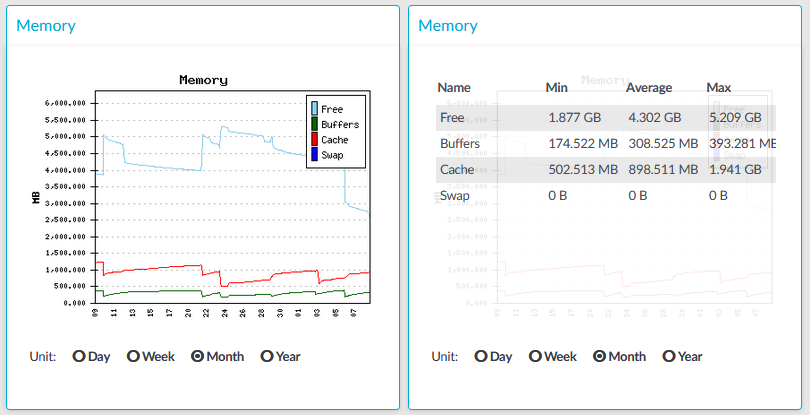
Figure 372: Basic Settings > Dashboard > Memory
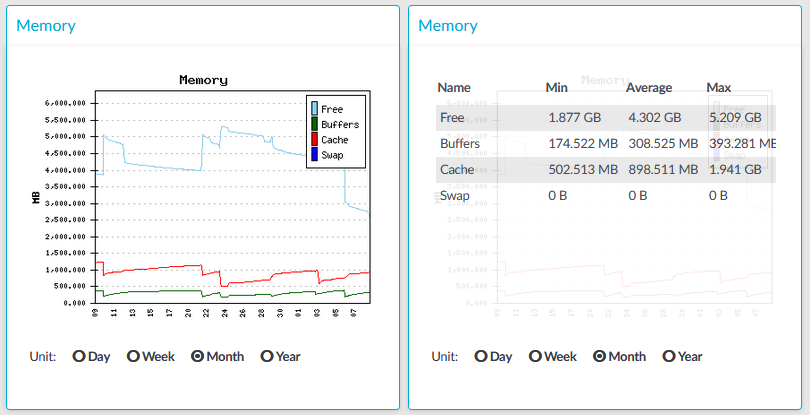
The Memory module on the Dashboard is based on data provided by the Linux kernel (/proc and /sys directories). The standard Munin plugins query this information from these locations and they are displayed on the GUI.
Statistics
The memory types displayed are the following:
-
Free: Free memory
-
Buffers: In-memory block I/O buffers.
-
Cache: Memory used for disk caching. This does not count as "used" memory, because it is freed when it is required.
-
Swap: Swap space usage (memory contents that have been temporarily moved to disk).This value might be high in case of lack of memory.
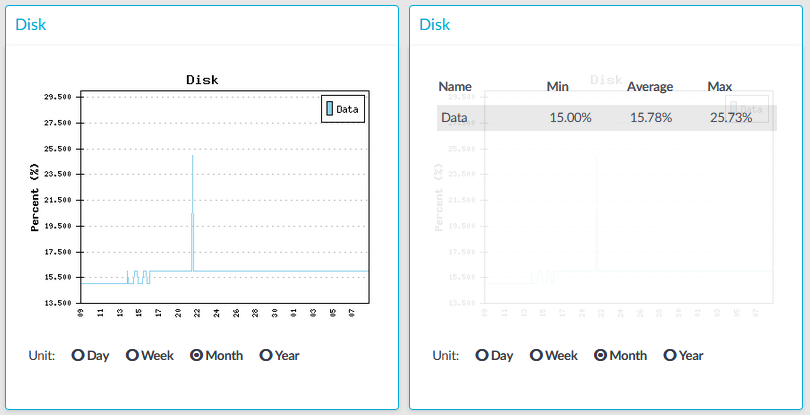
Figure 373: Basic Settings > Dashboard > Disk
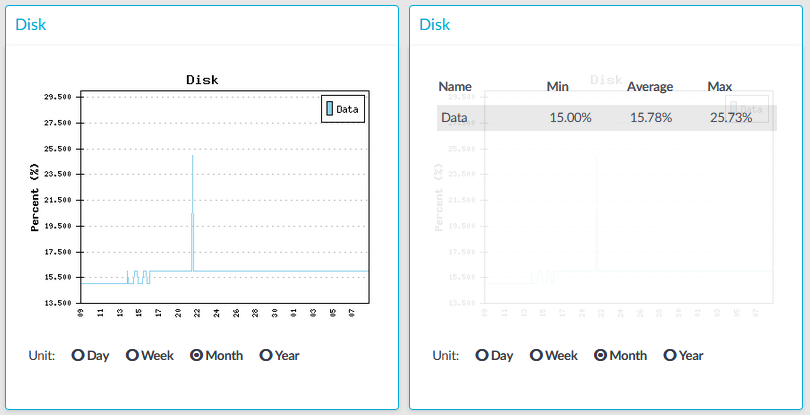
The Disk module on the Dashboard is based on the output of the df command.
