If a hardware failure occurs, Azure moves the Virtual Machine to another location and restarts it in 5-15 minutes. In case you require higher SLA, you are recommended to deploy two standalone SPS nodes into an availability set. Note that to deploy two active SPS nodes as an availability set, you must purchase two standalone SPS licenses.
For more information, see Locally redundant storage in the Azure Storage replication document and Service Healing - Auto-recovery of Virtual Machines.
The Welcome Wizard and the first login
This section describes the initial steps of configuring One Identity Safeguard for Privileged Sessions (SPS). Before completing the steps in The initial connection to One Identity Safeguard for Privileged Sessions (SPS), unpack, assemble, and power on the hardware. Connect interface 1 (labelled 1 or EXT) to the local network, or directly to the computer from which SPS will be configured.
NOTE: For details on unpacking and assembling the hardware, see Hardware Installation Guide in the Installation Guide. For details on how to create a High Availability SPS cluster, see Installing two SPS units in HA mode in the Installation Guide. For more information about the supported browsers, see Supported web browsers.
One Identity Safeguard for Privileged Sessions (SPS) can be connected from a client machine using web browsers and accessed from the local network.
Starting with version 3.1, SPS attempts to receive an IP address automatically via DHCP. If it fails to obtain an automatic IP address, it starts listening for HTTPS connections on the 192.168.1.1 IP address. Note that certain switch configurations and security settings can interfere with SPS receiving an IP address via DHCP. SPS accepts connections via its interface 1 (labelled 1 or EXT). For details on the network interfaces, see Network interfaces).
TIP: The SPS console displays the IP address on which interface 1 is listening.
If SPS is listening on the 192.168.1.1 address, note that the 192.168.1.0/24 subnet must be accessible from the client. If the client machine is in a different subnet (for example, its IP address is 192.168.10.X), but in the same network segment, the easiest way is to assign an alias IP address to the client machine. Creating an alias IP on the client machine virtually puts both the client and SPS into the same subnet, so that they can communicate. To create an alias IP complete the following steps.
|

