By default, One Identity Safeguard for Privileged Sessions (SPS) users are managed locally on SPS. To add local users in SPS, complete all steps of the following procedure:
-
Create users.
For detailed instructions on how to create local users, see Creating local users in One Identity Safeguard for Privileged Sessions (SPS).
-
Assign users to groups.
For details about how to add a usergroup, see Managing local user groups.
-
Assign privileges to groups.
For information on how to control the privileges of usergroups, see Managing user rights and usergroups.
This section describes how to create local users.
NOTE: The admin user is available by default, and has all possible privileges. It is not possible to delete this user.
When using RADIUS authentication together with local users, the users are authenticated to the RADIUS server, only their group memberships must be managed locally on One Identity Safeguard for Privileged Sessions (SPS). For details, see Authenticating users to a RADIUS server.
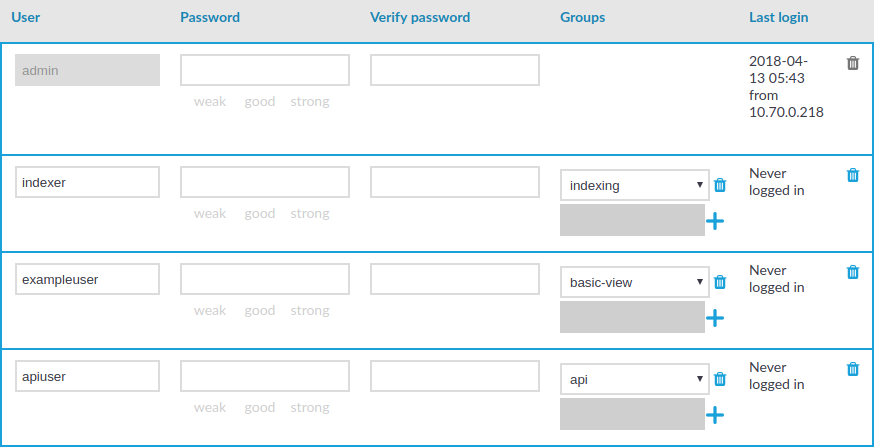
To create a local user
-
Navigate to Users & Access Control > Local Users and click  .
.
Figure 82: Users & Access Control > Local Users — Creating local users
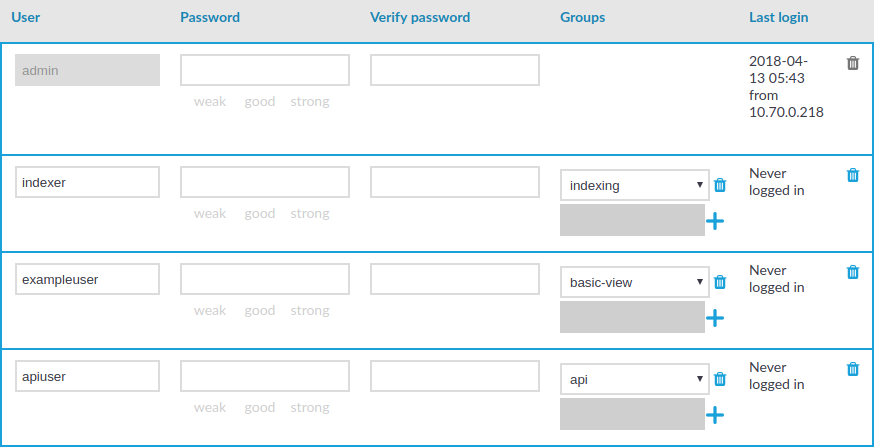
-
Enter the username in the User field.
NOTE: For the username of SSH users, only valid UTF-8 strings are allowed.
The following characters cannot be used in usernames: <>\/[]:;|=,+*?
-
Enter a password for the user in the Password and Verify password fields.
The strength of the password is indicated below the Password field, as you type. To set a policy for password strength, see Setting password policies for local users. The user can change the password later from the SPS web interface, and you can modify the password of the user here.
Use strong passwords: at least 8 characters that include numbers, letters, special characters, and capital letters. For local One Identity Safeguard for Privileged Sessions (SPS) users, require the use of strong passwords (set Users & Access Control > Login options > Minimal password strength to strong). For more information, see "Setting password policies for local users" in the Administration Guide.
NOTE: SPS accepts passwords that are not longer than 150 characters and supports the following characters:
NOTE: If possible, use a random password generator.
To create a strong password:
For strong passwords, do not use:
-
Personal information in the passwords
-
Sequential letters or numbers
-
The word password as the password
-
Keyboard paths (for example, qwerty)
-
Click  in the Groups section and select a group that the user will be a member of. Repeat this step to add the user to multiple groups.
in the Groups section and select a group that the user will be a member of. Repeat this step to add the user to multiple groups.
You can also modify the group membership of local users here.
To remove a user from a group, click  next to the group.
next to the group.
-
To save the modifications, click Commit.
This section describes how to delete local users from One Identity Safeguard for Privileged Sessions (SPS).
To delete a local user from SPS
-
Navigate to Users & Access Control > Local Users.
-
Find the user you want to delete.
-
Click  next to the user, at the right edge of the screen.
next to the user, at the right edge of the screen.
-
To save your modifications, click Commit.
One Identity Safeguard for Privileged Sessions (SPS) can use password policies to enforce the use of:
-
Password history
-
Password strength
-
Password length
-
Password expiry
-
Cracklib protection
Limitations
Consider the following limitations when configuring password policies:
-
Password policies apply only to locally managed users.
