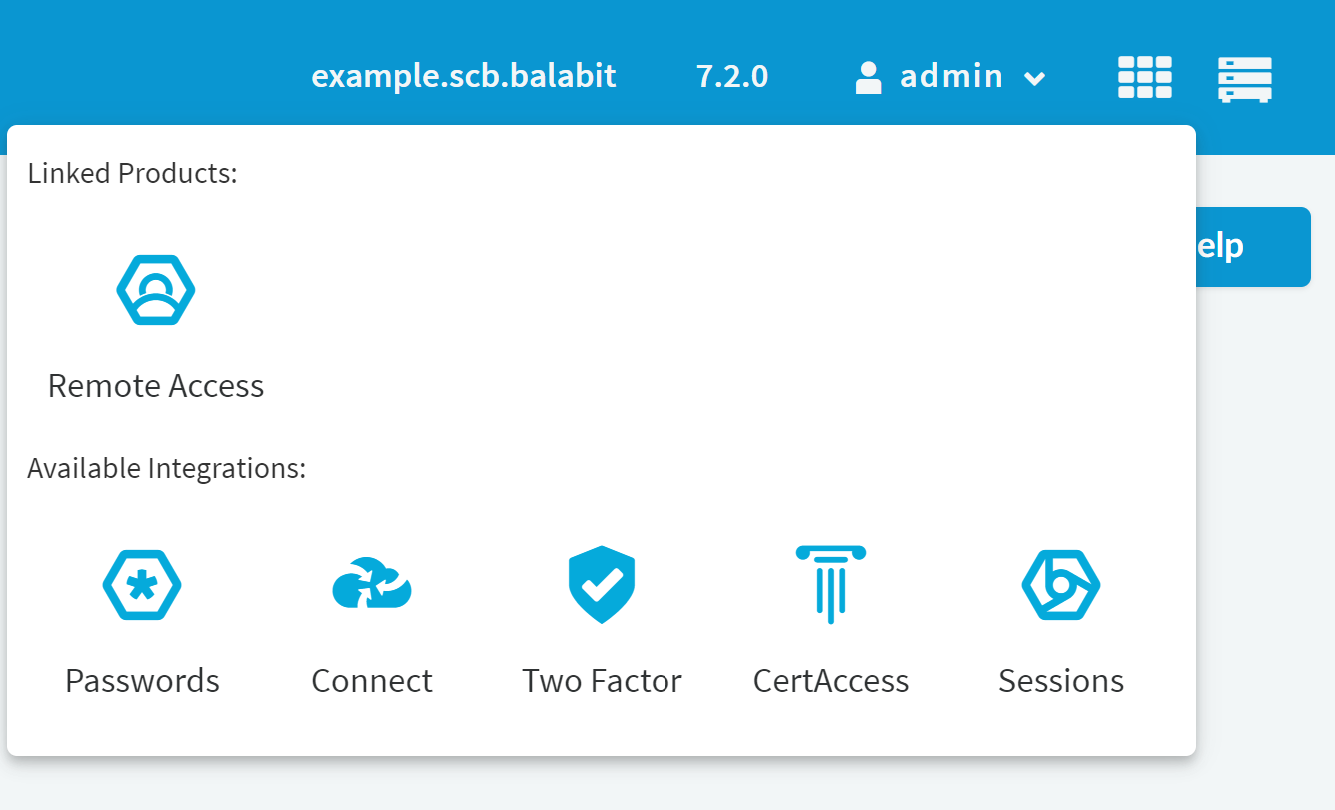
App switcher
Figure 33: App switcher
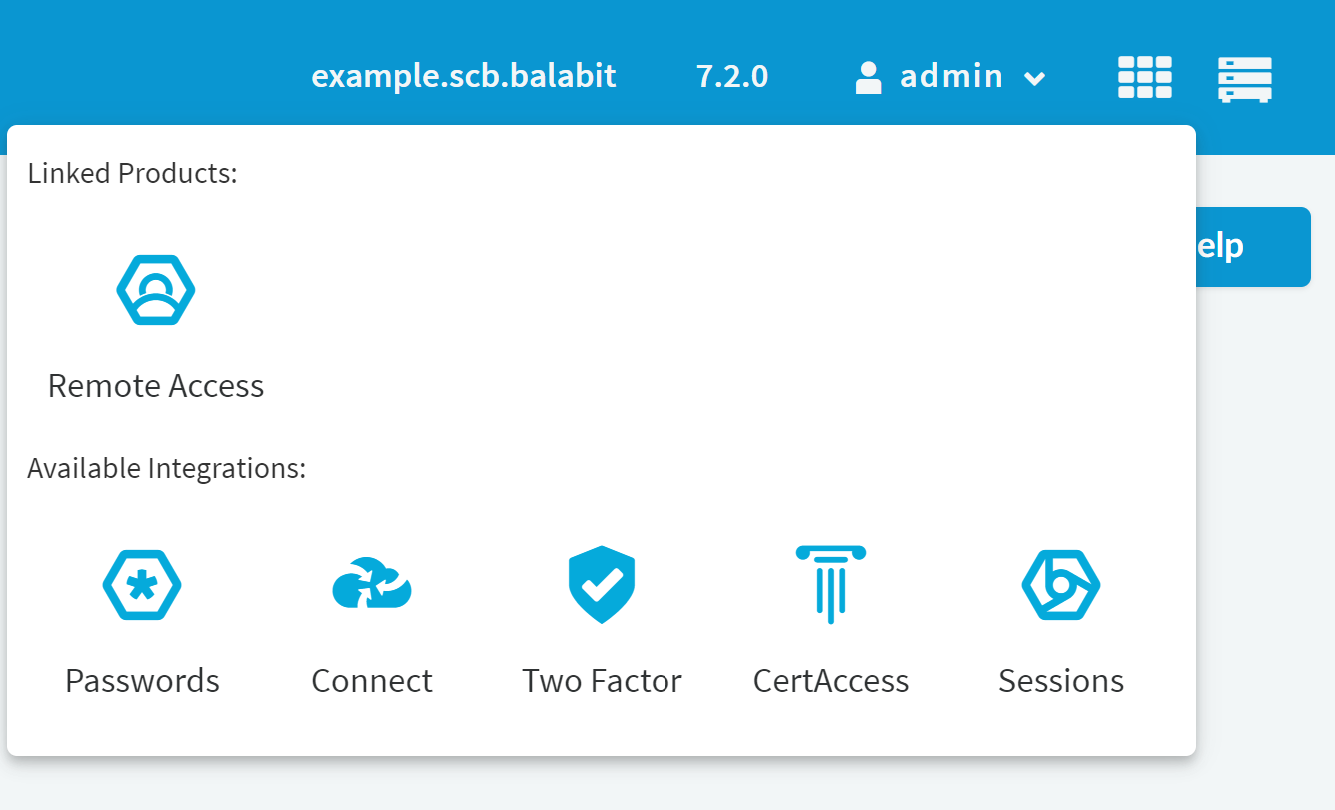
After setting up a federated login method between SPS and a linked product, you can seamlessly switch between SPS and the linked product by selecting the  app switcher icon.
app switcher icon.
