You can display a banner with a configurable text on the web and console login screen of One Identity Safeguard for Privileged Sessions (SPS).
Users will see the banner every time they try to log in to SPS. The login screen displays the banner text as plain text, with whitespaces preserved.
To enter a banner message, navigate to Users & Access Control > Settings — Authentication banner.
Figure 79: Users & Access Control > Settings > Authentication banner — Enter a banner message
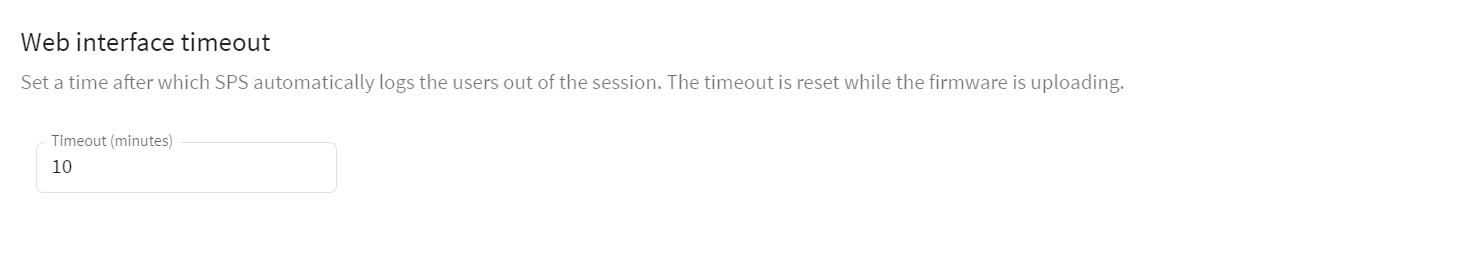
By default, One Identity Safeguard for Privileged Sessions (SPS) terminates the web session of a user after 10 minutes of inactivity. To change the value of this timeout, adjust the Users & Access Control > Settings > Web interface timeout option.
Figure 80: Users & Access Control > Settings — Web interface timeout
By default, One Identity Safeguard for Privileged Sessions (SPS) users are managed locally on SPS. To add local users in SPS, complete all steps of the following procedure:
-
Create users.
For detailed instructions on how to create local users, see Creating local users in One Identity Safeguard for Privileged Sessions (SPS).
-
Assign users to groups.
For details about how to add a usergroup, see Managing local user groups.
-
Assign privileges to groups.
For information on how to control the privileges of usergroups, see Managing user rights and usergroups.
This section describes how to create local users.
NOTE: The admin user is available by default, and has all possible privileges. It is not possible to delete this user.
When using RADIUS authentication together with local users, the users are authenticated to the RADIUS server, only their group memberships must be managed locally on One Identity Safeguard for Privileged Sessions (SPS). For details, see Authenticating users to a RADIUS server.
To create a local user
-
Navigate to Users & Access Control > Local Users and click  .
.
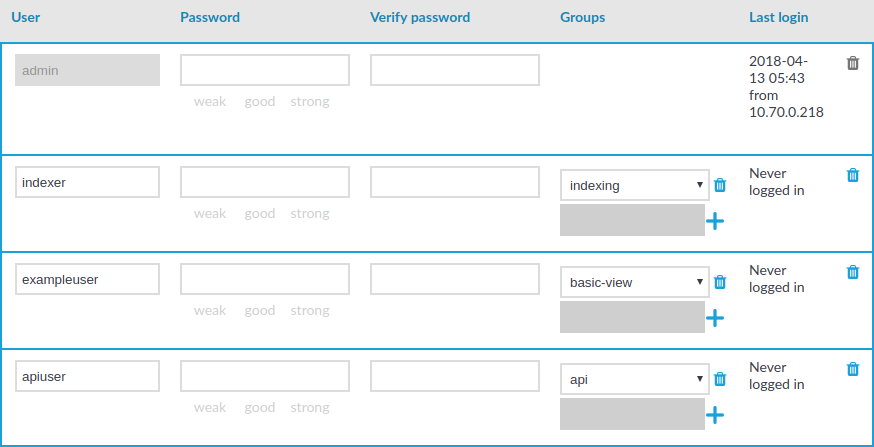
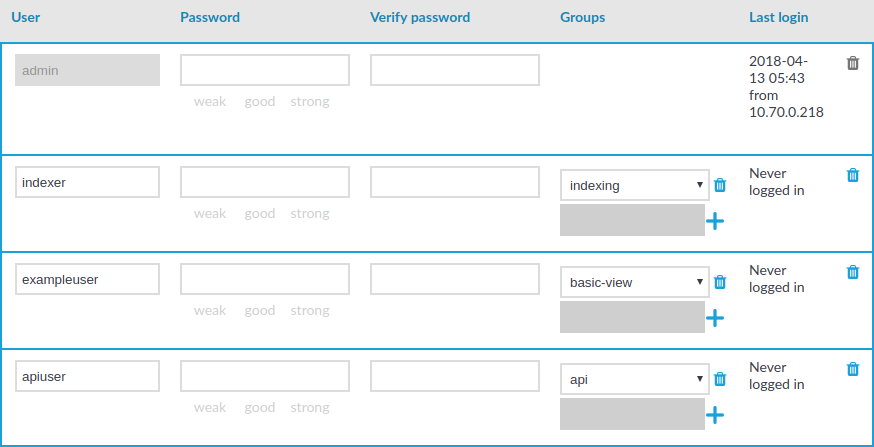
Figure 81: Users & Access Control > Local Users — Creating local users
-
Enter the username in the User field.
NOTE: For the username of SSH users, only valid UTF-8 strings are allowed.
The following characters cannot be used in usernames: <>\/[]:;|=,+*?
-
Enter a password for the user in the Password and Verify password fields.
The strength of the password is indicated below the Password field, as you type. To set a policy for password strength, see Setting password policies for local users. The user can change the password later from the SPS web interface, and you can modify the password of the user here.
Use strong passwords: at least 8 characters that include numbers, letters, special characters, and capital letters. For local One Identity Safeguard for Privileged Sessions (SPS) users, require the use of strong passwords (set Users & Access Control > Login options > Minimal password strength to strong). For more information, see "Setting password policies for local users" in the Administration Guide.
NOTE: SPS accepts passwords that are not longer than 150 characters and supports the following characters:
NOTE: If possible, use a random password generator.
To create a strong password:
For strong passwords, do not use:
-
Personal information in the passwords
-
Sequential letters or numbers
-
The word password as the password
-
Keyboard paths (for example, qwerty)
-
Click  in the Groups section and select a group that the user will be a member of. Repeat this step to add the user to multiple groups.
in the Groups section and select a group that the user will be a member of. Repeat this step to add the user to multiple groups.
You can also modify the group membership of local users here.
To remove a user from a group, click  next to the group.
next to the group.
-
To save the modifications, click Commit.

 .
.
 next to the group.
next to the group.