-
Password policies do not apply to users managed from an LDAP database, or authenticated to a RADIUS server.
NOTE: SPS accepts passwords that are not longer than 150 characters and supports the following characters:
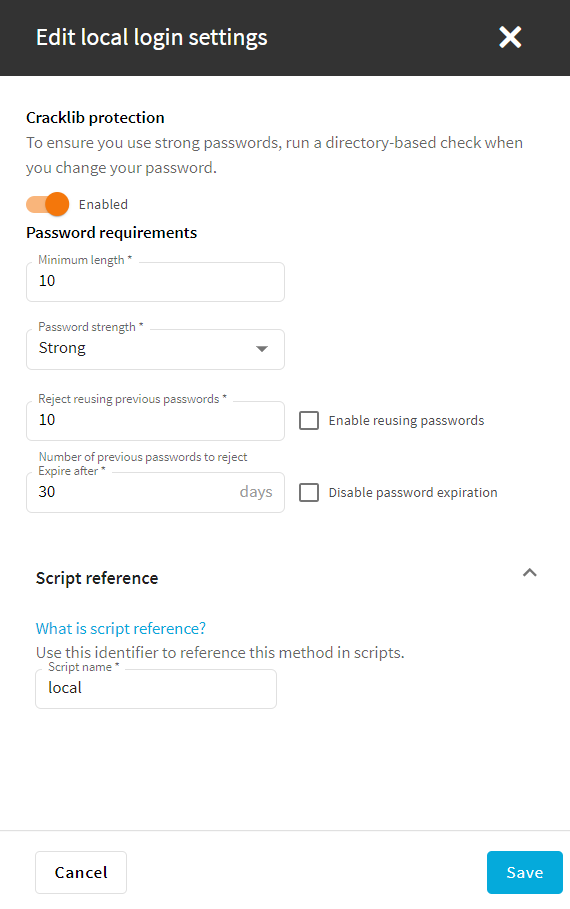
To edit a password policy
-
Navigate to Users & Access Control > Login options.
-
Under Login Options, select the Built-in Local login method and click Edit.
NOTE: Only the local users are affected by the password policy. The password rules of LDAP and RADIUS authentication are not managed by SPS.
Figure 83: Users & Access Control > Login options — Configuring password policies
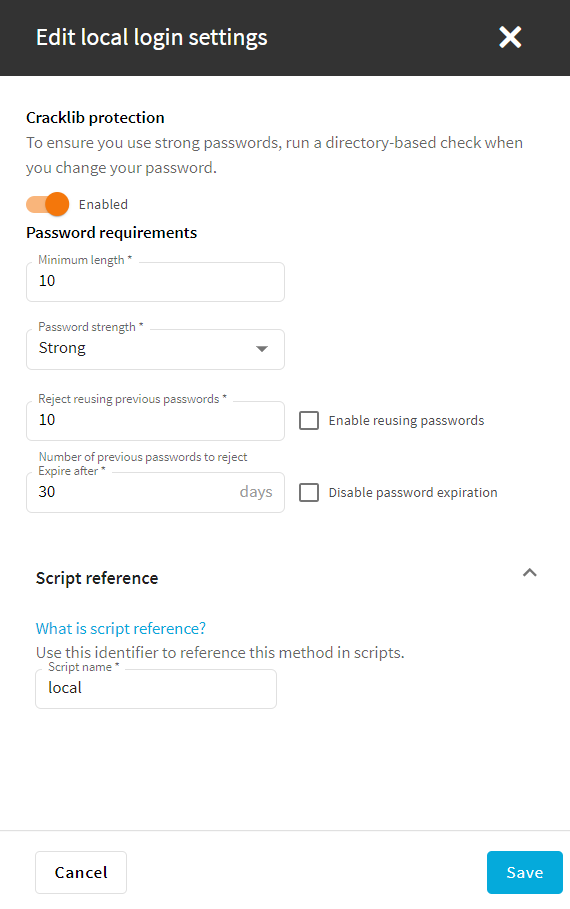
-
(Optional) To do a basic dictionary check on passwords, enable Cracklib protection.
-
In the Expire after text box, configure the validity period of passwords (in days). Once the configured period expires, SPS users must change their passwords. The value range is 1-365. You can also disable the password expiration.
-
Reject reusing previous passwords: use this option to prevent using the same password again for the configured number of password changes. For example, if the value is set to 10, the users must use 10 different passwords consecutively, until the first password can be used again. The acceptable values are 1-30. To disable this option, select Enable reusing passwords.
-
Set the required password complexity level in Password strength. The available values are disabled, good, and strong.
NOTE: The strength of a password is determined by its length and complexity: the variety of numbers, letters, capital letters, and special characters used.
To run simple dictionary-based attacks to find weak passwords, enable Cracklib (eg. dictionary) protection.
-
In Password length, set the minimum number of characters for the passwords. The acceptable values are 1-99.
-
In the Script reference text box, specify a unique, human readable ID for referencing the configured settings in scripts (for example, to enable the REST API clients to select the login method).
-
To save your modifications, click Commit.
NOTE: The changes you make in the password policy do not affect existing passwords. However, configuring password expiration will require every user to change their password after the expiration date. Also, new passwords must comply with the current password strength settings.

 .
.
 next to the group.
next to the group.