The host keys of the servers can be added either automatically or manually.
To add the host key automatically
-
Navigate to the Traffic Controls > SSH > Connections.
-
Configure a connection: fill the From, To, and Port fields.
You can use IPv4 and IPv6 addresses as well.
-
To configure a transparent connection, enter the IP address of the server into the To field.
-
To configure a non-transparent connection, enter the IP address of SPS into the To field, and the address of the target server into the Target field.
-
Click  to display the advanced settings and verify that the Server side host key settings > Plain host key check option is set to Accept key for the first time.
to display the advanced settings and verify that the Server side host key settings > Plain host key check option is set to Accept key for the first time.
Click  .
.
-
Initiate an SSH connection from the client to the server. SPS will automatically record the host key of the server — the server's IP address and the host key will be listed on the Traffic Controls > SSH > Server Host Keys page.
The following describes how to add the host key manually.
To add the host key manually
-
Navigate to the Traffic Controls > SSH > Server Host Keys and click Create new.
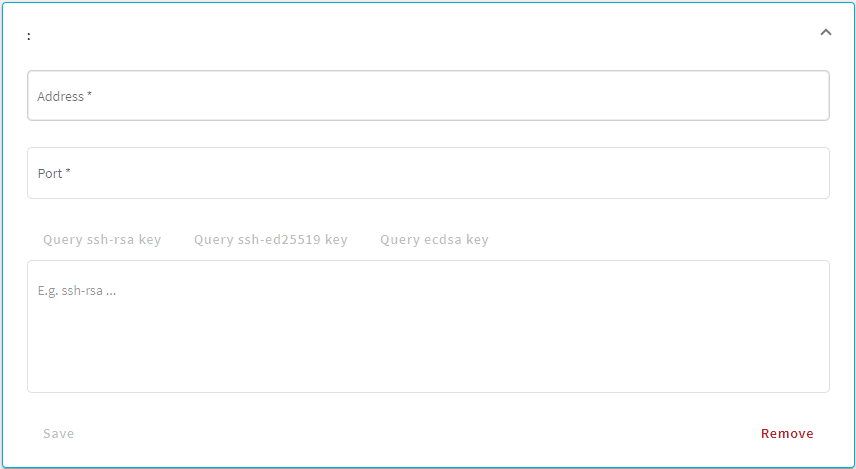
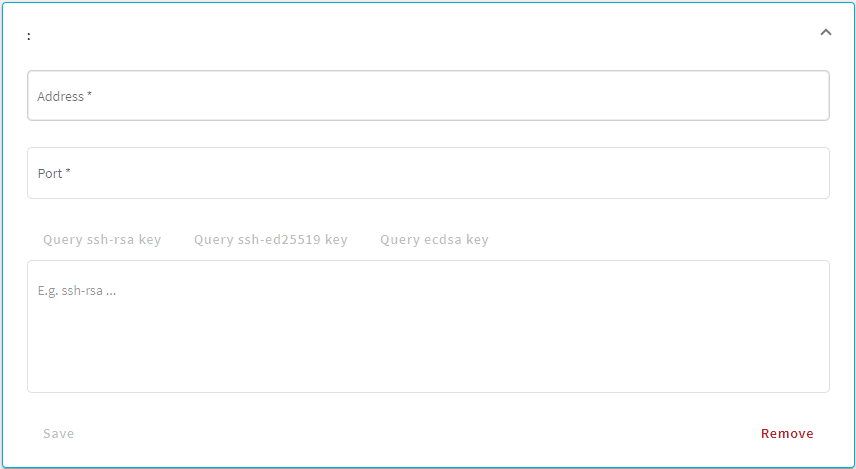
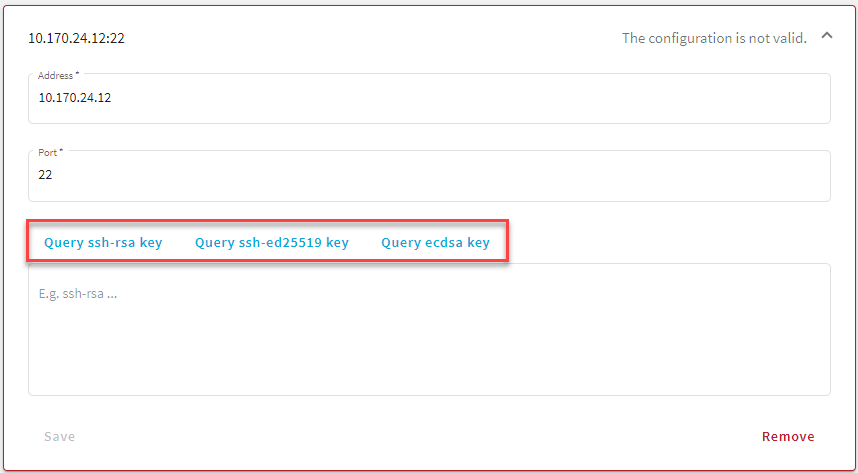
Figure 234: Traffic Controls > SSH > Server Host Keys — Create new
-
Enter the IP address and port of the server into the Address and Port fields.
