Protecting your SharePoint website with Cloud Access Manager
Protecting your SharePoint website with Cloud Access Manager
Now the trust has been established between Cloud Access Manager and SharePoint Server, you can protect your SharePoint website with Cloud Access Manager.
To protect your SharePoint website with Cloud Access Manager
- Open the SharePoint Central Administration console and navigate to Manage Web Applications.
- Select the Application to protect and then click Authentication Providers.
- Select the required Zone.
- Scroll down to the Trusted Identity provider section and ensure that Trusted Identity provider is selected.
-
Select the Cloud Access Manager authenticator you created previously.
NOTE: If you created the authenticator using the utility, it will be called CAM.
NOTE: Clear the Enable Windows Authentication check box. If more than one authenticator is specified, the user will be prompted to select which authenticator to use when SharePoint opens.
-
Click Save and return to Application Management.
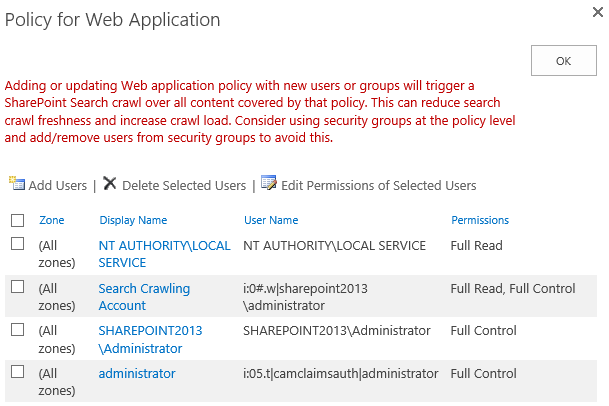
Finally you need to set permissions for users and groups to access your SharePoint sites.
Enabling SharePoint People Picker functionality
To enable SharePoint People Picker functionality with Cloud Access Manager for Microsoft SharePoint
-
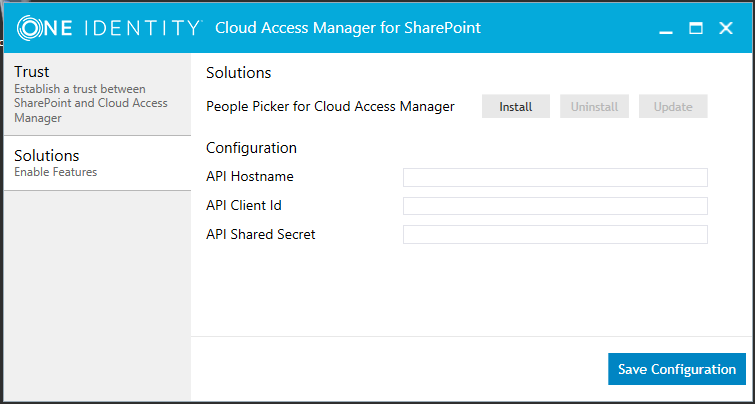
In the Cloud Access Manager for SharePoint application, select the Solutions tab.
- In the API Hostname field, enter the Cloud Access Manager Server hostname.
-
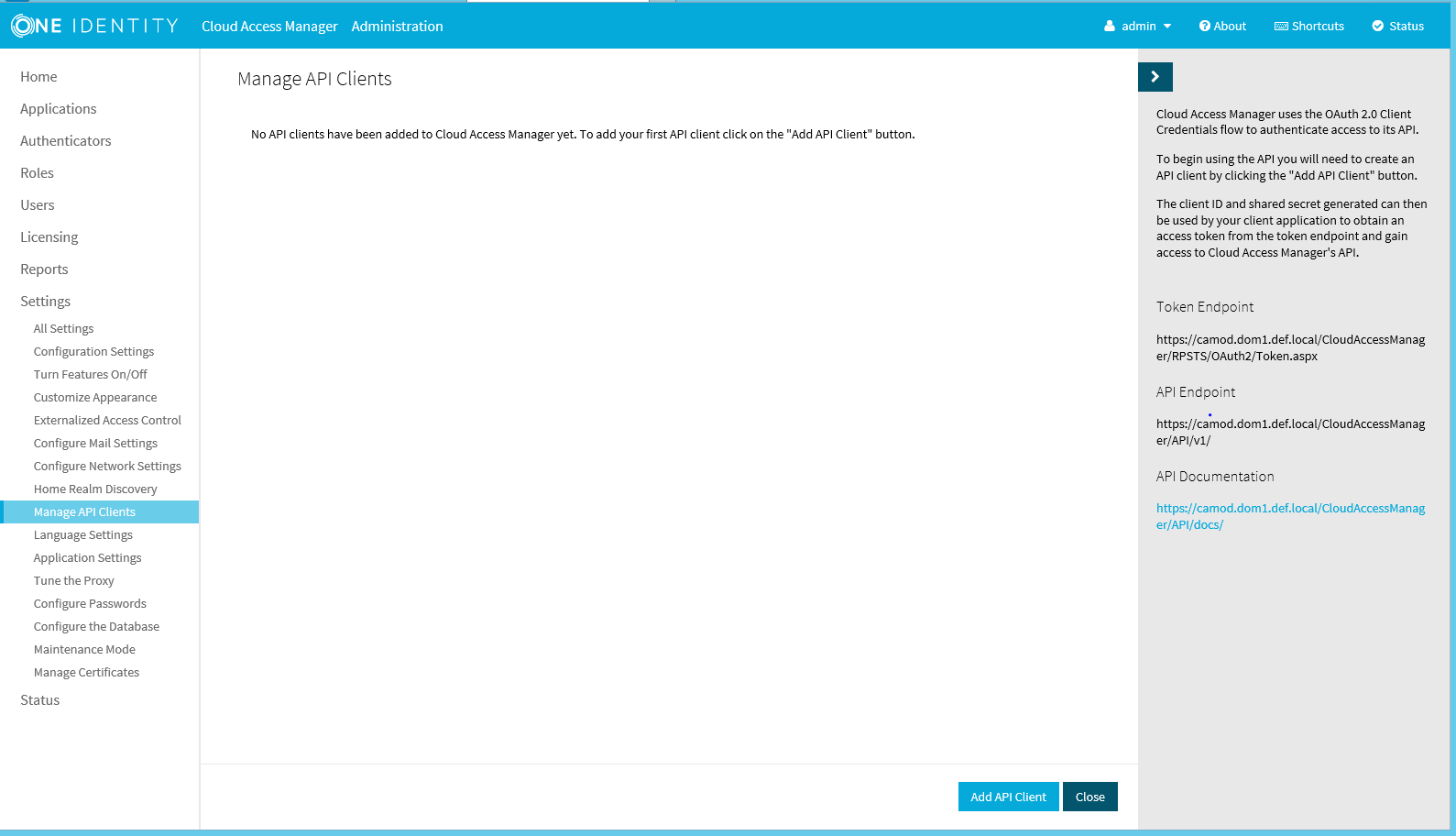
In the Cloud Access Manager Application Portal, select Settings, then Manage API Clients.
-
Click Add API Client.
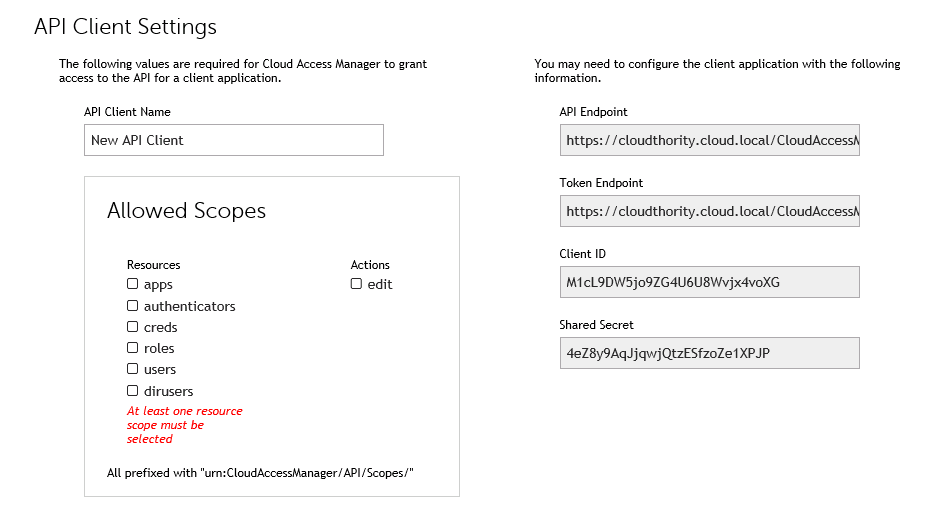
- Enter a name for the client and select roles and dirusers in the Allowed Scopes section.
- Copy and paste the Client ID and Shared Secret into the appropriate fields in the Cloud Access Manager for SharePoint application and then click Save.
- In the Cloud Access Manager for SharePoint application click Save Configuration, and then click Install.