About page
Figure 34: About page
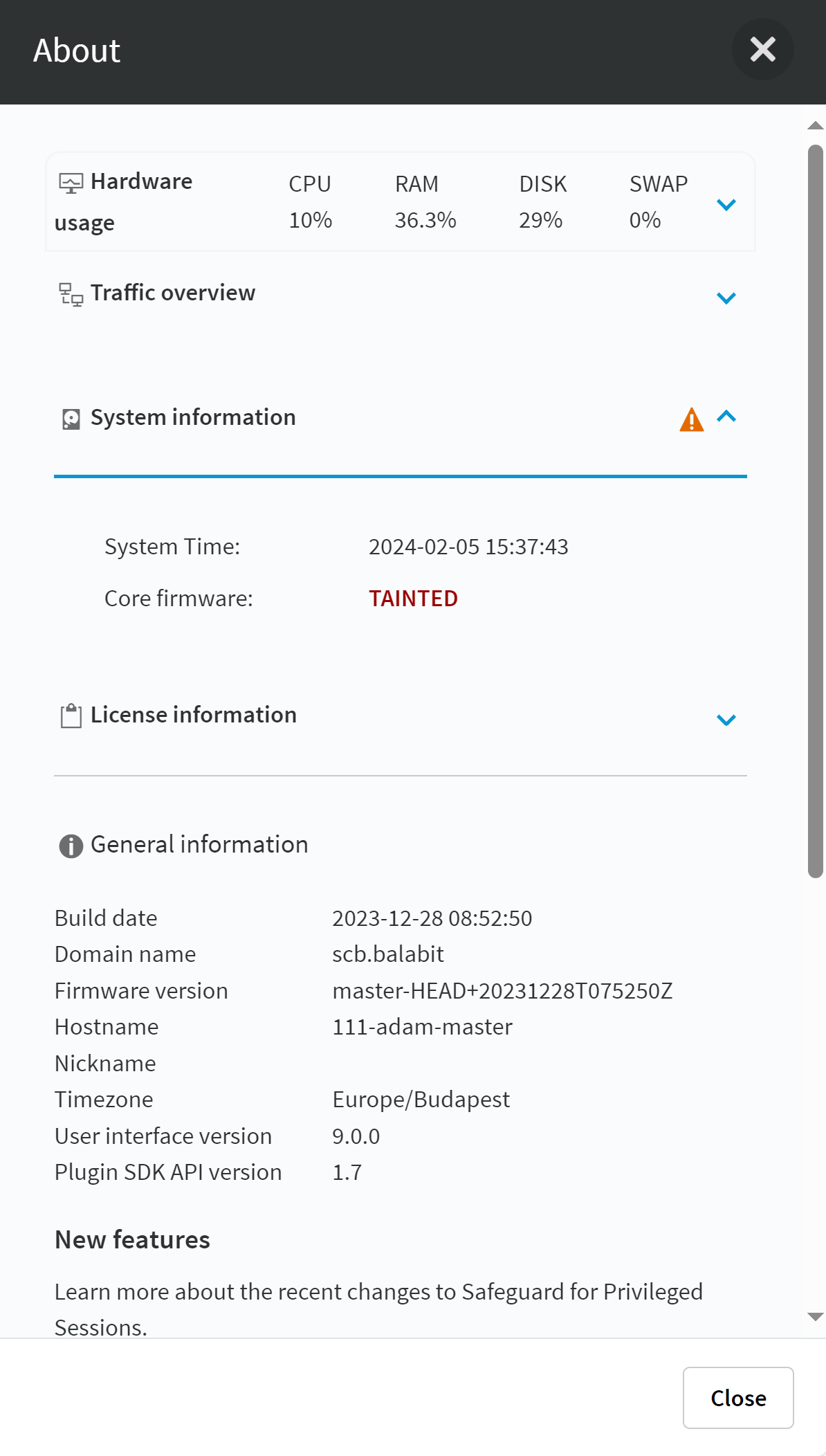
Displays accessibility and system health information about SPS, including the following:
-
Hardware usage: CPU, memory, hard disk, and swap use. Expand to see more details or navigate to Basic Settings > Dashboard for detailed reports.
-
Traffic overview: The number of active HTTP, ICA, MSSQL, RDP, SSH, TELNET, and VNC connections. For HTTP, Traffic overview displays the number of active HTTP sessions.
