One Identity Manager Data Governance Edition Deployment Guide
The One Identity Manager Data Governance Edition Deployment Guide contains the information required to install and configure One Identity Manager Data Governance Edition and deploy the Data Governance Edition components, including the Data Governance server, Resource Activity database and Data Governance agents. It also explains how to configure the Data Governance Edition components, including adding managed domains and working with managed hosts. It provides deployment requirements and step-by-step instructions to help you set up and configure Data Governance Edition functionality.
This guide is for network administrators, consultants, analysts, and IT professionals responsible for deploying, configuring and maintaining Data Governance Edition in their organization.
This section contains the following information to introduce you to Data Governance Edition and the deployment process:
Related Topics
Deployment requirements
Install One Identity Manager Data Governance Edition
Deploy Data Governance Edition components
Post installation configuration
Authentication using service accounts and managed domains
Working with managed hosts and agents
Upgrade Data Governance Edition
Remove Data Governance Edition
Troubleshooting
NetApp managed host deployment
EMC managed host deployment
SharePoint Farm managed host deployment
Data Governance Edition overview
Control over your organization’s data is vital to eliminating issues such as security breaches, loss of sensitive information, or non-compliance with external and internal guidelines. Data Governance Edition provides a systematic approach to managing data access, preserving data integrity, and providing content owners with the tools and workflows to manage their own data resources, removing reliance on IT administrators.
Ultimately, you need a process in place that allows you to:
- Ensure that your business runs efficiently with access to correct information on demand.
- Understand the access levels, patterns, and usage to build and maintain a governance strategy.
- Comply with organizational security and compliance policies.
- Bring accountability to contain damage.
- Review the usage patterns of sensitive information.
- Identify and assign business owners.
- Enable attestations from business owners to the validity of the data and its use.
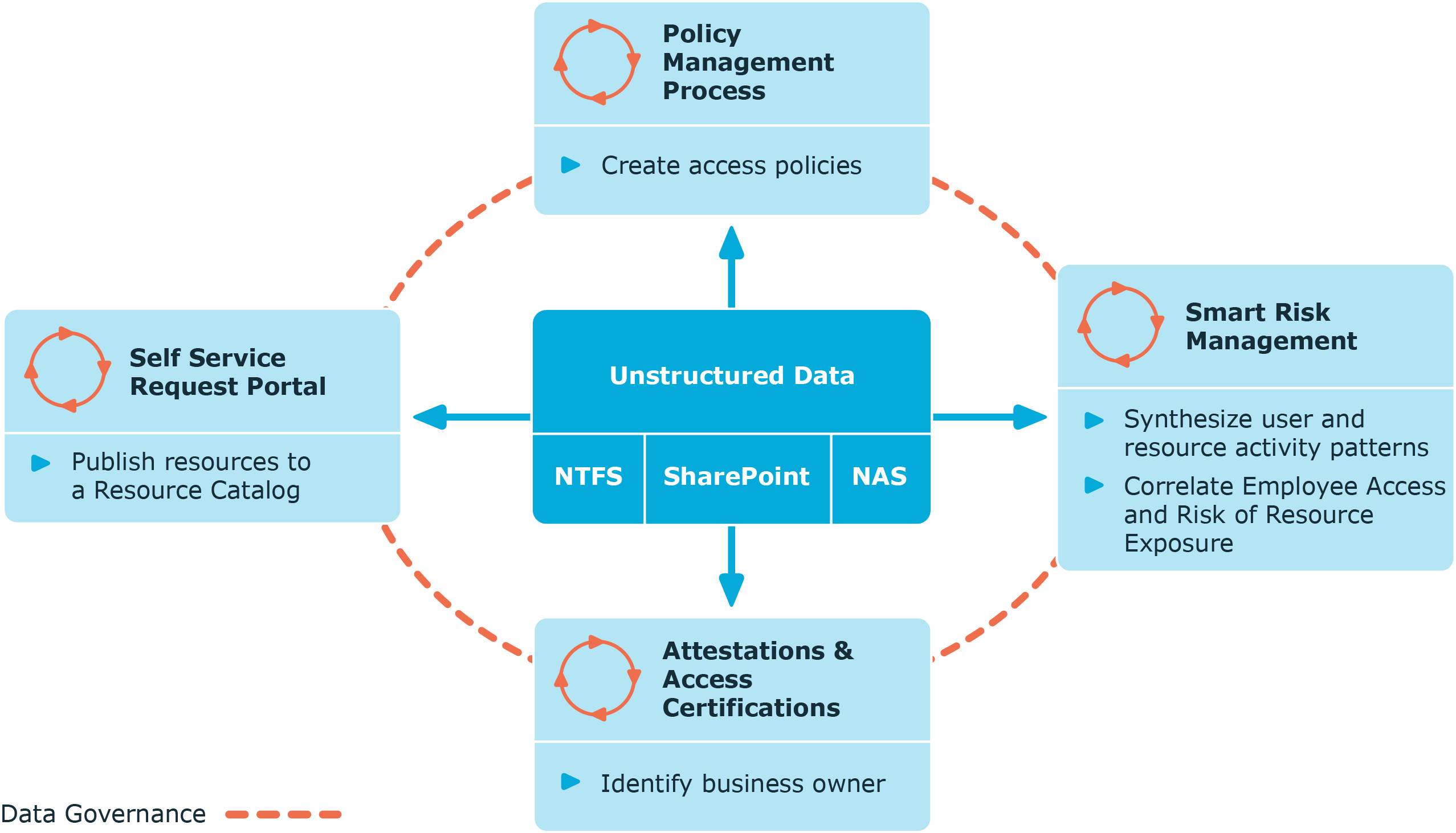
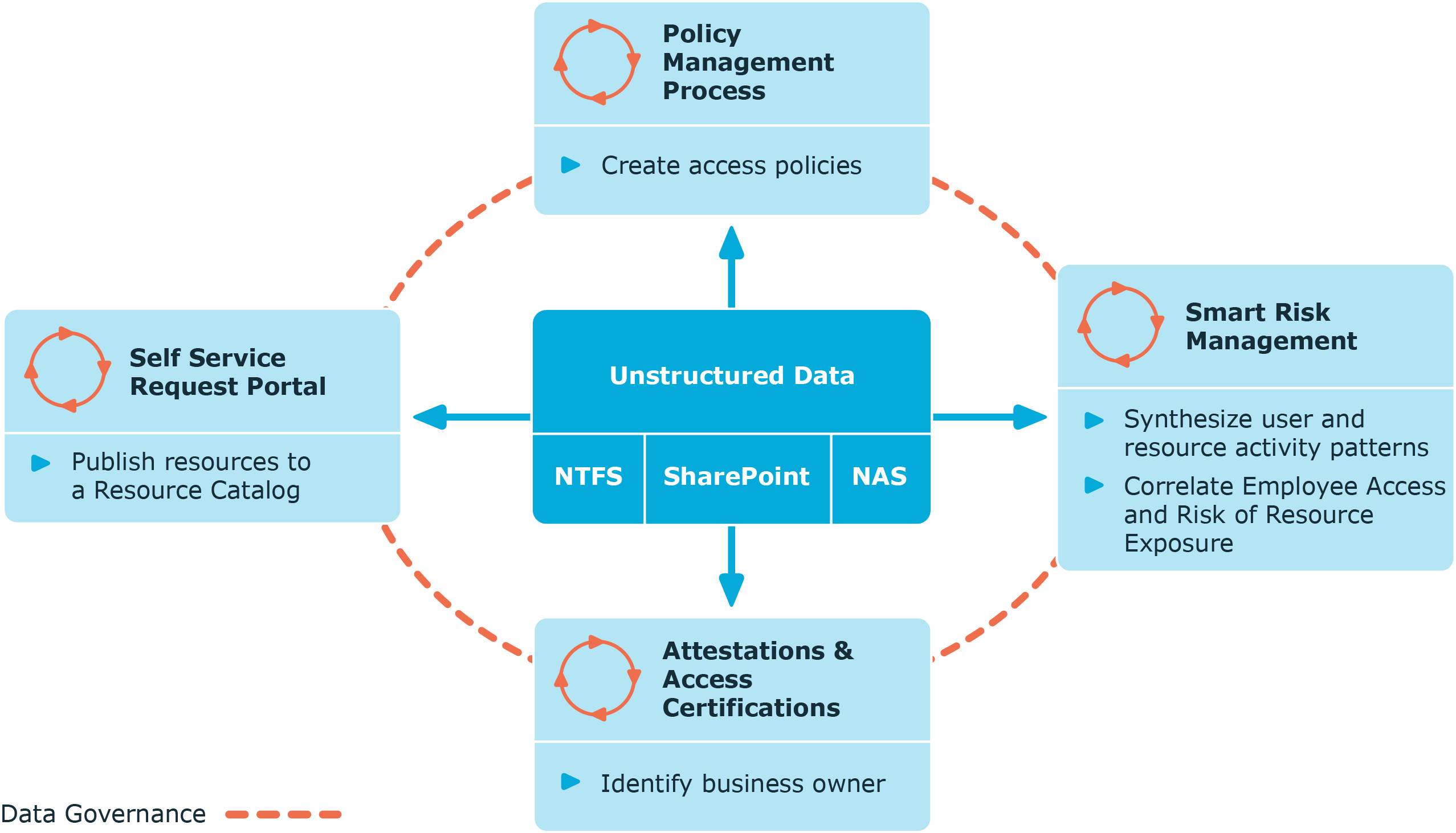
The governance of unstructured data is accomplished through workflows that cross both the Manager and the web portal. The following diagram identifies the key processes in securing and controlling access to your organization’s data.
