Overview
Topics:
Cloud Access Manager is an identity bridge. It connects your users, your partners, and your customers to the applications they need.
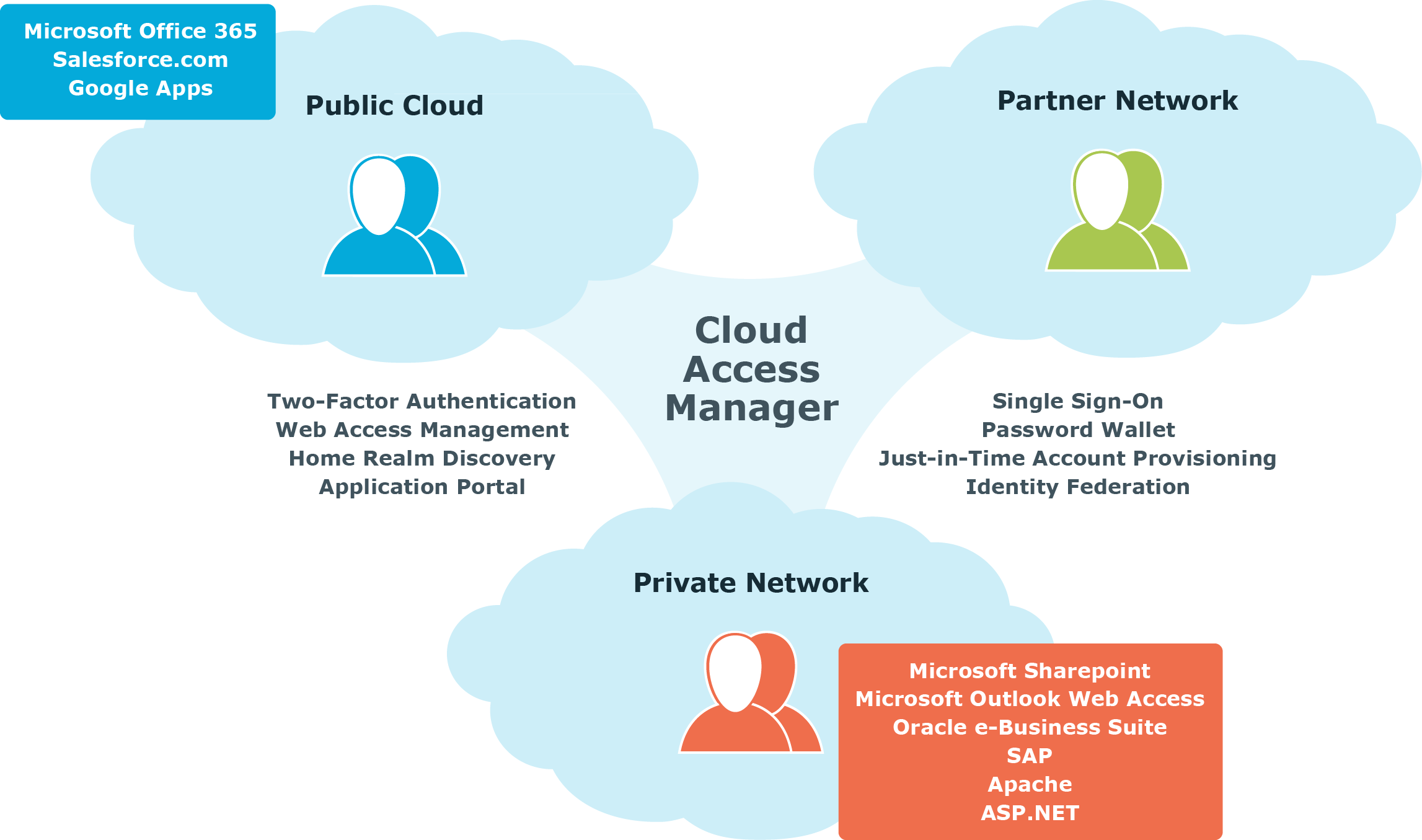
Cloud Access Manager delivers real productivity gains to your end users while minimizing the effort needed to control access to your on-premise applications and cloud service accounts:
- Password wallet and identity federation functions provide your users with the convenience of Single Sign-On (SS0) to all applications, whether they run on your private network or in the public cloud.
- Cloud Access Manager provides web access management functionality using its web proxy technology, allowing you to expose your internal web applications securely to external users.
- An easy-to-use customizable application portal provides your users with a convenient launchpad, allowing them to see and navigate to the applications they have access to.
- Identity federation with home realm discovery allows you to grant access to users in other forests within your own organization and in external organizations.
- For extra security you can configure Cloud Access Manager to require two-factor authentication for external users, or to protect sensitive applications.
- Just-in-time provisioning means that your users get access to the applications they need when they need them and not before, giving you cost savings in license seats, while at the same time reducing the administrative burden of application account provisioning.
- vWorkspace integration seamlessly brings application virtualization to the Cloud Access Manager environment, allowing vWorkspace application links to be displayed in the application portal, along with other web applications.
- For extra security you can configure Cloud Access Manager to require two-factor authentication for external users, or to protect sensitive applications.
- The Security Analytics Engine provides adaptive authentication, this enables the types of authentication users require to access applications to vary based on a variety of risk factors.
Clientless web single sign-on
Cloud Access Manager can automatically log users on to almost any web application. While its web proxy component can automate login to applications that require Kerberos, NT LAN Manager (NTLM), HTTP, or forms-based authentication, its built-in security token service (STS) can provide Single Sign-On (SS0) to claims-aware applications that comply with either SAML or WS-Federation standards.
Cloud Access Manager’s secure Password Wallet holds the user’s application credentials. Once Cloud Access Manager has learned the user’s credentials for an application, it will store them in the Password Wallet, and subsequently automatically forward them to the application whenever it is launched by the authenticated user through Cloud Access Manager.
In a Windows Active Directory environment, a Kerberos ticket is created and stored on a user’s computer when the user logs in. This ticket allows the user to access services on the network without having to enter their username and password again. Because Cloud Access Manager can accept Kerberos tickets as a form of authentication, Windows authenticated users can launch their application portal directly, without the need to log on again.
In addition, because Cloud Access Manager uses a proxy-based approach to SSO, your users do not have to download any client software. Their credentials are stored safely in the Cloud Access Manager Password Wallet on your private network.
Web access management
Cloud Access Manager’s web proxy component acts as a security gateway to protected applications on a private network. You do not have to install and manage plugins on all of your individual web servers — configuration, auditing and control is centralized through Cloud Access Manager — and because your applications can continue to run on your internal network, they are safely protected from many web-based attacks. In addition, you can grant access to application URLs through Cloud Access Manager’s Role Editor.
Role-based access control
Privileges can be granted or denied easily and quickly through Cloud Access Manager’s Role Editor. You can create roles for members and individual users from internal and external directories and the roles can then be applied to applications, groups of applications, and Cloud Access Manager administration functions.
