The central search functionality is available when your deployment consists of two or more instances of One Identity Safeguard for Privileged Sessions (SPS) organized into a cluster. When you have a cluster of nodes set up, you have the possibility to search all session data recorded by all nodes in the cluster on a single node. This is achieved by assigning roles to the individual nodes in your cluster: you can set up one of your SPS nodes to be the Search Master and the rest of the nodes to be Search Minions. Search Minions send session data that they record to the Search Master, and the Search Master acts as a central search node.
To set up your environment for central searching, complete the following steps:
- Enable cluster management on the nodes that you want to be part of your cluster.
- Build a cluster.
-
Assign roles to nodes in your cluster.
Familiarize yourself with:
- The available search roles before assigning them to nodes. For more information, see Cluster roles.
- Managing a central search configuration. For more information, see Managing a cluster with central search configuration and configuration synchronization.
Once you have your cluster set up and the appropriate roles assigned, you can start searching session data using the Search interface.
NOTE: Central search is not available on the Search (classic) interface.
Limitations of the central search functionality
Currently, the central search functionality comes with the following limitations:
-
Session data recorded by a node before it was joined to the cluster will not be searchable centrally. Only session data recorded after the node has been joined to the cluster is available for central search.
-
You cannot to run the indexer process on unindexed sessions after assigning the Search Master role to a node. Make sure all important sessions are indexed before assigning the Search Master role to the node.
-
The Search Master node cannot run internal indexer processes, nor does it receive connections from external indexers. Indexers work only with Search Minion nodes.
-
It is not possible to replay audit trail files in your browser from the Search Master node.
-
When near real-time indexing is configured on a Search Minion node, while session data from active connections is visible on the Search interface of the Search Master node, it is not possible to:
-
export the audit trail of an active connection,
-
follow an active connection, and
-
terminate an active connection.
Note, however, that you can terminate the active, ongoing connection on the Search Minion node that is recording the connection in question.
-
-
A reliable, high-bandwidth connection is required between the nodes. Small loss of connection is handled well but if the connection between the Search Minions and the Search Master is lost for a longer period of time, the Search Minions will stop accepting new connections until the connection is repaired. Data is automatically pushed to the Search Master after the connection is restored.
NOTE: Search Minion nodes do not send the files storing the audit trails to the Search Master node. When a user clicks 


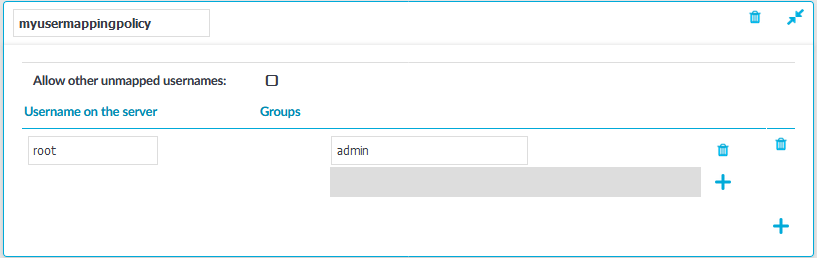
 to create a new policy, and enter a name for the policy.
to create a new policy, and enter a name for the policy. .
.