You can use IPv4 and IPv6 addresses as well.
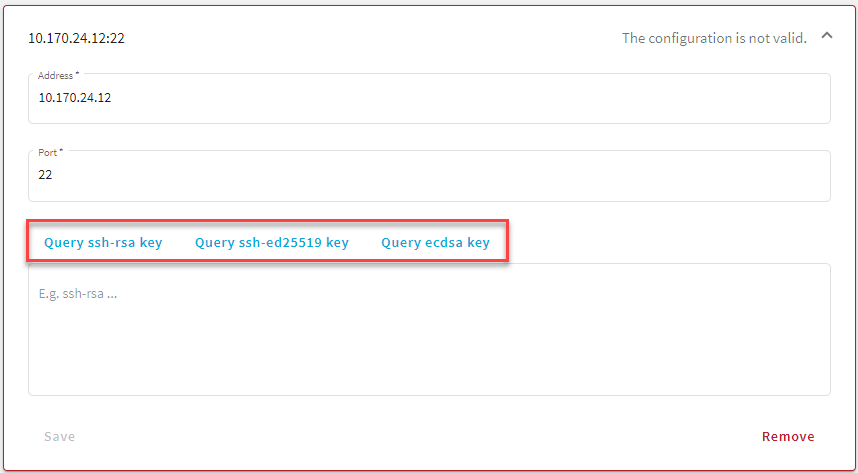
Figure 235: Traffic Controls > SSH > Server Host Keys — Example of active Query fields
-
Once you fill out the Address and Port fields, the Query... fields become active and you can query the public part of the host key of the server.
SPS allows you to use the following SSH host keys:
-
RSA (ssh-rsa), which is the most widely used public-key algorithm for the SSH key. In SPS, uploading RSA SSH host keys are supported in PKCS #1 PEM, PKCS #8 PEM, OpenSSH (openssh-key-v1), and PuTTY private key formats.
NOTE:
TIP: One Identity recommends using 2048-bit RSA keys (or stronger).
-
Ed25519 (ssh-ed25519), which offers a better security and faster performance compared to RSA.
In SPS, uploading Ed25519 SSH host keys are supported in PKCS #8 PEM, OpenSSH (openssh-key-v1), and PuTTY private key formats.
-
ECDSA NIST P-256 (ecdsa-sha2-nistp256), which is a variant of the Digital Signature Algorithm (DSA). In SPS, uploading ECDSA SSH host keys are supported in SEC1 PEM, PKCS #8 PEM, OpenSSH (openssh-key-v1), and PuTTY private key formats.
You can have multiple SSH server host keys on SPS for the same server, however, you cannot set more than one key for each type. For example, you can keep your old RSA SSH key and generate a new Ed25519 key but you cannot set two RSA keys.
Alternatively, paste the public part of the host key of the server.
-
Click Save.
SSH settings determine the parameters of the connection on the protocol level. For example, when the server-side connection is built, the timeout value, and greeting message of the connection. The following parameters determine which algorithms are used in the connections, and can be set independently for the client and the server side: key exchange, host key, cipher, MAC, and compression algorithms.
|

|
Caution:
Before modifying any of the algorithm settings, check whether the default algorithms are supported by your SSH client and server.
If yes, then you can leave these settings untouched.
If not and you need to amend the default algorithm settings, ensure that the client and server sides are harmonized. You can either do that in One Identity Safeguard for Privileged Sessions (SPS) or on the client/server itself.
