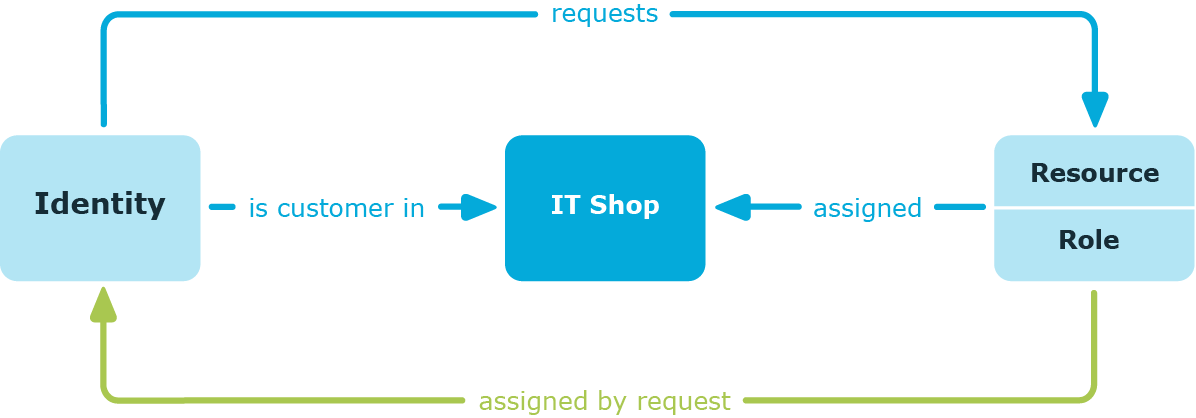
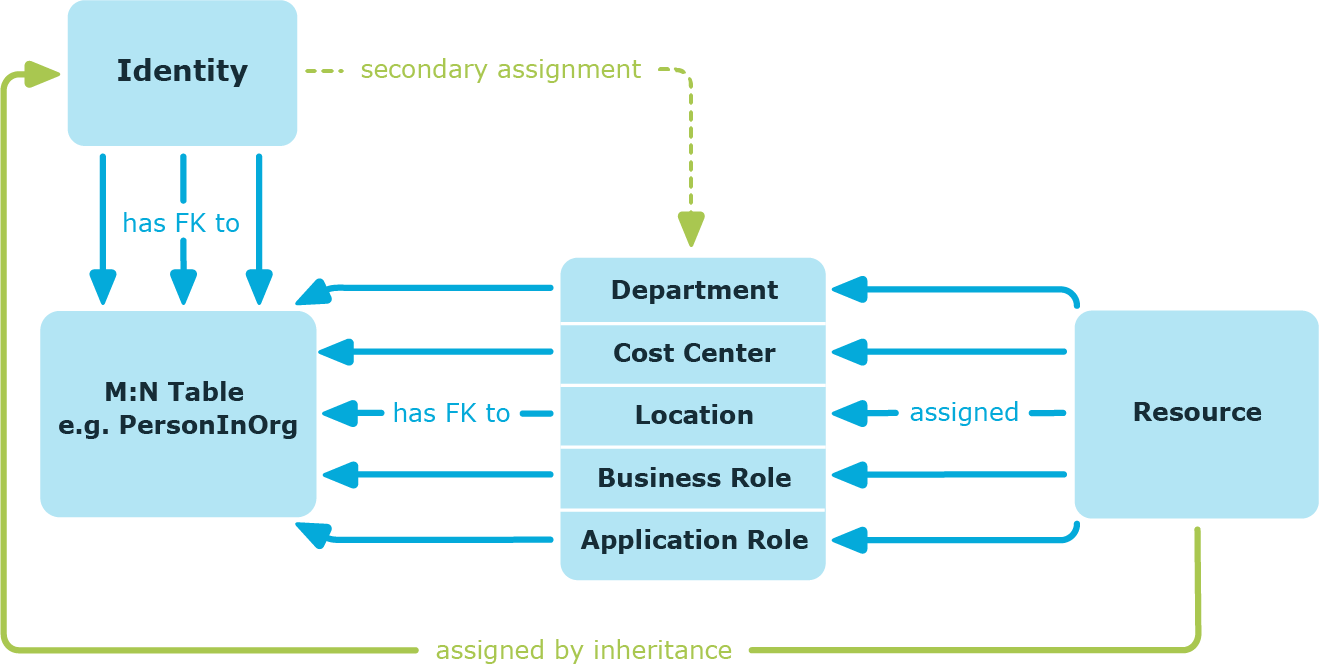
Secondary assignment of company resources
You make a secondary assignment by classifying an identity, a device, or a workdesk within a role hierarchy. Secondary assignment is the default method for assigning and inheriting company resources through roles. In the role classes , specify whether a secondary assignment of company resources to identities, device, and workdesk is possible.
Figure 7: Secondary assignment inheritance schema
Related topics
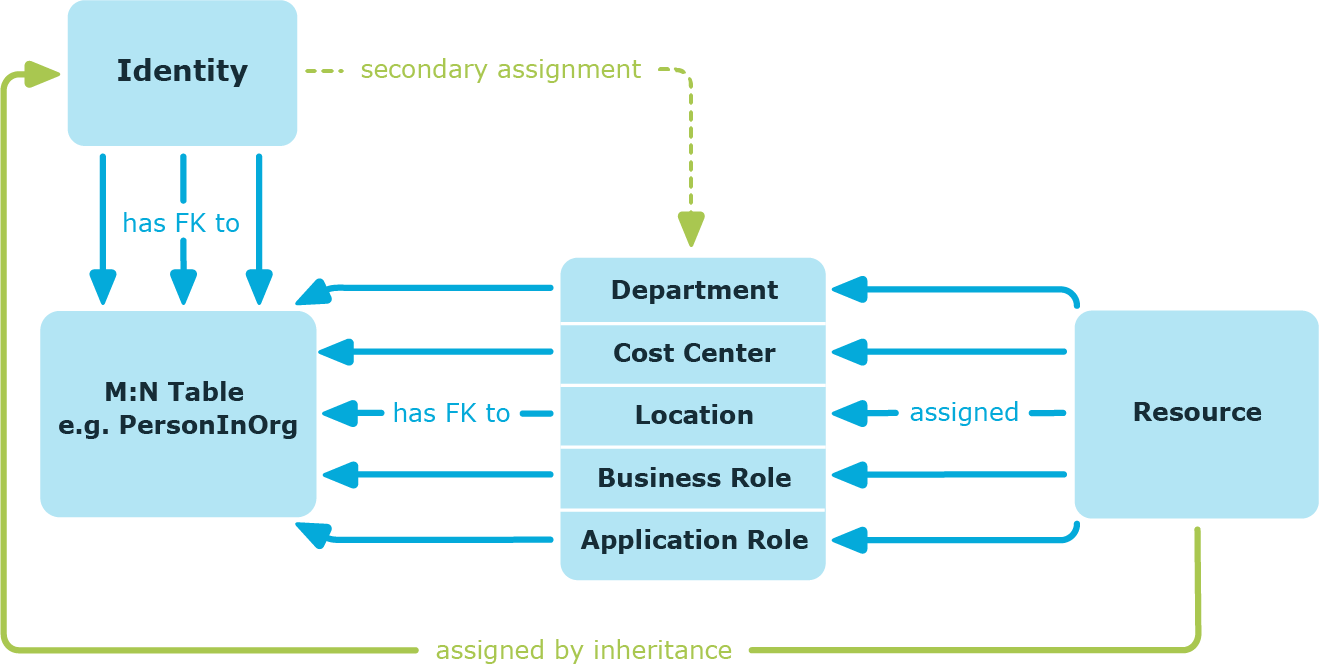
Primary assignment of company resources
You make a primary assignment using a business role, cost center, or location foreign key reference in identity, device and workdesk objects. To do this, use the role fields on the identity, device, and workdesk main data forms. Primary assignment inheritance can be enabled through configuration parameters. Primary assignment is enabled for identities by default.
