To configure a particular Administration Service using the Active Roles Console, you need to manually specify the Administration Service to connect to. Otherwise, the Console automatically selects the Administration Service.
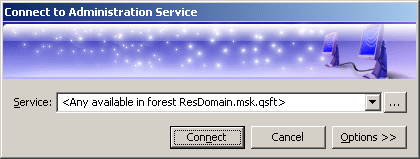
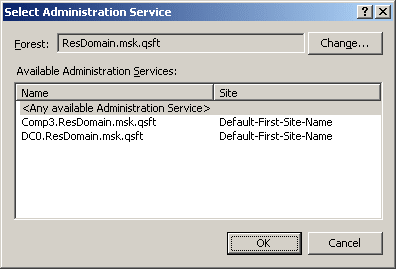
You can use the Connect to Administration Service dialog to select the appropriate Administration Service. To display this dialog, right-click Active Roles in the Console tree and click Connect. The dialog looks as shown in the following figure.
Figure 155: Connect to Administration Service
In the Service box, type or select the name of the computer running the Administration Service to connect to, then click Connect. The Service box provides a list of names that were specified for previous connection sessions. The last selected name is displayed by default.
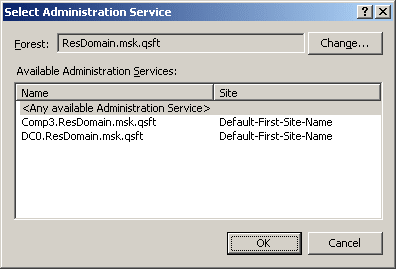
To select the Administration Service that is not in the list, click Select next to the Service box:

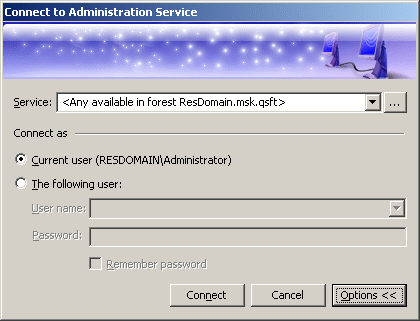
This displays the Select Administration Service dialog, shown in the following figure.
Figure 156: Select Administration Service
The Select Administration Service dialog lists the Administration Services that are available in the specified forest. You can choose a different forest by clicking Change. The list items are sorted according to priority, considering site location and service load (less loaded Administration Services are displayed at the top of the list). To add a certain Service to the Connect to Administration Service dialog, click that Service and then click OK.
If you have connected to a specific Service, the Console will attempt to automatically connect to that Service on every subsequent start. If you have selected <Any available Administration Service>, the Console will attempt to connect to the nearest, least loaded Service in the specified forest, giving preference to the Services that belong to the same replication group as the Service to which the console was connected in the previous session.
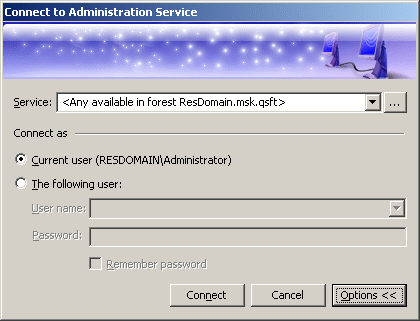
By default, the Console connects to the Administration Service in the security context of your logon account (that is, the user account to which you have logged on). This means that you can only use the Console to perform the tasks that are delegated to your user account. You have the option to establish a connection using a different account, in order to change the scope of the allowed tasks. Click Options to expand the Connect to Administration Service dialog, as shown in the following figure.
Figure 157: Connect to Administration Service
Click The following user and specify the user logon name and password of the account to be used for connection. By selecting the Remember password check box you can have the Console automatically use the specified user name and password in the future connection sessions. Otherwise, on a subsequent start, the Console will prompt you for a password.
By default, on installing Active Roles, all users are allowed to log in to the Active Roles Console. To manage the Console access for a user, you must configure the options using Configuration Center > MMC Interface Access > Manage settings. Selecting this option restricts all non-Active Roles Administrators from using the Console. All delegated users are affected, however, it does not apply to Active Roles Administrators.
To be able to log in to the Active Roles Console, the user must be delegated with the User Interfaces access rights on the User Interfaces container under Server Configuration. User Interfaces Access Templates that provide the access rights are available as part of the Active Roles built-in Access Templates in the User Interfaces container.
To delegate the control to users in the User Interfaces container you must apply the User Interface Access Template
-
In the Console tree, expand Active Roles > Configuration > Server Configuration.
-
Under Server Configuration, locate the User Interfaces container, right-click it, and click Delegate Control.
-
On the Users or Groups page, click Add, and then select the users or groups to which you want to delegate the control. Click Next.
-
On the Access Templates page, expand the Active Directory > User Interfaces folder, and select the check box next to User Interface Management-MMC Full control.
-
Click Next and follow the instructions in the wizard, accepting the default settings.
-
After you complete these steps, the users and groups you selected in Step 3 are authorized to log in to the Active Roles Console.
-
Click OK to close the Active Roles Security dialog.
Active Directory domains registered with Active Roles are referred to as managed domains. Each Administration Service maintains a list of managed domains, and stores this list in the Administration Database as part of the service configuration.
In the Active Roles Console, the Add Managed Domain wizard is used to register domains for management. You can access the wizard as follows:
-
Click the Console tree root.
-
In the details pane, in the Domains area, click Add Domain.
The Add Managed Domain wizard prompts you for the following information:
You have the option to use the default credentials (the service account of the Administration Service) or enter the user name and password of a different account (override account). In both cases, the account must have adequate rights in the managed domain. For more information, see Access to managed domains in the Active Roles Installation Guide.
NOTE: This option applies to all Administration Service in your environment. Each Administration Service in your environment will use its own service account to access the domain. Since different service accounts may have different levels of access to the domain, Active Roles may have different access rights to the domain, depending on which Administration Service is being used to manage the domain. The result is that the behavior of Active Roles may vary when you switch to a different Administration Service.
After you add a managed domain, the Administration Service retrieves the domain information, such as the Active Directory schema and the hierarchy of containers. This process is referred to as loading domain information.
It may take a few minutes for the Administration Service to load the domain information. Once this process is completed, the domain is available for management. Select the Active Directory item in the Console tree and press F5 to refresh the details pane and display the new domain. To start managing the domain, select it in the details pane and press Enter; or expand the domain item in the Console tree.
It is possible to remove a domain from the list of managed domains. Once removed, the domain and all directory objects contained in the domain can no longer be managed with Active Roles. To remove a managed domain, select the Console tree root and click Go to Managed Domains in the details pane, in the Domains area. This causes the details pane to display a list of managed domains. In the list, right-click the domain you want to remove, and click Delete.
The operation of adding a managed domain results in the creation of an object that holds the registration information about the domain. For this reason, it is also referred to as registering a domain with Active Roles.
To add a managed domain
-
In the Console tree, expand Configuration > Server Configuration.
-
Under Server Configuration, right-click Managed Domains, and select New > Managed Domain to start the Add Managed Domain wizard.
-
On the Welcome page of the wizard, click Next.
-
On the Domain Selection page, do one of the following, and then click Next.
-
On the Active Roles Credentials page, click one of these options that determine the logon information that Active Roles will use to access the domain:
If you choose the second option, type the user name and password of the user account you want Active Roles to use when accessing the domain.
-
Click Next, then click Finish.
To remove a managed domain
-
In the Console tree, expand Configuration > Server Configuration.
-
Under Server Configuration, click Managed Domains.
-
In the details pane, right-click the domain you want to remove, then click Delete.
NOTE: Consider the following when managing managed domains:
-
You can use the Properties command on an object held in the Managed Domains container to view or modify the registration information for the respective managed domain. For example, it is possible to change the logon information that is used to access the domain:
-
On the General tab in the Properties dialog, choose the appropriate option.
-
Click Apply.
You can choose one of the two options that are listed in Step 5 of the procedure above.
-
The Managed Domains container holds the registration objects for all domains that are registered with Active Roles. You can un-register domains by deleting objects from that container.
-
By default, no domains are registered with Active Roles. When you register a domain, the domain registration is saved as part of the Active Roles configuration.