Note that modifying algorithm settings in SPS is recommended to advanced users only. If you are unsure about which settings to amend, then contact our Support Team for assistance. |
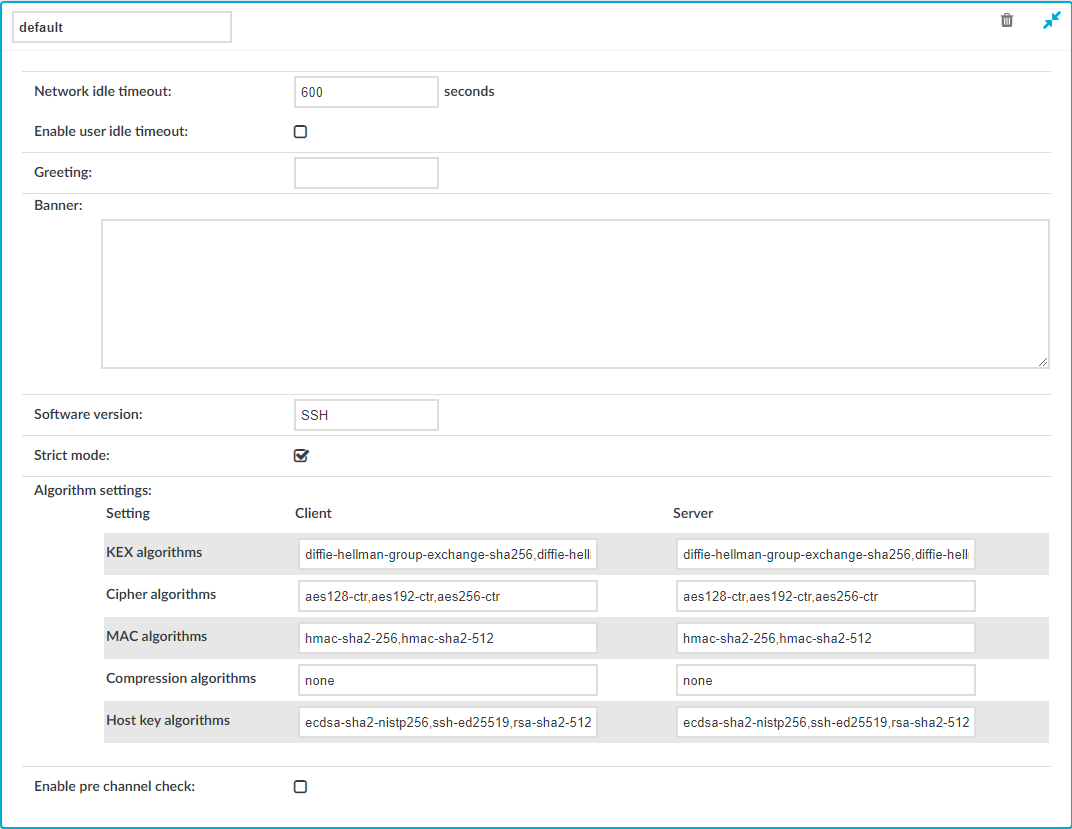
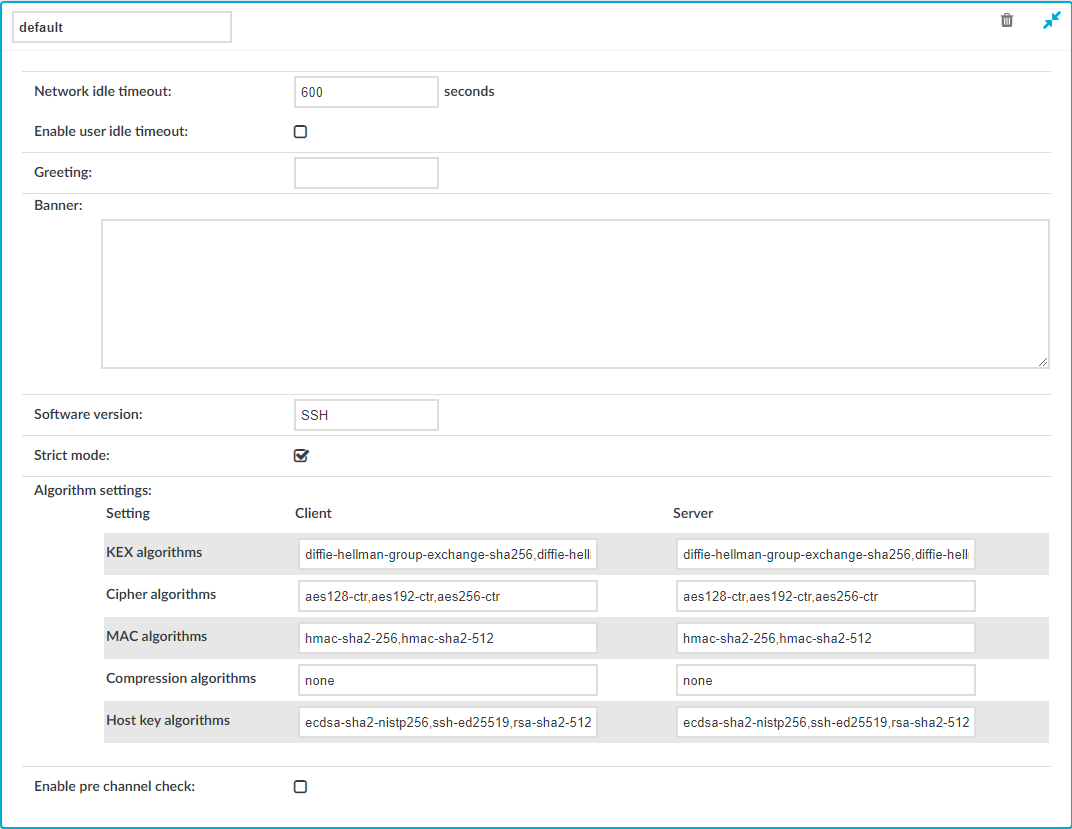
Figure 236: Traffic Controls > SSH > Settings — SSH settings
To create a new SSH settings profile or edit an existing one
-
Navigate to the Traffic Controls > SSH > Settings and click  to create an SSH setting profile. Enter a name for the profile (for example strongencryption).
to create an SSH setting profile. Enter a name for the profile (for example strongencryption).
-
Click  to display the parameters of the SSH connection.
to display the parameters of the SSH connection.
-
Network idle timeout: Connection timeout value in seconds. To avoid early timeout, set it to a larger value, for example a week (604800 seconds).
Even if the user is not active, the session can contain activity that must be audited (for example, the output of a script). The idle timeout period will start only after this activity has stopped.
|

|
Caution:
Determining if a connection is idle is based on the network traffic generated by the connection, not the activity of the user. For example, if an application or the taskbar of a graphical desktop displays the time which is updated every minute, it generates network traffic every minute, negating the effects of timeout values greater than one minute and preventing One Identity Safeguard for Privileged Sessions (SPS) from closing the connection. |
-
User idle timeout: If no user activity is detected, terminate the session after the configured time has passed since the last user activity.
This can be useful if only user-generated network traffic is important in a session. By using this option, situations described in the caution of Network idle timeout (such as a taskbar clock keeping the network traffic open indefinitely) can be avoided. To enable user idle timeout, select Enable user idle timeout and enter a value that is greater than or equal to the value of Network idle timeout.
-
To display a greeting message to the clients after connecting the server, enter the message into the Greeting field.
