This section describes how to create and customize HTTP error templates that you can use to send customized HTTP error messages to the users.
Figure 206: HTTP Control — Error templates
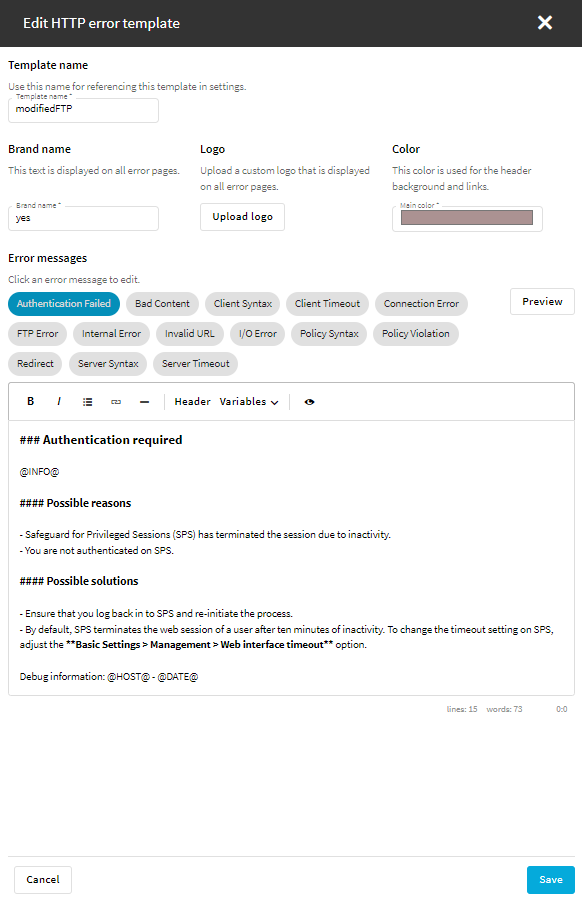
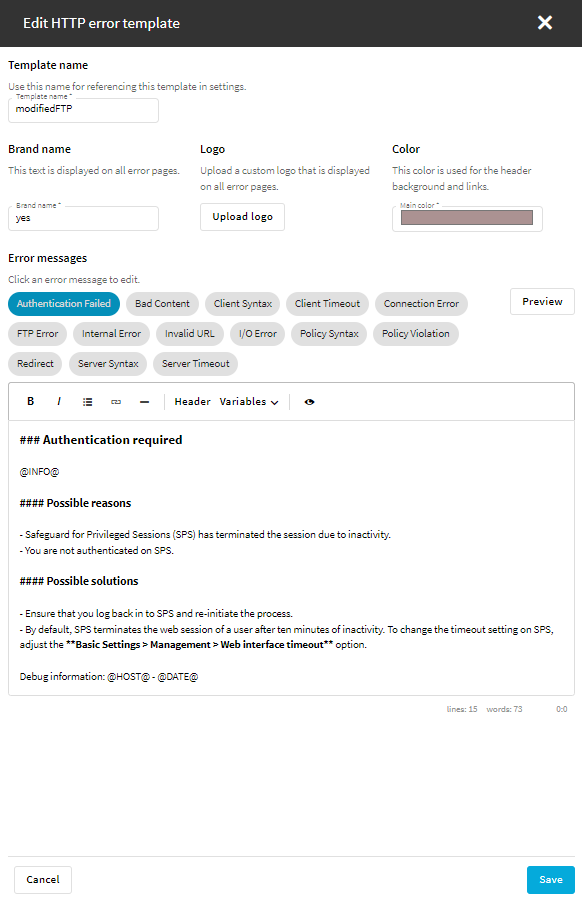
To customize HTTP error templates
-
To create or edit an HTTP error template, navigate to HTTP control > Error templates.
-
To create a new error template, select Create new template and name your template.
The new template contains all the error message templates listed on the Error templates page.
-
To modify an error template, select the template and click Edit.
The following error message templates are available:
-
Authentication Failed
-
Bad Content
-
Client Syntax
-
Client Timeout
-
Connection Error
-
FTP Error
-
Internal Error
-
Invalid URL
-
I/O Error
-
Policy Syntax
-
Policy Violation
-
Redirect
-
Server Syntax
-
Server Timeout
-
Select or modify the brand name, the color, and optionally the logo that is displayed on the customized HTTP error pages.
-
(Optional) Using Markdown language, customize the default content of the error message templates.
-
To check the layout and the content of an error message template, click Preview.
-
Save the error template.
-
In HTTP Control > Settings, select a setting, and in the Error template option, select the error template that you created or customized in this procedure.
For more information, see Creating and editing protocol-level HTTP settings.
The following sections describe configuration settings available only for the ICA protocol. Use the following policies to control who, when, and how can access the ICA connection.
NOTE: As an experimental feature, IPv6 addresses can be configured for ICA connections.
This section focuses on describing the ICA-specific details of connection configuration. For a detailed description on configuring connections, see General connection settings.
|

|
Caution:
If the clients are accessing a remote application or desktop that is shared for Anonymous users (that is, the Users properties of the application is set to Allow anonymous users in the Citrix Delivery Services Console), the actual remote session will be running under an Anonymous account name (for example, Anon001, Anon002, and so on), not under the username used to access the remote server. Therefore, you need to enable usermapping to the Anon* usernames.
To accomplish this, create a usermapping policy and set the Username on the server option to Anon*, and the Groups option to *, then use this usermapping policy in your ICA connections. For details on using usermapping policies, see Configuring usermapping policies. |
Reliable connection is also known as Common Gateway Protocol (CGP). It attempts to reconnect to the server in case of a network failure. To use this feature, enable Reliable and enter the default port in the Port field in the upper right corner.
Enable Act as SOCKS proxy to configure the client to use One Identity Safeguard for Privileged Sessions (SPS) as a SOCKS proxy. If you have enabled this option, you can select Inband destination selection as Target. Enter the IP address or the IP address/Prefix of the brokers (Citrix XML Brokers) used by the client in this connection policy into the Address field. It is also recommended to enable access to the brokers on port 443, as the clients usually try to access the broker using this port first. Disabling port 443 will cause a denied connection to appear on the SPS Search interface for every connection attempt (but the clients will be able to connect the server).
|

|
Caution:
SPS does not audit or monitor the traffic between the brokers and the clients in any way, and are not listed on the SPS search interface. Only the connections between the clients and the actual servers are audited. |
|

|
Caution:
If SPS is acting as a SOCKS proxy and a client attempts to access a server that it is not permitted to access according to the configuration of SPS, SPS will deny the connection. However, the Citrix client application will automatically attempt to connect the server directly without using a proxy and will succeed if the server is directly accessible from the client. Ensure that your firewalls are configured properly to prevent such connections, as these direct connections cannot be audited by SPS. |
NOTE: When enabling Reliable connection or Act as SOCKS proxy the first time, a warning is displayed suggesting the default port to be used based on the specific settings. Also, read the tooltips on these options as they contain up-to-date information about the default port numbers.
The available ICA channel types and their functionalities are described below. For a list of supported client applications, see Supported protocols and client applications.
-
Drawing (Thinwire): Enables access to the server's desktop (screen). This channel is for remoting graphics and user input (keyboard, mouse). This channel must be enabled for ICA to work.
-
Audio Mapping: Enable access to the sound device of the server.
-
Drive Mapping: Enable access to the client's hard drives on the server.
-
Clipboard: Enable access to the server's clipboard: the clipboard of the remote desktop can be pasted into local applications (and vice-versa). Note that One Identity Safeguard for Privileged Sessions (SPS) can audit the clipboard channel, but the Safeguard Desktop Player currently cannot search or display its contents.
-
Smartcard: Enable using client side installed smartcards in server-side applications.
-
Printer (COM1): Enable access to the serial port COM1.
-
Printer (COM2): Enable access to the serial port COM2.
-
Printer (LPT1): Enable access to the parallel port LPT1.
-
Printer (LPT2): Enable access to the parallel port LPT2.
-
Printer Spooler: Enable access to the client's printer from the remote desktops and applications.
-
HDX Mediastream: Some user widgets (for example Flash player) will not run on the server but on the client. These widgets are controlled from the server side using this channel. This is not supported by Safeguard Desktop Player and it is disabled by default.
-
USB: Enable using client side installed USB devices in server-side applications.
-
Seamless: Enable seamless channels that run a single application on the ICA server, instead of accessing the entire desktop. When disabled, the application window will be accessed along with an empty desktop.
-
Speedbrowse: Speeds up web browsing. Not currently supported by Safeguard Desktop Player, should be disabled by default.
-
Custom: Applications can open custom channels to the clients connecting remotely to the server. Enabling the Custom channel allows the clients to access all of these custom channels. To permit only specific channels, enter the unique names of the channel into the Details field.
NOTE: When the channel opens, there are certain cases when the remote group is not known yet. For example, in case of an RDP or ICA login screen, the drawing channel has to be opened first to properly display the logon screen. Only those channel rules will apply, where the Remote group field is empty. In case of network level authentication, all required information is present already so this limitation does not apply.
NOTE: Multi-stream ICA is not supported in SPS6.14.