To access protected website
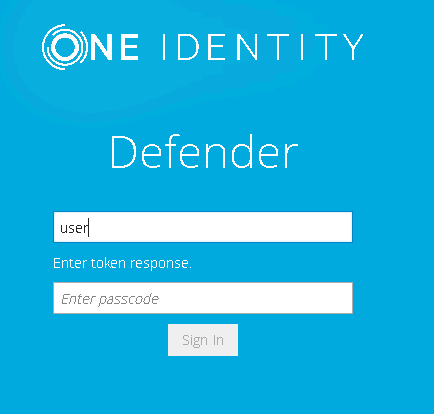
- Using any supported browser, access the protected website. On the Login page, enter your user name and click Sign in.
- In the example below, users are required to authenticate themselves by entering their passcode. The authentication type depends on how the Defender policy has been configured. For example, if Defender is configured to use a token policy, the Enter Synchronous Response prompt will be displayed.
- If users have entered a valid response, they will be authenticated and permitted to access the website.
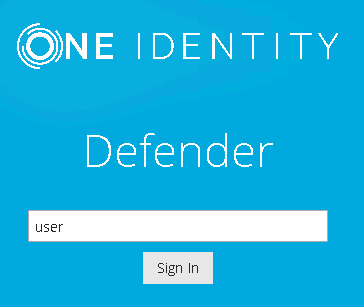
You can configure Defender to authenticate users when they sign in to their Windows-based computers in your organization.
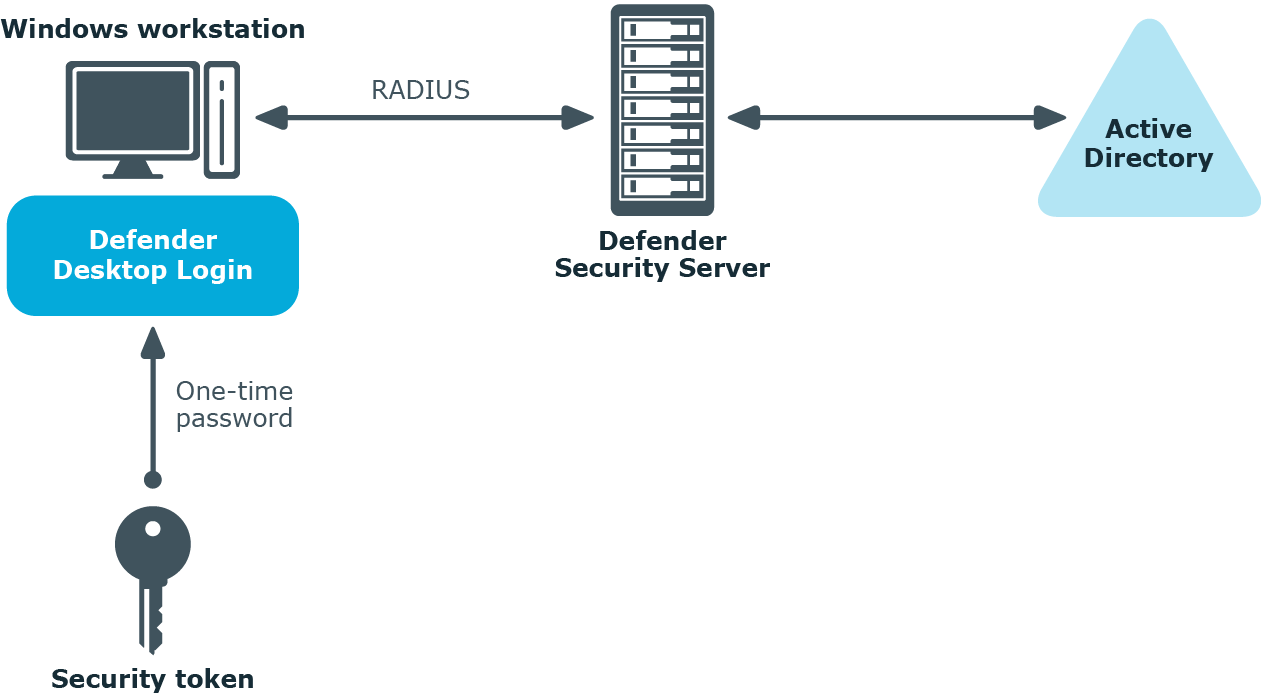
To secure Windows-based computers, in addition to the required Defender components you need to install and configure the component called the Defender Desktop Login on each computer you want to secure with Defender. For more information about installing and configuring the required Defender components, see Deploying Defender.
You can use a wizard to install Defender Desktop Login on a local computer.
To install Defender Desktop Login
- Run the DefenderDesktopLogin.exe file supplied in the Defender distribution package.
- Complete the wizard to install Defender Desktop Login.
You can perform an unattended installation of Defender Desktop Login by using the following .msi files supplied in the Defender distribution package:
- DefenderDesktopLogin_x86.msi Installs Defender Desktop Login on 32-bit systems.