-
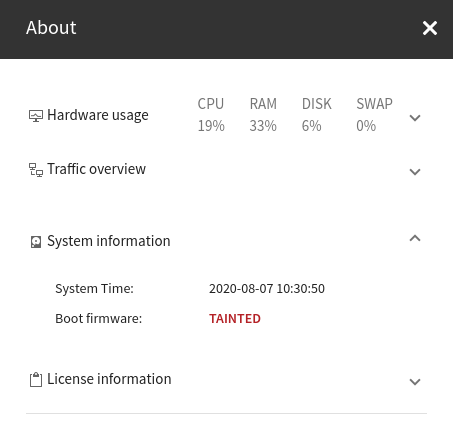
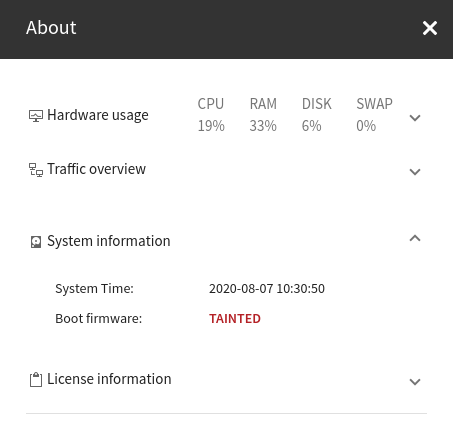
System information: Shows the system date, the system time, and the status of the core and boot firmware.
- Corrupted: The firmware integrity check failed. If a firmware is shown as corrupted, contact our Support Team.
- Tainted: It indicates that you have modified a file of the firmware locally. If you have modified a local file unintentionally, contact our Support Team.
Figure 35: Boot firmware - Tainted
-
General information such as, current timezone or user interface version, and so on, as well as, links related to new features, help or feedback.
Context-sensitive help
SPS offers context-sensitive help, which is used to display information about the user interface relative to the task a user performs.
There are different levels of context sensitivity that have been implemented in SPS.
-
Screen-level help
When available, SPS opens the help topic for that screen. Instead of having the user browse through the help system to find the right topic, SPS can quickly and directly display the topic that corresponds to the screen.
To open a screen-level help, click I need help, when available.
-
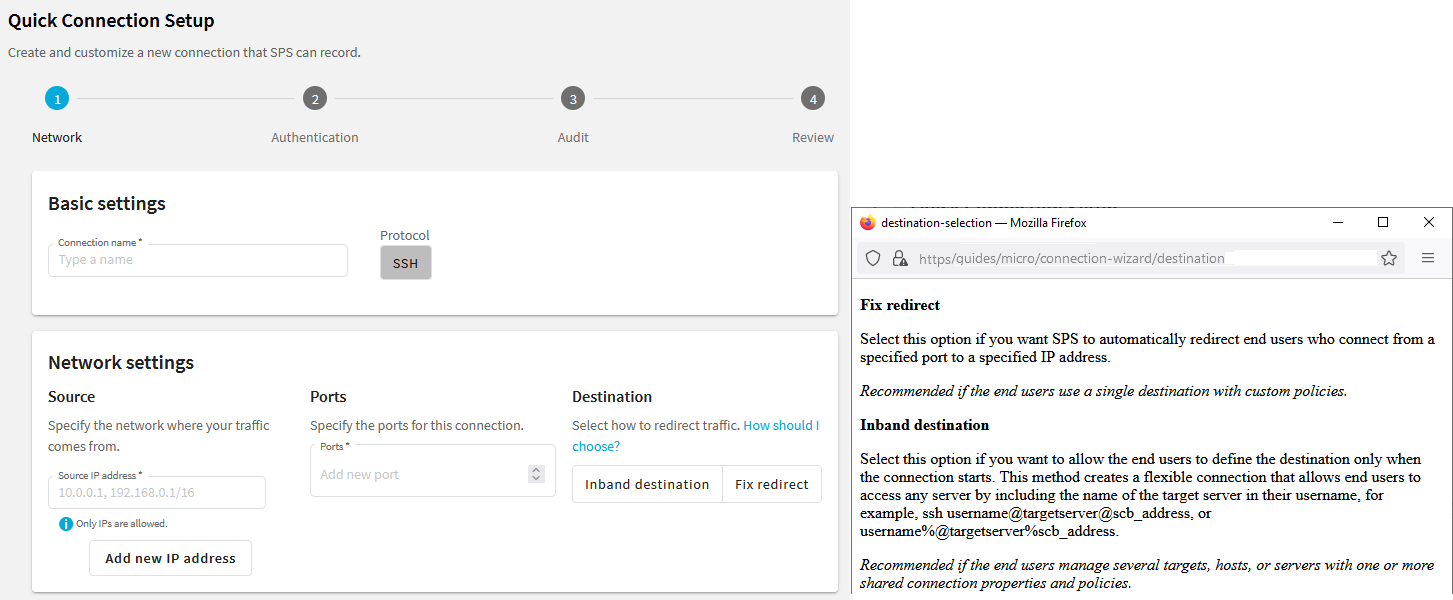
Field-level help
When available, field-level help provides help text detailing the purpose and function of a field.