Figure 8: A primary assignment schema
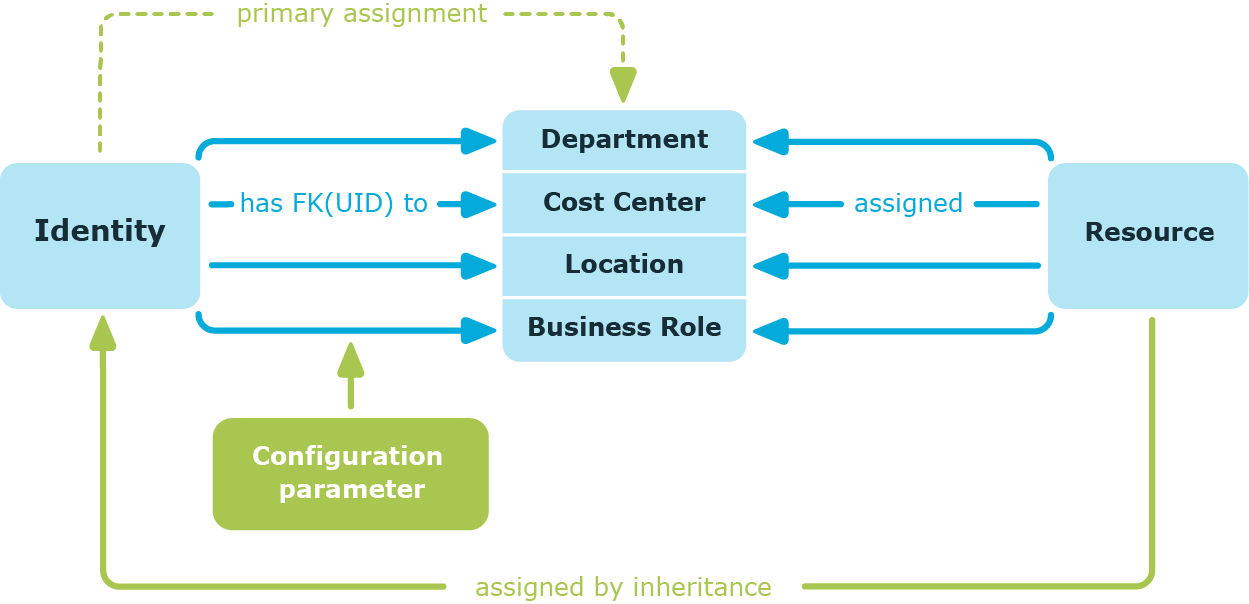
NOTE: Changes to the configuration parameter result in the inheritance data being recalculated! That means: if the primary assignment is disabled at a later date, the inheritance data created in this way will be removed from the database.
Table 2: Configuration parameters for primary assignment
|
QER | Structures | Inherite | Person |
Identities can inherit through primary assignment. |
|
QER | Structures | Inherite | Person | FromOrg |
Identities inherit assignments from their primary business role (Person.UID_Org). |
|
QER | Structures | Inherite | Hardware |
Devices can inherit through primary assignment. |
|
QER | Structures | Inherite | Hardware | FromOrg |
Devices inherit assignments from their primary business role (Hardware.UID_Locality). |
|
QER | Structures | Inherite | Workdesk |
Workdesks can inherit though primary assignment. |
|
QER | Structures | Inherite | Workdesk | FromOrg |
Workdesks inherit assignments from their primary business role (Workdesk.UID_Org). |
Assigning company resources through dynamic roles
Assignment through dynamic roles is a special case of indirect assignment. Dynamic roles are used to specify role memberships dynamically. Identities, devices, and workdesks are not permanently assigned to a role, just when they fulfill certain conditions. A check is performed regularly to assess which identities, devices, or workdesks fulfill these conditions. This means the role memberships change dynamically. For example, company resources can be assigned dynamically to all identities in a business role in this way; if an identity leaves the department they immediately lose the resources assigned to them.
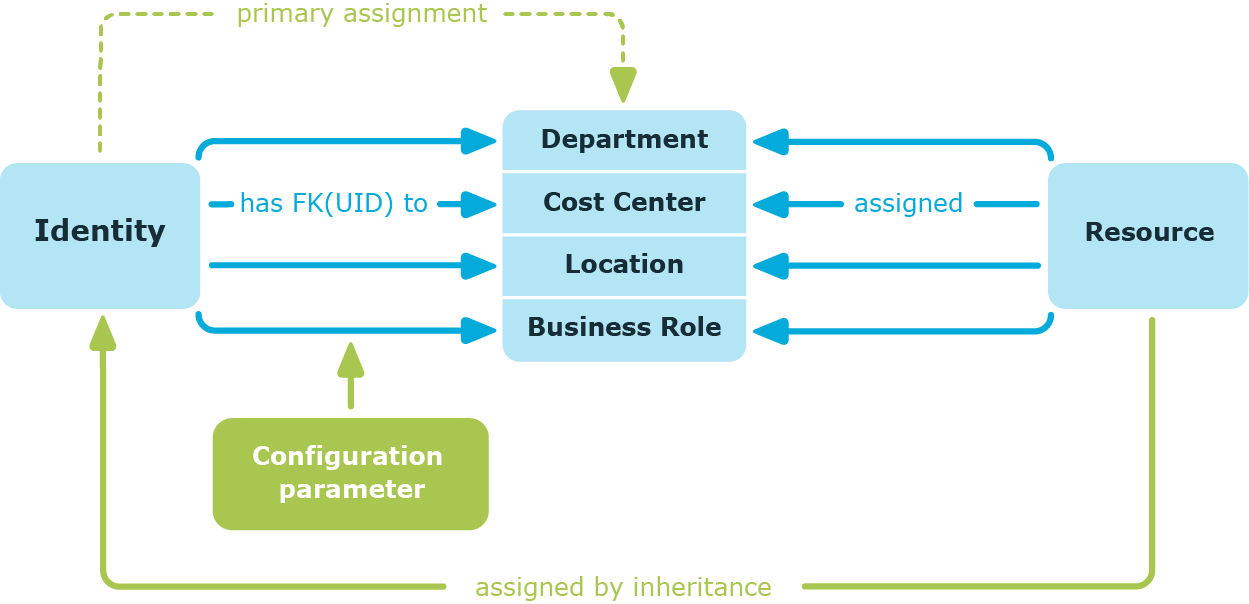
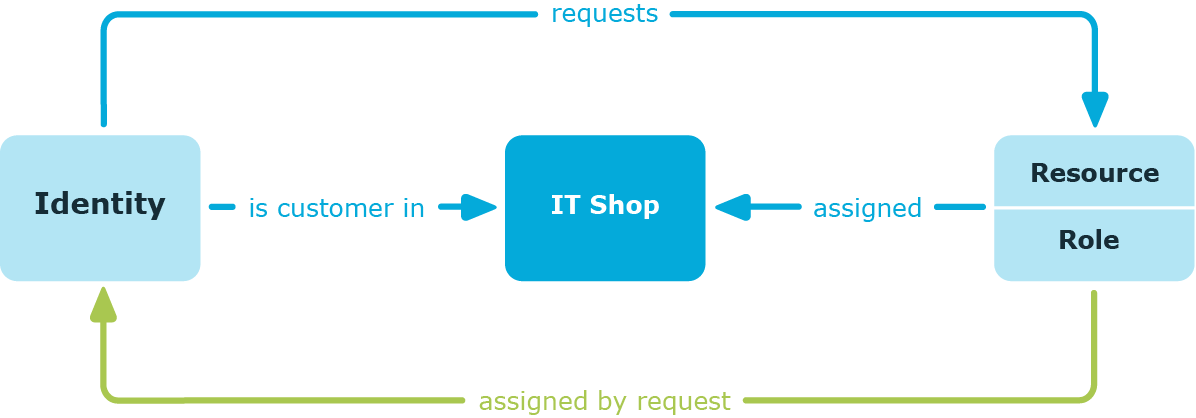
Assigning company resources through IT Shop requests
Assignment through the IT Shop is a special case of indirect assignment. Add identities to a shop as customers so that company resources can be assigned through IT Shop requests. All company resources assigned as product to this shop can be requested by the customers. Requested company resources are assigned to the identities after approval is granted. Role memberships can be requested through the IT Shop as well as company resources.
Figure 9: Schema of assignment by requests