The time policy determines the timeframe when the users are permitted to access a particular channel. By default, there is no time-based restriction, all channels are available 7x24.
Figure 175: Policies > Time Policies — Configuring time policies

To create a time policy or edit an existing one
-
Navigate to the Time Policies tab of the Policies menu item and click
to create a new time policy. Enter a name for the policy (for example workhoursonly).
-
Click
to display the days of the week and the allowed intervals.
-
Enter the intervals for each day when the users are allowed to access the connection. Use the hh:mm format (for example from 08:00 to 16:00).
-
To add multiple intervals for a day, click
.
-
Click
.
-
To actually restrict access to a connection or a channel based on the policy created in the previous steps:
-
Select this policy in the Time Policy field of the channel policy.
-
Click
.
-



 and enter a username into the displayed field. Repeat this step until all required usernames are listed.
and enter a username into the displayed field. Repeat this step until all required usernames are listed.
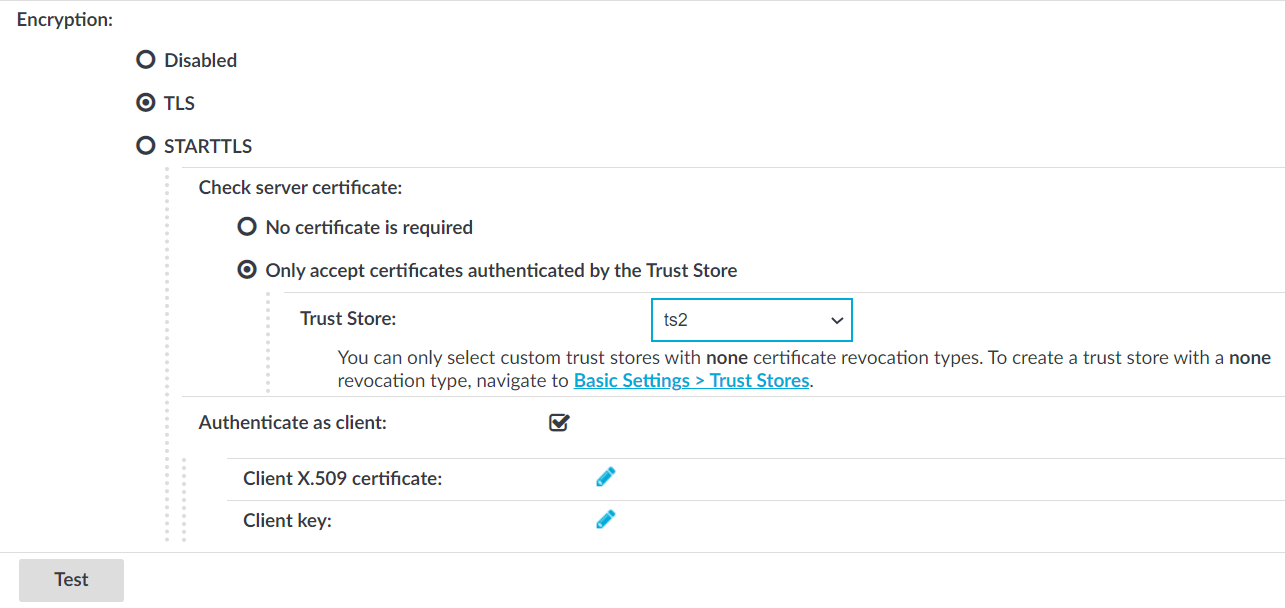
 in the Client X.509 certificate field to upload the certificate. After that, click
in the Client X.509 certificate field to upload the certificate. After that, click