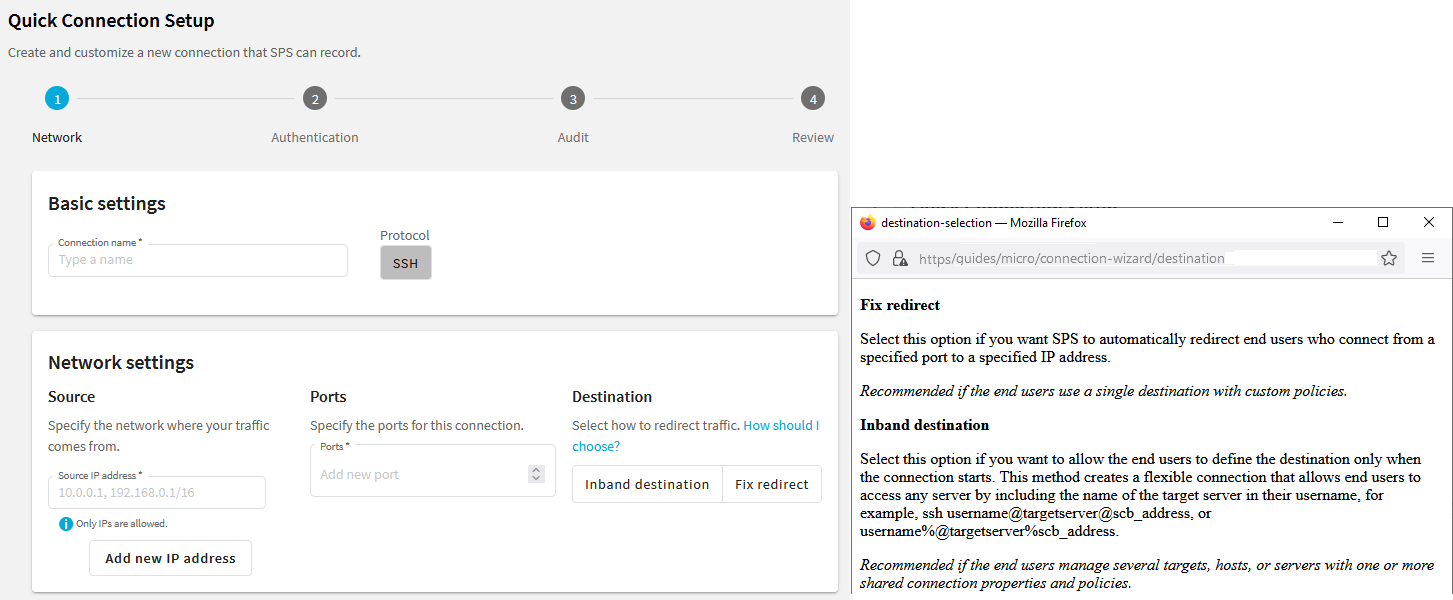
The following is an example of a field-level help where you can click How should I choose? and the help opens with more details about making the relevant destination settings.
Figure 36: Quick Connection Setup — Example of a field-level help
The main workspace displays the configuration settings related to the selected Main menu item grouped into one or more submenus. Related parameters of a submenu are organized into labeled groups or sections, marked with blue outline  .
.
