Introduction
The following guide explains how to integrate SonicWALL with Cloud Access Manager.
Topics:
Overview
Support for SonicWALL malware detection in the Security Analytics Engine, provided with a One Identity Cloud Access Manager installation, requires coordinated configuration with SonicWALL Next Generation Firewall (NGFW), Single Sign-On (SSO), Security Analytics Engine and Cloud Access Manager user authentication.
This guide describes how to implement a typical deployment highlighting the required configuration to fully enable SonicWALL malware detections for Security Analytics Engine user access evaluations, when users access Cloud Access Manager applications.
Functional highlights
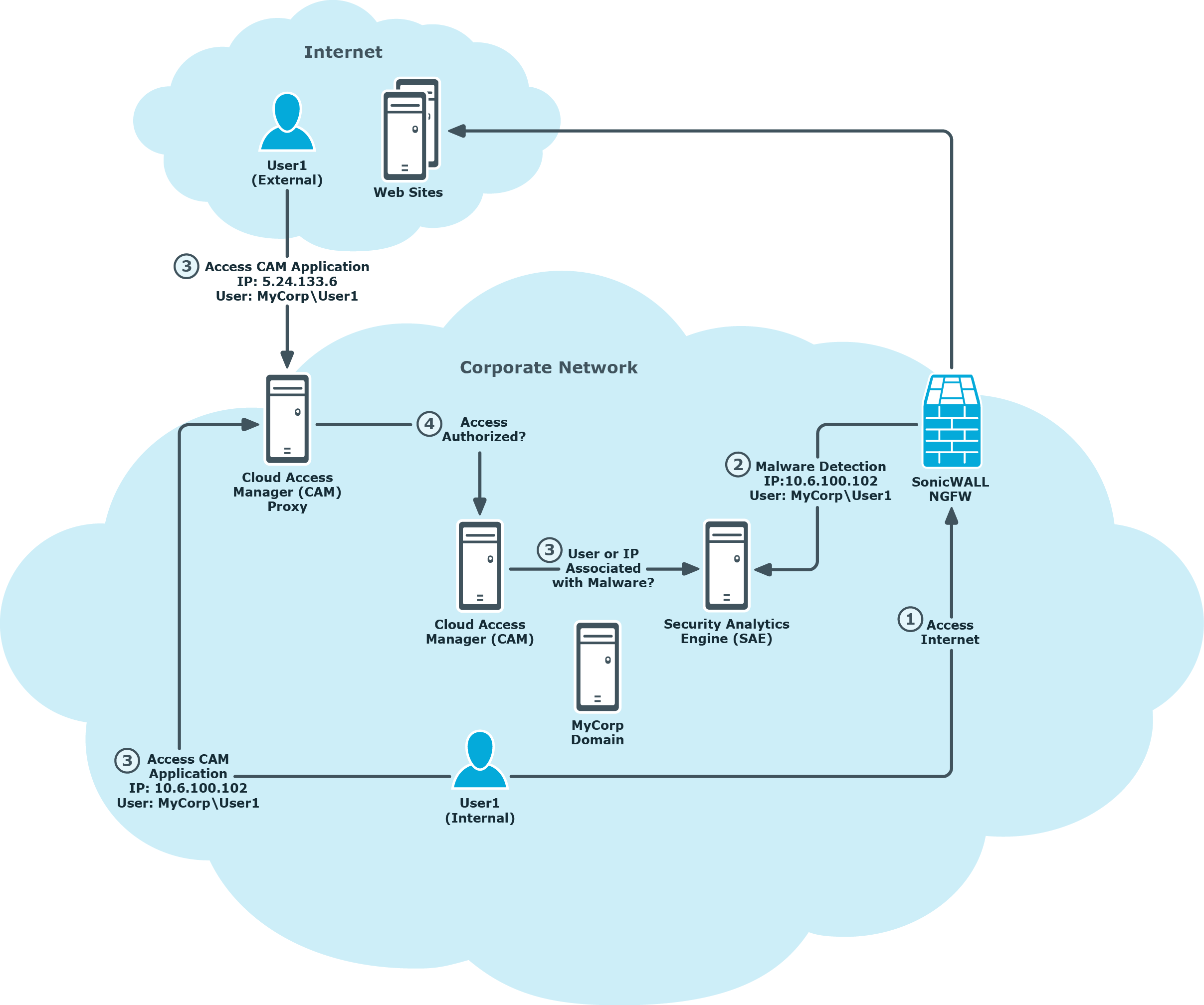
In the following example a typical corporate network is used to illustrate how SonicWALL, the Security Analytics Engine and Cloud Access Manager products are configured to enable Security Analytics Engine risk scoring. This is for Cloud Access Manager users who may have malware detections indicated by a SonicWALL Next Generation Firewall (NGFW), this environment includes:
- A Cloud Access Manager installation configured for internal and external corporate user access.
-
Security Analytics Engine enabled for Cloud Access Manager step-up authentication, with the following:
- Security Analytics Engine policy for Cloud Access Manager configured to enable the Associated w/ Malware condition.
- The optional Security Analytics Engine SonicWALLProcessor service installed and configured to process malware detection information from the firewall.
-
At least one SonicWALL NGFW configured to monitor user Internet access, with the following enabled:
- Single Sign-On enabled for user identification Gateway.
- Anti-Virus, Anti-Spyware and Intrusion Prevention features enabled.
- AppFlow configured to send malware detection flow information to the SonicWALLProcessor service.
The following is a high level overview of the user actions and information flow; this is illustrated in Figure 1 with further details provided in Functional details:
- An internal corporate network user, User1 in the MyCorp domain accesses the internet and encounters some malware. The user is authenticated using the firewall SSO feature; the malware is detected by the NGFW, and optionally blocked.
-
The firewall forwards the malware detection information to the Security Analytics Engine installation, including the IP address and SSO-provided domain and user name, for example:
IP: 10.6.100.102
User: MyCorp\User1
- Later, User1 accesses a Cloud Access Manager application from either inside the corporate network, or from the Internet.
- Cloud Access Manager authenticates the user, detects the IP address and evaluates if the user is authorized to access the application.
-
As part of the authorization determination, Cloud Access Manager queries Security Analytics Engine to determine the user’s risk score, and forwards the user name and IP information for processing by Security Analytics Engine. During the risk score evaluation, Security Analytics Engine will search for malware records received from the firewall and match them on either a user name or IP address, for example:
Internal Access
IP: 10.6.100.102
User: MyCorp\User1
or
Internet Access
IP: 5.24.133.6
User: MyCorp\User1
Figure 1: Cloud Access Manager and SonicWALL deployment overview
Functional details
The following sections provide a detailed breakdown of functionality related to the user authentication, malware detection and risk assessment steps highlighted in Functional highlights, this includes:
