The next diagram illustrates a scenario where Defender is configured to authenticate the users who access Web sites hosted on Microsoft Internet Information Services (IIS).
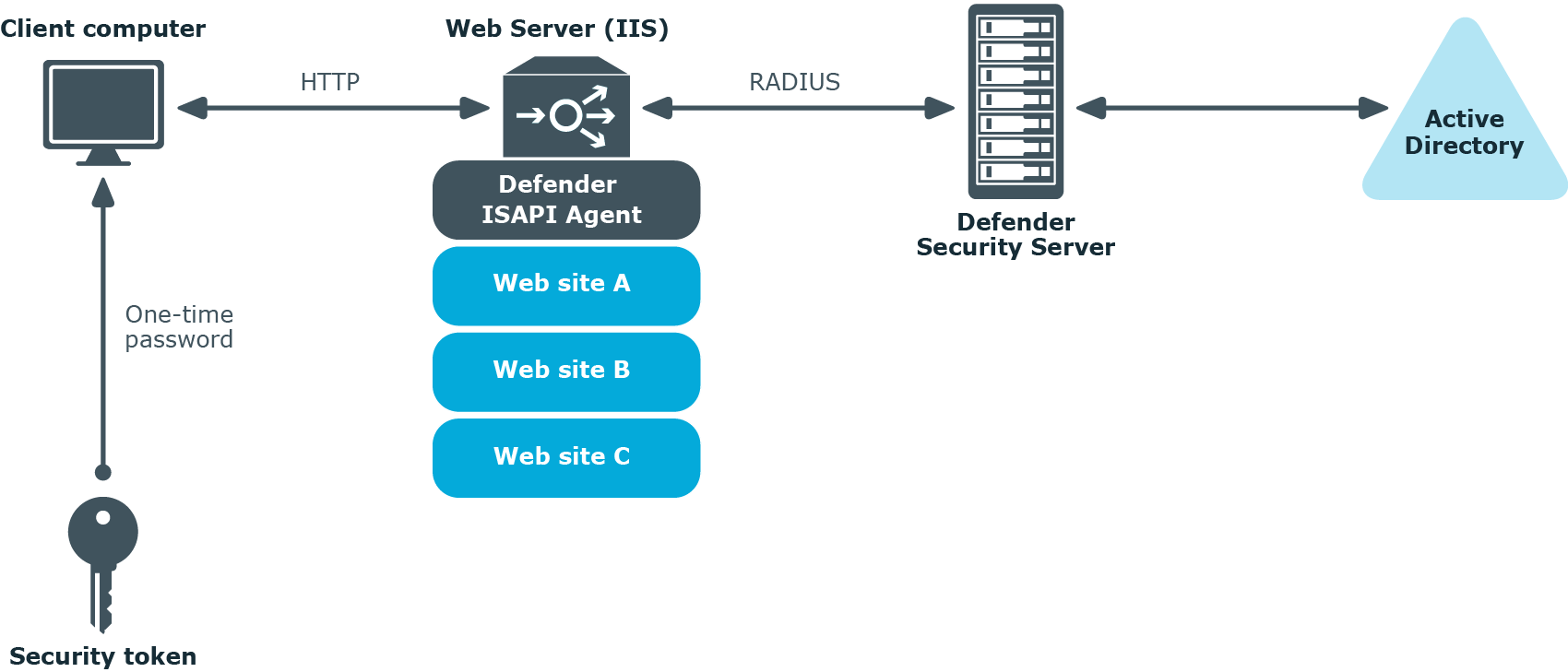
In this scenario, the Defender ISAPI Agent must be deployed on the Web Server that hosts the Web sites to be secured with Defender. The ISAPI Agent acts as an ISAPI filter and requires users to authenticate via Defender in order to get access to the Web sites hosted on the Web Server.