Using the SharePoint People Picker
Before you use the Cloud Access Manager SharePoint people picker solution you need to ensure that Ambiguous Name Resolution (ANR) is enabled for all Active Directory attributes that you are using to map your Cloud Access Manager users to SharePoint user accounts. By default this is the mail attribute. For details on how to configure ANR in Active Directory, please refer to Microsoft TechNet:
To use the SharePoint People Picker
- To allow user access through your authenticator use the User Policy editor in the SharePoint application ribbon for your SharePoint web application.
- Select All Zones, then click Next.
- Select Add Users.
-
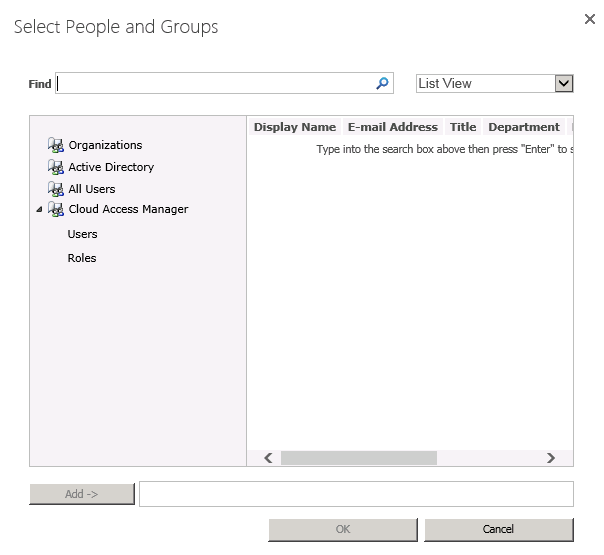
To open the SharePoint People Picker, select the address book icon below the Users field. If you have installed the Cloud Access Manager for People Picker, you will see Cloud Access Manager in the tree with two sub-categories of Users and Roles.
- If you do not enter any search criteria in the Find field to search the Cloud Access Manager address book, all available Cloud Access Manager roles will be found.
- If you enter search criteria in the Find field to search the Cloud Access Manager address book, any users or roles that match the criteria you specified will be found.
-
Select the users or roles you want to allow access to your SharePoint sites.
NOTE: If you add users manually from the Active Directory address book, they must be added by their email address to the new authentication provider — not by their sAMAccountName or other identifier. Remember to check that test users have the mail attribute populated in Active Directory as it is not populated by default.
You can now Single Sign-On (SSO) to the SharePoint application from a Cloud Access Manager user log in.
Adding Microsoft SharePoint to Cloud Access Manager using the reverse proxy
Adding Microsoft SharePoint to Cloud Access Manager using the reverse proxy
This section describes how to configure your SharePoint Server for authentication using the reverse proxy, including how to configure SharePoint for form-fill configuration.
In addition you need to configure SharePoint Server for forms based authentication to allow a Cloud Access Managerform-fill application to operate. For further information, please refer to Microsoft TechNet for SharePoint Server 2010 and SharePoint Server 2013 configuration steps.
|
|
NOTE: Integrated Windows Authentication (IWA) and HTTP basic authentication are also valid authentication configuration options when using the reverse proxy. For further information, please refer to the One Identity Cloud Access Manager Configuration Guide. |
|
|
NOTE: Microsoft Office rich client applications, for example desktop Microsoft Office 2007 and Microsoft Office 2013, are not supported when Cloud Access Manager is used to proxy SharePoint 2013; you should use WS-Federation if rich client support is required. |
To enable Cloud Access Manager to use the reverse proxy with SharePoint Server
-
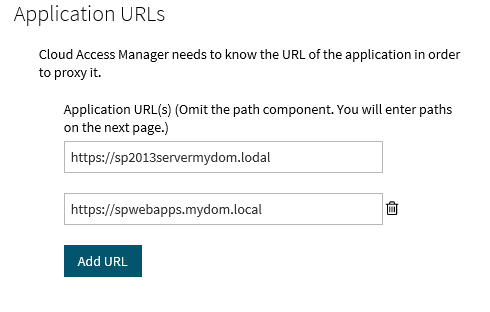
Manually configure a SharePoint application using the form-fill authentication method as described in the One Identity Cloud Access Manager Configuration Guide.
NOTE: For SharePoint Server 2013, configure the Application URLs to use two proxy aliases for the root-to-root mapping of your SharePoint Server and Office Web Apps Server.
The application URLs you add for the Office Web Apps farm may differ in format depending on the authentication type used. For example, you may need to add the simple server name for the Office Web Apps farm as an alias for proxying SharePoint 2013. This is due to the way SharePoint constructs its URLs.