-
To display a banner message to the clients before authentication (as specified in RFC 4252 — The Secure Shell (SSH) Authentication Protocol), enter the message into the Banner field. For example, this banner can inform the users that the connection is audited.
-
Optional. You can specify additional text to append to the SSH protocol banner, for example to mask the OpenSSH version upon connection. Enter the text in the Software version field.
-
If needed, modify the encryption parameters. SPS enforces policies on the various elements of the encrypted SSH communication, such as the MAC, key-exchange, and cipher algorithms that are permitted to be used. The parameters can be set separately for the client and for the server side. The attributes are comma-separated strings listing the enabled methods/algorithms, in the order of preference.
For a complete list of the available parameters, see Supported encryption algorithms.
NOTE:
Do not use the CBC block cipher mode, or the diffie-hellman-group1-sha1 key exchange algorithm. For details, see Supported encryption algorithms in the Administration Guide.
-
To check the protocol-level parameters of the connections very strictly, select the Strict mode option. This option is enabled by default. When this option is enabled:
SPS will reject connections that use unrealistic parameters, for example:
SPS will reject port-forwarding connections where the address in the port-forwarding request and the channel-opening request does not match.
NOTE: Strict mode can interfere with certain client or server applications.
NOTE: Strict mode is not working with the Windows internal Bash/WSL feature, because it uses a very large terminal window size. Using Windows internal Bash/WSL is not supported.
-
Before establishing the server-side connection, SPS can evaluate the connection and channel policies to determine if the connection might be permitted at all, for example it is not denied by a Time Policy. To enable this function, select the Enable pre channel check option. That way SPS establishes the server-side connection only if the evaluated policies permit the client to access the server.