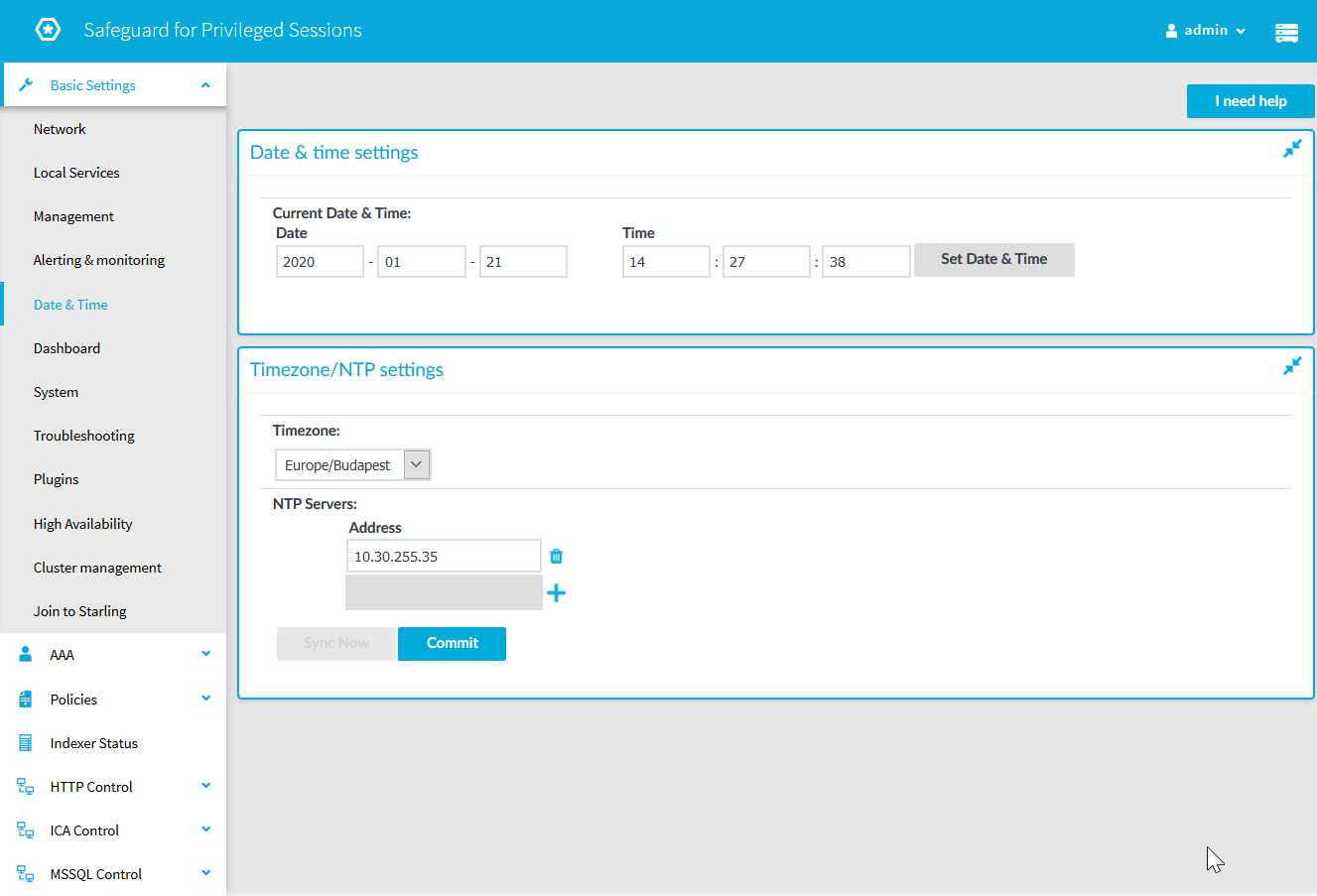
Figure 37: Main workspace
-
 Each page includes one or more blue action buttons. The most common action button is
Each page includes one or more blue action buttons. The most common action button is  , which saves and activates the changes of the page.
, which saves and activates the changes of the page.
-
 /
/ Show/Hide details: Displays or hides additional configuration settings and options.
Show/Hide details: Displays or hides additional configuration settings and options.
-
 Create entry: Create a new row or entry (for example an IP address or a policy).
