Introduction
This guide describes how to deploy Cloud Access Manager within a virtual private cloud that is connected to your on-premise network using a site-to-site virtual private network (VPN). This enables you to rent virtual machines, hosted by a third party, rather than purchase hardware to host on-premise. The example in this guide describes how to use the Windows Azure platform with a SonicWALL VPN device. Virtual private clouds from other Cloud providers, such as Amazon, and other VPN devices supporting IPSec site-to-site can also be used.
For information on deploying Cloud Access Manager on-premise, please refer to the One Identity Cloud Access Manager Installation Guide.
Topics:
Configuring the SonicWALL device
Establishing the IPSec VPN connection
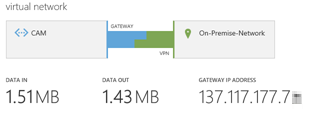
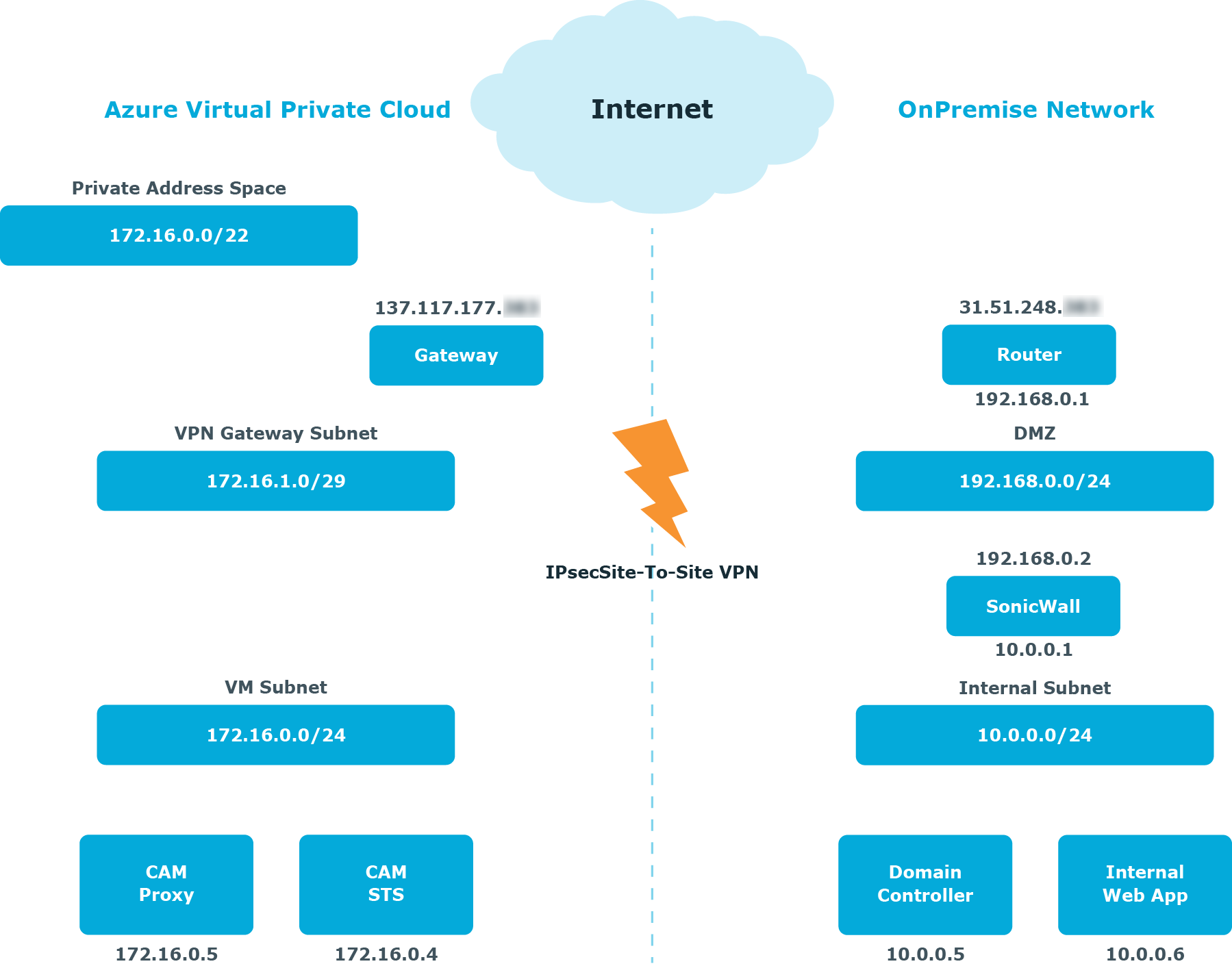
Figure 1 illustrates how to extend an on-premise network into a Windows Azure virtual private cloud to deploy Cloud Access Manager off-premise. A SonicWALL VPN device connects the on-premise network to the cloud network to enable access to the cloud network, just like any other remote office and allows the virtual machines in the cloud network to behave as if they were on-premise. You can use the on-premise VPN device to restrict access to and from the cloud network if required.
Figure 1: Extending an on-premise network
Creating a virtual network
To create a virtual network using Windows Azure
- From the Windows Azure portal, click Create a virtual network to start the wizard.
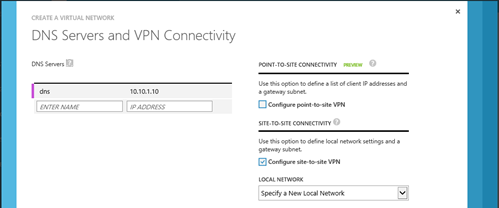
- On the DNS Servers and VPN Connectivity tab, enter the IP address of at least one Active Directory Domain Name System (DNS) server residing on the on-premise network.
-
Select the Configure site-to-site VPN check box.
- On the Site-to-Site Connectivity tab, enter the address space used by the on-premise network and the public IP address used by the SonicWALL VPN device.
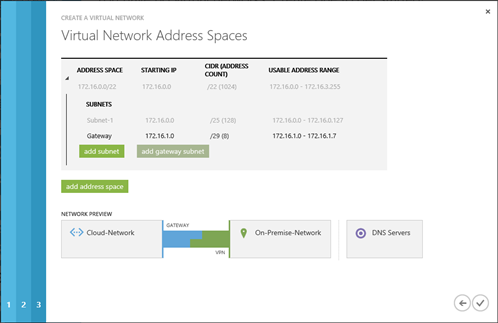
- On the Virtual Network Address Spaces tab, enter the address space to use for the virtual network. This must not clash with the on-premise network.
- Add a subnet to use for the virtual network.
-
Add a gateway subnet. This subnet is used for the Windows Azure VPN Gateway endpoint to enable routing between the on-premise network and the cloud network. The Windows Azure VPN Gateway endpoint uses two IP addresses from this subnet to set up its routing.
- Complete the wizard and wait a few moments while the virtual network is created.
- Return to the network dashboard and click CREATE GATEWAY, then select Static Routing.
- When it has been created, the public IP address of the Windows Azure VPN Gateway is displayed. A shared key is also generated. Click MANAGE KEY to view the shared key.
Configuring the SonicWALL device
To configure a SonicWALL device
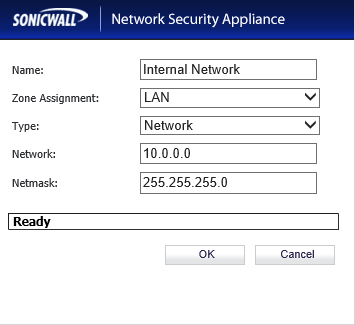
-
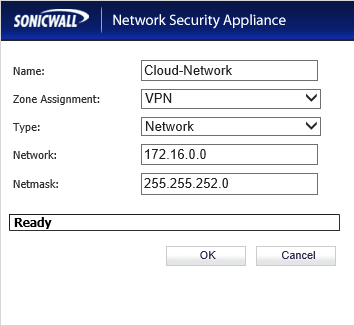
Create a new security object for the virtual network.
-
If not already present, create a new security object for your on-premise network.
-
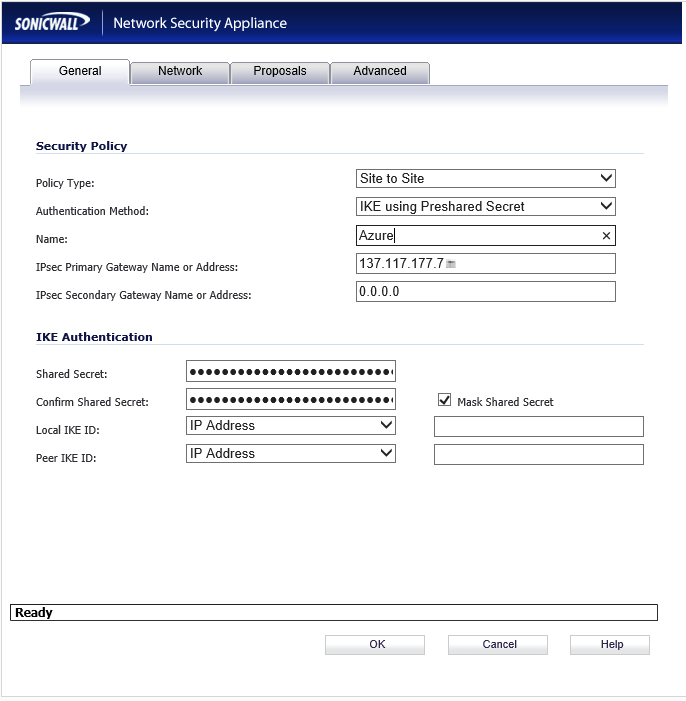
Create a virtual private network (VPN) Policy.
-
Select a Policy Type of Site-to-Site.
-
Select an Authentication Method of IKE using Preshared Secret.
-
In the IPsec Primary Gateway Name or Address field, enter the GATEWAY IP ADDRESS displayed on the Virtual Network page of the Windows Azure Management Portal.
-
In the Shared Secret field, enter the VPN KEY obtained from the Windows Azure network dashboard.
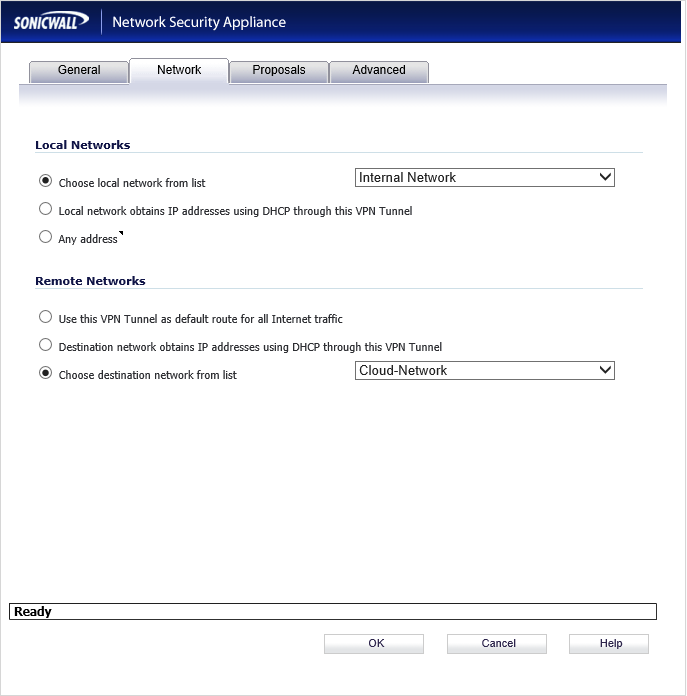
-
On the Network tab, select the local and remote network security objects created in steps 1 and 2.
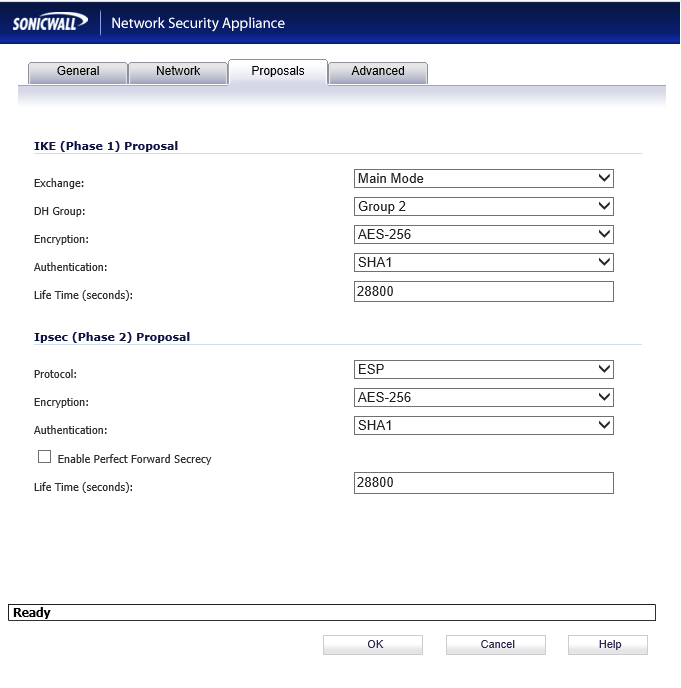
-
On the Proposals tab, select an Exchange type of Main Mode and an Encryption type of AES-256.
-
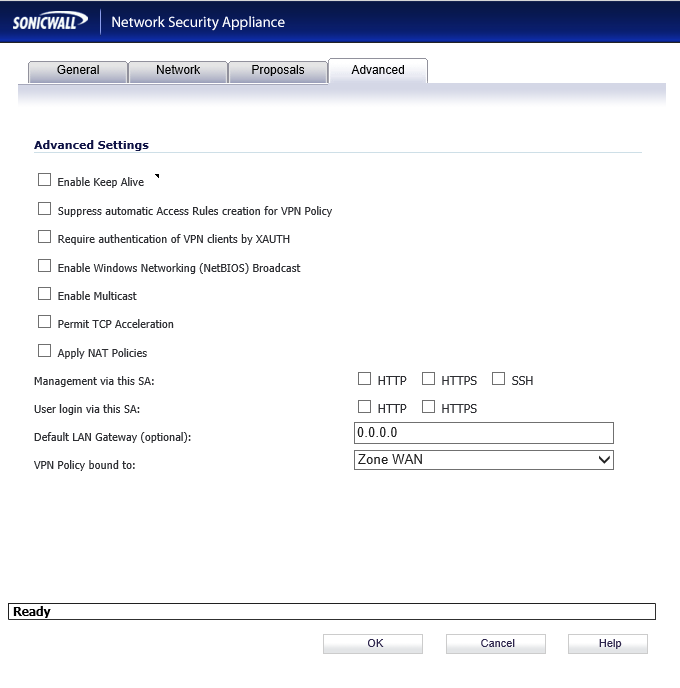
Finally, on the Advanced tab, in the VPN Policy bound to: field, select Zone WAN interface.
Establishing the IPSec VPN connection
Within the Windows Azure user interface, navigate to the network dashboard and click Connect to establish the virtual private network (VPN) connection.