-
Click  .
.
-
Select this settings profile in the SSH settings field of your connections.
The following tables contain all the encryption algorithms you can configure One Identity Safeguard for Privileged Sessions (SPS) to recognize. If you use a configuration that is only partially supported, SPS might ignore the connection without warning.
NOTE: Do not use the CBC block cipher mode, or any sha1-based KEX, MAC, or host key algorithm, which are considered weak.
Key exchange algorithms
The default SPS configuration for both the client and the server is the following:
ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,diffie-hellman-group14-sha256
The following key exchange (KEX) algorithms are recognized:
Figure 237: Key exchange (KEX) algorithms
| ecdh-sha2-nistp256 |
✔ |
|
| ecdh-sha2-nistp384 |
✔ |
|
| ecdh-sha2-nistp521 |
✔ |
|
| diffie-hellman-group1-sha1 |
- |
Not recommended |
| diffie-hellman-group14-sha1 |
- |
Not recommended |
| diffie-hellman-group14-sha256 |
✔ |
|
| diffie-hellman-group15-sha512 |
- |
|
| diffie-hellman-group16-sha512 |
✔ |
|
| diffie-hellman-group17-sha512 |
- |
|
| diffie-hellman-group18-sha512 |
✔ |
|
| diffie-hellman-group-exchange-sha256 |
✔ |
|
| diffie-hellman-group-exchange-sha1 |
- |
Not recommended |
During an SSH session, SPS performs a key re-exchange after each gigabyte of transmitted data or after each hour of connection time, whichever comes sooner.
Cipher algorithms
The default SPS configuration for both the client and the server is the following:
aes128-ctr,aes192-ctr,aes256-ctr
The following cipher algorithms are recognized:
Figure 238: Cipher algorithms
| 3des-cbc |
– |
Not recommended |
| blowfish-cbc |
– |
Not recommended |
| twofish256-cbc |
– |
Not recommended |
| twofish-cbc |
– |
Not recommended |
| twofish192-cbc |
– |
Not recommended |
| twofish128-cbc |
– |
Not recommended |
| aes256-cbc |
– |
Not recommended |
| aes192-cbc |
– |
Not recommended |
| aes128-cbc |
– |
Not recommended |
| aes256-ctr |
✔ |
|
| aes192-ctr |
✔ |
|
| aes128-ctr |
✔ |
|
| serpent256-cbc |
– |
Not recommended |
| serpent192-cbc |
– |
Not recommended |
| serpent128-cbc |
– |
Not recommended |
| arcfour |
– |
Not recommended |
| idea-cbc |
– |
Not recommended |
| cast128-cbc |
– |
Not recommended |
| none |
– |
Means no cipher algorithm; not recommended |
Message authentication code (MAC) algorithms
The default SPS configuration for both the client and the server is the following:
hmac-sha2-256,hmac-sha2-512
The following MAC algorithms are recognized:
Figure 239: Message Authentication Code (MAC) algorithms
| hmac-sha1 |
– |
Not recommended |
| hmac-sha1-96 |
– |
Not recommended |
| hmac-md5 |
– |
Not recommended |
| hmac-md5-96 |
– |
Not recommended |
| hmac-sha2-256 |
✔ |
|
| hmac-sha2-512 |
✔ |
|
SSH compression algorithms
The default SPS configuration for both the client and the server is the following:
none
The following SSH compression algorithms are recognized:
Figure 240: SSH compression algorithms
| zlib |
– |
Not recommended |
| none |
✔ |
Means no compression |
Host key algorithms
The default SPS configuration for both the client and the server is the following:
ecdsa-sha2-nistp256,ssh-ed25519,rsa-sha2-512,rsa-sha2-256,ssh-rsa
The following host key algorithms are recognized:
Figure 241: Host key algorithms
| ecdsa-sha2-nistp256 |
✔ |
|
| ssh-ed25519 |
✔ |
|
| rsa-sha2-512 |
✔ |
|
| rsa-sha2-256 |
✔ |
|
| ssh-rsa |
✔ |
Not recommended
NOTE: The ssh-rsa public key signature algorithm that depends on SHA-1 is not recommended and will be disabled in a future release. |
to display the advanced settings and verify that the Server side host key settings > Plain host key check option is set to Accept key for the first time.
.


 to create an SSH setting profile. Enter a name for the profile (for example strongencryption).
to create an SSH setting profile. Enter a name for the profile (for example strongencryption).