If any of the following special characters must appear in the search filter as literals, they must be replaced by the listed escape sequence.
Table 7: Special characters
|
* |
\2a |
|
( |
\28 |
|
) |
\29 |
|
\ |
\5c |
|
NUL |
\00 |
In addition, arbitrary binary data may be represented using the escape sequence syntax by encoding each byte of binary data with the backslash (\) followed by two hexadecimal digits. For example, the four-byte value 0x00000004 is encoded as \00\00\00\04 in a filter string.
In object creation wizards and properties dialog boxes, some property labels may be displayed as hyperlinks. This indicates that Active Roles enforces policy restrictions on the property.
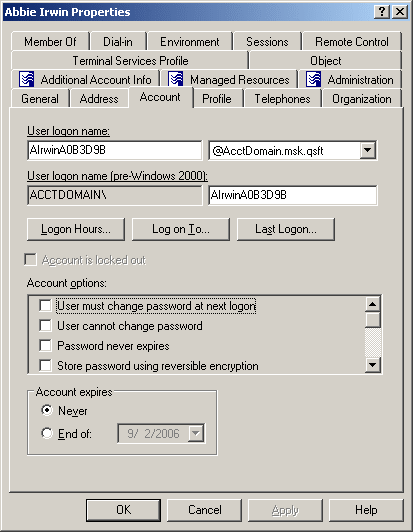
In the following figure, the User logon name and User logon name (pre-Windows 2000) labels are underlined, which means that these properties are under the control of a certain policy defined with Active Roles.
Figure 1: Getting policy-related information
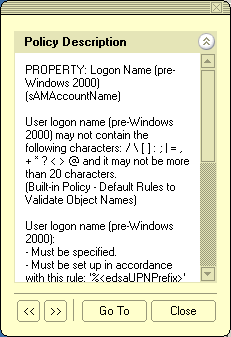
To examine the policy in detail, you can click the label. For example, if you click User logon name (pre-Windows 2000), the Active Roles console presents you with a window similar to the following figure.
Figure 2: Policy description
The window may display the following information:
- Policy Description Provides a brief description of the policy.
- Message Details the problem if the supplied property value violates the policy.
You can click arrows in the lower-left corner to display description of other policies enforced on the given property.
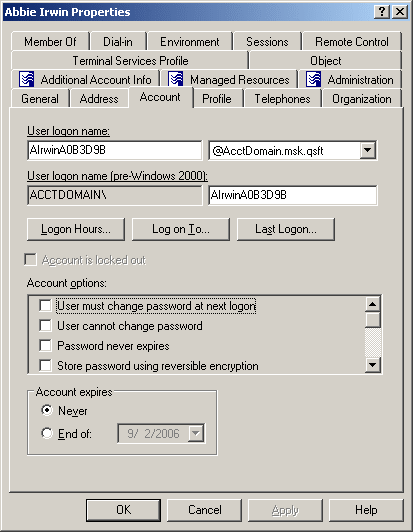
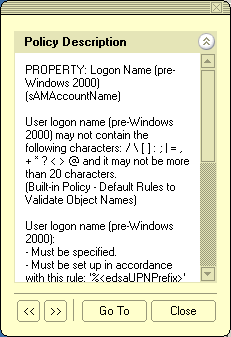
The Message section is displayed whenever the specified property value violates the policy. The following figure illustrates the situation where a value has not been supplied for a mandatory property.
Figure 3: Policy violation message

When you click Go To in this window, the console moves the pointer to the field that needs to be corrected. You can type or select an appropriate value to correct your input.
Since Active Roles manages confidential Active Directory user details in both on-premises and cloud based environments, it is appropriate and safer to have an additional security measure such as the two-factor authentication. Active Roles now supports One Identity's Starling Two-Factor Authentication service.
The Starling Two-factor authentication provides enhanced security by necessitating users to provide two forms of authentication to Active Roles, namely a user name and password combination along with a token response. The token response is collected through an SMS, Phone call, or push notification received on a physical device such as a mobile or any other device other than the browser.
Before you configure Starling using the Active Roles Configuration Center, ensure the following:
-
Users must have acquired valid Starling Credentials, such as a Starling Organization Admin account or a Collaborator account. For more information on Starling, see the One Identity Starling User Guide.
-
The computer running Active Roles must have TLS version 1.2 enabled. For more information, see How to enable TLS 1.2 on clients in the Microsoft Core infrastructure documentation.
-
The computer running Active Roles must be able to connect directly to the web and reach the following web addresses at a minimum:
-
*.cloud.oneidentity.com
-
*.cloud.oneidentity.eu
NOTE: Additional Microsoft URLs may be required depending on your Starling integration with Azure. For more information, see KB Article 229909 on the One Identity Support Portal.
- The Active Roles Administration Service must be running on the computer where you want to configure Starling.
- The Active Roles Administration Service must have a managed domain.
-
You must disable IE Enhanced Security Configuration to allow the Starling Join process to complete. Once the Starling Join process has completed, you can re-enable this setting.
Follow the steps to disable IE Enhanced Security Configuration.
To disable IE Enhanced Security Configuration
-
Open Server Manager.
-
On the left pane, select Local Server.
-
On the right pane, next to IE Enhanced Security Configuration, click On and in the popup window, turn Off the appropriate connection type (Administrators or Users). If unsure, turn off both connection types.