This section describes how to create and customize HTTP error templates that you can use to send customized HTTP error messages to the users.
Figure 195: Traffic Controls > HTTP — Error templates
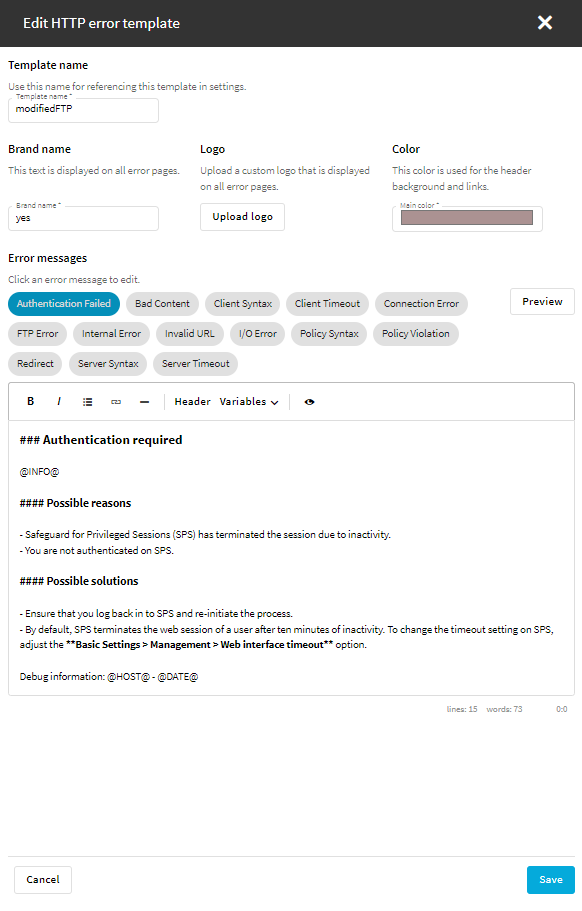
To customize HTTP error templates
-
To create or edit an HTTP error template, navigate to Traffic Controls > HTTP > Error templates.
-
To create a new error template, select Create new template and name your template.
The new template contains all the error message templates listed on the Error templates page.
-
To modify an error template, select the template and click Edit.
The following error message templates are available:
-
Authentication Failed
-
Bad Content
-
Client Syntax
-
Client Timeout
-
Connection Error
-
FTP Error
-
Internal Error
-
Invalid URL
-
I/O Error
-
Policy Syntax
-
Policy Violation
-
Redirect
-
Server Syntax
-
Server Timeout
-
-
Select or modify the brand name, the color, and optionally the logo that is displayed on the customized HTTP error pages.
-
(Optional) Using Markdown language, customize the default content of the error message templates.
-
To check the layout and the content of an error message template, click Preview.
-
Save the error template.
-
In Traffic Controls > HTTP > Settings, select a setting, and in the Error template option, select the error template that you created or customized in this procedure.
For more information, see Creating and editing protocol-level HTTP settings.