Statistics
The information displayed is the following:
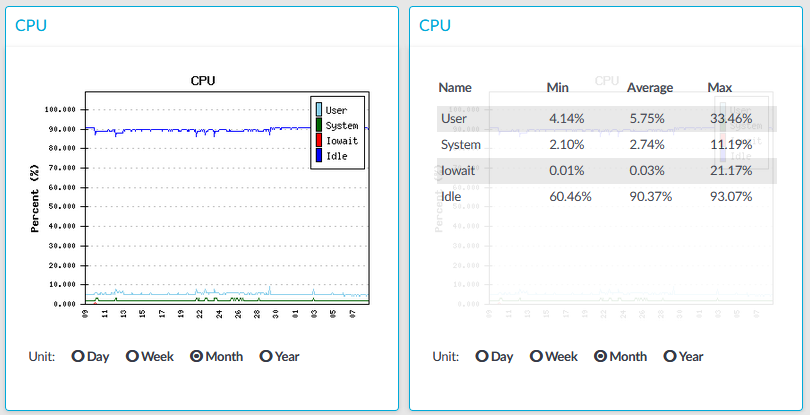
Figure 374: Basic Settings > Dashboard > CPU
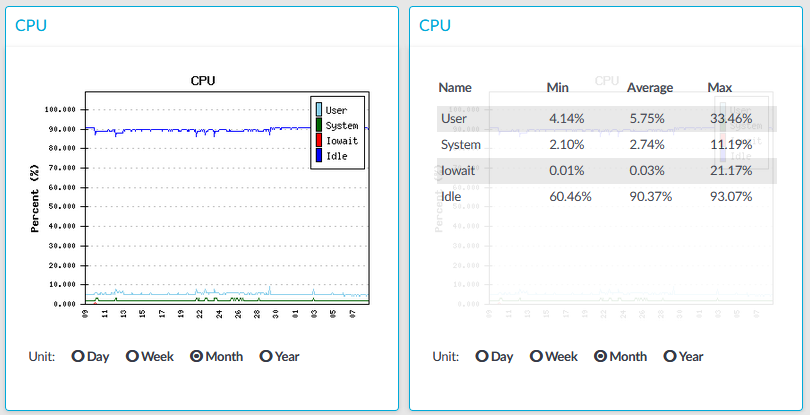
The CPU module on the Dashboard is based on data provided by the Linux kernel (/proc and /sys directories). The standard Munin plugins query this information from these locations and they are displayed on the GUI.
Statistics
The following details are displayed about CPU usage:
-
Idle: Idle time of the processors. If there are more than one processors, they all add up to x100%, for example in case of 2 processors it adds up to 200% maximum.
-
Iowait: Time spent receiving and handling hardware interrupts as a percentage of processor ticks. That is, waiting for IO.
-
System: Kernel CPU usage.
-
User: CPU usage of everything other than kernel.
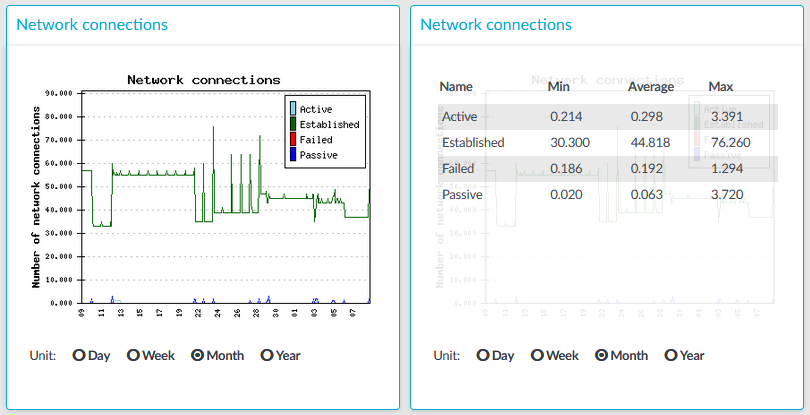
Figure 375: Basic Settings > Dashboard > Network connections
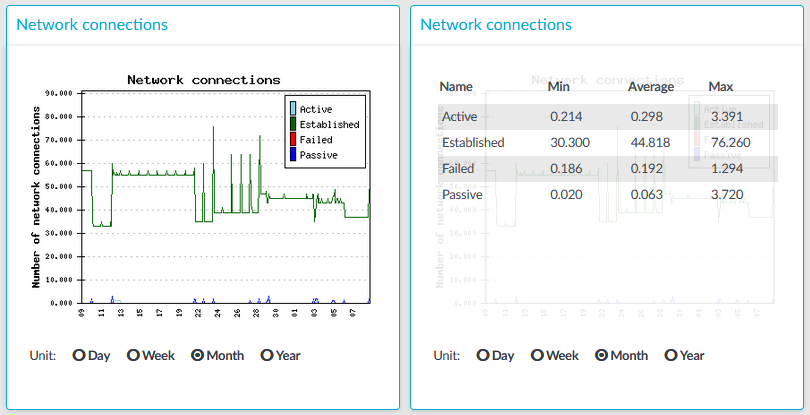
The Network connetion module on the Dashboard is based on the output of the netstat -s command. This command generates statistical information from all interfaces of all TCP connections. This means that in addition to the high-level proxy-service protocols (SSH, RDP, VNC, ICA, and so on), but all types of TCP connections are counted as well. The standard Munin plugins query this information and then it is displayed on the GUI. The graph itself displays the TCP activity of all network interfaces combined.
Statistics
The connection types displayed can be the following:
-
Active: The number of active TCP openings per second.
-
Established: The number of currently open connections.
-
Failed: The number of failed TCP connection attempts per second.
-
Passive: The number of passive TCP openings per second.
-
Resets: The number of TCP connection resets.
The Min, Average and Max values are displayed as a whole number if the value is constant for the statistics interval (the statistics are stored every 5 minutes). If minor changes occur in the actual values (for example, new connections are established), these changes can be displayed as fractions.
To determine the maximum values that the system can handle, consider the following: