Identities, devices, and workdesks can only be members in roles that are extensions of the BaseTree table. These role are display in views, each of which represents a certain of the BaseTree table. To map company structures, the One Identity Manager data model obtains the following views:
Table 2: BaseTree table views
|
Department |
Graphical representation of departments |
|
Locality |
Graphical representation of locations |
|
PROFITCENTER |
Graphical representation of cost centers |
|
ORG |
Graphical representation of business roles |
|
AERole |
Application role mapping |
NOTE: Because the views are subsets of the BaseTree table, all the inheritance mechanisms described below also apply to the views.
Inheritance comes from the BaseTree table. The BaseTree table can map any number of hierarchical role structures using the UID_Org - UID_ParentOrg relationship. These are stored in the BaseTreeCollection table. All the roles inherited from the given role are listed and, depending on their subset of the table BaseTree there is a corresponding, so-called *Collection table containing a subset of the role hierarchy.
The following relations apply in the BaseTreeCollection table:
This principle also applies to bottom-up trees that pass inheritance from bottom to top, even if the parent relationship from the BaseTree table appears to be reversed.
Each role inherits from itself.
Each role in a role hierarchy must be related to the OrgRoot table (Role classes). OrgRoot is the anchor for role hierarchies. A role hierarchy is always mapped for one role class only. Roles from different role classes may not be in one and the same role hierarchical or point to each other through a parent-child relationship.
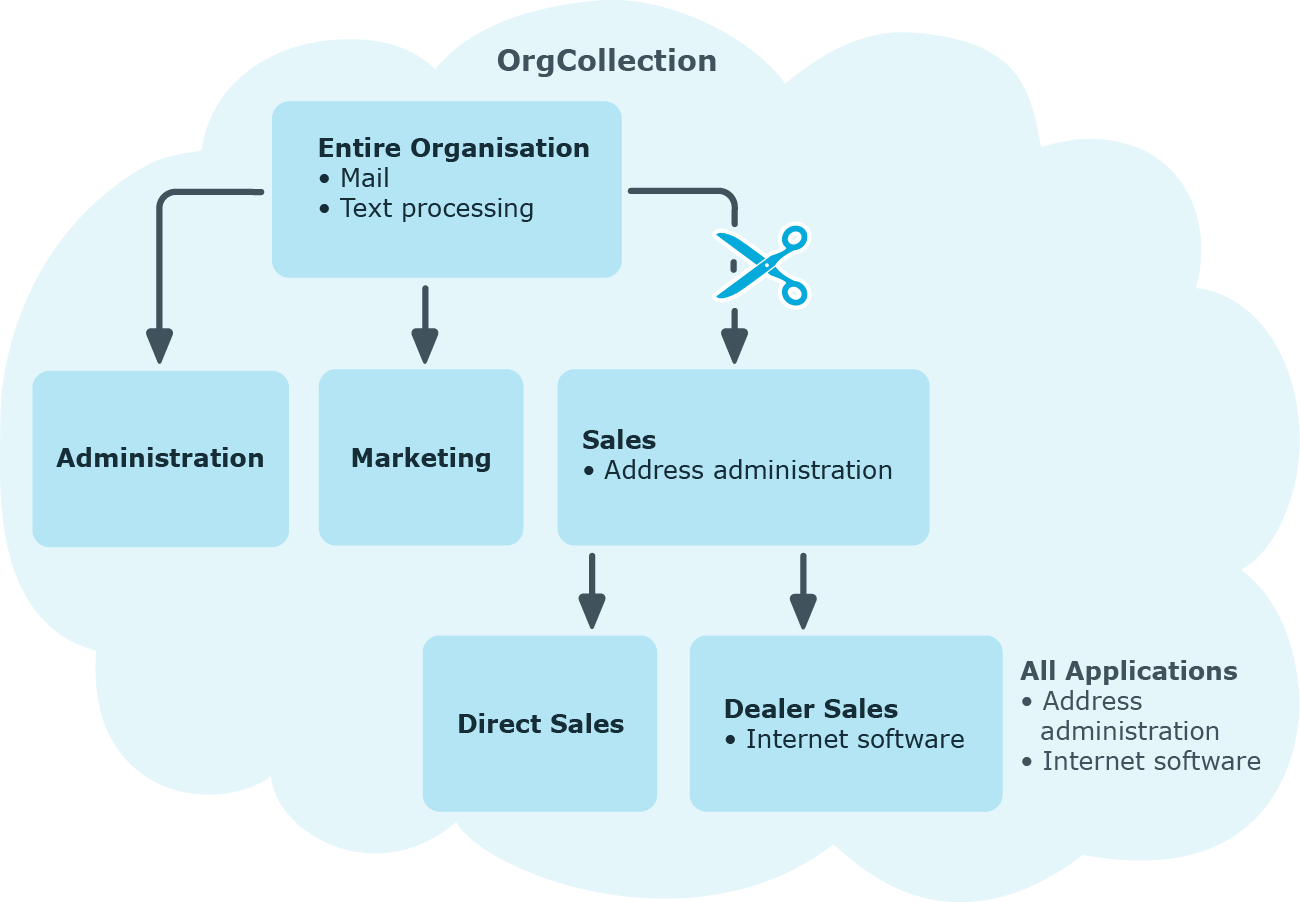
Figure 11: Hierarchical role structure based on an OrgCollection
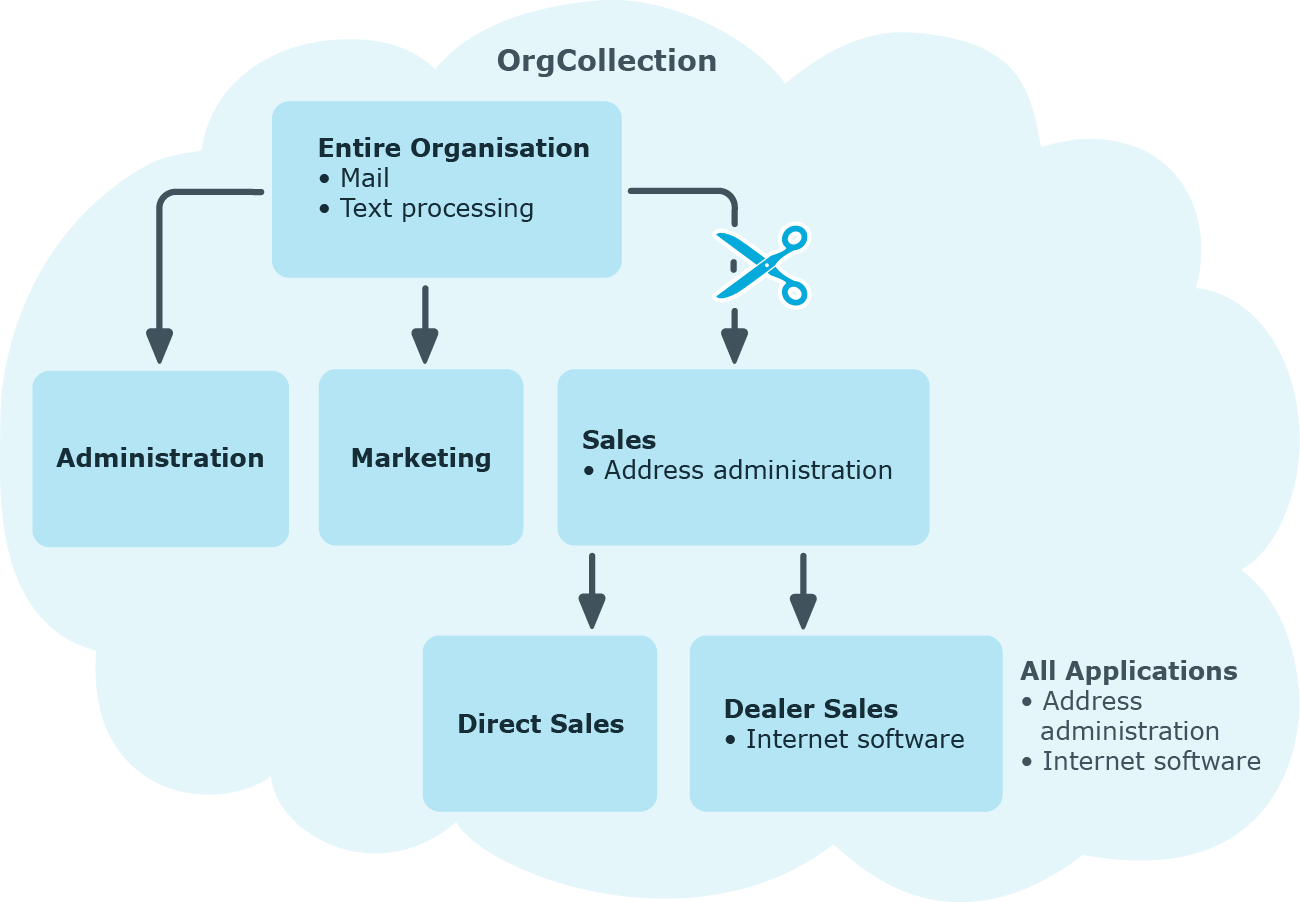
A role inherits everything that is assigned to its parents in the role hierarchy including those it assigned to itself. If the number of roles from which the role has inherited something changes, the assigned objects are recalculated for all members of this role. If the number of assigned objects of one class changes, the objects assigned in this class are recalculated for all members of the role. If a software application is assigned to a parent role, the members of the BaseTreeHasApp table are recalculated.
The members of a role inherit all their assignments through primary and secondary role structures in accordance with the BaseTree table and also previous structures in accordance with the BaseTreeCollection table .
When inheritance is calculated, an entry is made for each assignment in the corresponding assignment table. Each table, in which assignments are mapped, has an XOrigin column. The origin of an assignment is stored in this column as a bit field. Each time an entry is made in the assignment table, the bit position is changed according to the assignment type. Each assignment type changes only its allocated bit position.
That means:
-
Bit 0: direct assignment.
-
Bit 1: indirect assignment but not through a dynamic role.
-
Bit 2: assignment through a dynamic role.
-
Bit 3: assignment through an assignment request.
-
Bit 4: module specific bit. For more information, see the administration guide of the module in which the bit is used.
Table 3: Possible values for column XOrigin
|
0 |
0 |
0 |
1 |
1 |
Only directly assigned. |
|
0 |
0 |
1 |
0 |
2 |
Only indirectly assigned. |
|
0 |
0 |
1 |
1 |
3 |
Directly and indirectly assigned. |
|
0 |
1 |
0 |
0 |
4 |
Assigned through dynamic roles. |
|
0 |
1 |
0 |
1 |
5 |
Assigned directly and through dynamic roles. |
|
0 |
1 |
1 |
0 |
6 |
Assigned indirectly and through dynamic roles. |
|
0 |
1 |
1 |
1 |
7 |
Assigned directly, indirectly, and through dynamic roles. |
|
1 |
0 |
0 |
0 |
8 |
Assignment request. |
|
1 |
0 |
0 |
1 |
9 |
Assigned by assignment request and directly. |
|
1 |
0 |
1 |
0 |
10 |
Assigned by assignment request and indirectly. |
|
1 |
0 |
1 |
1 |
11 |
Assigned by assignment request, directly, and indirectly. |
|
1 |
1 |
0 |
0 |
12 |
Assigned by assignment request and through dynamic roles. |
|
1 |
1 |
0 |
1 |
13 |
Assigned by assignment request, directly, and through dynamic roles. |
|
1 |
1 |
1 |
0 |
14 |
Assigned by assignment request, indirectly, and through dynamic roles. |
|
1 |
1 |
1 |
1 |
15 |
Assignment request, direct, indirect, and through dynamic roles. |
Special features of inheriting assignments though a role hierarchy
NOTE: If an assignment is inherited through a role hierarchy, bit 1 is set on the inherited assignment. Inherited assignments are consequently, always assigned indirectly even if they were originally created directly though dynamic role or an assignment request.
Example:
An Active Directory group assignment was requested for the "Europe" location. The "Madrid" sub-location inherits this assignment. In the LocalityHasADSGroup table, XOrigin is set as follows:
- Location "Europe": XOrigin='8' (assignment resource)
- Location "Madrid": XOrigin='2' (indirect assignment)
Effectiveness of assignments
The XIsInEffect column shows whether an assignment is in effect. For example, if an identity is deactivated, marked for deletion, or classified as a security risk, inheritance of company resources can be prohibited for this identity. The assignment of company resources is maintained but the assignment has no effect.
DBQueue Processor monitors changes to the XOrigin column. The XIsInEffect column is recalculated when changes are made to the value in XOrigin.
One Identity Manager supplies a configuration, which support immediate usage of hierarchical roles for departments, cost centers, locations, and application roles. However, it may be necessary to make additional role assignments depending on the company structure.
You should check the following settings and make adjustments as required:
-
Specify whether identities, devices, and workdesks and company resources may be assigned to roles.
Identity, device, workdesk, and company resource assignments are predefined for departments, cost centers, location, and application roles. The configuration of application role assignments cannot be changed.
-
Define the direction of inheritance with the hierarchy.
Top down inheritance is defined for departments, cost centers, locations, and application roles.
-
Limit inheritance for specific roles if necessary.
You can specify whether inheritance of company resources can be limited for single identities, devices, or workdesks.
-
If required, define roles that are mutually exclusive.
By specifying conflicting roles, you can prevent identities, devices, or workdesks being added to roles which contain mutually excluding company resources.
Detailed information about this topic
Identities, devices, and workdesks can inherit company resources though indirect assignment. To do this, identities, devices, and workdesks may be members of as many roles as required. Identities, devices, and workdesks obtain the necessary company resources through defined rules.
To assign company resources to roles, apply the appropriate tasks to the roles.
The following table shows the possible assignments of company resources to identities, workdesks, and devices using roles.
NOTE: Company resources are defined in the One Identity Manager modules and are not available until the modules are installed.
Table 4: Possible assignments of company resources through roles
|
Resources |
Possible |
- |
| Account definitions |
Possible |
|
|
Groups of custom target systems |
Possible (assigns to all an identity's custom defined target systems user accounts, for which group inheritance is authorized) |
- |
|
System entitlements of custom target systems |
Possible (assigns to all an identity's custom defined target systems user accounts, for which system entitlement inheritance is authorized) |
- |
|
Active Directory groups |
Possible (assigns to all an identity's Active Directory user accounts and Active Directory contacts, for which Active Directory group inheritance is authorized) |
- |
|
SharePoint groups |
Possible (assigns to all an identity's SharePoint user accounts for which SharePoint group inheritance is authorized) |
- |
|
SharePoint roles |
Possible (assigns to all an identity's SharePoint user accounts for which SharePoint role inheritance is authorized) |
- |
|
LDAP groups |
Possible (assigns to all an identity's LDAP user accounts for which LDAP group inheritance is authorized) |
- |
|
Notes groups |
Possible (assigns to all an identity's Notes user accounts for which Notes group inheritance is authorized) |
- |
|
SAP groups |
Possible (assigns to all an identity's SAP user accounts, in the same SAP system and for which SAP group inheritance is authorized) |
- |
|
SAP profiles |
Possible (assigns to all an identity's SAP user accounts, in the same SAP system and for which SAP profile inheritance is authorized) |
- |
|
SAP roles |
Possible (assigns to all an identity's SAP user accounts, in the same SAP system and for which SAP role inheritance is authorized) |
- |
|
SAP parameters |
Possible (assigns to all an identity's SAP user accounts in the same SAP system) |
- |
|
Structural profiles |
Possible (assigns to all an identity's SAP user accounts, in the same SAP system and for which structural profile inheritance is authorized) |
- |
|
BI analysis authorizations |
Possible (assigns to all an identity's BI user accounts, in the same system and for which group inheritance is authorized) |
- |
|
Azure Active Directory groups |
Possible (assigns to all an identity's Azure Active Directory user accounts for which Azure Active Directory group inheritance is authorized) |
- |
|
Azure Active Directory administrator roles |
Possible (assigns to all an identity's Azure Active Directory user accounts for which Azure Active Directory administrator role inheritance is authorized) |
- |
|
Azure Active Directory subscriptions |
Possible (assigns to all an identity's Azure Active Directory user accounts for which Azure Active Directory subscription inheritance is authorized) |
- |
|
Disabled Azure Active Directory service plans |
Possible (assigns to all an identity's Azure Active Directory user accounts for which disabled Azure Active Directory service plans inheritance is authorized) |
- |
|
Cloud groups |
Possible (assigns to all an identity's user accounts for which cloud group inheritance is authorized) |
- |
|
Cloud system entitlements |
Possible (assigns to all an identity's user accounts for which cloud system entitlement inheritance is authorized) |
- |
|
Unix groups |
Possible (assigns to all an identity's Unix user accounts for which Unix group inheritance is authorized) |
- |
|
E-Business Suite permissions |
Possible (assigns to all an identity's E-Business Suite user accounts, in the same E-Business Suite system and for which E-Business Suite group inheritance is authorized) |
- |
|
PAM user groups |
Possible (assigns to all an identity's PAM user accounts for which PAM group inheritance is authorized) |
- |
|
Google Workspace products and SKUs |
Possible (assigns to all an identity's Google Workspace user accounts, in the same customer and for which Google Workspace products and SKU inheritance is authorized) |
- |
|
Google Workspace groups |
Possible (assigns to all an identity's Google Workspace user accounts, in the same customer and for which Google Workspace group inheritance is authorized) |
- |
|
SharePoint Online groups |
Possible (assigns to all an identity's SharePoint Online user accounts for which SharePoint Online group inheritance is authorized) |
- |
|
SharePoint Online roles |
Possible (assigns to all an identity's SharePoint Online user accounts for which SharePoint Online role inheritance is authorized) |
- |
|
Office 365 groups |
Possible (assigns to all an identity's Azure Active Directory user accounts for which Office 365 group inheritance is authorized) |
- |
|
Exchange Online mail-enabled distribution groups |
Possible (assigns to all an identity's Exchange Online mailboxes, Exchange Online mail users and Exchange Online mail contacts for which Exchange Online mail-enabled distribution group inheritance is authorized) |
- |
|
OneLogin roles |
Possible (assigns to all an identity's OneLogin user accounts for which OneLogin role inheritance is authorized) |
|
|
System roles |
Possible |
Possible |
|
Subscribable reports |
Possible |
- |
|
Software |
Possible |
Possible |
Related topics