Data Governance Edition is designed to serve the needs of different users.
Table 31: Typical users and associated tasks
|
Business Owner |
- Resource owner.
- Uses the web portal.
- Reviews the resource security and usage; approves or denies requests for resource access; requests access on behalf of others, such as a new identity; and validates the security on resources.
- Can view and assign a classification level to their owned resources.
- Attests to the authorizations specified for the resources they own. A business owner who is also a department manager, performs access attestations for their department identities.
Business owners are automatically assigned to the Data Governance | Direct Owners application role when they are assigned as the business owner of a resource. They must also be assigned to the Request & Fulfillment | IT Shop | Product Owners application role or an application role under the Product Owners role to approve IT Shop requests.
For more information on how to perform the business owner tasks, see Managing governed resources using the web portal |
|
Compliance Officer\Security Officer |
- Responsible for ensuring policies are created and are being enforced in the company.
- Creates "Governance Programs", including all the required policies and workflows.
- Verifies the state and progress of governance programs.
- Oversees the activities of IT security personnel.
This user must be assigned the Identity & Access Governance | Compliance & Security Officer application role.
For more information, see Application roles. |
|
Data Governance Administrator |
- Maintains and edits resource security using the Manager.
- Facilitates business owner and auditor requests.
- Performs ad-hoc investigations of the rights of users and groups.
- Configures and deploys Data Governance Edition.
- Sets the resource owner and business owner.