Create entry: Create a new row or entry (for example an IP address or a policy).
-
 Delete entry: Delete a row or an entry (for example an IP address or a policy).
Delete entry: Delete a row or an entry (for example an IP address or a policy).
-
 Modify entries or upload files: Edit an entry (for example a host key, a list, and so on), or upload a file (for example a private key). These actions open a pop-up window where the actual modification can be performed.
Modify entries or upload files: Edit an entry (for example a host key, a list, and so on), or upload a file (for example a private key). These actions open a pop-up window where the actual modification can be performed.
-
 ,
,  Position an item in a list: Modify the order of items in a list. The order of items in a list (for example the order of connections, permitted channels in a channel policy, and so on) is important because when One Identity Safeguard for Privileged Sessions (SPS) is looking for a policy, it evaluates the list from top to down, and selects the first item completely matching the search criteria. For example, when a client initiates a connection to a protected server, SPS selects the first connection policy matching the client's IP address, the server's IP address, and the target port (the From, To, and Port fields of the connection).
Position an item in a list: Modify the order of items in a list. The order of items in a list (for example the order of connections, permitted channels in a channel policy, and so on) is important because when One Identity Safeguard for Privileged Sessions (SPS) is looking for a policy, it evaluates the list from top to down, and selects the first item completely matching the search criteria. For example, when a client initiates a connection to a protected server, SPS selects the first connection policy matching the client's IP address, the server's IP address, and the target port (the From, To, and Port fields of the connection).
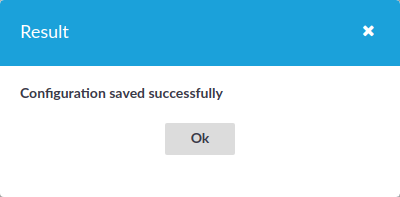
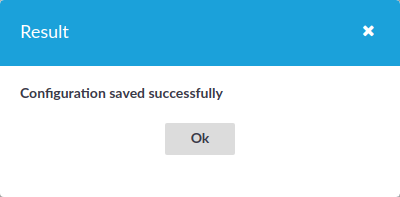
Message window: This pop-up window displays the responses of SPS to the user's actions, for example Configuration saved successfully. Error messages are also displayed here. All messages are included in the system log. For detailed system logs (including message history), see the Troubleshooting tab of the Basic Settings. To make the window appear only for failed actions, navigate to User menu > Preferences and enable the Autoclose successful commit messages option.