- DefenderDesktopLogin_x64.msi Installs Defender Desktop Login on 64-bit systems.
For example, you can use these files to silently install Defender Desktop Login from a command line or by using Group Policy. For instructions on how to install software by using Group Policy, refer to Microsoft’s knowledge base article 816102.
When using .msi file to install Defender Desktop Login, you can use the following command-line parameters:
Table 13:
Defender MSI parameters
|
DSS |
Specifies a list of Defender Security Servers (by IP address or DNS name) and ports for the Defender Desktop Login software to authenticate against.
Each IP address or DNS name must have a port which is specified using a colon. For multiple entries, use a semicolon as shown in the example (without a space). |
DSS=10.0.0.1:1812
DSS=MyServer1:1812;
MyServer2:1812 |
|
SHARED_SECRET |
Specifies the shared secret which is used to securely communicate and authenticate against the Defender Security Server. |
SHARED_SECRET=MySharedSecretString
|
|
EXCLUSION_MODE |
Determines how Defender Desktop Login authenticates users.
This parameter can take one of the following values:
- 0 Specifies that all users must authenticate via Defender.
- 1 Specifies that members of groups in the EXCLUSION_GROUPS parameter are not required to authenticate via Defender.
- 2 Specifies that only members of groups in the EXCLUSION_GROUPS parameter must authenticate via Defender.
|
EXCLUSION_MODE=0
|
|
EXCLUSION_GROUPS |
Specifies the groups whose members must or are not required to authenticate via Defender.
Behavior of this parameter depends on the value set in the EXCLUSION_MODE parameter.
To specify multiple groups in this parameter, use a semicolon as a separator. |
EXCLUSION_GROUPS=
Administrators;
DEFENDER\Domain Admins
|
|
ALWAYS_ALLOW_LOCAL_LOGON |
Specifies whether to allow local users to log on to a computer that has Defender Desktop Login installed without authenticating via Defender.
This parameter can take one of the following values:
- 0 Do not allow local users to bypass Defender authentication (default value)
- 1 Always allow local users to bypass Defender authentication
|
ALWAYS_ALLOW_LOCAL_LOGON=1 |
|
ALLOW_OFFLINE_LOGON |
Specifies whether users are allowed to log on if all Defender Security Servers are unavailable.
This parameter can take one of the following values:
- 0 Specifies that users cannot log on if all Defender Security Servers are unavailable.
- 1 Specifies that users can only log on for a specified period of time from the moment when all Defender Security Servers become unavailable. If you specify this value, use the OFFLINE_LOGON_DAYS to set the number of days you want.
- 2 Specifies that users can only log on a specified number of times from the moment when all the Defender Security Servers become unavailable. If you specify this value, use the OFFLINE_LOGON_COUNT to set the number of times you want.
|
ALLOW_OFFLINE_LOGON=2
|
|
OFFLINE_LOGON_DAYS |
Specifies the period of time (in days) during which users can log on. This period is counted from the moment when all Defender Security Servers become unavailable.
You can only use this parameter if you set the ALLOW_OFFLINE_LOGON parameter value to 1. |
OFFLINE_LOGON_DAYS=12
|
|
OFFLINE_LOGON_COUNT |
Specifies the number of times user can log on from the moment when all Defender Security Servers become unavailable.
You can only use this parameter if you set the ALLOW_OFFLINE_LOGON parameter value to 2. |
OFFLINE_LOGON_COUNT=45
|
|
DISPLAY_NOTIFICATIONS |
Specifies whether to provide the user with information about the remaining number of offline logons or the remaining number of days when the offline logon will be available.
This parameter can take one of the following values:
- 0 Specifies not to display any offline logon notifications.
- 1 Specifies to display offline logon notifications.
|
DISPLAY_NOTIFICATIONS=1
|
|
STORE_PASSWORDS |
Specifies whether to store user’s password, so that the user is not prompted to reenter the password during each two-factor login.
This parameter can take one of the following values:
- 0 Specifies not to store the user’s password.
- 1 Specifies to store the user’s password.
|
STORE_PASSWORDS=1 |
|
MANAGE_PASSWORDS |
Specifies whether Defender Desktop Login can change a user’s password when the password has expired.
This parameter can take one of the following values:
0 Specifies that Defender Desktop Login can change user’s password.
- 1 Specifies that Defender Desktop Login cannot change user’s password.
|
MANAGE_PASSWORDS=1 |
|
WAIT_FOR_NETWORK |
Specifies the time period (in seconds) during which Defender Desktop Login waits for the network to become available at startup. The default value is 60 seconds. |
WAIT_FOR_NETWORK=60 |
|
BLOCK_CREDENTIAL_PROVIDERS |
Specifies credential providers Defender Desktop Login should block.
This parameter can take one of the following values:
- 0 Specifies to allow all credential providers.
- 1 Specifies to block all credential providers except Defender Credential Provider.
- 2 Specifies to block Microsoft’s credential providers.
|
BLOCK_CREDENTIAL_PROVIDERS=0 |