|
Caution:
The Welcome Wizard can be accessed only using interface 1, as the other network interfaces are not configured yet. |
This procedure describes how to assign an alias IP address to a network interface on Microsoft Windows platforms.
To assign an alias IP address to a network interface on Microsoft Windows platforms
-
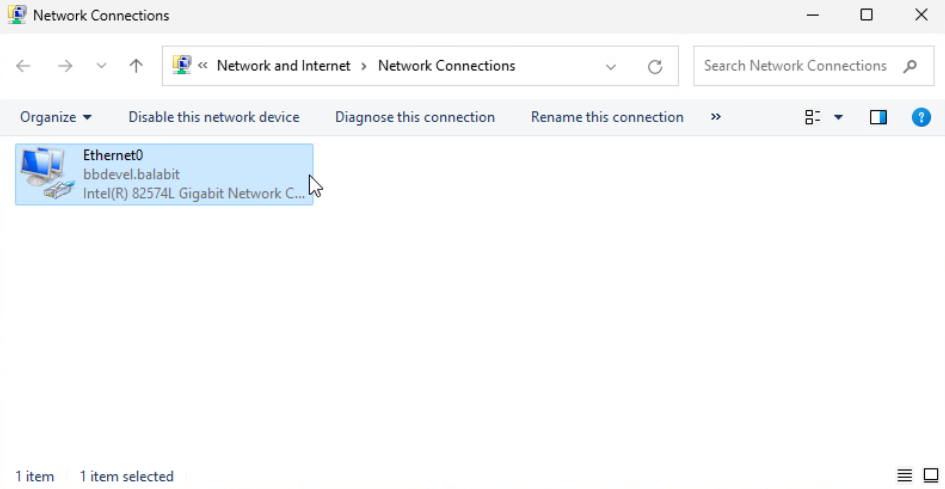
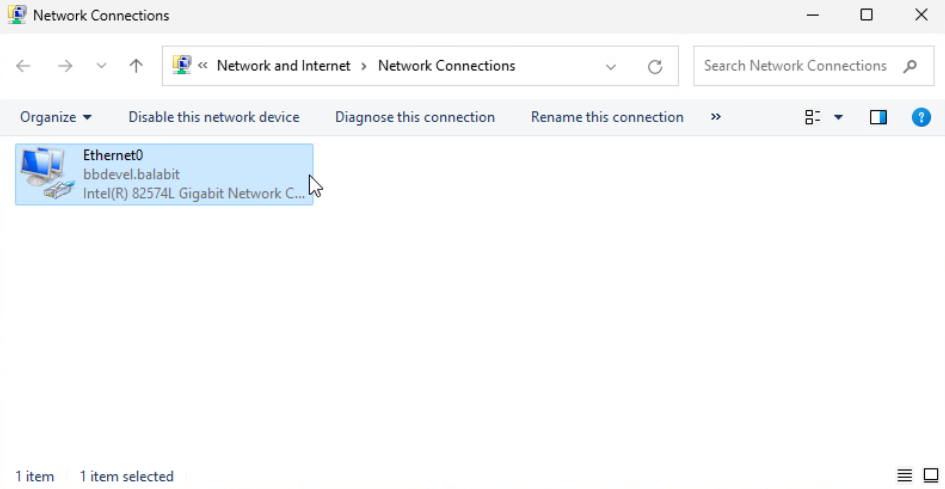
Open Network Connections via the Run dialog box (that is, press the Windows key + R, type ncpa.cpl, then press Enter.
-
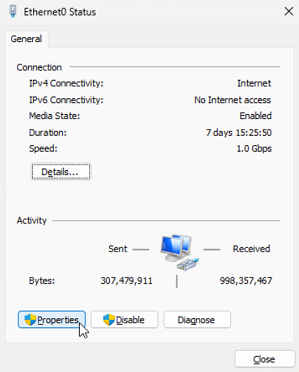
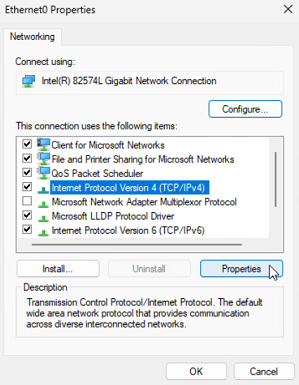
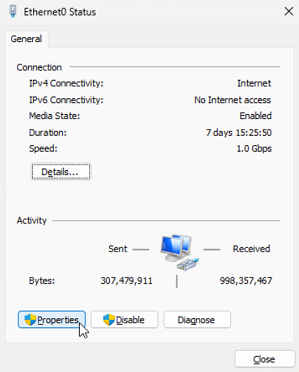
Double click the Ethernet0 network interface, then click Properties.
-
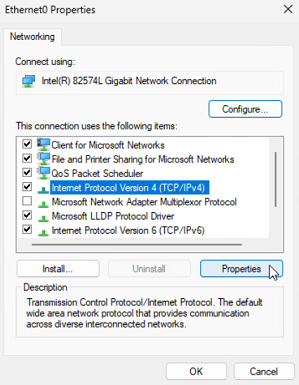
Under the Networking tab, select Internet Protocol Version 4 (TCP/IPv4).
-
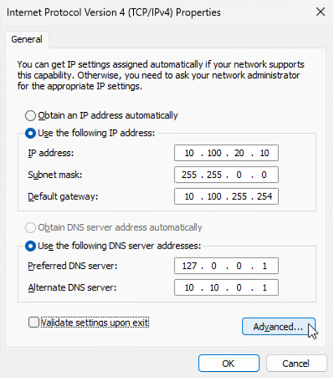
If the IP address is not configured automatically, under the General tab, select Advanced.
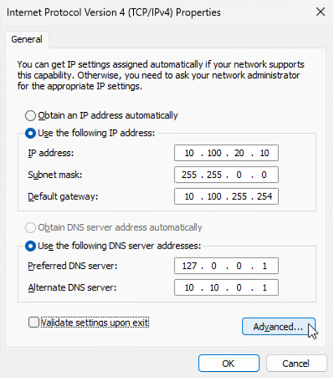
NOTE: You can only add a custom secondary IP address via manual configuration. If the IP address configuration is automatic, the Advanced button is inactive.
-
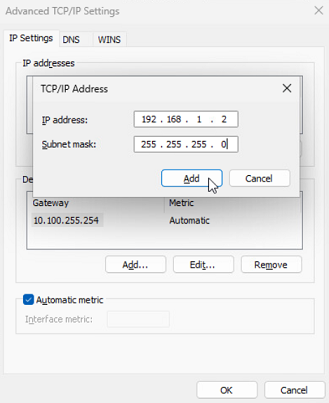
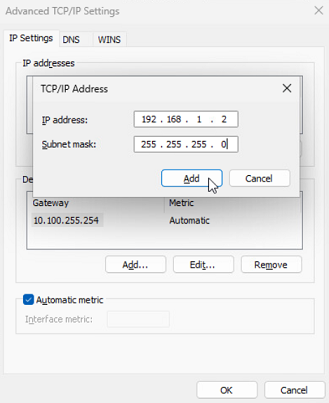
Under the IP Settings tab, select Add next to the IP addresses box.

-
Configure the IP address and Subnet mask fields.
-
Enter 192.168.1.2 into the IP address field, and 255.255.255.0 into the Subnet mask field.
|

|
Caution:
If your internal network uses the 192.168.1.0/24 IP range, it is possible that the 192.168.1.1 and 192.168.1.2 addresses are already in use. In this case, disconnect One Identity Safeguard for Privileged Sessions (SPS) from the network, and connect a computer directly to interface 1 (labelled 1 or EXT) using a standard cross-link cable. |
-
To activate your settings, click OK.