Table 1: General configuration parameters for company policies
| QER | Policy |
Preprocessor relevant configuration parameter for controlling company policy validation. Changes to the parameter require recompiling the database. If the parameter is enabled, you can use the model components. |
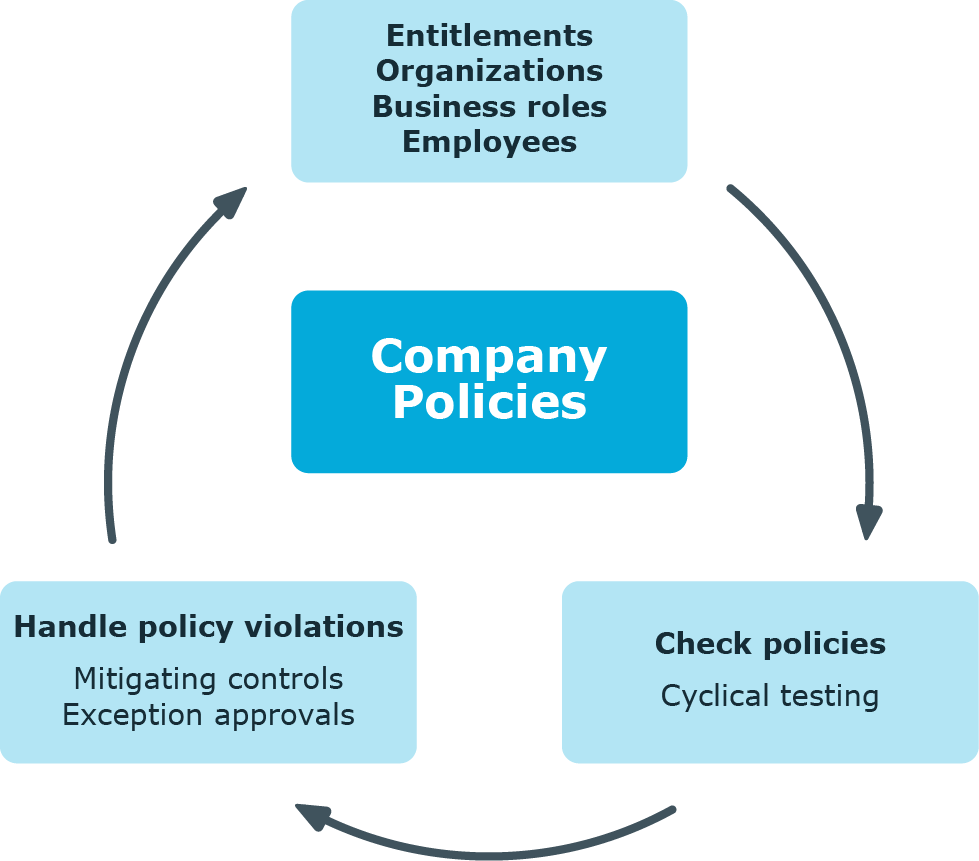
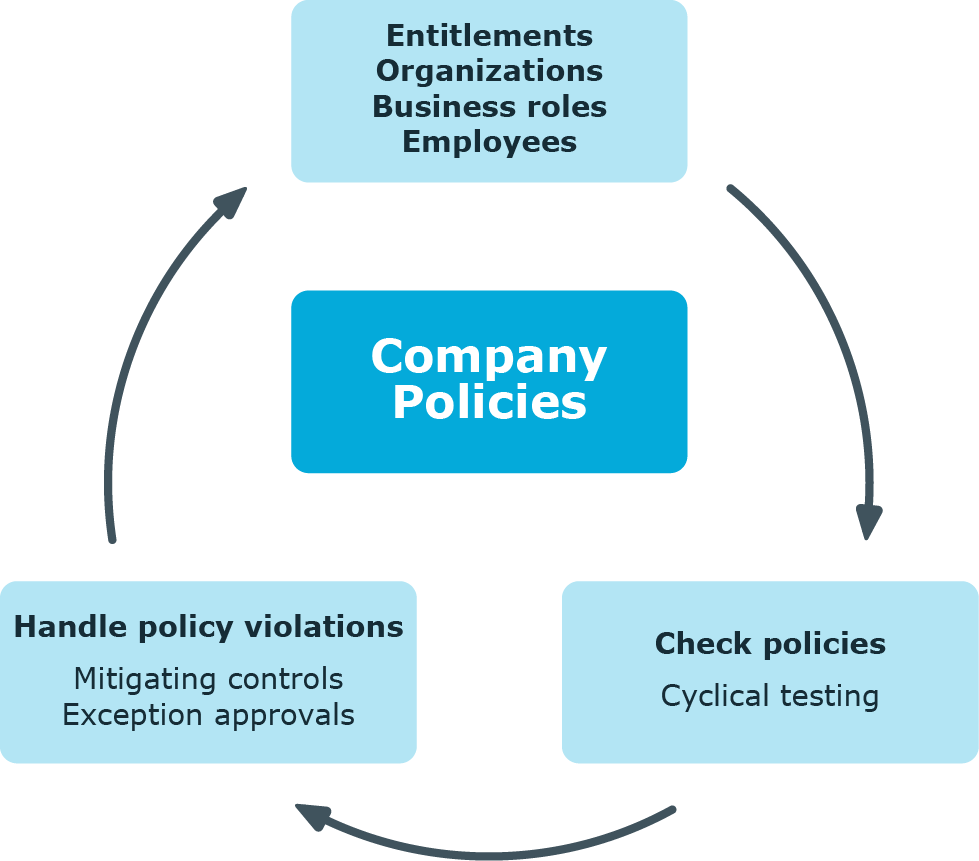
Companies have varying requirements that they need for regulating internal and external employee access to company resources. They also have to demonstrate that they adhere to legal requirements. Such requirements can be defined as policies.
One Identity Manager allows you to manage these company policies and thus to assess the risk involved. Assuming the appropriate data is stored in the One Identity Manager database, One Identity Manager determines all the company resources that violate these company policies. You can also define company policies for the purpose of providing reports that do not have any connection with One Identity Manager.
Adherence to company policies is checked regularly using scheduled tasks. You can incorporate company policies into the regular attestation of your company resources to decide on further handling of any violated ones. Risk assessment can be run for all company policies. Different reports and statistics provide you with an overview of violated policies.
Figure 1: Company policies in One Identity Manager
Example of company policies are:
- All cost centers are assigned a manager.
- All departments are assigned employees.
- All employees are attested.
- Deactivated employees do not have any enabled user accounts.
To be able to map company policies
- In the Designer, set the QER | Policy configuration parameter.
If you disable the configuration parameter at a later date, model components and scripts that are not longer required, are disabled. SQL procedures and triggers are still carried out. For more information about the behavior of preprocessor relevant configuration parameters and conditional compiling, see the One Identity Manager Configuration Guide.
The following users are used for setting up and administration of company policies.
Table 2: Users
| Company policy administrators |
Administrators must be assigned to the Identity & Access Governance | Company policies | Administrators application role.
Users with this application role:
-
Enter base data for setting up company policies.
-
Set up policies and assign policy supervisors to them.
-
Can calculation policies and view policy violations if required.
-
Set up reports about policy violations.
-
Enter mitigating controls.
-
Create and edit risk index functions.
-
Administer application roles for policy supervisors, exception approvers and attestors.
-
Set up other application roles as required. |
| Policy supervisors |
Policy supervisors must be assigned to the Identity & Access Governance | Company policies | Policy supervisors application role or another child application role.
Users with this application role:
-
Are responsible for the contents of company policies.
-
Edit working copies of company policies.
-
Enable and disable company policies.
-
Can calculation policies and view policy violations if required.
-
Assign mitigating controls. |
| One Identity Manager administrators |
administrator and administrative system users Administrative system users are not added to application roles.
administrators:
-
Create customized permissions groups for application roles for role-based login to administration tools in the Designer as required.
-
Create system users and permissions groups for non role-based login to administration tools in the Designer as required.
-
Enable or disable additional configuration parameters in the Designer as required.
-
Create custom processes in the Designer as required.
-
Create and configure schedules as required. |
| Exception approvers |
Exception approvers must be assigned to the Identity & Access Governance | Company policies | Exception approvers application role or a child application role.
Users with this application role:
|
| Company policy attestors |
Attestors must be assigned to the Identity & Access Governance | Company policies | Attestors application role.
Users with this application role:
NOTE: This application role is available if the module Attestation Module is installed. |
| Compliance and security officer |
Compliance and security officers must be assigned to the Identity & Access Governance | Compliance & Security Officer application role.
Users with this application role:
-
View all compliance relevant information and other analysis in the Web Portal. This includes attestation policies, company policies and policy violations, compliance rules, and rule violations and risk index functions.
-
Edit attestation polices. |
| Auditors |
Auditors are assigned to the Identity & Access Governance | Auditors application role.
Users with this application role:
|
Various basic data is required to create company policies, run policy checks and handle policy violations.
Use policy groups to group together company policies by functionality. You can use policy to groups to structure company policies hierarchically.
To edit a policy group
- Select the Company Policies > Basic configuration data > Policy groups category.
- Select a policy group in the result list. Select the Change main data task.
- OR -
Click  in the result list.
in the result list.
- Edit the main data of the policy group.
- Save the changes.
Enter the following data for a policy group
Table 3: General main data of a policy group
| Group name |
Name of the policy group. |
| Parent group |
Policy group above this one in a hierarchy.
Select a parent policy group area from the list for organizing your policy groups hierarchically. |
In the Policy violation overview report, you can get an overview of all policy violations for a policy group.

 in the result list.
in the result list.