Figure 1: Data Governance Edition key processes
Architecture
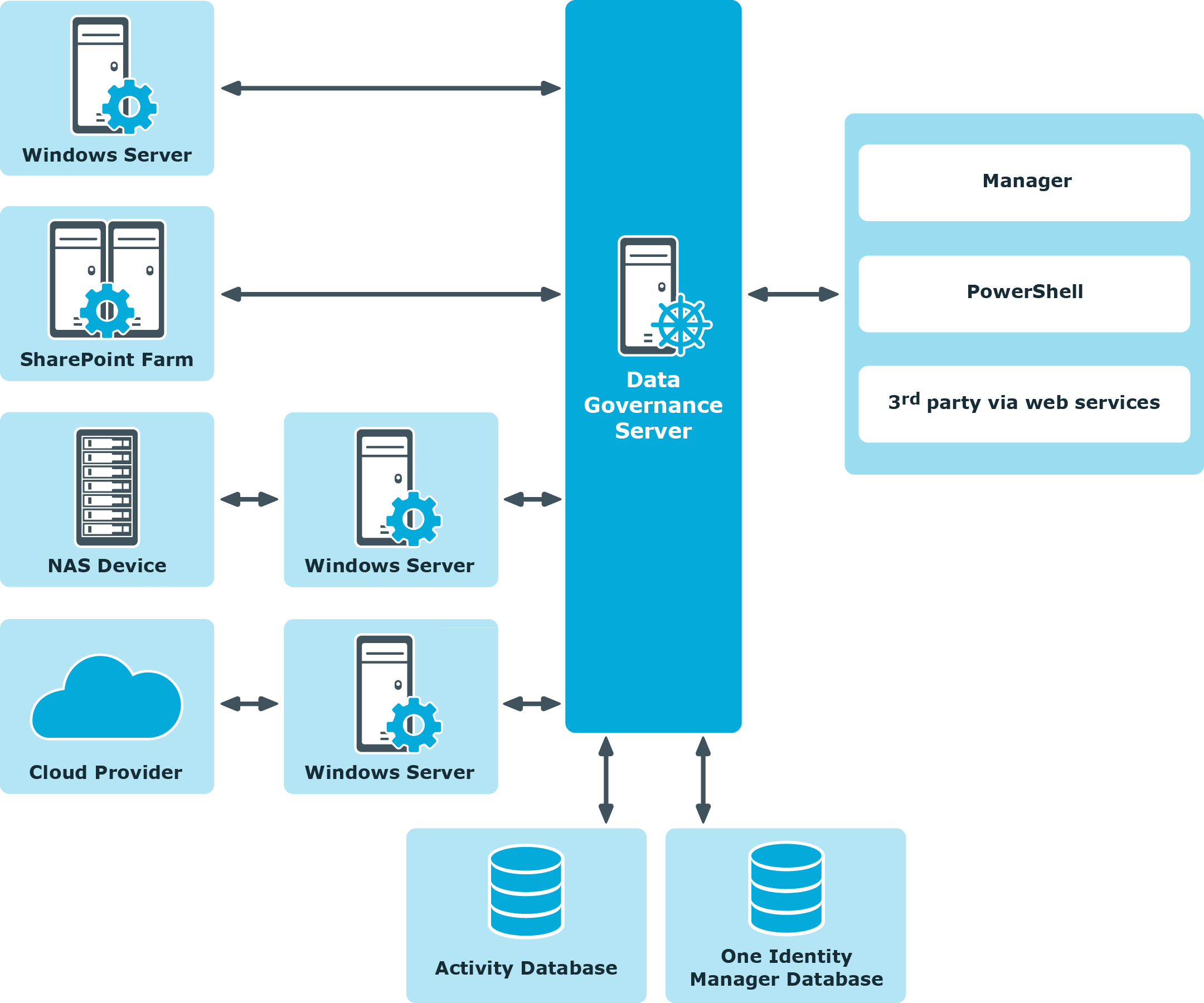
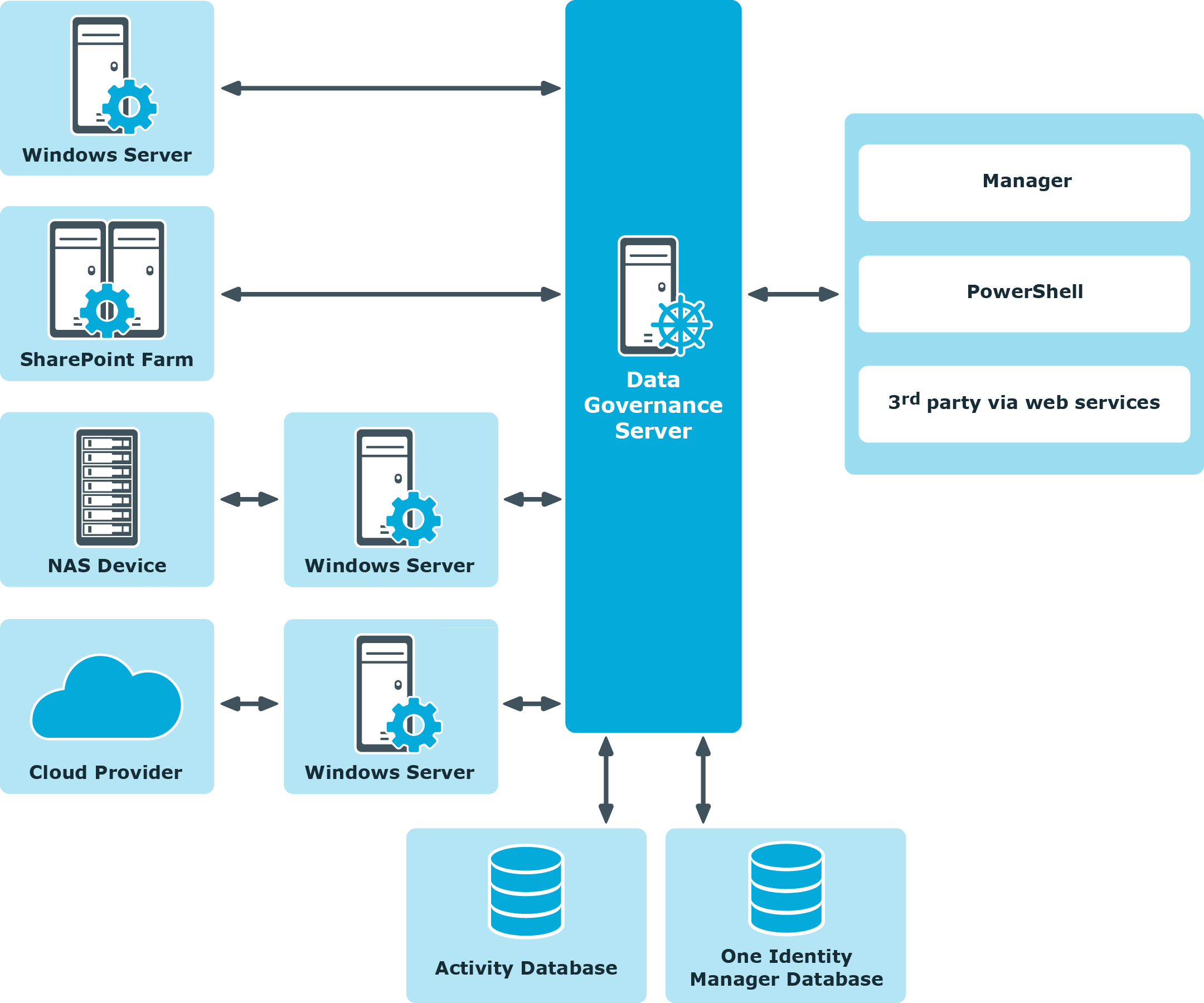
Data Governance Edition consists of the following components:
-
Data Governance server: The server acts as an intermediary between the agents and the databases where information is stored. It coordinates all agent deployments and communication, and manages the security index for each managed host.
The server is the central authority that receives and indexes information from agents deployed on target computers. It only maintains a subset of information for the computers that are being indexed (essentially access to specific resource types on managed computers). When you request detailed access information, the server attempts to contact the local agent and provide information stored in the local agent index.
- Data Governance agents: Agents collect security data from your managed hosts, and if configured, can also collect resource activity data. The agent cache stores all the detailed indexed information.
- Databases: The One Identity Manager database stores configuration and security information. The Data Governance Resource Activity database stores resource activity information.
- Managed hosts: A managed host is any network object that can host resources and can be assigned an agent to monitor security and resource activity. Managed hosts store the data on which users perform actions. Currently supported managed hosts include Windows computers, Windows clusters, certain network attached storage (NAS) devices, SharePoint farms and certain cloud providers, including SharePoint Online and OneDrive for Business.
For more information about component communications and how communication is encrypted, see the One Identity Manager Data Governance Edition Technical Insight Guide.
Figure 2: Data Governance Edition architecture
Data Governance Edition Services
Data Governance Edition is comprised of the following services: