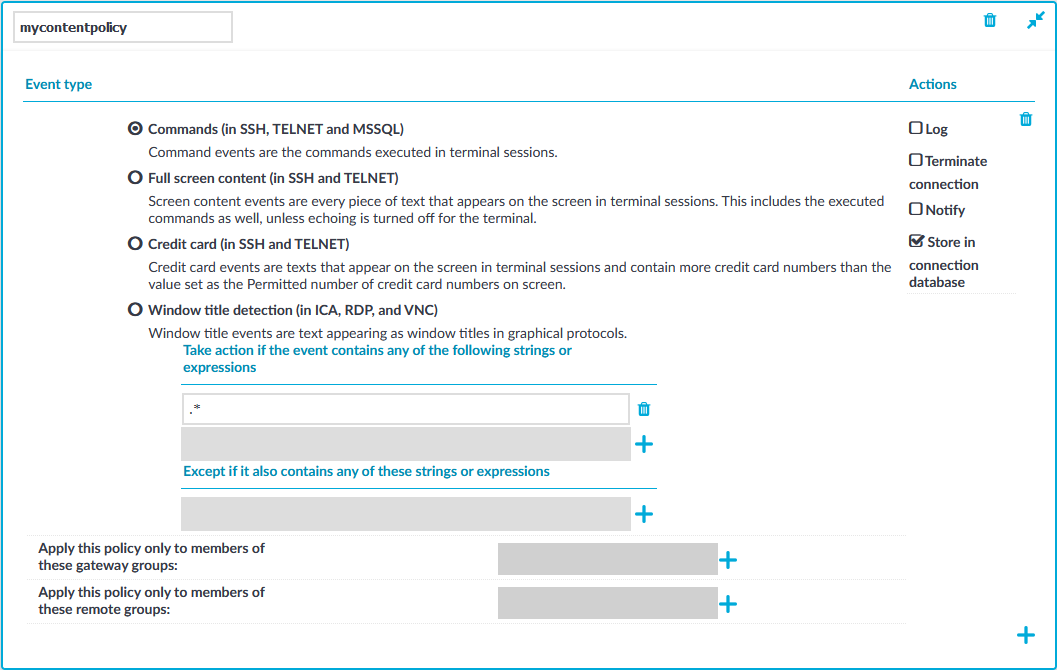
Creating a new content policy
The following describes how to create a new content policy that performs an action if a predefined content appears in a connection.
NOTE: Using content policies significantly slows down connections (approximately 5 times slower), and can also cause performance problems when using the indexer service.
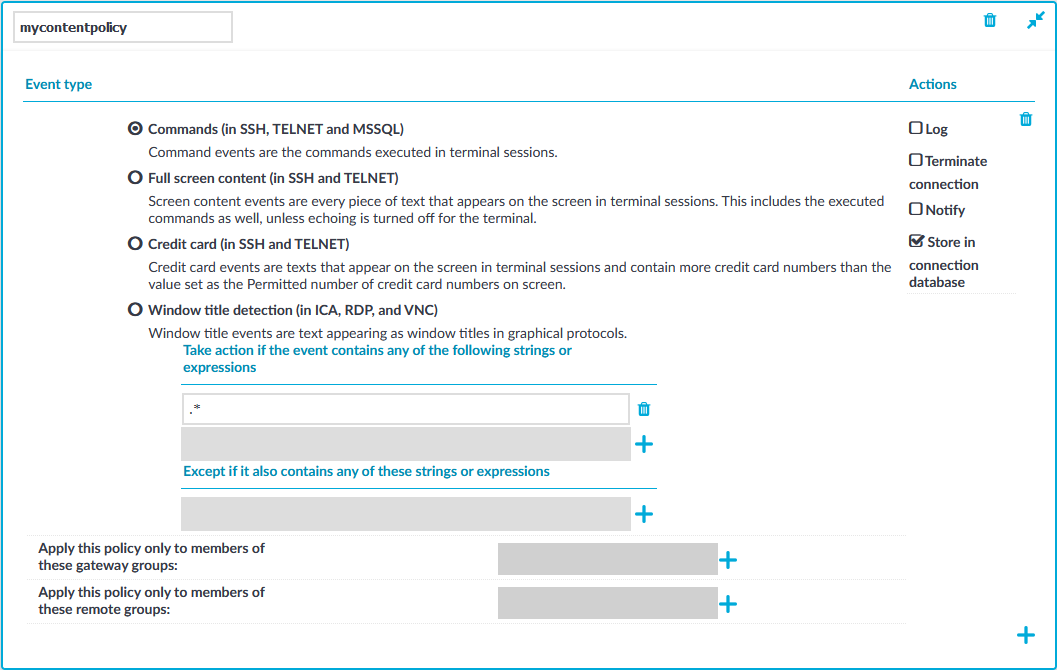
Figure 173: Policies > Content Policies — Content policies
To create a new content policy that performs an action if a predefined content appears in a connection
-
Navigate to Policies > Content Policies, click  and enter a name for the policy.
and enter a name for the policy.
-
Select the type of event that you want to monitor:
-
Commands: The commands executed in the session-shell channel of SSH connections, or in Telnet connections.
|

|
Caution:
During indexing, if a separate certificate is used to encrypt the upstream traffic, command detection works only if the upstream key is accessible on the machine running the indexer. |
NOTE: Command detection is case-insensitive.
-
Screen content: Every text that appears on the screen. For example, every text that is displayed in the terminal of SSH or Telnet connections. This includes the executed commands as well, unless echoing is turned off for the terminal.
-
Credit card: Process every text that appears on the screen and attempt to detect credit card numbers in SSH or Telnet connections. One Identity Safeguard for Privileged Sessions (SPS) performs an action if the number of detected credit card numbers exceeds the value set as Permitted number of credit card numbers.
Credit card number detection is based on the Luhn algorithm and lists of known credit card number prefixes.
-
Window title detection: Text appearing as window titles that can be detected on the screen in RDP, Citrix ICA, and VNC connections. Window title detection involves Optical Character Recognition (OCR) on parts of the screen, and can be slightly resource-intensive. SPS versions up till 6.2 only detected only the active window in the screen. From SPS version 6.3, multiple windows can be detected.
Limitations
-
Default Windows themes are supported.
-
Windows that do not have an X (close window) button in the top-right corner (or it is not visible) are not detected.
-
Use window title detection for sessions that use a single monitor. The feature works in multi-monitor environments as well, but becomes very slow, therefore it is not recommended.
-
Window title detection is case-insensitive.
-
Select Take action if the event contains any of the following strings or expressions, click  and enter a string or regular expression. SPS will perform an action if this expression is found in the connection, unless it is listed in the Except if it also contains any of these strings or expressions list. For example, SPS can terminate the connection if the user issues the rm -rf * in an SSH connection. Repeat this step to add further expressions if needed.
and enter a string or regular expression. SPS will perform an action if this expression is found in the connection, unless it is listed in the Except if it also contains any of these strings or expressions list. For example, SPS can terminate the connection if the user issues the rm -rf * in an SSH connection. Repeat this step to add further expressions if needed.
-
Use Perl Compatible Regular Expressions (PCRE).
-
The following characters must be escaped using a backslash character: '(single-quote). For example, instead of .*' use .*\'
-
SPS uses substring search to find the expression in the content. That is, SPS finds the expression even if there is more content before or after the matching part. For example, the conf pattern will match the following texts: conf, configure, reconfigure, arcconf, and so on.
-
Using complicated regular expressions or using many regular expressions will affect the performance of SPS.
-
If the multiple expressions are set, SPS processes them one after the other, and stops processing the content if the first match is found, even if other expressions would also match the content. Therefore, when using multiple expressions, start with the most specific one, and add general expressions afterward.
Example: Sample regular expressions for content policies
The following simple regular expressions are samples to demonstrate what kinds of events that can be detected using content policies.
-
The enable command on Cisco devices: the user enters privileges mode.
-
The conf term command on Cisco devices: the user configures the networking parameters of the device.
-
The sudo and su - commands: the user enters privileged mode Linux and other UNIX platforms.
-
To add an exception to the Take action if the event contains any of the following strings or expressions rule, select Except if it also contains any of these strings or expressions, click  and enter a string or regular expression. SPS will not perform any action if this expression is found in the connection. For example, to permit the users to delete only the /tmp directory in an SSH connection, enter rm -rf /tmp. Repeat this step to add further expressions if needed.
and enter a string or regular expression. SPS will not perform any action if this expression is found in the connection. For example, to permit the users to delete only the /tmp directory in an SSH connection, enter rm -rf /tmp. Repeat this step to add further expressions if needed.
Example: Sample content policies using Ignore rules
The following expressions can be used to perform an action if any SQL command is used in MySQL, except for the select and help commands:
-
Into the Take action if the event contains any of the following strings or expressions expression, enter mysql>.*
-
Add two Except if it also contains any of these strings or Except if it also contains any of these strings or Except if it also contains any of these strings or expressions expressions: mysql> select.* and mysql> help.*
-
Select the action to perform.
-
Log: Send a log message into the system logs. The log message includes the expression that matched the content. On log level 6, the message includes the matching content as well.
-
Terminate connection: Immediately terminate the connection. When using the Terminate connection action for the Command event type, and a command matches an expression, the connection is terminated before the command is executed. When using the Terminate connection action, note the following points.
-
Select the Log or Notify action as well so that it is easy to find out why a connection was terminated.
-
If the connection is terminated by a content policy, the Verdict of the connection becomes ACCEPT-TERMINATED.
-
Notify: Send an e-mail or SNMP alert about the event. To configure the alerts, navigate to Basic Settings > Alerting & Monitoring and set the required alerts for the Real time audit event detected (scbAuditRealTime) event.
-
Store in connection database: Add the event to the SPS connection database. These events are displayed in the Alerts column of the Search page. If the column is not visible, click Customize columns....
-
To apply the content policy only for users belonging to specific groups, select Apply this policy only to members of these gateway groups or Apply this policy only to members of these remote groups,  and specify the usergroups as needed. If Apply this policy only to members of these gateway groups or Apply this policy only to members of these remote groups is set, the content policy is applied only to connections of these usergroups.
and specify the usergroups as needed. If Apply this policy only to members of these gateway groups or Apply this policy only to members of these remote groups is set, the content policy is applied only to connections of these usergroups.
-
To add a new rule to the policy, click  and repeat Steps 2-6.
and repeat Steps 2-6.
Note that if you have more than one rules in a policy, SPS evaluates them as follows.
-
SPS evaluates the first (top) rule.
-
If the rule contains Apply this policy only to members of these gateway groups or Apply this policy only to members of these remote groups restrictions, SPS checks if the current user belongs to any of the specified groups. If the groups do not match, SPS skips the rule.
-
If the content matches any entry of the Except if it also contains any of these strings or expressions list, SPS skips the rule.
-
If the content matches any entry of the Take action if the event contains any of the following strings or expressions list, SPS performs the action configured for the rule. Otherwise, SPS skips the rule.
-
If the current rule did not match the content, SPS evaluates the next rule of the policy (if any).
-
Click  . A new content policy is created.
. A new content policy is created.
-
To use the content policy created in the previous steps, select the policy in the channel policy that is used to control the connections.
NOTE: It is not required to enable auditing to use content policies.
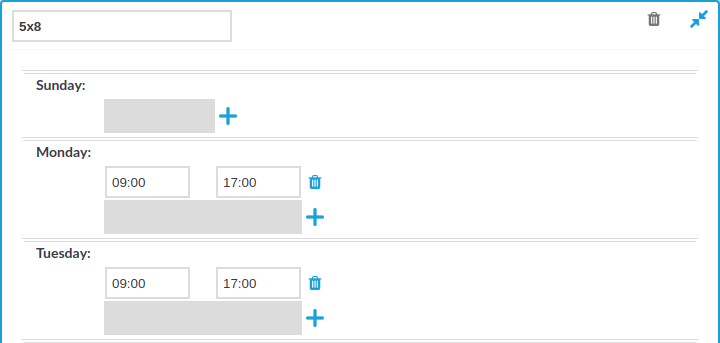
Configuring time policies
The time policy determines the timeframe when the users are permitted to access a particular channel. By default, there is no time-based restriction, all channels are available 7x24.
Figure 174: Policies > Time Policies — Configuring time policies
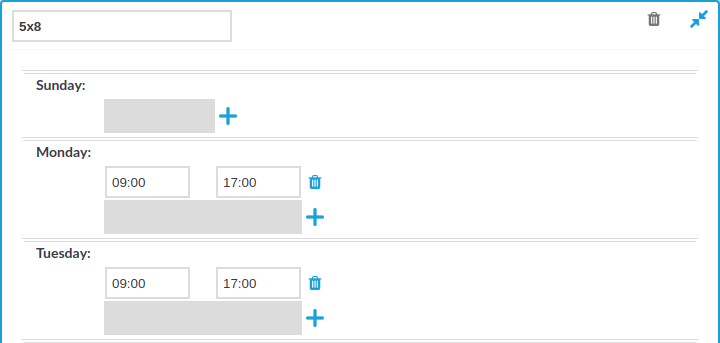
To create a time policy or edit an existing one
-
Navigate to the Time Policies tab of the Policies menu item and click  to create a new time policy. Enter a name for the policy (for example workhoursonly).
to create a new time policy. Enter a name for the policy (for example workhoursonly).
-
Click  to display the days of the week and the allowed intervals.
to display the days of the week and the allowed intervals.
-
Enter the intervals for each day when the users are allowed to access the connection. Use the hh:mm format (for example from 08:00 to 16:00).
-
To add multiple intervals for a day, click  .
.
-
Click  .
.
-
To actually restrict access to a connection or a channel based on the policy created in the previous steps:
Creating and editing user lists
User lists are white- or blacklists of usernames that allow fine-control over who can access a connection or a channel.
|

|
Caution:
User Lists are white- or blacklists of usernames that determine who can access the server remotely. However, this cannot prevent a user from accessing the server from a local terminal. |
Figure 175: Policies > User Lists — Configuring user lists
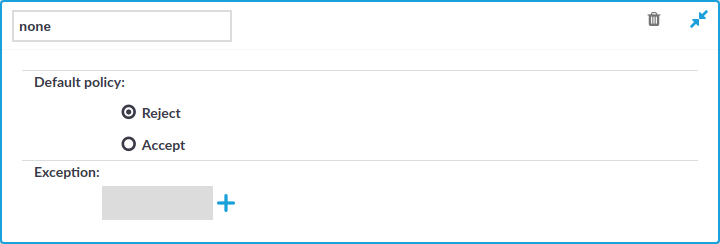
To create a new user list or edit an existing one
-
Navigate to the User Lists tab of the Policies menu and click  to create a new user list. Enter a name for the list User List field (for example serveradmins).
to create a new user list. Enter a name for the list User List field (for example serveradmins).
|

|
Caution:
Usernames, the names of user lists, and the names of usergroups are case sensitive. |
-
Click  to display the list of users.
to display the list of users.
-
Select the default policy of the user list. Select Reject for a whitelist, that is, to allow access only to the members of the list. Select Accept for a blacklist, that is, to allow access to everyone except the members of the list.
-
Click  and enter a username into the displayed field. Repeat this step until all required usernames are listed.
and enter a username into the displayed field. Repeat this step until all required usernames are listed.
|

|
Caution:
Usernames, the names of user lists, and the names of usergroups are case sensitive. |
-
Click  to save the list.
to save the list.
-
To actually restrict access to a channel based on the user list created in the previous steps:
-
Navigate to the Channel Policies tab of the type of connection you want to control and click  to display the details of the policy.
to display the details of the policy.
-
Click  in the Group section to add a new group to the policy and enter the name of the group. Repeat this step to add other groups.
in the Group section to add a new group to the policy and enter the name of the group. Repeat this step to add other groups.
|

|
Caution:
Usernames, the names of user lists, and the names of usergroups are case sensitive. |
NOTE: When listing more groups, users of any of the listed groups can access the channel. For details, see Creating and editing channel policies.
When listing both a whitelist and blacklist in the Group section and a username appears on both lists, the user will be able to access the channel.
-
Click  .
.
Authenticating users to an LDAP server
You can use the LDAP policy to set the details of the LDAP server you wish to use to:
-
authenticate gateway users (available in SSH and Telnet as Authentication Policy)
-
query gateway groups (available for RDP, Telnet, SSH, and ICA)
-
query remote groups (available for RDP, Telnet, SSH, ICA, and HTTP)
NOTE: This feature is not available for Virtual Network Computing (VNC) connections.
Prerequisites
Make sure that the response timeout of the LDAP/Active Directory server is set to a minimum of 120 seconds.
NOTE: Consider the following:
-
In RDP (including RDG) connections, you can use the LDAP policy for group membership check only, you cannot use it as the authentication backend. However, you can use a trusted AD domain for authentication and LDAP for group membership check.
In this case, LDAP will only use the username without the domain name to verify the group membership.
- One Identity Safeguard for Privileged Sessions (SPS) treats user and group names in a case insensitive manner if the matching rule for the attribute in question is case insensitive in the LDAP database.
To configure an LDAP policy for a connection
-
Navigate to Policies > LDAP Servers and click  to create a new LDAP policy.
to create a new LDAP policy.
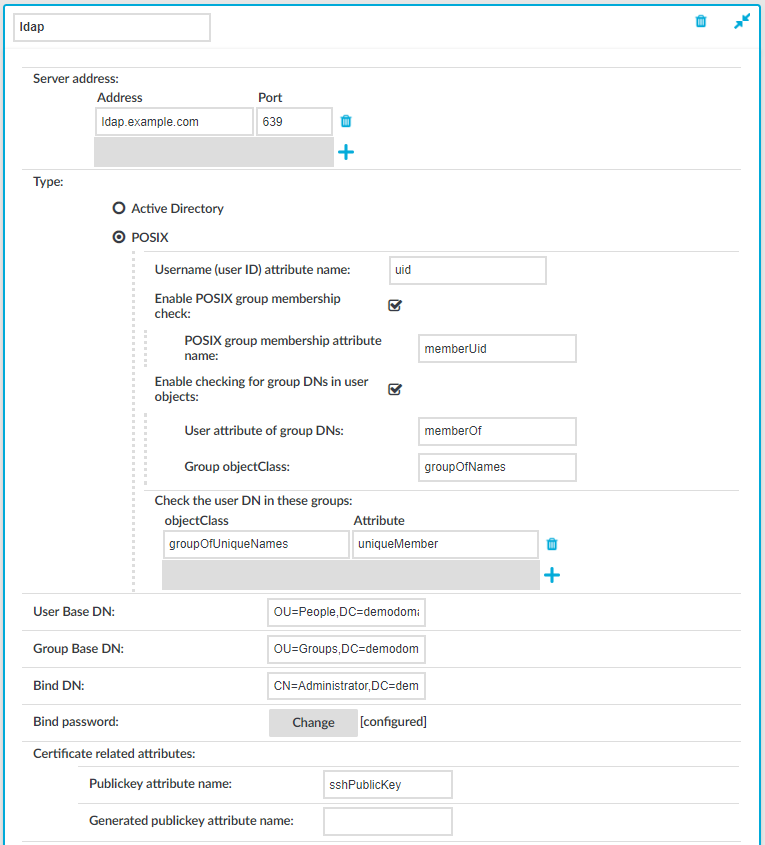
Figure 176: Policies > LDAP Servers — Configuring LDAP Server policies
-
Enter a name for the policy (for example ldapservers).
-
Select the type of your LDAP server in the Type field. Select:
-
Active Directory to connect to Microsoft Active Directory servers.
You can enable nested groups. Select Enable AD group membership check, then Enable nested groups.
|

|
Caution:
Nested groups can slow down the query and cause the connection to timeout if the LDAP tree is very large. In this case, disable the Enable nested groups option. |
To also check group membership based on group DNs in a user attribute, select Enable checking for group DNs in user objects and enter the name of the user attribute, for example, memberOf in the User attribute of group DNs field.
|

|
Caution:
If you have too many groups, using this option significantly slows down logging in to the SPS web interface.
Use this option only if you have an LDAP schema where the user groups can only be determined from a user attribute that contains the group DNs. |
To check for group membership based on user DNs in group attributes, use the Check the user DN in these groups options.
For more information, see Active Directory LDAP backend.
-
POSIX to connect to servers that use the POSIX LDAP scheme.
If your LDAP server uses a custom POSIX LDAP scheme, you might need to set which LDAP attributes store the username, or the attributes that set group memberships. For example, if your LDAP scheme does not use the uid attribute to store the usernames, set the Username (user ID) attribute name option.
In addition to the primary group membership checking, you can allow checking for supplementary group memberships by selecting Enable POSIX group membership check and specifying the POSIX group membership attribute name field.
To also check group membership based on group Distinguished Names (DNs) in a user attribute, select Enable checking for group DNs in user objects. Then, enter the name of the user attribute (for example, memberOf) in the User attribute of group DNs field, and objectClass (for example, groupOfNames) in the Group objectClass field.
|

|
Caution:
If you have too many groups, using this option significantly slows down logging in to the SPS web interface.
Use this option only if you have an LDAP schema where the user groups can only be determined from a user attribute that contains the group DNs. |
To check for group membership based on user DNs in group attributes, use the Check the user DN in these groups option.
For more information, see POSIX LDAP backend.
For an overview about LDAP user and group resolution in SPS, see Overview.
-
Enter the IP address/hostname and the port of the LDAP server in the respective text boxes.
Consider the following when specifying the address information:
-
If you want to encrypt the communication between SPS and the LDAP server, use the following port numbers:
-
For TLS, specify 636 as the port number.
-
For STARTTLS, specify 389 as the port number.
-
Use an IPv4 adress or a hostname.
-
To add multiple servers, click  and enter the address of the next server. If a server is unreachable, SPS will try to connect to the next server in the list in failover fashion.
and enter the address of the next server. If a server is unreachable, SPS will try to connect to the next server in the list in failover fashion.
-
When you configure the location of the LDAP server, that is, the IP address or hostname and the port number, you can use a Service record (SRV record), which is a type of information record in the DNS that maps the name of a service to the DNS name of the server. SRV records have the following format: _ldap._tcp.<SITE_NAME>._sites.dc._msdcs.<DOMAIN.NAME> in the Address field. SPS looks up of the SRV record during committing the configuration change.
For more information on SRV records, see the relevant Microsoft documentation.
-
|

|
Caution:
If you connect to the LDAP server over a TLS-encrypted connection with certificate verification, you must fill the Address field with a name or IP address, which must be present in the certificate. |
-
In the User Base DN field, enter the name of the DN to be used as the base of queries regarding users (for example: OU=People,DC=demodomain,DC=exampleinc).
NOTE: This field is mandatory. You can use the same value for the User Base DN and the Group Base DN settings.
To speed up LDAP operations, specify a sufficiently narrow base for the LDAP subtrees where users and groups are stored.
-
In the Group Base DN field, enter the name of the DN to be used as the base of queries regarding groups (for example: OU=Groups,DC=demodomain,DC=exampleinc).
NOTE: This field is mandatory. You can use the same value for the User Base DN and the Group Base DN settings.
To speed up LDAP operations, specify a sufficiently narrow base for the LDAP subtrees where users and groups are stored.
-
In the Bind DN field, enter the Distinguished Name that SPS must use to bind to the LDAP directory (for example: CN=Administrator,DC=demodomain,DC=exampleinc).
NOTE: SPS accepts both pre Windows 2000-style and Windows 2003-style account names, or User Principal Names (UPNs). For example, administrator@example.com is also accepted.
-
To configure or change the password to use when binding to the LDAP server, click Change and enter the password. Click Update. Click Commit.
NOTE: SPS accepts passwords that are not longer than 150 characters and supports the following characters:
-
Skip this step if you use passwords to authenticate the users.
-
If you use public-key authentication and receive the public key of the users from the LDAP database, enter the name of the LDAP attribute that stores the public keys of the users into the Publickey attribute name field. For details on using public-key authentication with the LDAP database, see Configuring public-key authentication on One Identity Safeguard for Privileged Sessions (SPS).
-
If you use X.509 certificate for authentication and receive the certificates of the users from the LDAP database, enter the name of the LDAP attribute that stores the certificates of the users into the Certificate attribute name field.
-
Skip this step if you use passwords to authenticate the users.
-
If you use public-key authentication and want SPS to generate server-side encryption keys on-the-fly and store them in a separate attribute on the LDAP server, enter the name of the attribute into the Generated publickey attribute name field.
-
If you use certificate authentication and want SPS to generate server-side certificates on-the-fly and store them in a separate attribute on the LDAP server, enter the name of the attribute into the Generated certificate attribute name field.
-
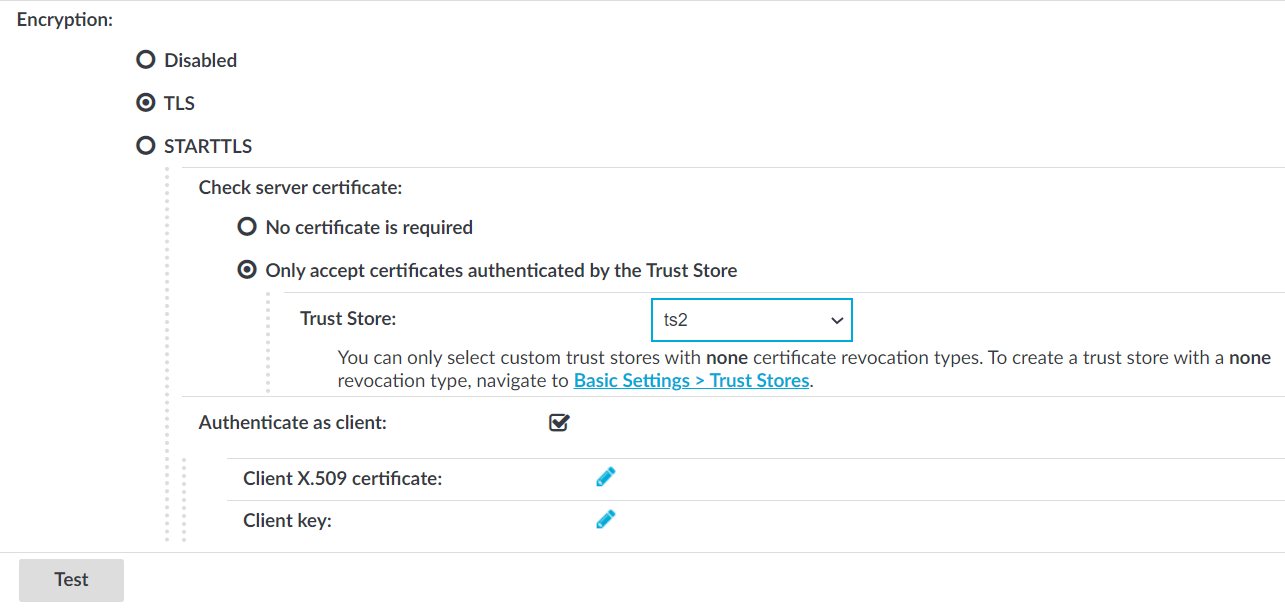
If you want to encrypt the communication between SPS and the LDAP server, in Encryption, select the TLS or the STARTTLS option and complete the following steps:
Figure 177: Policies > LDAP Servers — Configuring encryption
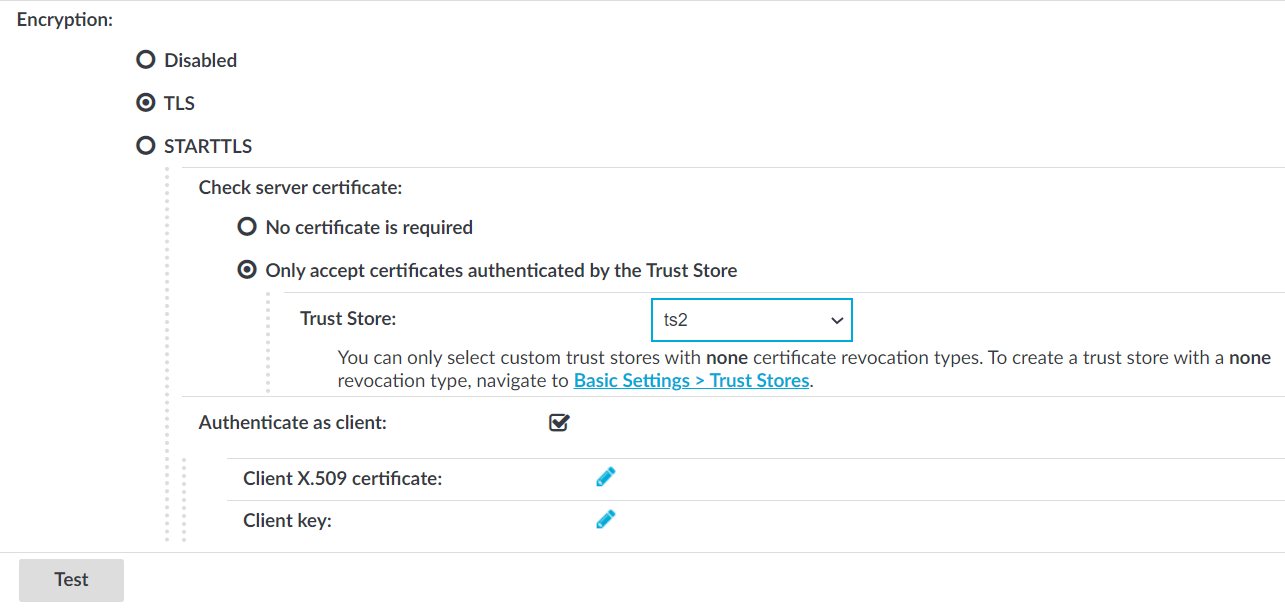
NOTE: TLS-encrypted connection to Microsoft Active Directory is supported only on Windows 2003 Server and newer platforms. Windows 2000 Server is not supported.
Verify the certificate of the server
-
If you want SPS to verify the certificate of the server, select Only accept certificates authenticated by the Trust Store and select a trust store in the Trust Store field.
SPS will use the selected trust store to verify the certificate of the server, and reject the connections if the verification fails.
|

|
Caution:
SPS checks if the certificate revocation list (CRL) has expired and that the CRL has been signed by the same certificate authority (CA). |
|

|
Caution:
If you connect to the LDAP server over a TLS-encrypted connection with certificate verification, you must fill the Address field with a name or IP address, which must be present in the certificate. |
Authenticate as client
-
If the LDAP server requires mutual authentication, that is, it expects a certificate from SPS, enable Authenticate as client. Generate and sign a certificate for SPS, then click  in the Client X.509 certificate field to upload the certificate. After that, click
in the Client X.509 certificate field to upload the certificate. After that, click  in the Client key field and upload the private key corresponding to the certificate.
in the Client key field and upload the private key corresponding to the certificate.
TIP: One Identity recommends using 2048-bit RSA keys (or stronger).
-
To commit the changes, click  .
.
-
Click Test to test the connection.
NOTE: Testing TLS and STARTTLS-encrypted connections is not supported.
and enter a name for the policy.
and enter a string or regular expression. SPS will perform an action if this expression is found in the connection, unless it is listed in the Except if it also contains any of these strings or expressions list. For example, SPS can terminate the connection if the user issues the rm -rf * in an SSH connection. Repeat this step to add further expressions if needed.
and enter a string or regular expression. SPS will not perform any action if this expression is found in the connection. For example, to permit the users to delete only the /tmp directory in an SSH connection, enter rm -rf /tmp. Repeat this step to add further expressions if needed.
and specify the usergroups as needed. If Apply this policy only to members of these gateway groups or Apply this policy only to members of these remote groups is set, the content policy is applied only to connections of these usergroups.
and repeat Steps 2-6.
. A new content policy is created.


 to display the days of the week and the allowed intervals.
to display the days of the week and the allowed intervals.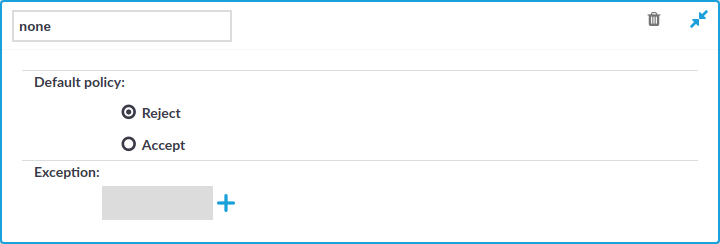
 and enter a username into the displayed field. Repeat this step until all required usernames are listed.
and enter a username into the displayed field. Repeat this step until all required usernames are listed.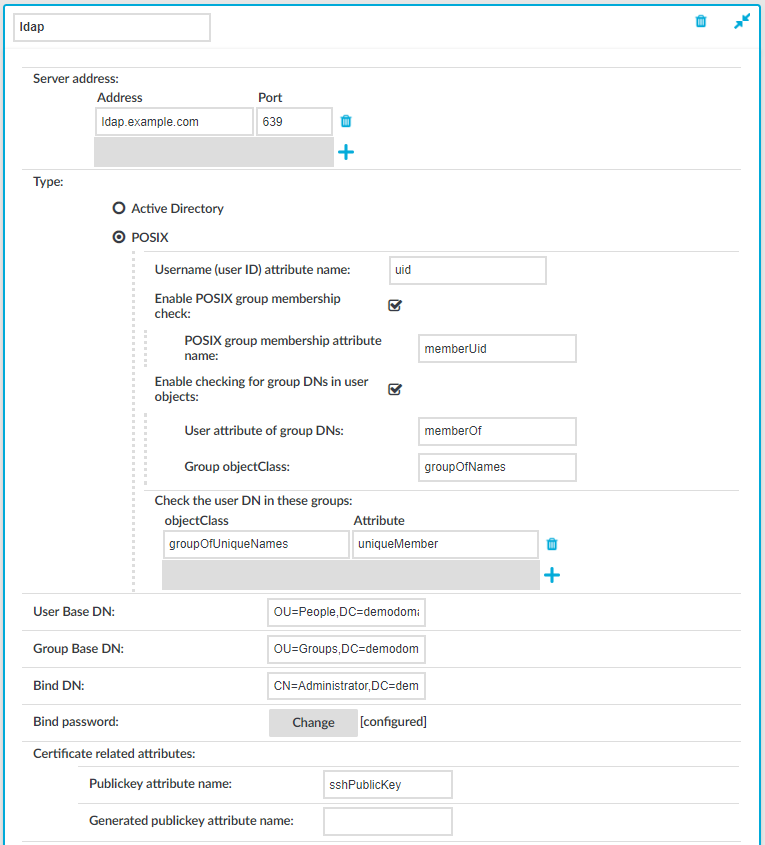
 in the Client X.509 certificate field to upload the certificate. After that, click
in the Client X.509 certificate field to upload the certificate. After that, click