- Defines classification levels for use in classifying governed resources.
- Maintains Data Governance Edition.
- Delegates access to Data Governance Edition.
- Implements the workflow defined by security officers, business owners, and others who need to consume the services of Data Governance Edition.
- Assigns the server and share root path to be used for creating file system shares requested through the IT Shop. Also, defines the group naming pattern to be used to create the Active Directory groups for the new share.
This user must be assigned the Data Governance | Administrators application role. They must also be assigned to the Request & Fulfillment | IT Shop | Product Owners application role or an application role under the Product Owners role to approve IT Shop requests.
For more information, see Application roles. |
|
Identity\End-User\Resource Consumer\Knowledge Worker |
- Uses the web portal.
- Makes IT Shop requests to gain access to resources.
- Makes IT Shop requests to create file system shares.
All active identities are automatically members of the Identity & Access Lifestyle shop and can therefore make self-service requests. |
|
Identity manager |
- Uses the web portal.
- Approves or denies requests for creating file system shares.
Identity managers must be assigned the Request & Fulfillment | IT Shop | Product Owners application role or an application role under the Product Owners role to approve IT Shop requests. |
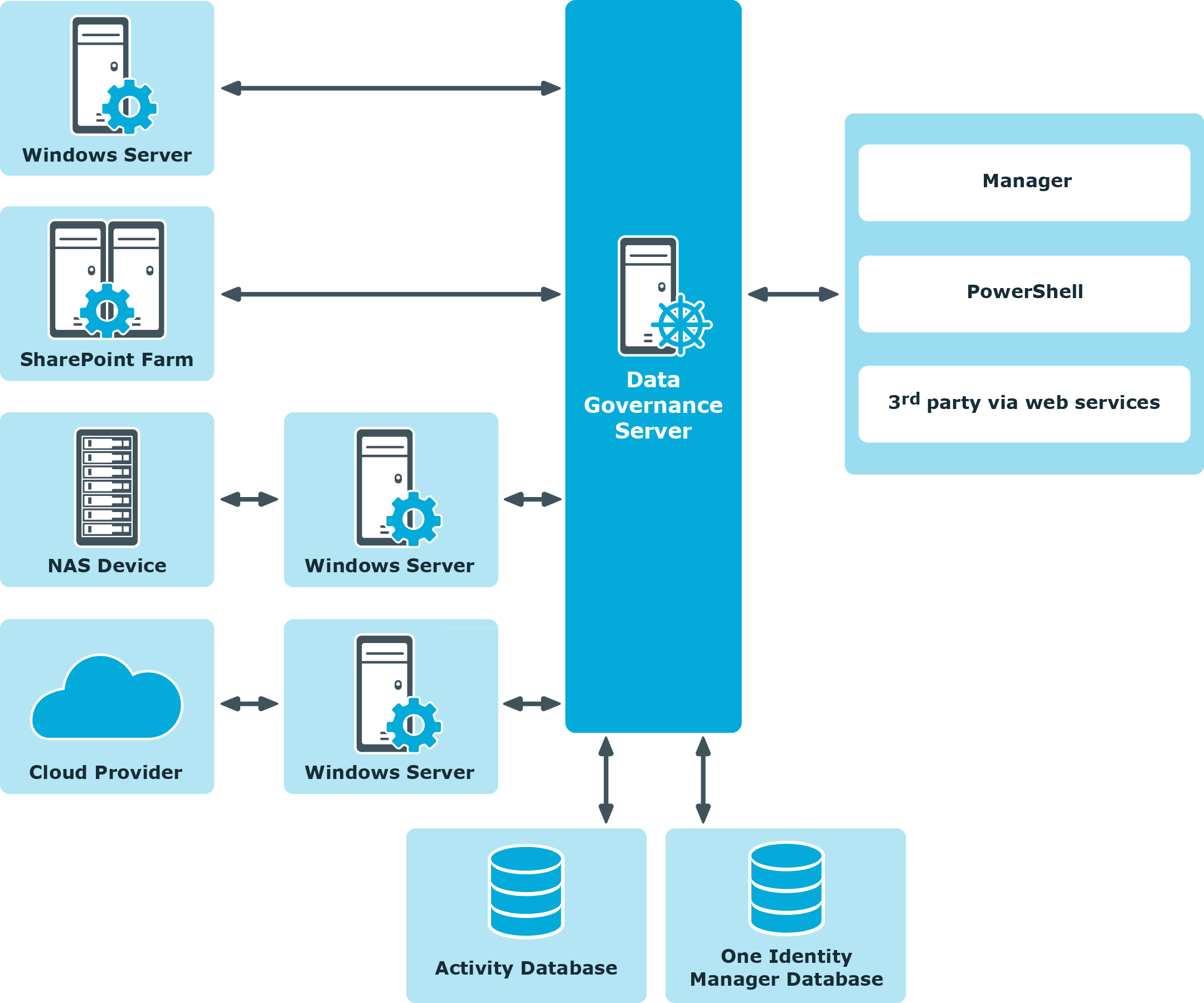
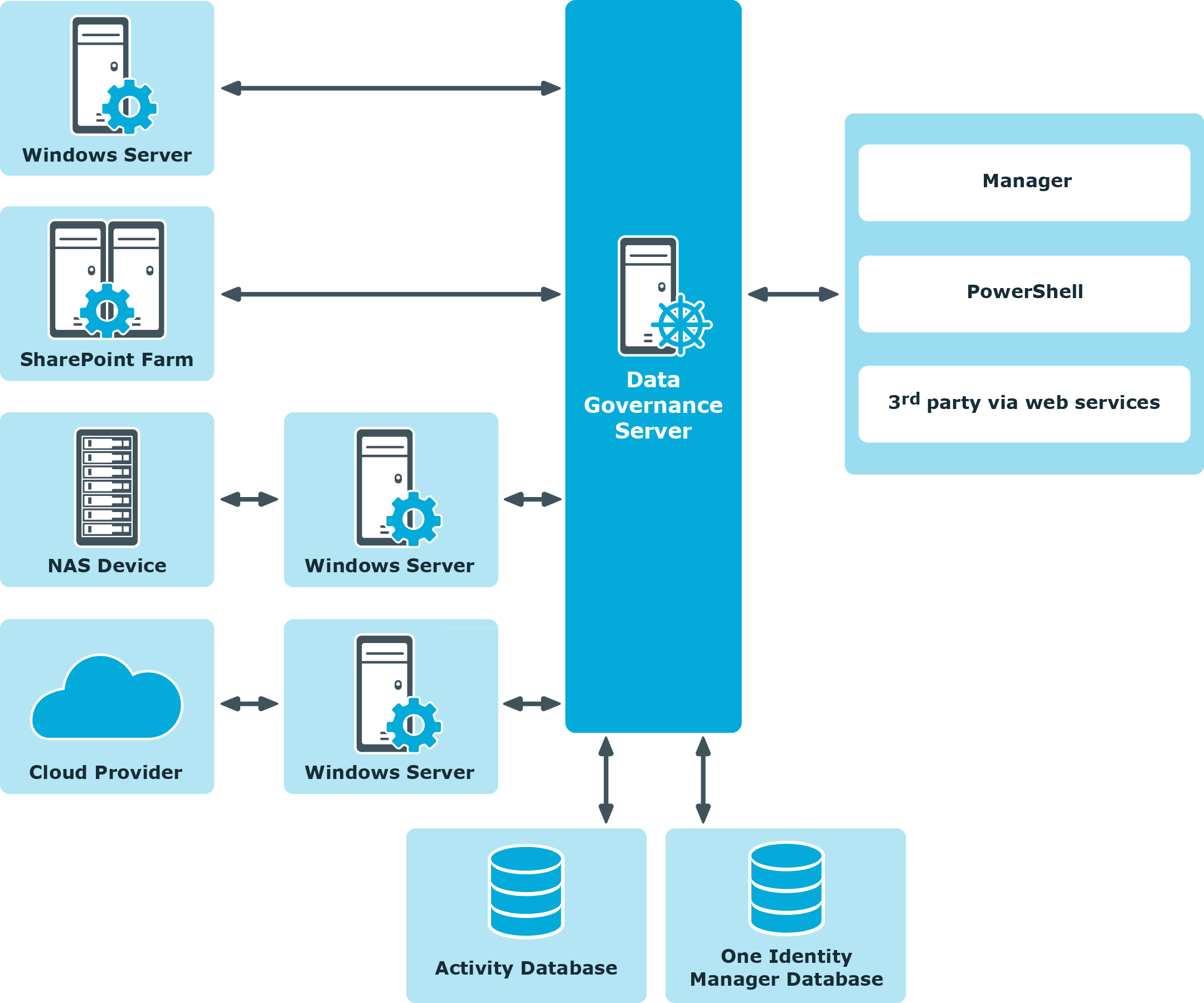
Data Governance Edition consists of the following components:
-
Data Governance server: The server acts as an intermediary between the agents and the databases where information is stored. It coordinates all agent deployments and communication, and manages the security index for each managed host.
The server is the central authority that receives and indexes information from agents deployed on target computers. It only maintains a subset of information for the computers that are being indexed (essentially access to specific resource types on managed computers). When you request detailed access information, the server attempts to contact the local agent and provide information stored in the local agent index.
- Data Governance agents: Agents collect security data from your managed hosts, and if configured, can also collect resource activity data. The agent cache stores all the detailed indexed information.
- Databases: The One Identity Manager database stores configuration and security information. The Data Governance Resource Activity database stores resource activity information.
- Managed hosts: A managed host is any network object that can host resources and can be assigned an agent to monitor security and resource activity. Managed hosts store the data on which users perform actions. Currently supported managed hosts include Windows computers, Windows clusters, certain network attached storage (NAS) devices, SharePoint farms and certain cloud providers, including SharePoint Online and OneDrive for Business. See the One Identity Manager Data Governance Edition Deployment Guide for a complete list of supported platforms.
For more information about component communications and how communication is encrypted, see the One Identity Manager Data Governance Edition Technical Insight Guide.
Figure 2: Data Governance Edition architecture
You must perform the following activities to have a fully functional Data Governance Edition deployment:
NOTE: New in 7.0: Active Directory synchronization via the One Identity Manager service (job server) is not required for managed host deployment.
In the absence of One Identity Manager target system synchronization, the Data Governance service automatically harvests the forest topology. It creates Identity records for all members found in each domain's Domain Admins group and for the current account running the Data Governance configuration wizard. It also links these accounts to the correct Data Governance application roles, which allows you to add managed hosts and deploy agents.
When additional One Identity Manager functionality is required, including generating complete Data Governance Edition reports, perform the following steps:
-
Run the One Identity Manager Synchronization Editor to synchronize your target environments (Active Directory, and if applicable, SharePoint and Unix).
IMPORTANT: Active Directory synchronization MUST be complete before starting the SharePoint synchronization.
- Assign Data Governance application roles to Identities.
For detailed installation and configuration procedures, see:
- Installing One Identity Manager in the One Identity Manager Installation Guide.
- Install One Identity Manager Data Governance Edition in the One Identity Manager Data Governance Edition Deployment Guide.
- Readying a service account and domains for deployment.
- Working with managed hosts and agents.
- Installing, Configuring and Maintaining the Web Portal in the One Identity Manager Installation Guide and the One Identity Manager Web Portal User Guide.
- Setting Up Synchronization with an Active Directory Environment in the One Identity Manager Administration Guide for Connecting to Active Directory.
- Setting Up Synchronization with a SharePoint Environment in the One Identity Manager Administration Guide for Connecting to SharePoint.
- One Identity Manager Application Roles in the One Identity Manager Identity Management Base Module Administration Guide.
The following application roles are specifically for Data Governance Edition. They are to be used with One Identity Manager application roles. For details on applying application roles, see One Identity Manager Application Roles in the One Identity Manager Identity Management Base Module Administration Guide.
- Data Governance | Access Managers
Members of this role can access all information related to Data Governance Edition, and can query information from Data Governance agents. Also, they can modify the security of objects contained on managed hosts.
-
Data Governance | Administrators
Members of this role can perform all administrative tasks necessary for the management of Data Governance Edition. This includes deploying and configuring managed hosts, managing data access, editing security, and placing data under governance.
- Data Governance | Business Owner
Members of this role can view and edit information on resources they own. This role is used to control permissions in the web portal, and approvals and attestation workflows.
- Data Governance | Direct Owners
This role is held by accounts and roles marked as the owners of resources within Data Governance Edition. It cannot be assigned manually; it is assigned programmatically when ownership is assigned.
-
Data Governance | Managed Resources
A default container used for roles automatically generated by Data Governance Edition managed resources. For more information on managed resources, see the One Identity Manager Data Governance Edition IT Shop Resource Access Tickets User Guide.
-
Data Governance | Operators
Members of this role have read-only access to the Managed hosts view and Agents view in the Manager.
Note: This role should not be used in conjunction with any of the other Data Governance application roles.
- Identity & Access Governance | Compliance & Security Officer
Members of this role have a view into all security-related information collected by Data Governance Edition. They are responsible for ensuring security-related compliance regulations are being followed correctly.