Figure 38: Message window


 app switcher icon.
app switcher icon.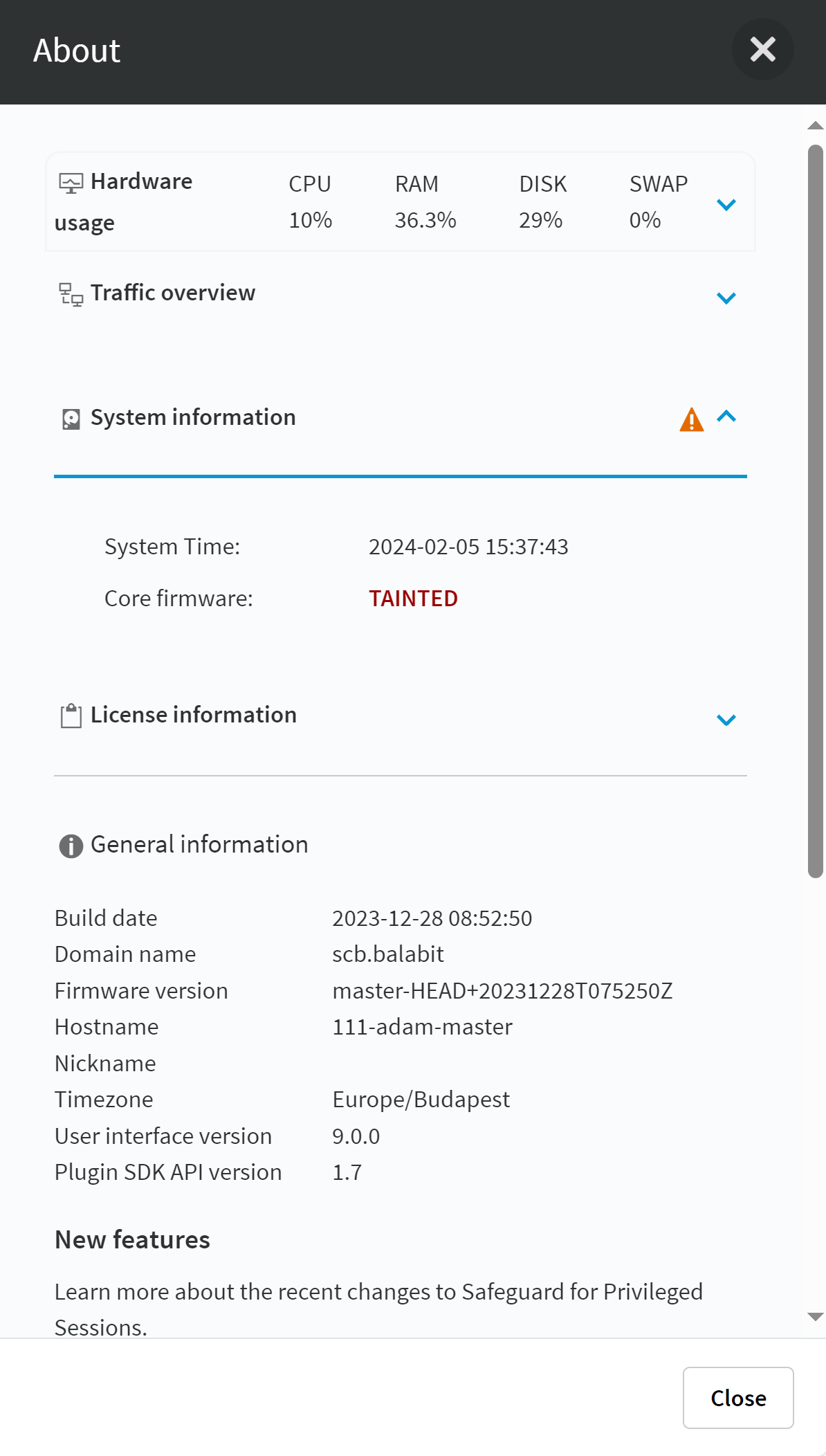
 .
.
 /
/ Show/Hide details: Displays or hides additional configuration settings and options.
Show/Hide details: Displays or hides additional configuration settings and options. Create entry: Create a new row or entry (for example an IP address or a policy).
Create entry: Create a new row or entry (for example an IP address or a policy). Delete entry: Delete a row or an entry (for example an IP address or a policy).
Delete entry: Delete a row or an entry (for example an IP address or a policy). Modify entries or upload files: Edit an entry (for example a host key, a list, and so on), or upload a file (for example a private key). These actions open a pop-up window where the actual modification can be performed.
Modify entries or upload files: Edit an entry (for example a host key, a list, and so on), or upload a file (for example a private key). These actions open a pop-up window where the actual modification can be performed. ,
,  Position an item in a list: Modify the order of items in a list. The order of items in a list (for example the order of connections, permitted channels in a channel policy, and so on) is important because when One Identity Safeguard for Privileged Sessions (SPS) is looking for a policy, it evaluates the list from top to down, and selects the first item completely matching the search criteria. For example, when a client initiates a connection to a protected server, SPS selects the first connection policy matching the client's IP address, the server's IP address, and the target port (the From, To, and Port fields of the connection).
Position an item in a list: Modify the order of items in a list. The order of items in a list (for example the order of connections, permitted channels in a channel policy, and so on) is important because when One Identity Safeguard for Privileged Sessions (SPS) is looking for a policy, it evaluates the list from top to down, and selects the first item completely matching the search criteria. For example, when a client initiates a connection to a protected server, SPS selects the first connection policy matching the client's IP address, the server's IP address, and the target port (the From, To, and Port fields of the connection).