NOTE: The SharePoint Office Web Apps server farm cannot be accessed using the proxy server until a valid Secure Sockets Layer (SSL) certificate is in place on the Cloud Access Manager Proxy.
A signed wildcard SSL certificate is required to cover the proxy server and the two previously created aliases. However, you do not need to create a new Secure Sockets Layer (SSL) certificate specific to the SharePoint configuration. For further details, please refer to Managing your SSL certificate in the One Identity Cloud Access Manager Configuration Guide.
- Next, log in to the Administration Console, and navigate to the Settings page.
- Click Show Advanced Settings.
- Click Tune the Cloud Access Manager Proxy.
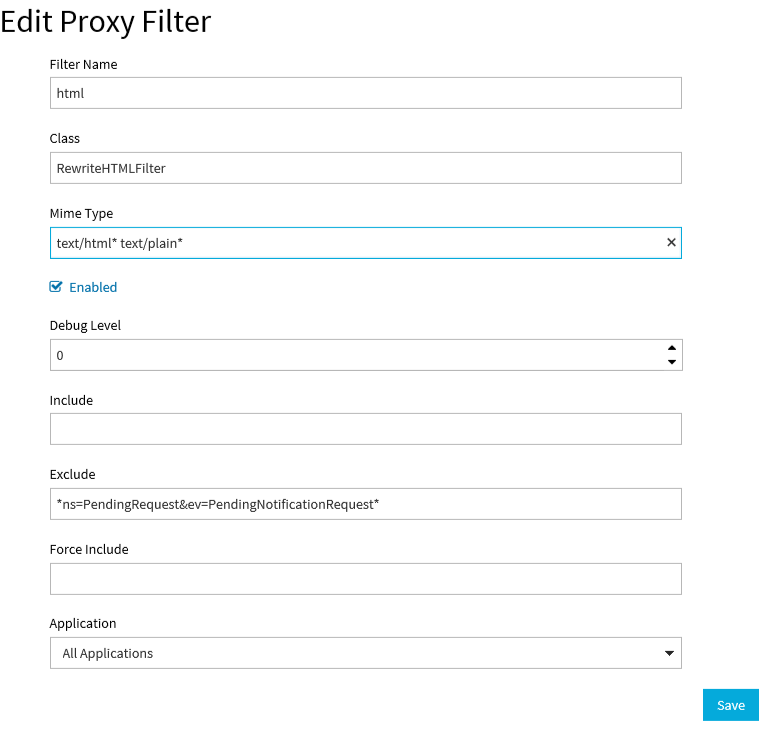
-
In the Proxy Filters, edit the Class listed as RewriteHTMLFilter, appending the Mime Type with text/plain* as the value.
- Click Save.
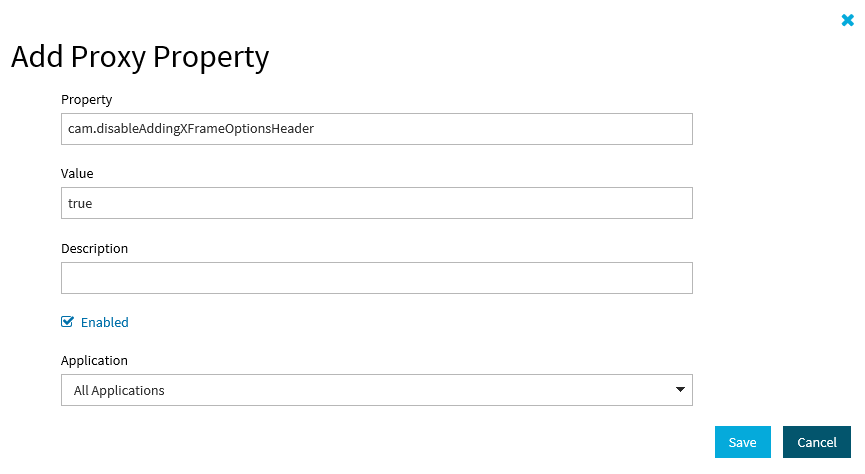
- On the Add Proxy Property page add a new property. In the Property field, enter the string cam.disableAddingXFrameOptionsHeader.
-
In the Value field, enter true. Ensure the Enabled check box is selected, this will allow Office Web Apps to load in an iFrame embedded in the SharePoint page.
- Click Save to save your settings. When you have completed these steps all links using Office Web Apps will function as expected, this includes opening and editing documents.
The application configuration is now complete.